Tracing a Hacker
Tracing a Hacker is a article aimed at beginners (computer users who do not have a lot of experience working with computers) who want to learn the basics of finding out if unauthorized third parties are connected to their computer system. It gives a rough introduction to some basic concepts like tcp/ip, ports and how hackers find their targets.
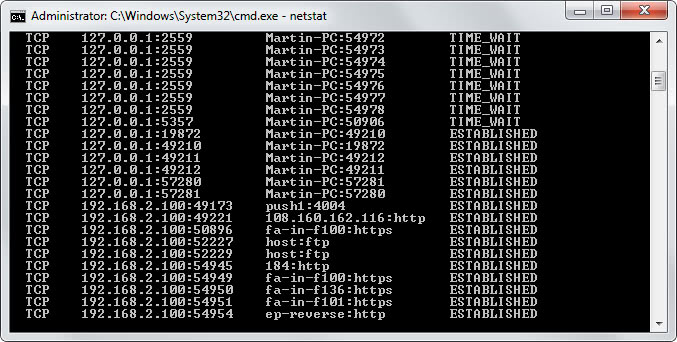
This is a good read if you don't know where to start as it provides you with an overview of things you can use for that. The first command that is explained in detail is the netstat command which you can use to list all systems that are currently connected to your Windows system. The list can be quite large if you are running P2P (peer to peer) software or other software that makes use of many connections. It is probably a good idea to exit P2P software and similar programs before you run the netstat command so that you end up with a smaller list that you can go through much easier.
After explaining various netstat -commands, ports are explained which may help you identify suspicious connections to your computer. It is a good idea to know standard basic ports like 80 for a http connection and 21 for ftp connections, as they are best ignored. This does not mean that every connection on port 80 for instance is harmless but it is a good indicator to ignore those ports in the beginning and concentrate on non-standard ports at first.
The next command in line is the tracert command which can be extremely useful as it enables you to trace a connection back to its origin. So, if you want to find out more about an IP address that is connected to your PC, you can use it to do so. Note that the IP in question does not need to be a home user's IP address. It can very well be a proxy IP or VPN IP.
After that reverse dns querries and dns are explained. The last chapter lists common ports that are often used by trojans and other malicious software. All in all a very good article for anyone who wants to know more about computers and Internet and network connections. This is of course aimed at beginners and a good starting point for them. Its easy to use Google to retrieve further information.
Advertisement















