Microsoft Patch Day August 2011 Overview
Microsoft yesterday evening released this month's security patches for their software products. The 13 security bulletins fix security related issues in Microsoft products such as the Windows operating system, Microsoft Office, the .Net Framework and Internet Explorer. Two of the security bulletins have received a critical severity rating, the highest possible rating while nine have received an important rating and two a moderate one. Please note that this is the maximum severity rating, the rating may be lower for specific products.
All in all, the bulletins address 22 vulnerabilities in Microsoft products. The two critical updates address issues in Internet Explorer and DNS Server.
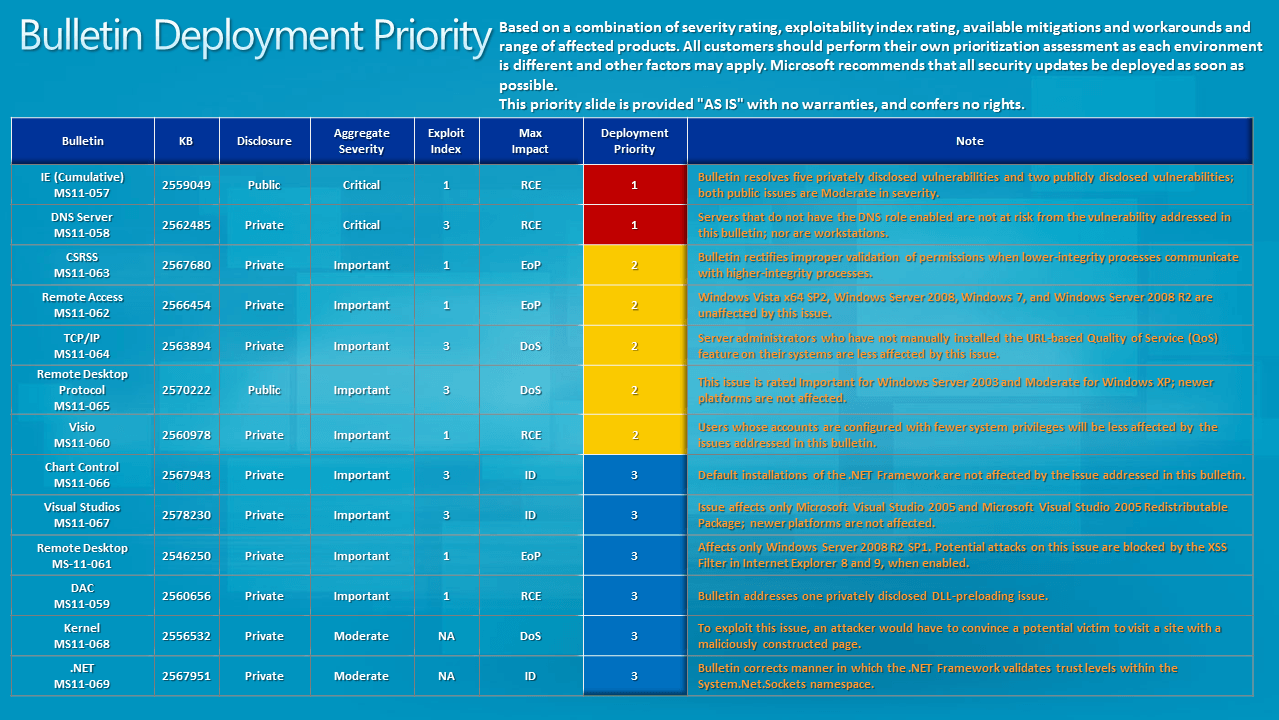
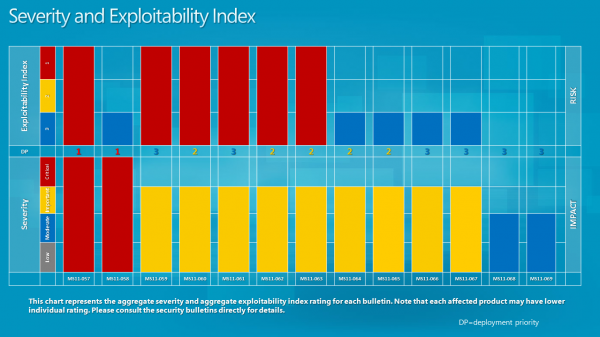
Microsoft has released deployment priorities and the severity and exploitability index. (click on the images for full size)
- MS11-057 - Cumulative Security Update for Internet Explorer (2559049) - This security update resolves five privately reported vulnerabilities and two publicly disclosed vulnerabilities in Internet Explorer. The most severe vulnerabilities could allow remote code execution if a user views a specially crafted Web page using Internet Explorer. An attacker who successfully exploited any of these vulnerabilities could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS11-058 - Vulnerabilities in DNS Server Could Allow Remote Code Execution (2562485) - This security update resolves two privately reported vulnerabilities in Windows DNS server. The more severe of these vulnerabilities could allow remote code execution if an attacker registers a domain, creates an NAPTR DNS resource record, and then sends a specially crafted NAPTR query to the target DNS server. Servers that do not have the DNS role enabled are not at risk.
The bulletins that fix important issues.
- MS11-059 - Vulnerability in Data Access Components Could Allow Remote Code Execution (2560656) - This security update resolves a privately reported vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if a user opens a legitimate Excel file (such as a .xlsx file) that is located in the same network directory as a specially crafted library file. An attacker who successfully exploited this vulnerability could gain the same user rights as the logged-on user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS11-060 - Vulnerabilities in Microsoft Visio Could Allow Remote Code Execution (2560978) - This security update resolves two privately reported vulnerabilities in Microsoft Visio. The vulnerabilities could allow remote code execution if a user opens a specially crafted Visio file. An attacker who successfully exploited this vulnerability could gain the same user rights as the logged-on user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS11-061 - Vulnerability in Remote Desktop Web Access Could Allow Elevation of Privilege (2546250) - This security update resolves a privately reported vulnerability in Remote Desktop Web Access. The vulnerability is a cross-site scripting (XSS) vulnerability that could allow elevation of privilege, enabling an attacker to execute arbitrary commands on the site in the context of the target user. The XSS Filter in Internet Explorer 8 and Internet Explorer 9 prevents this attack for its users when browsing to a Remote Desktop Web Access server in the Internet Zone. The XSS Filter in Internet Explorer 8 and Internet Explorer 9 is not enabled by default in the Intranet Zone.
- MS11-062 - Vulnerability in Remote Access Service NDISTAPI Driver Could Allow Elevation of Privilege (2566454) -
This security update resolves a privately reported vulnerability in all supported editions of Windows XP and Windows Server 2003. This security update is rated Important for all supported editions of Windows XP and Windows Server 2003. Windows Vista, Windows Server 2008, Windows 7, and Windows Server 2008 R2 are not affected by the vulnerability.The vulnerability could allow elevation of privilege if an attacker logs on to an affected system and runs a specially crafted application designed to exploit the vulnerability and take complete control over the affected system. An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability.
- MS11-063 - Vulnerability in Windows Client/Server Run-time Subsystem Could Allow Elevation of Privilege (2567680) -
This security update resolves a privately reported vulnerability in Microsoft Windows. The vulnerability could allow elevation of privilege if an attacker logs on to an affected system and runs a specially crafted application designed to send a device event message to a higher-integrity process. An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability. - MS11-064 - Vulnerabilities in TCP/IP Stack Could Allow Denial of Service (2563894) - This security update resolves two privately reported vulnerabilities in Microsoft Windows. The vulnerabilities could allow denial of service if an attacker sends a sequence of specially crafted Internet Control Message Protocol (ICMP) messages to a target system or sends a specially crafted URL request to a server that is serving Web content and has the URL-based Quality of Service (QoS) feature enabled.
- MS11-065 - Vulnerability in Remote Desktop Protocol Could Allow Denial of Service (2570222) - This security update resolves a privately reported vulnerability in the Remote Desktop Protocol. The vulnerability could allow denial of service if an affected system received a sequence of specially crafted RDP packets. Microsoft has also received reports of limited, targeted attacks attempting to exploit this vulnerability. By default, the Remote Desktop Protocol (RDP) is not enabled on any Windows operating system.
- MS11-066 - Vulnerability in Microsoft Chart Control Could Allow Information Disclosure (2567943) - This security update resolves a privately reported vulnerability in ASP.NET Chart controls. The vulnerability could allow information disclosure if an attacker sent a specially crafted GET request to an affected server hosting the Chart controls. Note that this vulnerability would not allow an attacker to execute code or to elevate the attacker's user rights directly, but it could be used to retrieve information that could be used to further compromise the affected system. Only web applications using Microsoft Chart Control are affected by this issue. Default installations of the .NET Framework are not affected.
- MS11-067 - Vulnerability in Microsoft Report Viewer Could Allow Information Disclosure (2578230) - This security update resolves a privately reported vulnerability in Microsoft Report Viewer. The vulnerability could allow information disclosure if a user views a specially crafted Web page. In all cases, however, an attacker would have no way to force a user to visit the Web site. Instead, an attacker would have to persuade a user to visit the Web site, typically by getting them to click a link in an e-mail message or Instant Messenger message that takes the user to the vulnerable Web site.
And finally the moderate bulletins.
- MS11-068 - Vulnerability in Windows Kernel Could Allow Denial of Service (2556532) - This security update resolves a privately reported vulnerability in Microsoft Windows. The vulnerability could allow denial of service if a user visits a network share (or visits a Web site that points to a network share) containing a specially crafted file. In all cases, however, an attacker would have no way to force a user to visit such a network share or Web site. Instead, an attacker would have to convince a user to do so, typically by getting the user to click a link in an e-mail message or Instant Messenger message.
- MS11-069 - Vulnerability in .NET Framework Could Allow Information Disclosure (2567951) - This security update resolves a privately reported vulnerability in Microsoft .NET Framework. The vulnerability could allow information disclosure if a user views a specially crafted Web page using a Web browser that can run XAML Browser Applications (XBAPs). In a Web-based attack scenario, an attacker could host a Web site that contains a Web page that is used to exploit this vulnerability. In addition, compromised Web sites and Web sites that accept or host user-provided content or advertisements could contain specially crafted content that could exploit this vulnerability. In all cases, however, an attacker would have no way to force users to visit these Web sites. Instead, an attacker would have to convince users to visit the Web site, typically by getting them to click a link in an e-mail message or Instant Messenger message that takes users to the attacker's Web site. This vulnerability could also be used by Windows .NET applications to bypass Code Access Security (CAS) restrictions.
The updates are as usually available via Windows Update and Microsoft's Download Center (even though I would not recommend using this at this time as it is a mess).
Advertisement





















Wow! Thanks for the images and graphs. Very helpful! Did you make them or does Microsoft produce them?
Microsoft produces them.
Hoi and thanks Martin,
For this ferry elaborate explanation (especially the pictures are great visual help) for this again ferry extensive update/upgrade from Microsoft. What a hassle extra month again with first updating, installing, restarting the system, cleaning the system and making a backup from the system. And than afcourse the update from other software venders like the updates yesterday from as Adobe (always a problem to uninstall there flash software correctly from main firefox) flash player and shockwave player. Not to forget the new Revo uninstaller an µTorrent. So with this upgrades i am almost one hole evening busy. But i have three windows operating system running computers and lets not forget main ubuntu computer.
Where do i get the time and energies from to do this only once? And this same cycle i have to do once every mouth in the year, year after year upon to main everlasting resting place. :)