Malware exploits decade old Windows bug, which has an opt-in fix

A decade old Windows bug, for which a fix is available, is used by malware currently in attacks against Windows devices. Malware actors may exploit the vulnerability to add malicious code to signed Windows files without them losing their signed status.
Digital signatures are used on Windows to determine the authenticity of files. Most security solutions check for signatures when they check files on Windows machines.
What makes this exploit even more problematic is the fact that a fix is available, but that it is opt-in. If that was not enough, it appears that upgrades to Windows 11 may drop the fix, if applied in the Windows Registry.
Bleeping Computer reported this week that the VOIP communications company 3CX was compromised. The attackers managed to include malware into the company's desktop application for Windows. Two DLL files used by the desktop application were modified by the threat actors to include malware, more precisely, an information-stealing trojan.
What makes the attack special is that the attackers are exploiting CVE-2013-3900, WinVerifyTrust Signature Validation Vulnerability, which Microsoft confirmed in 2013 for the first time and has updated in early 2022 with additional information.
How to protect Windows devices against the attacks
Microsoft published an opt-in fix to address the issue in 2013, and it has been valid ever since.
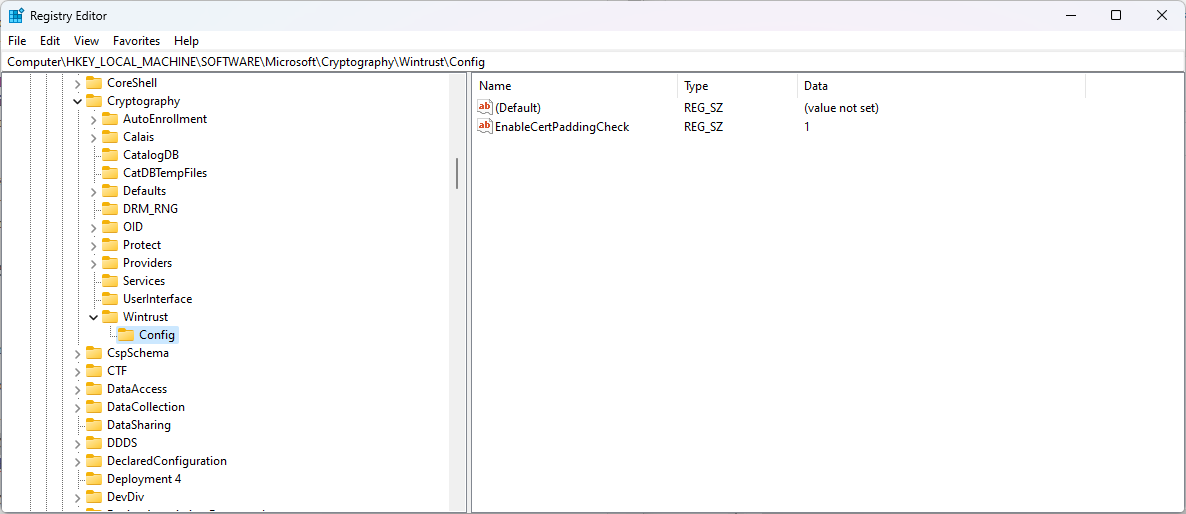
Windows 64-bit versions may be protected with the following Registry code:
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\Wintrust\Config]
"EnableCertPaddingCheck"="1"
[HKEY_LOCAL_MACHINE\Software\Wow6432Node\Microsoft\Cryptography\Wintrust\Config]
"EnableCertPaddingCheck"="1"
Note: you need to paste the code into a plain text file and rename its file extension, so that it is .reg. We have uploaded a Zip archive with Registry files for 32-bit and 64-bit versions of Windows: windows-registry-fix
All you need to do is double-click on the file to add the information to the Registry (a verification prompt is displayed, which you need to allow).
A restart of the system is required. Delete the listed Registry values to undo the change at any time.
Enabling the changes will make non-confirming binaries "appear unsigned" and be rendered untrusted as a consequence.
Why opt-in?
Why did Microsoft release the patch this way, and did not integrate it directly into Windows? The extensive FAQ on the support page provides an answer. According to Microsoft, enabling the stricter verification behavior may "impact some installers" and also certain AppLocker behavior and Software Restriction Policies.
Closing Words
Windows administrators may check the listed Registry values above to verify if the devices are protected against the vulnerability. Windows devices that were upgraded to Windows 11 need to be rechecked, as the Registry values are likely no longer there after the upgrade. Note that applying the changes using policies should keep them enabled after the upgrade.























! always, backup ur reg. otherwise say hello to bluescreens !
anyway, I’ve been always up-to date on my w10 machine, and I
have many other problems to afraid, than this reg exploit .
@Martin,
On Windows 8.1 there isn’t a WinTrust key at either of the locations mentioned in the article. Does the fix create those as well?
Thanks Martin, appreciated the reg files.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\Wintrust\Config]
“EnableCertPaddingCheck”=-
[HKEY_LOCAL_MACHINE\Software\Wow6432Node\Microsoft\Cryptography\Wintrust\Config]
“EnableCertPaddingCheck”=-
Hmmm . . . another .reg file provided w/o one to undo the change.
Thanks.
For convenience – in case I come across installers that I definitely trust but this “fix” doesn’t – I created the MS recommended “undo” reg files and included them inside my copy of your zip file. That way I can reverse the fix then quickly apply the fix again. Others might consider updating your zip to include them as well.
So this alone is a fix?:
“Windows 64-bit versions may be protected with the following Registry code:” etc etc
64-bit Win 7 also?
In few words… signed software mean nothing for MS.
Just a decade to fix something that they recognized to be unable fixing it in a clear way.
Garbagesoft in all the extension of the word itself.
Thanks for the convenient Zip file Martin. Problem fixed on my Win 11.