After Stuxnet, Flame and Duqu comes Gauss, another highly-targeted malware
If you are into math, computers or computer games, you have probably come into contact with the Gauss name. If you are living in the Middle East, or are one of the unfortunate souls in other regions of the world that have been targeted, you'd also may have come into contact with a newly discovered form of malware known as Gauss.
This malware follows the lines of previously discovered highly sophisticated programs such as Stuxnet, Flame and Duqu which all have targeted the Middle East in particular.
Kaspersky has published an in depth analysis of Gauss on Securelist which provides background information and a summary at the beginning. According to Kaspersky's information, Gauss was first distributed back in the September to October months of 2011. And just like it has been with other malware of its type, it took security companies more than six months to discover the malware and begin analysis of it.
One of the reasons for this is that the malware has been used to target individuals in specific countries with the Lebanon, Israel and Palestine being targeted the most with the Lebanon topping the list by a wide margin. According to Kaspersky, Gauss uses the same exploit that Stuxnet was using, but in a more effective manner.
The module masks the Trojan's files on the USB drive without using a driver. It does not infect the system: information is extracted from it using a spy module (32- or 64-bit) and saved on the USB drive.
The primary purpose of Gauss is to collect information and send those information to servers. The trojan can for instance intercept user sessions in browsers and steal passwords, cookies and the browser history, collect information about the computers hardware, the processes and folders of the operating system, and information about local, network and removable drives. It in addition can infect USB Flash drives with a "spy module" to spread to other computer systems and extract information from those systems as well.
The attack users various modules to collect data, infiltrate web browsers and communicate with a master server.
| Module name | Location | Description |
|---|---|---|
| Cosmos | %system32%\devwiz.ocx | Collects information about CMOS, BIOS |
| Kurt, Godel | %system32%\dskapi.ocx | Infects USB drives with data-stealing module |
| Tailor | %system32%\lanhlp32.ocx | Collects information about network interfaces |
| McDomain | %system32%\mcdmn.ocx | Collects information about user's domain |
| UsbDir | %system32%\smdk.ocx | Collects information about computer's drives |
| Lagrange | %system32%\windig.ocx | Installs a custom 'Palida Narrow' font |
| Gauss | %system32%\winshell.ocx | Installs browser plugins that collect passwords and cookies |
| ShellHW | "%system32%\wbem\wmiqry32.ocx %system32%\wbem\wmihlp32.ocx " |
Main loader and communication module |
One interesting aspect of Gauss is that it is designed to specifically steal and monitor data related to online transactions, such as those with banks or PayPal. While it would have been certainly in the realm of possibility that Gauss has been designed to steal money from individuals, it is more likely that it is information the attackers were after. Bank transactions reveal a lot about potential targets, not only about funding but also contact related.
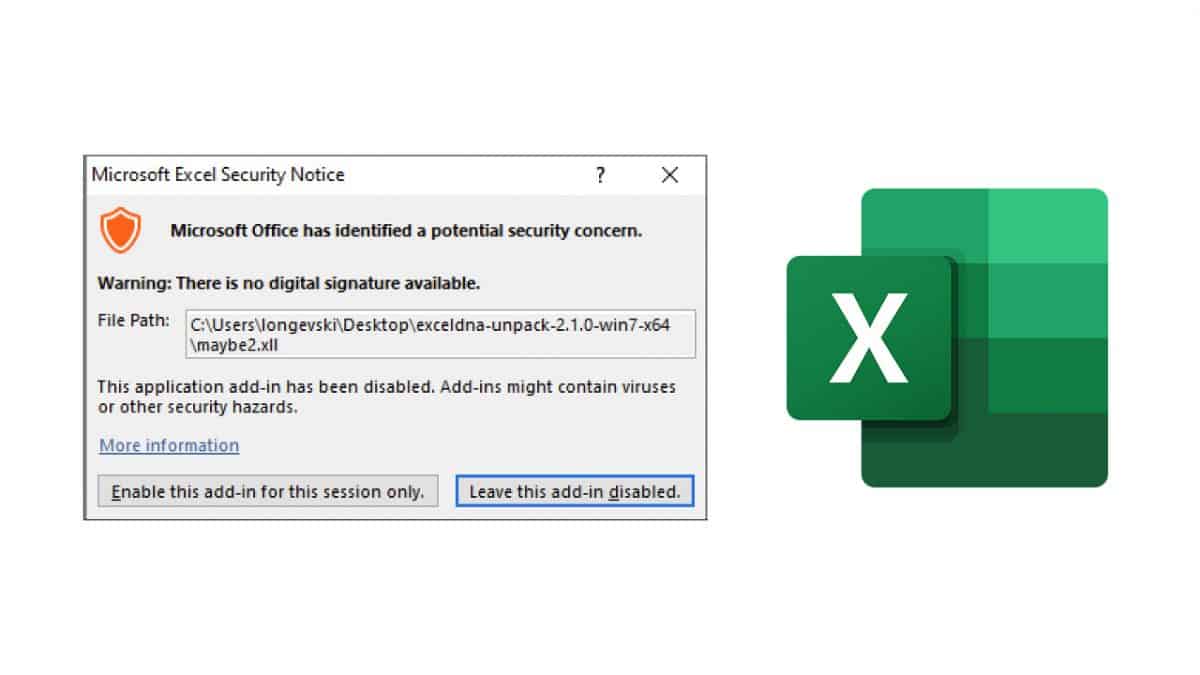
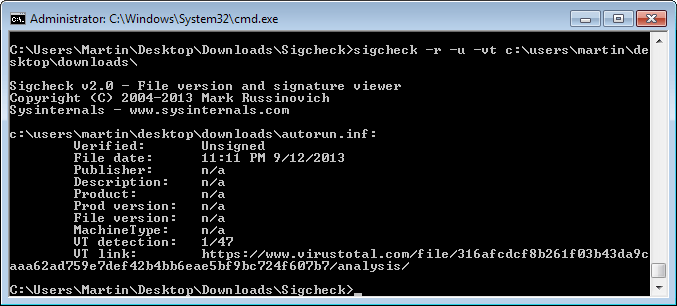
All Kaspersky products are detecting the Gauss trojan by now. If you do not use a Kaspersky product you can use the file names and locations in the table above, or contact your antivirus vendor to find out if Gauss is also detected by its products.
It is highly recommended to install security patches as soon as they get released. Check out our Windows Update overview here for additional information on how that is done under Windows.
Update: Kaspersky's free removal tool can detect Gauss malware on your PC. There is also an online check available that tests your computer for a font that the malware installs on the system.
Advertisement













So , what a check after the fact, when all private info has been stolen for 6 months, will help those poor Windows and Android users ? If the OS can’t protect the users and needs help from 3rd party applications that fail as well, it is time either to move to a safer OS , for the time being, or , it time for new, really secure OS to emerge.
>Bank transactions reveal a lot about potential targets, not only about funding but also contact related.
Just the type of information an intelligence agency would be after!