Secure your files: An introduction to GnuPG
GnuPG allows you to encrypt data so only the intended recipient, with a key and a password, can decrypt it. It also provides a mechanism for verifying data is from the person who has claimed to send it. GnuPG can also provide a way for you to securely prevent your files from being opened without authorisation (at a US border, for example).
GnuPG, in technical terms, utilises a mixture of symmetric-key cryptography and public-key cryptography. This basically means a person generates a pair of keys; one of which is publicly shared and one is not. The publicly shared key is used to people can encrypt data for a specific person whilst the private key is used to decrypt, encrypt and sign data.
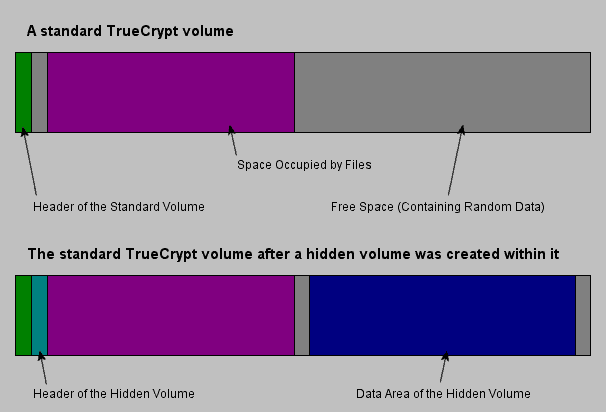
If you encrypt data to only be decrypted only by your private key and you carry your private key on another medium of storage, the data you encrypted will be effectively impossible to decipher.
To get started with GnuPG, you must download GnuPG which is free and open-source.
GnuPG is available for effectively all operating systems. After you have downloaded and installed GnuPG, it might be wise to download a graphical interface because it is command line based.
Some GUIs focus on the management of keys, such as the generation of them and storing other people's public keys, whilst others focus on the encrypting/decrypting.
WinPT is a popular Windows option. As for encrypting and decrypting, there are many choices including Enigmail for Thunderbird, FireGPG for Firefox and WinPT also provides facilities to do this.
With a GUI, it is fairly easy to get to grips with GnuPG. Most key managers provide wizards for the generation of keys.
To obtain someone's public key, so you can send data to them securely, you could either ask them or go onto a keyserver such as pgp.mit.edu, copy their key into Notepad and then import it into your key manager.
It is essential to send your keys to keyservers, I would suggest pgp.mit.edu, and this can be done either through the GUI or through exporting your public key and uploading it to these sites. Once you have someone's public key, and you are sure it belongs to them and is not a hoax, you can sign the key inside your key manager and then submit it, so people know that key is authentic.
Key software to get started with GPG
- GnuPG is absolutely necessary. There is a Windows binary available.
- A GUI is also necessary. For Windows users, WinPT is a safe bet.
- If you use Thunderbird, install Enigmail. If you use Firefox, install FireGPG.
If you have installed GPG and would like to try it out, feel free to send me an encrypted email. My email is computerjoe (at) gmail.com and my key is on this page.
Advertisement


















How can I run the commeand from Java as this ask for validation of User ID. means are you sruer User Id is ,
I agree with Windows Fix. Having to share your public keys with everyone you intend to correspond with, look up the keys of people you want to send messages to and store your private key in a separate location seems like a lot of hoops to jump through. And the average user probably won’t know how or have time to do the jumping. So I suggest the Voltage Security Network (VSN). It makes secure messaging really as easy as “click and encrypt.” Leveraging Identity-Based Encryption, it uses something as easy as an email address as the encryption key. So no need to manage keys or encryption/decryption passwords. Because if people are going to start securing their everyday communications, it will only be if the solution is seamless. You don’t need to watch a tutorial video or take a cryptography class to be able to use the VSN. And better yet, recipients need no software or add-ons to view—or reply to—secure messages. Super simple email (and file & document) encryption, it just works. Learn more at http://www.voltage.com/vsn/index.htm.
Hi,
you can find a VideoTutorial about this on http://www.sempervideo.de/?p=686.
Its in german, but you can of course take the article text hier. Its basicly the same.
Greetings.
The Windows Fix: Maybe, and I dislike the idea of TSA looking through my files. Software makes tihs all really easy when it’s set up
Are encrypting your files like this becoming more commonplace? I suppose if you are communicating often with someone, but it just seems like an added annoyance.