Internet Explorer security update KB4483187 released
Microsoft released a security update for Internet Explorer on December 19, 2018 that patches a security issue in the scripting engine.
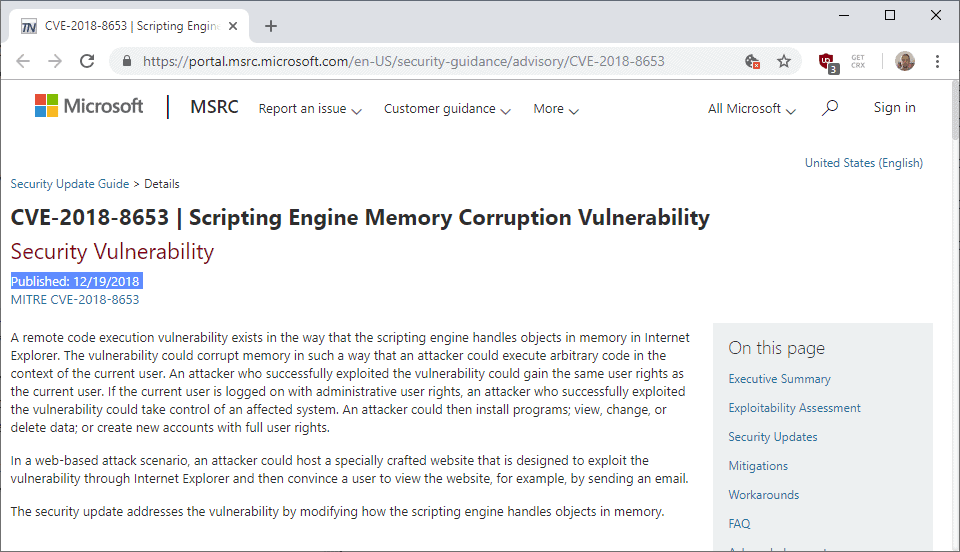
Microsoft describes the issue in the following way:
A remote code execution vulnerability exists in the way that the scripting engine handles objects in memory in Internet Explorer.
The issue is filed under CVE-2018-8653. The Security Advisory page for CVE-2018-8653 offers additional details. The vulnerability could be used by attackers to execute arbitrary code in the user context if exploited successfully.
If a user has administrative rights, the attacker would get these rights as well; this would allow the attacker to install and run software, and modify system settings among other things.
It appears, from the description, that it is enough to open a specifically prepared website in Internet Explorer to get infected.Woody thinks so, too.
The security issue affects Internet Explorer 11, 10 and 9 on all supported client and server versions of Windows. In particular, it fixes the issue on devices running Windows 7, Windows 8.1 and Windows 10, and Windows Server 2008 and 2012, Windows Server 2012 R2, Windows Server 2016, and Windows Server 2019.
The update is available as a cumulative update for Internet Explorer and Windows. Microsoft enabled the update on Windows Update already but it can also be downloaded from the Microsoft Update Catalog website.
Microsoft Update Catalog website link:
- Windows 7, 8.1, Windows Server 2008 und 2008 R2, Windows Server 2012, 2012 R2, and Windows Embedded: KB4483187
- Windows 10 version 1793: KB4483230
- Windows 10 version 1803: KB4483234
- Windows 10 version 1809: KB4483235
Note that it is not recommended to run a "check for updates" on Windows Update as it may deliver updates that you don't want installed on the device; this may be a new feature update for Windows 10.
The cumulative Internet Explorer security update has a known issue that affects devices running Windows 8.1 or Windows Server 2012 R2. The "About Internet Explorer 11" dialog box shows KB4470199 from December 11, 2018 and not the new update.
Microsoft notes that users may confirm that the system is patched by checking that jscript.dll has the version 5.8.9600.19230. The file is located under C:\Windows\System32\jscript.dll














Thanks for your article, due to your info I have decided to hide this update as it is causing a strange issue with the power management options on one of my machines, specifically the minimum and maximum processor state settings.
I have an old Dell Optiplex 780 running Win7 Pro 64bit which I purposefully run at reduced power settings, ie. both the min and max processor power set to 1%, keeping the processor locked at it’s minimum Hz.
After I installed the latest Windows 7 updates a few days ago (Boxing day, 2018) I noticed my fan CPU fan was ramping up and down. I then realized that the CPU was boosting up to it’s maximum Hz.
When I checked the processor power state settings I noticed they had vanished! The only option left was the system cooling policy.
After a number of google searches I could only find suggestions that Hyper-V and/or the virtualisation settings in BIOS can/will disable these power options, but I had no Hyper-V installed and my BIOS virtualization settings were off. The only thing I had done to the machine recently was to install this Windows update.
The only way I could get my processor power state settings back was to do the following:
Uninstall this update, allow the machine to reboot and log back into windows.
Reboot the machine and go into BIOS and turn ON the virtualization settings, then boot into windows.
Next, reboot the machine again and go back into BIOS and turn OFF the virtualization options and boot back into windows.
After these steps the processor power states were available and interestingly enough my old settings were remembered and the CPU was again locked at minimum Hz.
I hope this info helps anyone else with this weird issue, though if it only affects old Dell machines running Win7, then it’s probably not going to be a common issue!
“Microsoft notes that users may confirm that the system is patched by checking that jscript.dll has the version 5.8.9600.19230. The file is located under C:\Windows\System32\jscript.dll”
Is this aforementioned version specific to KB4483187?, because I am running Win 10 1809 and I got this update on December 19, 2018 as KB4483235. My version for jscript.dll is totally different: 5.812…….16384
Just want to make sure that I am updated since I also use IE11 from time to time.
security isn’t an issue, it’s an actual problem or concern. Dumb euphemisms don’t help,
What is Internet Explorer ?
A browser for those stuck in Windows 98.
If someone does not have IE in the system anymore this patch is not needed, right?
I have removed IE from my Windows 7 more than 8 years ago.
From time to time the opening of a site can only happen in IE (as a result or not of the installation of a program).
That’s the only reason I kept it … Thank you for info Martin.
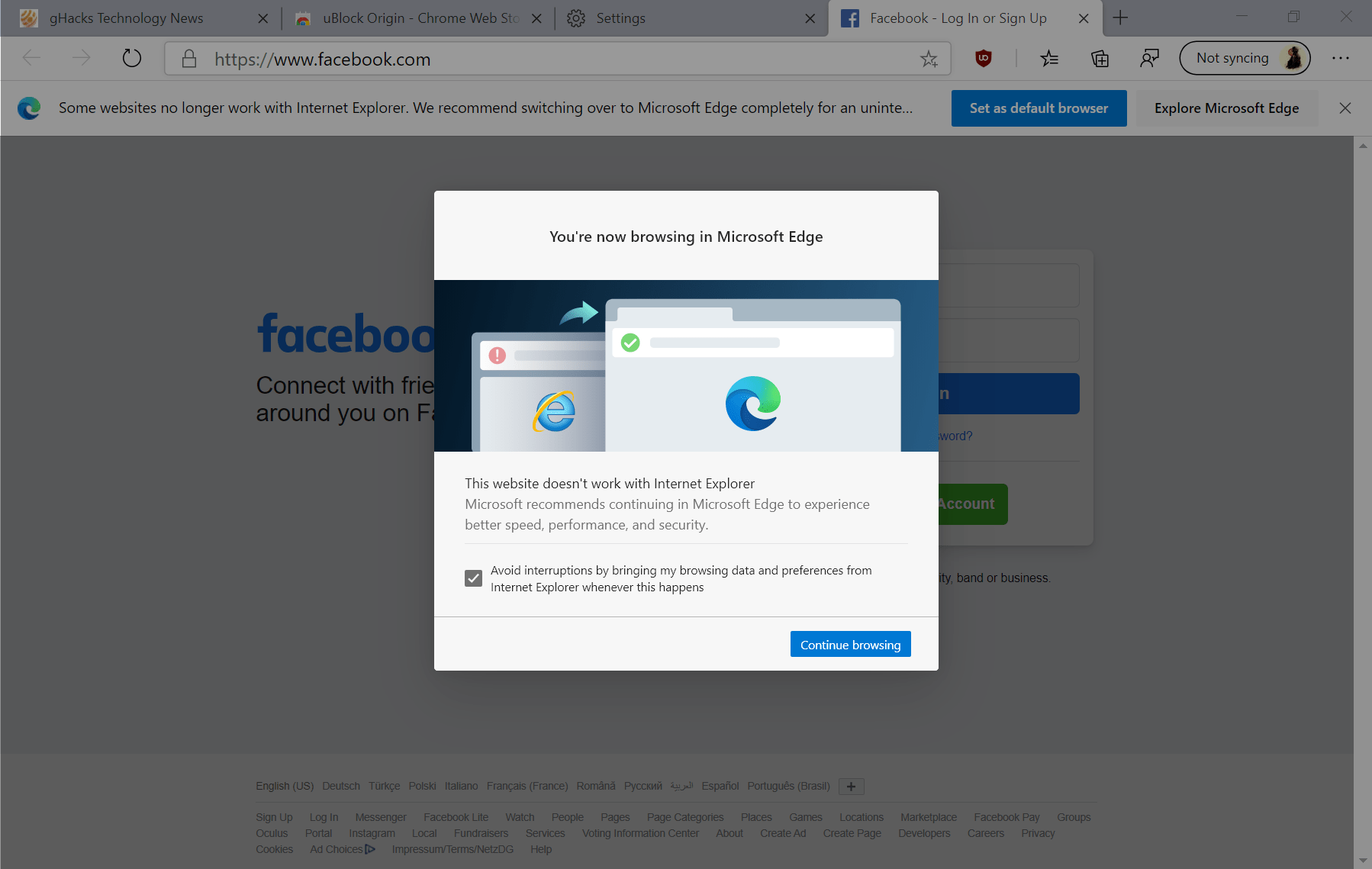
It seems a little odd to see Internet Explorer sticking around several years after Windows released a new version of their operating system, 10, with a new Microsoft browser, Edge. Its been years since IE has even been Microsoft’s default browser on default installs of its most recent operating system release.
IE isn’t available crossplatform for Android or iOS either, in an era where that is close to mandatory to be a serious competitor (Even some of the small under 1% marketshare browsers like Vivaldi and Waterfox have mobile browsers in the alpha or beta stages).
Does IE even get active development anymore apart from the occasional security patch? Is it tested against by web developers and compatible with the modern web? Is it a useable browser for general web use here in 2018 as we move towards 2019?
If Edge was having enough compatibility and cost issues associated with its use of a relatively modern EdgeHTML engine to the point where its switching to Google’s Blink engine, I can only imagine how bad cost and compatibility are for IE’s Trident engine at this point. And with the EdgeHTML engine biting the dust, the cost expeditures on Trident aren’t even going to be mitigated by the idea that some portion of the work on Trident and IE benefits or is benefiting from Edge. Now the whole IE/Trident thing is going to an independent budget expediture that neither helps make Edge less expensive to maintain or costs less to maintain because it benefits from Edge. The rendering engines for the two are now going to be totally different animals.
On the consumer side, people rarely even use a Microsoft browser on Windows anymore period, so its not as though they really have the numbers to justify a both regular and a legacy browser anymore. And Edge is going to be available on prior versions of Windows shortly.
IE lost the browser wars a long time ago. Few people have a sentimental attachment to it. It doesn’t really represent anything a consumer might want in terms of user choice either.
Really, it seems like the choice of users who don’t understand that they have a choice and think it is “the Internet” and businesses that want to run old intranet programs from their services for office use that rely on ActiveX. And I wonder if both sets of users would overall be better off if it was just deprecated and replaced. It mainly just compromises their security and enables botnets that compromisr the rest of our security.
We do need more diversity in browsing rendering engines, and more choice in terms of how browsers do things in general, but Internet Explorer doesn’t represent those things.
Does it just persist until the end of time? This was a contemporary of Netscape Navigator that predated Mozilla Firefox, Google Chrome, and Apple Safari. Its probably the oldest maintained browser around- and probably maintained only very loosely. If it was still the default Windows browser and was being developed in an attempt to compete with other browsers, that wouldn’t be a negative, but since its not, it seems like the equivalent of using AOL to access the Internet a couple decades after all their keyword non-WWW sites, chat rooms, and message forums are gone, and the lights have been turned out.
The importance of patching this problem is emphasized in this article, which blasts and/or confirms how the problem can manifest itself.
https://www.kb.cert.org/vuls/id/573168/
Thanks for the information, Martin. I wondered where it was in the last Patch Tuesday update batch.
> Products
> Windows XP Embedded
Neat!