Your NoIP.com powered site is not reachable? Here is why
When you run a remote service on your home computer, one of the things that you need to take into account is a changing IP address. The issue here is that if your IP address changes, you and everyone else connecting to that service needs to use it.
Since many home Internet connections get dynamic IP addresses regularly, it means that you have to communicate those changes to everyone so that your service remains accessible.
One way around this is to use a dynamic DNS service which assigns a static domain name to the hostname which can be used to access the service regardless of IP address.
One of No-IP.com's services is dynamic DNS. It is not the only service the company offers, you can register domain names and get mail access as well among other things, but it is probably its core product.
If you are making use of the service, you may have noticed that it is not working properly or at all anymore for a couple of days.
The reason why is explained in a company blog post. Microsoft has apparently seized several commonly used domains of the service on June 30.
Malware writers and spreaders used the system like this: their malware infects user computer systems which contact NO-IP subdomains that point to the control center so that these systems can be controlled over the Internet.
According to Microsoft, these domains have been used to spread malware and the company is filtering out the bad from the good so that legitimate hostnames should not be affected by it at all.
No-IP on the other hand claims that this is not the case and that "millions of innocent users are experiencing outages" because Microsoft's infrastructure cannot handle that many customer queries.
If your site or service is down or slow currently, that is why. Neither Microsoft nor No-IP have revealed which domains are affected.
One question that arises out of this is why Microsoft went this road. According to No-IP, the company has a strict abuse policy and would have taken immediate action if Microsoft would have contacted the service first.
The two malware campaigns Bladabindi and Jenxcus were targeted specifically by Microsoft. By taking control of the domains, Microsoft controls all requests made to them so that it can stop any trying to contact the control center or commands from the it to the infected systems.
Our research revealed that out of all Dynamic DNS providers, No-IP domains are used 93 percent of the time for Bladabindi-Jenxcus infections, which are the most prevalent among the 245 different types of malware currently exploiting No-IP domains. Microsoft has seen more than 7.4 million Bladabindi-Jenxcus detections over the past 12 months, which doesn’t account for detections by other anti-virus providers.
Find out if your domain is affected
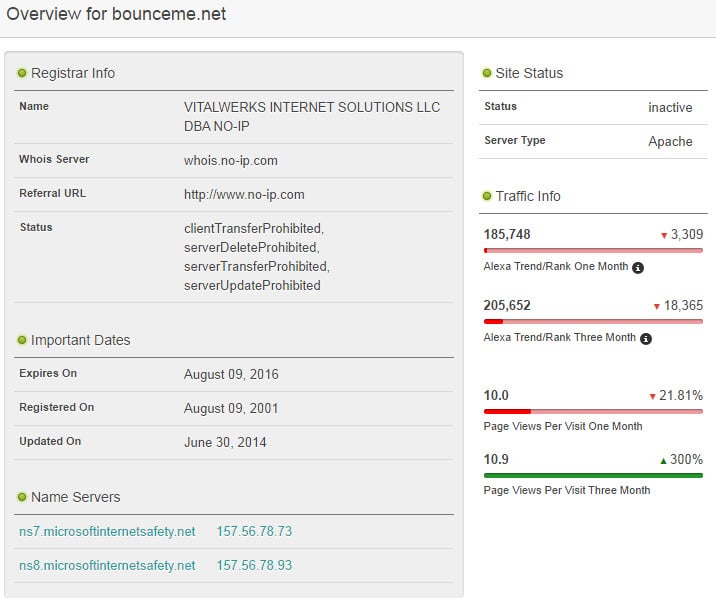
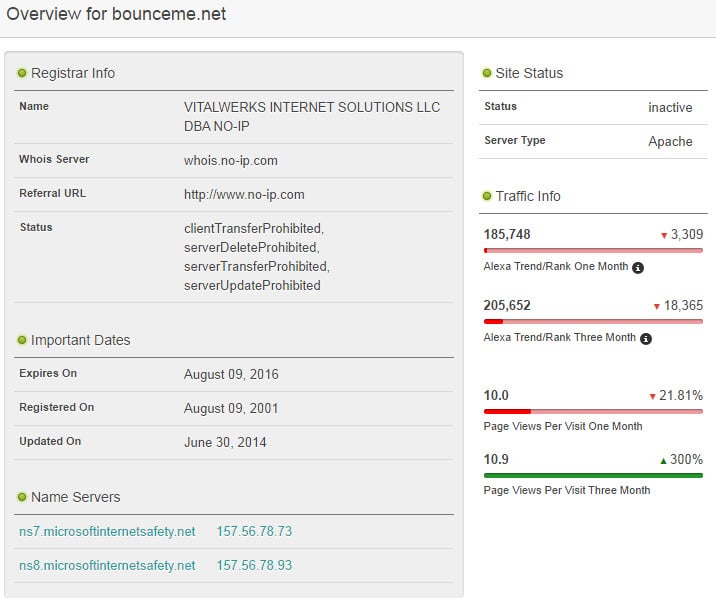
The easiest way to find out if your domain is infected is by looking up its nameservers. You can do so by visiting who.is. It displays the name servers and if they show microsoftinternetsafety.net, they have been seized.
Some domains that are affected by this include
- bounceme.net
- myftp.biz
- no-ip.biz
- no-ip.info
- myvnc.com
- serveblog.net
- redirectme.net
- servehttp.com
- systes.net
What can you do?
It is not clear how this will evolve. While you may be able to switch to different domain names offered by No-IP, you may want to consider moving to a different provider instead. Here is a short list of free dynamic DNS providers:
- http://www.dnsdynamic.org/
- http://www.changeip.com/
- http://freedns.afraid.org/
- http://www.zonomi.com/
What's your take on the this? Was Microsoft right in seizing the domains (temporarily)?

















Protip: Try DuckDNS.org
I recently needed DDNS for a project and decided to look around for a new provider. Signup is easy, and setup is easy too. They use Twitter, Facebook, Reddit, or Google as signup options. The idea I assume, is to help weed out spammer/bot people, as they have to set up new accounts with those services, and they generally are strict themselves about verifying new accounts for their own services.
No.IP needs to sue the hell out of Microsoft.
Total abuse of power.
Lovely! Just paid for the service last week.
I also have a paid subscription to their DDNS services. It was unaffected because it was not in a targeted domain. Don’t worry. At worst, pick a different domain. They have a large number to choose from. I suspect Microsoft had issues with the free domains only. No-ip is one of the few DDNS provider that still offers a free public DDNS service. Asus offers one but it is limited to users of a few Asus products.
“Don’t worry. At worst, pick a different domain.”
I realize that, but the site wasn’t available at all for me till this morning. Changed to one of their suggested domains – still not working for me – I will give it some time.
Absolutely Rodalpho! Microsoft has everyone’s best interests at heart. And what does it matter if a few small people are slightly inconvenienced? I mean the fact that I use NO-IP to access my home security cameras to watch over my house and dog is of little consequence to me or my wife. I would much rather ‘Big Uncle’ come and use his pimp hand to take care of the spammers and malware issuers than have incompetent NO-IP personnel fix their own problems.
Too bad the rest of us can’t have the DOJ, NSA, and any of the other alphabet-soup government group do our bidding when we tell them to jump.
Keep on truckin’ Microsoft.
Of course they were in the right!
Similarly, I’m going to petition the courts to assign the rights to HOTMAIL.COM to me, as that host is widely known to distribute spam email.
What’s that you say? It has millions of legitimate users, and the spammers keep popping up like cockroaches, incredibly difficult to block permanently? Screw ’em.
Right?