Microsoft removed malicious extensions from its Edge Extensions Store
Microsoft maintains an extensions store similar to the stores maintained by Mozilla and Google. Users of the new Edge web browser may download and install extensions from that store or from the official Chrome Web Store.
Mozilla's and Google's extensions store had issues with spam, malware, and privacy-invading extensions in the past. Mozilla tried to address the problem with the introduction of the Firefox Recommended Extensions program; extensions in the program go through a verification process that includes code analysis before they are published on Mozilla AMO.
Tip: check out our guide that helps you find out if a Chrome extension is safe.
And Microsoft? The company's extensions store for Microsoft Edge surpassed the 1000 listed extensions mark a few months ago and it looked like as if it would finally get some traction. Not all is positive though when it comes to the store.
The developer of the popular dark mode extension Dark Reader noticed recently that copycat extensions appeared on the Microsoft Store and also on Mozilla AMO. He analyzed the extensions like any good developer would do and noticed that they were replicas of Dark Reader. More worrying than that was that they included malicious code that was hidden inside a png file.
A malicious code was hidden and encoded in a *.png file. In 5 days it downloaded and executed another code, that was collecting data from web pages using fake forms, and later sent this data to a remote server.
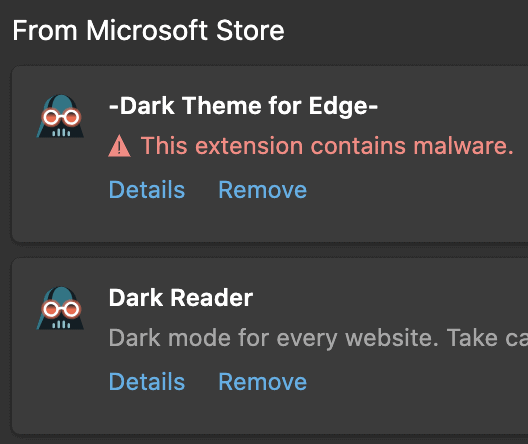
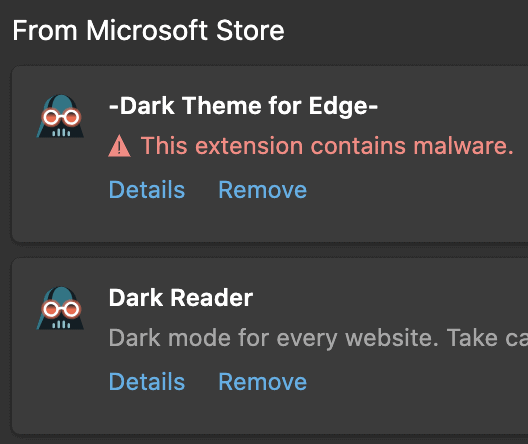
The developer contacted Microsoft and the company removed the offending extensions from its Extensions Store. Users of the new Edge browser who have installed the malicious extension should see it flagged when they open the list of installed extensions in the Microsoft browser.
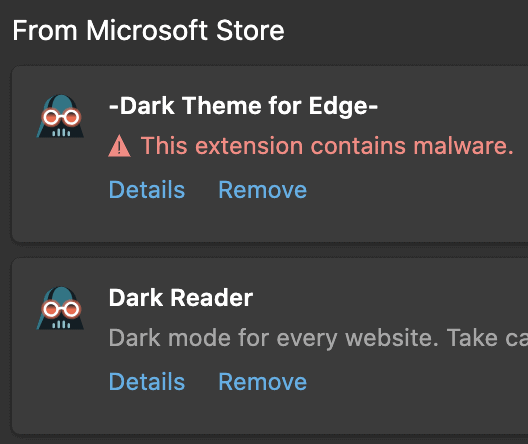
The warning "This extension contains malware" should be displayed underneath the extension.
Closing Words
The big three extensions stores had to deal with problematic extensions in the past and it looks as if this won't change anytime soon. Extensions of Mozilla's recommended extensions program for Firefox are probably the safest option when it comes installing browser extensions because of the program's strict rules.
Risks can be minimized, for instance by analyzing the code and the manifest of extensions before installing them, or by focusing on a handful of highly regarded extensions by trusted developers.
Now You: Do you vet extensions before you install them? (via Techdows)




















Recently tried to find a good Gestures extension for Brave that wasn’t basically spyware or adware. What a pain that was.
Chromes extension store is filled with malware so it stands to reason some of it will find its way to Microsoft’s extension store.
At least Microsoft removed it after being contacted. With Google it can take MONTHS for them to remove even obvious malware from the extension store and Google play Android store.
As for the comment above about Microsoft “security bloatware”… I guess arguably being the #1 AV/Anti malware scanned available for Windows isnt important but what do tons of security experts write articles about it know?
Anyways there is no AV scanner in the world that would have flagged this because the code in the extension itself wasn’t “malicious”.
The problem is Google’s design of how the extension system in Chromium works. It’s an issue they have known about literally since it launched… Actually it was talked about on the testing forum chrome was in alpha.
I’ve wanted to ditch chrome for a while because of its extension system and other security issues.. some of which Microsoft has fixed in edge but they would be wise to gut the extension system as well. I understand why they would want to keep it since it means instant compatibility with every chrome extension.
It’s a shame they ditched the non chromium version of edge. I actually liked it quite a bit but I kept using chrome as my primary browser because it would sync to my phone and across PC’s. Something edge hadn’t yet implemented on mobile.
Honestly the further from Google’s eco system any of us can get the better. They are an advertising company. User security and privacy isn’t in their best interest.
Thank God for adguard. I block so many Google bs on my Android phone it’s insane. Almost 2 gigs a month between ads and app analytics. I use it on windows as well since Google is gimping the ability for adblock extensions to work which is a huge security risk in itself. Also adguard would have blocked this extension from being able to connect because it works at a system level and the extension was connecting to a blocked up, I got a copy and checked.
@ d0x360
Thank you for the tip-off about AdGuard
This Dark Reader extension slows down the browser, why I prefer using the built in flag “Force Dark Mode for Web Contents”, but Microsoft broke it in latest Dev and Canary build of Edge. No choice but to use this extension.
how can i trace my extension?
Chrome (Chromium):
Open chrome://extensions page.
For each extension click Details.
Click View in Chrome Web Store.
Genuine Dark Reader has 2,000,000+ users, extension ID is eimadpbcbfnmbkopoojfekhnkhdbieeh.
Firefox:
Open about:addons page.
Click on each extension’s tile.
At the bottom click reviews and remove reviews/ from the URL.
Genuine Dark Reader has 447,538 users at the moment of writing.
I think that main separation of extension should be based on their communication with outer sources.
E.g. it’s not fair that extension which inserts script in every page for zooming or something like that, is treated the same way as some potentially malicious extension that also inserts scripts into every page but with communication logic to third party services.
Both of those extensions are presented to users as:
“Read and change all your data on websites you visit”.
While firs is simple tool, other (potentially) collects data or whatever
Yup, “Read and change all your data on websites you visit†doesn’t help much with learning about privacy concerns.
There’s also “Read your browsing history”, “Change your privacy-related settings”, and more, all of which may be used in ways we don’t like.
And even if it just says “This extension requires no special permissions”, does that mean it’s legit?
That said, regardless of the permissions, it’s always best to read the Privacy Statement from the dev, if there is one, and if there isn’t, then perhaps you should avoid those extensions.
Yea, that helps (a little) with companies that collects data and do legal business in general
but… potential hacker or deceiver can put anything in privacy statement, like “we don’t resell your private data”
Same goes for GitHub repo
who guaranties that extension code is the same as presented on GitHub?
One thing I do, besides the obvious things, is track down the dev, to see if they look trustworthy, as with having a personal tech blog and/or site that goes back several years, where they actually provide a link to the extension at the given browser store.
I’ll even use the Wayback Machine to dig back further, to see what they were up to in the past, as with Martin and gHacks. Ah ha!.. But I digress.
Other than that, I may go as far as to contact the dev, and pish for anything fishy.
Also, I will check their software claims, and if it’s mostly BS hype, then I move on.
“This extension contains malware”
Shouldn’t all of MS’s Security Bloatware have detected that on download or unpacking? Downloading on Chrome/Chredge is an onerous process, is it all for show? Does ANYthing MS produce work correctly?
I guess MS is relying on developers to provide malware definitions while they dream up new ways to hobble Windows.
@ULBoom
Good guess, but if you’re smart, there’s much more to speculate about.
For example, perhaps this was a new type of exploit that can’t be simply detected by security software?
Or perhaps this was not an exploit at all, where the dev of Dark Reader reported it as such because is was a copycat extension, and thus Microsoft went along with it, such as with their rather silly malware warnings they give in Edge based on their limited “file reputation” data.
Or perhaps that image here is fake, provided to Martin by the dev of Dark Reader, and Microsoft actually removed the copycat extension for other reasons.
Or perhaps, gHacks was hacked, and this whole report is fake. But I digress.
Personally, I don’t know, nor do I care to research this proper, as I don’t work for gHacks or the like.
The bottom line is, unless you’re a fool, you can’t trust any software much.
Personally, I’m a lazy fool, but I’m also very lucky, thus I have nothing to worry about with no fuss.
Why should anyone vet extensions? If these extensions are available to download, surely the onus is on the respective distribution store and not in the interest of the end-user to vet.
what if:
there was a pre-upload store (isolation) where vetting/testing prior to store upload with a fast-track for those who have a solid reliable track history/record…
@MF
> surely the onus is on the respective distribution store and not in the interest of the end-user to vet.
That’s sounds logical, but as it is with most any other store, the distributor often takes the least responsibility with what the law permits. What they are clearly responsible for, is to remove harmful products from their store, at least after they learn such products are indeed harmful. And if a product may be a risk of doing harm, then they may just post warnings.. Thus, the legal onus is not so much on the respective distribution store, and it is in the interest of the end-user to vet what they consume, regardless.. Furthermore, the legal onus is mainly on the producer/owner of the product.
Other than the law, companies can make and enforce their own policies, so perhaps we need more of that, as you suggested.
That said, understand that stores/distributors want to keep both their suppliers and customers happy, as both can make trouble for them. As such, things are not as simple as they may seem, as with Risk Management, PR, contracts, and so on.
As it is, folks like Google have much data to know how far they can push such risks on consumers, and although they will likely do more to make things safer at some level, there’s likely always going to be risks.
I minimize extension threat (using Chrome) by limiting my use of them. I currently run 7 extensions.
Sincerely, I want to know what do understand Microsoft as “malicious”. For me, Windows Update is some kind of maliciuos thing twice per month. For me, a 24 years old unsolved bug is quite malicious imho in certain way. It sounds like a joke, really, a bug with more years than me. :[
https://www.tellerreport.com/tech/2020-05-16-update-your-computer–microsoft-fixes-a-windows-bug-after-more-than-24-years.SJ4J1-hnc8.html