Unseen, a 4096-bits encryption communication service from Iceland
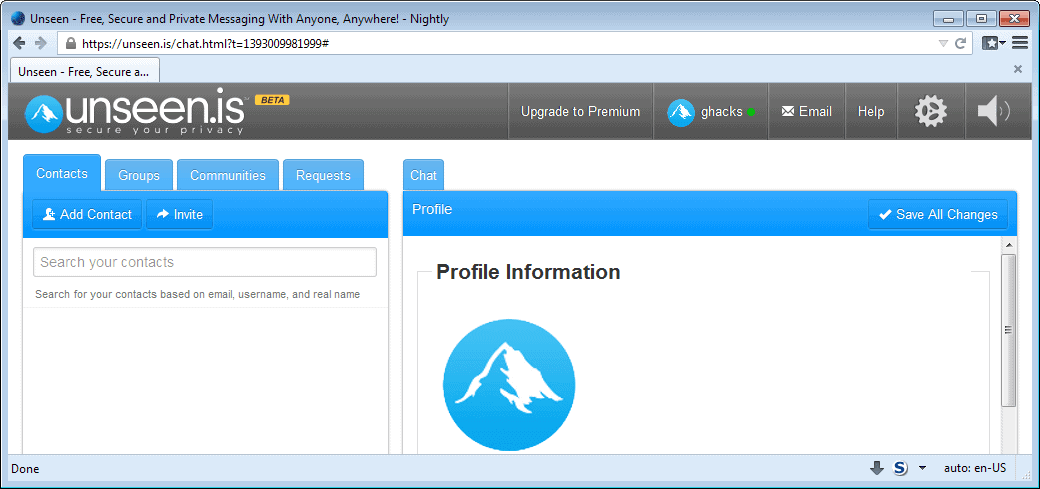
Quite a few companies and individuals aim to improve communication security. Unseen.is is third service that I have reviewed in the past 24 hour period that promises to improve user communication security and privacy (the other two are ShazzleMail and Telegram).
Unlike the two services, Unseen is a complete communication product that combines email, audio and video calling, and chat in a single service.
It needs to be noted -- again -- that Unseen has not been audited by third-parties, and that you should keep that in mind while reading the review.
So what is Unseen? Unseen is a communication service that is available as a free and pro version. The free version supports the majority of features that the service has to offer with two notable exceptions.
Both versions of the service share the same strong 4096 bit encryption that it uses to protect communication. One difference though is that premium users can generate and store their own private keys, while free users cannot.
The second difference is that only premium users can make use of secure and encrypted email, while free users can only use email regularly.
Premium users on top of that gain group calling options and 2 Gigabytes of storage instead of the 25 Megabytes that free users get. 25 Megabytes is not much, and it is not clear if that is all the storage that users get to store emails on the servers.
File transfers, the service supports those, can be larger than those though. According to the company website, premium users can transfer files up to 40 Gigabytes in size.
Unseen is currently only available as a web-based version, but versions for Windows, Mac and Linux systems as well as Android and iPhone are in development. All of the applications and programs will be free of charge.
Encryption details
All messages that are transferred using Unseen are encrypted and decrypted by users of the service, not by Unseen. According to the FAQ page of the service, it does not have access to the key.
Messages are encrypted using 4096-bit encryption and "advanced symmetrical encryption".
Little is know about the type of encryption that Unseen uses, other than that it "proprietary encryption based on open source standards" such as xAES and NTRU.
Issues
Unseen does not reveal much about the technology that it is using to protect and secure the system. While that does not necessarily have to be a bad thing, at least some users may prefer if developers are open about what is being used so that they can audit the service or at least evaluate the claims that are being made.
The major challenge for Unseen is that it only works properly if both sender and recipient are using it. While you can use services such as chat or video calls only if both users have an Unseen account, the same cannot be said for email.
If you want secure email and sign up for a premium account, you need to convince your contacts to sign up and do the same.
You can still send emails to unprotected email addresses, but that means that the information are not fully secure.
One thing that I could not figure out how to do was how the "control your private key" feature worked for free users. I could not find any information about the private key after logging in to the service.
Closing Words
Unseen offers more communication forms than popular solutions such as Skype. While some are missing, such as SMS, it is not really necessary as soon as the mobile and desktop clients get released by the service's parent company.
If you can convince your contacts to make the switch -- the free account is sufficient if you only want to chat -- then this may be worth taking a look at.
The premium service for now is offered for $49 for a lifetime license, a fair price.
Advertisement


















Nov 28, 2018
Greetings,
About a week ago, Unseen suffered a hardware failure in the Thor data center in Iceland. Four hard drives in a RAID failed. The drives have been replaced and rebuilt and of 8 hypervisors that run the email system, 1 of these failed to restart. We tried restoring from a recent backup, but the back up was corrupted. We are still working to restore the data from the drives, but it’s possible that data is lost. Having four drives fail at once is highly unusual.
Who is affected? Only email is affected, chat is not affected. About 1/8th of our Unseen user’s email is affected, 7/8th of our users have had no effect and see normal service. If you have not been able to access your Unseen email, you might be affected. If you used POP3 or IMAP (which most users do), you already have a complete backup of all your email. If you used web mail only to access your Unseen, if you don’t have a backup, it’s possible your data is lost, though we are going to try to recover it if the drives do not have physical damage. Unseen was designed to be a secure communications system, not a cloud data storage service; please keep your own backup always.
If your account was affected, you will need to send an email to:
adminreport@unseen.is
Let the devs know which account(s) you have that are affected and we can restart them so you can begin using your Unseen account. Please tell them both the Unseen.is account name and the recovery email (as a security check).
We’re very sorry for this outage, and apologize to everyone for the inconvenience or any loss of data.
We are now at a crossroads. Email and other centralized communications are easily disrupted. Privacy is not the biggest concern, rather censorship or disruption or interference with communications is becoming a huge issue. The centralized model along with services like email are dying.
Other non-Unseen services operated by our team members have also been targeted, experiencing disruption of advertising revenue, loss of bank accounts (for no good reason), hassling of employees or contractors and so on. For these reasons, we think the only future for a service like Unseen will be using a non-centralized Peer to Peer (P2P) communications system and business model. Over time the centralized services will be completely phased out, including the current centralized chat and email. Everything will become P2P though we don’t know exactly when the new services will be perfected. We will work towards a seamless transfer.
This means the company Unseen, ehf will be shut down and everything will move to a pure opensource and distributed model, similar to how bitcoin operates. Payments will be done between users on the network using crypto only, as the project will not have any centralized team or bank accounts, it will have only peers/nodes. FLASHcoin.io will be the primary payment medium. Premium Unseen users will get special features and some FLASH to use on the network. It will also be possible for individuals or businesses to provide services on the network and charge a fee. If you paid for premium in the past six months and no longer wish to use P2P continue, we can arrange a refund if that’s what you want. You are free to test out the new system and opt out if you don’t like it.
The first version of Unseen P2P will be based on RetroShare’s network technology and it should be available for testing within two weeks. We will send a message to everyone letting them know the specifics. The initial features will be chat and group chat, a contact manager, a type of P2P email for inside the network, file storage, channels and fora (forums for you Americans), and shortly after the initial version is released, we will build a way for Unseen users to migrate all their Unseen contacts over.
We think this is the best and most responsible way to protect our Unseen users and help them move to a bright future.
Best,
The Unseen Team
The international Academic R&D PQCrypto project states:
“information encrypted today using RSA or elliptic curves and stored until quantum computers are available will then be as easy to decipher as Enigma-encrypted messages are today”
http://cordis.europa.eu/project/rcn/194347_en.html
And they work on “post-quantum” encryption to REPLACE the current standards. NTRU (public key crypto) is not on their list of directions to explore – nor xAES is.
Thanks for the review
So is it safe to use or no?
Thanks
http://www.budgetcamerareview.com/forum/discussion/723/100-confirmation-that-unseen-is-is-not-private-or-secure-/p1
Unseen is a trap and always has been.
Wake-up., stop spreading bad info.
Look up Chris Kitze and others, like I said, Unseen is corrupt.
Don Ron
Got news for you. People did land on the moon.
@Maelish,
Nice,
You have a responsibility to focus attention on corrupted email services and you respond with this garbage, and in a time when reliable mechanisms for communication are fading rapidly.
Try doing your homework. The fact is that Unseen is corrupted and is completely unreliable unless you are sending your uncle pictures of the family cat.
How’s that for a moonshot.
Don Ron
Has anyone done a hard technical review of Unseen or its brethren? Between this, wickr and textsecure. I’d like something solid that I can use on my pc and my phones.
I created my own offline encryption messaging service called Invisocial using off the shelf open source code.
I think UnSeen offers a slick encrypted messaging service… chat and more.
Actually, the German word for ‘island’ is: ‘Insel’…
Oy. Now I wish I hadn’t even mentioned it.
__________________________________
Gregg L. DesElms
Napa, California USA
gregg at greggdeselms dot com
Veritas nihil veretur nisi abscondi.
Veritas nimium altercando amittitur.
Really like all your comments in the ghacks blog, Gregg.
btw:
I believe “Island” is the German term for “Iceland”,
Martin/GHacks being German,
he must have overlooked it…
Knowing Martin,
I am sure he’ll chime in soon. :-)
SFER WROTE: I believe “Island” is the German term for “Iceland”, Martin/GHacks being German, he must have overlooked it.
MY RESPONSE: Ahhhh… I see. So then maybe it’s a thing where one is typing in one language, and the word that one meant to type in the language being typed-in ends-up on the page in the other language. Understandable mistake.
My wife’s Filipino; they speak Tagalog. When they mix-up Tagalog and English words, they call it “Taglish.” So maybe this is… wait… what would it be? “Englerman”? Or… wait… “Germanish.”
Ha! I love combining words. Sometimes if you do it fast, and don’t think it through first, you end-up blurting-out either words that actually are already words, or interesting profanity. Or what amounts to a phrase…
…that’s even MORE interesting if it’s also profane. Just don’t do it in front of your mom.
__________________________________
Gregg L. DesElms
Napa, California USA
gregg at greggdeselms dot com
Veritas nihil veretur nisi abscondi.
Veritas nimium altercando amittitur.
It happens at times without me realizing it. Usually, when the two words spell and sound similar.
Right, Iceland it is, not Island. Corrected the mistake.
THE HEADLINE: Unseen, a 4096-bits encryption communication service from Island
MY RESPONSE: Umm… wait… on its website, it says “from Iceland.” I’ll bet Martin got in a hurry, or was thinking about content and not keystrokes while typing and wrote “island” instead of “Iceland.” I do that sort of thing all the time. Either that, or it’s a spell-check victim.
In any case, I don’t remember reading anywhere that Iceland was particularly well-fortified. I’m pretty sure that a troop of Girl Scouts could breach it…
…and, actually, if memory serves, I think some already have.
Just sayin’ (and kiddin’). [grin]
My point, really, is that I don’t see why it would make any difference — or be of particular benefit — that it’s hosted in Iceland versus pretty much anywhere else. That was really my point.
__________________________________
Gregg L. DesElms
Napa, California USA
gregg at greggdeselms dot com
Veritas nihil veretur nisi abscondi.
Veritas nimium altercando amittitur.
“Nebulus” wrote that “if you have someone listening to your CPU, you are in big trouble already,” suggesting, I’m guessing, that if someone’s listening to your CPU, then he’s probably gotten into your house to plant a listening device or something; and that would, indeed, mean that you have a bigger problem. However, if you read the various articles about what the 4096-bit-encryption crackers did, you’ll see that it can be accomplished just using a smartphone that’s sitting on the table next to the one at which you’re sitting with your laptop that’s decrypting something at a coffee shop.
“Nebulus” also correctly wrote that what they did is a side-channel attack, and not an actual decryption cracking; but the bottom line is the same: they can get your key and so see your stuff. Six of one is a half dozen of the other, and all that.
Reading this article…
http://www.extremetech.com/extreme/173108-researchers-crack-the-worlds-toughest-encryption-by-listening-to-the-tiny-sounds-made-by-your-computers-cpu
…and the others…
http://bit.ly/MNXpH7
…about how the researchers cracked 4096-bit security purely acoustically, it occurs to me that how to end-run the problem of devices listening to one’s CPU as one decrypts things could be to simply play a recording of the exact same sounds that the CPU makes — only one that’s all jumbled-up and means nothing — through the computer’s speakers, at a very low volume that would confuse the listening devices about whether the sound’s coming from the CPU or the speakes. Of course, if it’s a recording that everyone starts using, then the listeners could simply write a filter which detects and ignores it, and still culls the real decryption sounds from the environment in spite of it. And so then, any such through-the-speakers method would have to involve an algorithm that jumbles-up the sounds randomly.
If the sounds are outside the typically 20 to 20,000 Hz range of normal speakers, then it would be a no-brainer to write an Android app that just sits there and decrypts nonsensical things, and then run it in a cheap box like this…
http://amzn.to/MNYP4y
…(which is made for use with TVs, but it doesn’t matter, it’s a computer with a CPU, and that’s all we’re looking for (and they’re out there for about half that price, if you look hard enough)) that’s just sitting there, next to the computer that’s actually doing the real decrypting. In fact, one could theoretically run such an app on one’s smartphone that’s sitting next to one’s laptop or desktop computer whenever one decrypts anything using said laptop or desktop. It would be ideal if there were an Android app that could do it on smartphones: that way, one’s device that will obfuscate the CPU sounds of his/her laptop or desktop while decrypting can be right in one’s pocket at all times.
Or, who knows: maybe this is a business opportunity niche. Perhaps someone needs to develop a simple circuit board device and put it into a tiny box, with a simple on/off switch; and have it either run off batteries, or, better yet, the USB port of any computer (since it will pretty much always be sitting alongside a computer whenever used) which emits the full range of sounds via a variety of different chip types that mimics the sounds that pretty much any CPU would make whenever it’s decrypting anything (only with said sounds being completely random so that they neither mimic actual decryption codes, nor exhibit any pattern which may be discerned and then filtered/ignored by acoustic listening systems) to obfuscate the sounds of the real computer’s real decryption.
The articles talk about how simple is the method, but the thing with simple methods is that it usually takes only simple solutions to defeat them.
__________________________________
Gregg L. DesElms
Napa, California USA
gregg at greggdeselms dot com
Veritas nihil veretur nisi abscondi.
Veritas nimium altercando amittitur.
I wonder if anyone using Unseen will need to
worry about 4096 being “cracked”.
Researchers, Daniel Genkin, one of the inventors of RSA, Eran Tromer and Adi Shamir cracked the 4096-bit by using a simple microphone to listen into CPU sounds – and through this decrypting data.
Source: Internet researchers crack RSA 4096-bit encryption | The Stringer
The algorithm itself was not cracked. This is what is called a side channel attack. If you have someone listening to your CPU, you are in big trouble already :)
Pointless now that 4096 bit encryption has been cracked.
Stupid. Likely disinfo to deceive. 4096 nor 3072 nor 2048 have been “cracked”. Nonsense. Show me the data somewhere, anywhere dealing with “cracking” huge primes in iterations.
And I suppose you have some proof of that? Otherwise you should stop spreading FUD…