Microsoft .Net Framework Security Update Released
Microsoft has released an out-of-band security update for the Windows operating system that fixes a number of security vulnerabilities in the Microsoft .NET Framework.
The vulnerability affects all 32-bit and 64-bit versions of Windows that receive security updates, and the following versions of the Microsoft .NET Framework: Microsoft .Net Framework 1.1, 2.0, 3.5 Service Pack 1 and 4.
At least one of the vulnerabilities received the maximum severity rating of critical, the highest possible rating, on all affected operating systems and .Net versions.
Microsoft notes that the most severe vulnerability could allow elevation of privileges "if an unauthenticated attacker sends a specially crafted web request to" a target site. Attackers who successfully exploit the issue can "take any action in the context of an existing account on the ASP.NET site, including executing arbitrary commands".
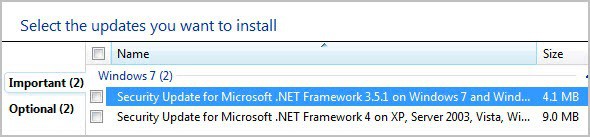
Security updates are already listed on Windows Update. Windows users who have only installed the Microsoft .Net Framework 4.0 Client Profile may only see the update rated as important in Windows Update instead of critical. That is because ASP.Net, the component that is affected by the critical vulnerability, is not included in that version of the framework.
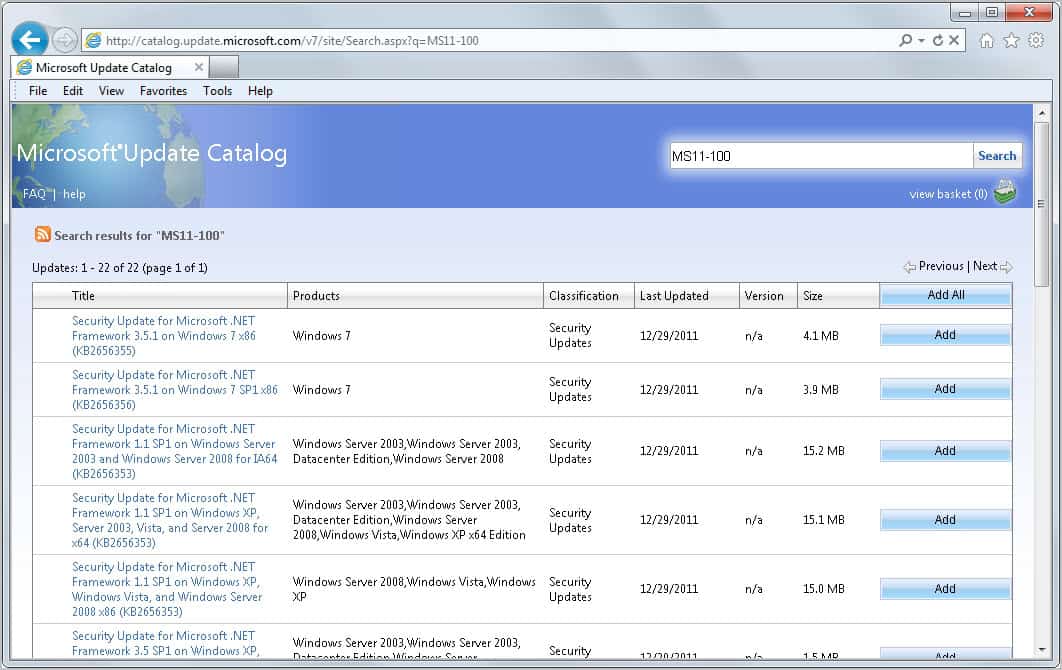
Most Windows users have configured automatic updates. Users who do not use automatic updates or Windows Update may download the patches from the Microsoft Update Catalog site instead. Please note that you can only open the site in Internet Explorer and not in other browsers.
Microsoft's Download Center is currently not listing the security updates. It is however likely that they will appear on the site in the next days.
A restart of the computer is not required after applying the patches. The patches will merely stop related services during patches before they are restarted.
Additional information about the security vulnerability is available on the Microsoft Security Bulletin page. This bulletin raises the count to 100 bulletins that have been released by the Redmond company in 2011.


















“… restart of the computer is not required after applying the patches. The patches will merely stop related services during patches before they are restarted.”
A restart was required when I applied the updates to my WIn7-SP1 Professional (32-bit) system.
A surprise since I wasn’t expecting it..
That’s strange, as Microsoft noted that a restart is not required.
I only have .Net Framework 4 installed but I get the Update for 3.51 and 4 like in the first image in the article.
Is this normal and if not how do I fix this?
Thanks
Microsoft is known to push un-needed updates to Windows PCs.
I too don’t have .Net 3.5.1 installed , yet Microsoft pushed and run the update on my Win 7, wasting download time, and for some users , with Internet data quota, may have been over charged for the data.
The .Net Framework 3.5 is embedded into Windows 7.
Yes that is normal, no need to worry.
Thanks Martin, For this ferry useful MS-update news, good that MS did not wait with the update till there scheduled update date next month.
Got the updates yesterday!
Good reminder for everybody else! :)