How to override the Firefox Add-on Signing requirement
The following guide walks you through the steps of overriding the add-on signing enforcement in Firefox Stable and Beta. You will be able to install unsigned add-ons in Firefox versions in which this should not be possible.
Mozilla implemented the add-on signing security feature in Firefox some time ago, and made it mandatory in Firefox 48 for the Stable and Beta channel.
This means that Firefox users who run Stable or Beta versions of the browser can only install signed add-ons in the browser. Firefox Dev, Nightly and ESR users can install unsigned add-ons however after making a change in the preferences.
Add-on developers get access to unbranded Firefox builds which are stable versions of Firefox that still support the preference.
All add-ons submitted to Mozilla's main add-on repository are signed, but that is not necessarily the case for add-ons distributed through other channels.
Add-ons provided by applications, security software comes to mind, on development platforms like Github, and old add-ons that are not in development anymore, may not be signed. These add-ons cannot be installed in Firefox Stable or Beta in that case.
Update: The method does not seem to work anymore. You need to install and use Firefox ESR to disable add-on signing in the Firefox web browser (if you don't want to use Firefox Dev or Nightly builds).
All that is required in Firefox ESR is to set the preference xpinstall.signatures.required to False on about:config.
Override the Firefox Add-on Signing enforcement
The method requires that you create two new files and place them in the main Firefox installation / run folder.
Step 1: Create config.js file
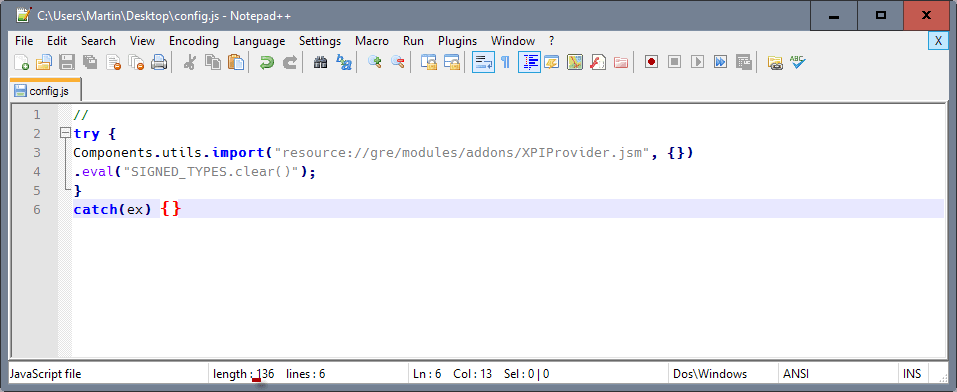
- Create a config.js file first. You can do so on Windows by right-clicking on the desktop and selecting New > Text Document.
- Leave the name for the time being, and open the text document afterwards by double-clicking on it.
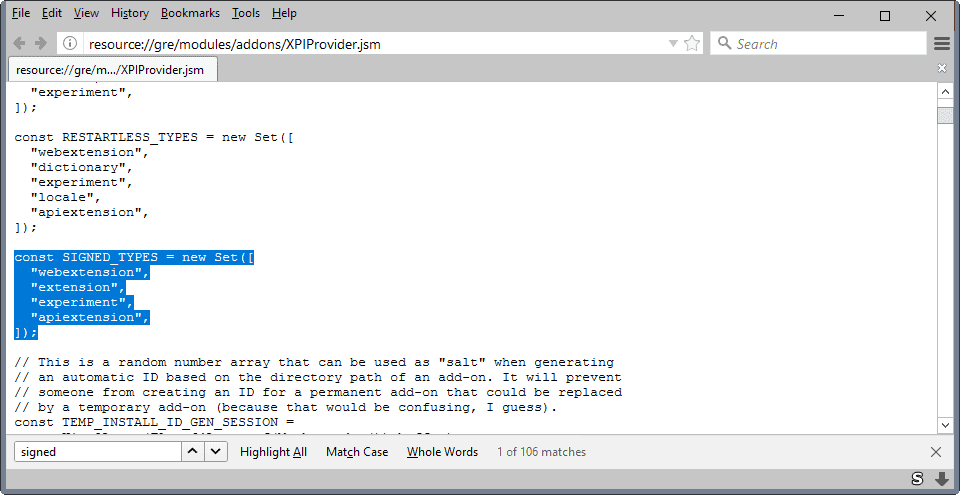
- Paste the following code into the document. Make sure you copy all of it, including the two // in the first line (See screenshot above).
//
try {
Components.utils.import("resource://gre/modules/addons/XPIProvider.jsm", {})
.eval("SIGNED_TYPES.clear()");
}
catch(ex) {}
- Save the document afterwards.
- Right-click on it, and select rename.
- Name it config.js. Make sure it is called config.js and not config.js.txt.
- Move the config.js file in the Firefox installation folder.
- On Windows, this is either C:\Program Files\Mozilla Firefox\ or C:\Program Files (x86)\Mozilla Firefox\.
- On Linux, it is /usr/lib/firefox-<version> or /usr/lib64/firefox-<version>
- On Mac, it is /Applications/Firefox.app
Please note that you are free to select any installation directory, and that you may run Firefox as a portable program as well. Adjust the program path accordingly. Make sure you place the file in the root program folder of Firefox.
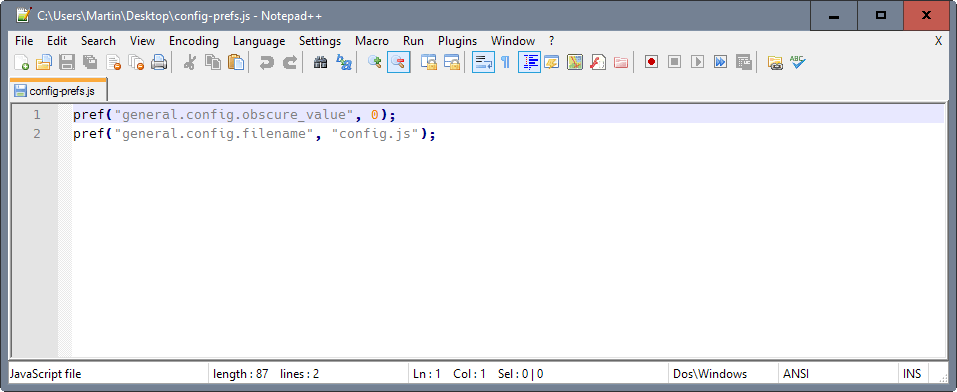
Step 2:Â Create config-prefs.js
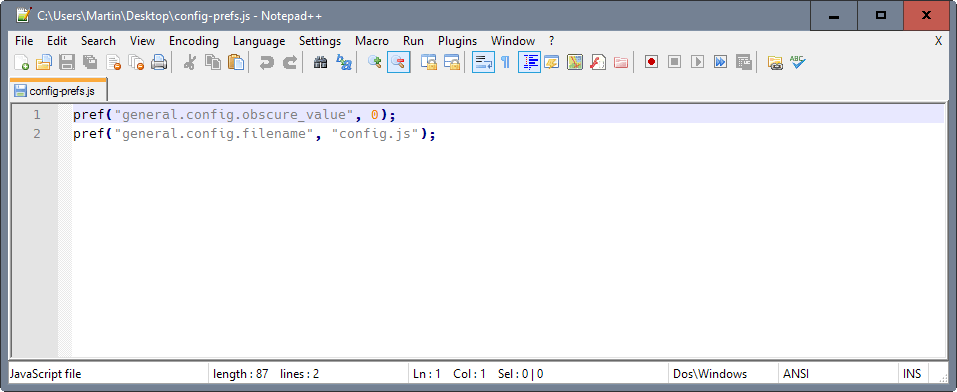
- Create a second text document on the desktop and open it afterwards in an editor.
- Paste the following lines into it:
pref("general.config.obscure_value", 0);
pref("general.config.filename", "config.js");
- Rename the file to config-prefs.js.
- Move the file into the defaults\pref folder of the Firefox program folder, e.g. C:\Program Files\Mozilla Firefox\defaults\pref
Restart Firefox.
Step 3: Install unsigned add-ons in Firefox Stable or Beta.
Once done, you may once again install any add-on, signed or unsigned, in Firefox Stable or Beta just like before.
What happens in the background
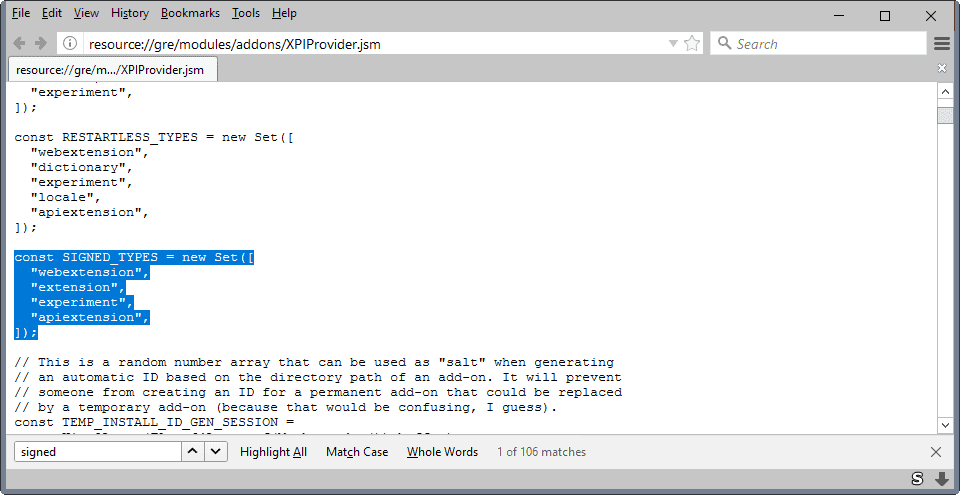
You are probably wondering what the few lines of code do, and whether it is save or dangerous.
Without going into too many details, here is what is happening:
The first bits of code, those added to the config.js file, load one of Firefox's configuration files and remove information from the Signed_Types constant in that file. It so happens that this constant defines the types of add-ons and extensions that need to be signed for be installed.
You may remember that some extensions, themes for instance, don't need to be signed. So, the code clears the constant from all types of add-ons so that none requires signing.
The preferences in the second file tell Firefox to load the config.js file on start.
Closing Words
The method removes the add-on signing enforcement in Firefox. It is rather surprising that it is this easy, considering that one of the main arguments for enforcing add-on signing is security.
Thanks to Howard and Michel who notified me about the trick.





















Question: does this workaround STILL work with firefox version 99 (stable release channel), or have mozilla patched this workaround and prevented anything like this from working ever again?
Update, Feb 2021
@Steven re.: “…rolled my browser back to FF51.0.1…”
Did not work for me, 64bit Version still denies not verified addons e.g. checkplaces latest from github.
re.: %PROGRAMFILES%/mozilla firefox/defaults/pref
Latest (utmost fair) ESR portable version 55.0.3 (64-bit) does
contain such a folder structure.
It is:
App
Data
Other
Theme
firefoxportable.exe
help.html
where the defaults can be found within \App\Firefox resp. \Firefox64.
Copy the scripts there does not work either,
can produce the error Jegar describes the latest though.
Copy as suggested config.js two upper directories will stop that,
the scripts still don’t do it, 136byte one of as John Bilicki stated earlier.
I’d gave a damn shyte about Mozilla since version 60x+
when it became more and more bloatware with a sinister
attitude towards users disregarding professional demands
on purpose faking FAQ into NIL.
Forgotten where you came from former Netscapers?
Now you are worse than IE ever was or Edge can be!
But I have hundreds of passwords stored over many years
in the addon Password-Exporter which FF left me behind
with. I have not figured out how to get them through into
Opera or else. So I am stuck with v55.0.3 hassled by
some sites that my browser needs an update despite
I have Comodo as an outbound firewall always for donkeys
years which serves and protects me very well.
F Y, Mozilla.
And thank you, Martin anyway, subject you still check
your “dinosaur”-thread.
Michael
To get this hack works you must paste “config-prefs.js” file on /pref directory (usually “%PROGRAMFILES%/mozilla firefox/defaults/pref” on Windows) and paste “config.js” file on firefox instalation upper level directory (“%PROGRAMFILES%/mozilla firefox”). This solve the error “Could not read configuration file. Please contact System Adminâ€.
This does not work as of june 31 2019. I have the hotfix for the stupid cert crap updated to ff55 due to capcha BS (no auto check) did the above files and it still refuses to install a updated Classic theme restorer. I am stuck on 1.5 which means I have transparent icons and cannot see my back fwd reload etc. I have wasted 3 hours on this. All because stupid google decides older stuff is shit. I have read people reinstalling and talking about disabled addons but mine is working. I do not want to uninstall it and continue to be blocked from installing meaning I wont have it at all.
@joop You should create the file using Notepad++ (on Windows) or another text editor that will NOT add a BOM (Byte Order Mark) to the beginning of the file. The config.js file must be exactly 136 bytes. You can not change the whitespace, linebreaks, ANYTHING – it MUST be EXACTLY as it is shown above or it simply won’t work.
If you do everything and are absolutely certain then I’d be willing to create a portable version of Waterfox completely up-to-date along with a cleaned up profile that already has Classic Theme Restorer working. I maintain the Fixed Firefox website, you can reply here and/or contact me directly there; my goal is to make people’s lives easier when it comes to technology.
Aware of it; WF requires 64-bit. I’ve got a clunker OS XP SP2 Home, 32-bit.
BUT…I’m actually very happy w/ your js code (brilliant!) & my rollback. Pages load super fast now, don’t hang; I’m working thru 2 routers & a firewall, so not worried about hacks, virus, yada. Actually never had them…ever.
I’m surfing the Net like the Silver Surfer surfs space. ;o)
PS. DDG, great SE!
PPS. As well, see hushmail.com…a spam filter that actually works; simple, non-flash platform, FREE; it’s Canadian & have had it for a number of years. For online emails, I love it to death!
SB
“I want to live forever. So far, so good.” -Steven Wright
“I was married by a judge. I should have asked for a jury.” – Groucho Marx
Found the only w/o available…now. (Does FF stand for Effing Fascists?). I rolled my browser back to FF51.0.1, Screw ’em. Original java script works beautifully.
Suggest you guys start-up a tech company & come out with a browser that doesn’t need updating–with the option to update.
Whenever I hear a techie say, “Update,” I know all hell is about to break loose. (Yeah, I know, all Geeks & Techies are *not* Stupid Smart Sheldons.)
THANK YOU!
Steven, your comments heavily suggest you’re not aware of Waterfox. I’d recommend using that instead and look up “Fixed Firefox” (WITH quotes) on Duck Duck Go; I record as much as I can there not only for myself though to help others clean up and fix (now) Waterfox (and previously Firefox). You ARE by the way, spot on in regards to their “politics”.
The workaround js (Classic Theme Restorer killed by FF) worked for a couple of days; then FF disabled flash for update & it went back to the horse & buggy FF of the past. Tried all 3 versions, short, longer & long.
I do appreciate the 3 days I had, though, and thank you. The problem is: Geeks (at least those at FF) ain’t got a clue how to run…a business.
If you come up with another w/o, would love to use it.
The solution for Firefox 57, is to delete the Firefox installation folder and use Iceweasel. Profiles are 100% compatibles and the browser doenst have any strange modifications, as Waterfox for example that promise compatibility for old xul addons. I really suggest to use it.
https://sourceforge.net/projects/libportable/files/Iceweasel/Stable/
Very nice! Thanks!
I wish there is easy way to allow unsigned addons which are already installed.
Hm, maybe if I can assign a empty function to “XPIProvider.verifySignatures”…
See post BlackJack August 14, 2017 at 1:48 pm
That modified config.js file
> //
> try {
> Components.utils.import(“resource://gre/modules/addons/XPIProvider.jsm”, {})
> .eval(“SIGNED_TYPES.clear()”);
> }
> catch(ex) {}
>
> try {
> Components.utils.import(“resource://gre/modules/addons/XPIInstall.jsm”, {})
> .eval(“SIGNED_TYPES.clear()”);
> }
> catch(ex) {}
works here with FX56
Thanks for the info. I fixed it using this tutorial and files:
http://www.largrizzly.net/firefox.html
No more working with 56.0.2.
Is there a workaround for Firefox Quantum 57?
To make it short : no
And with Firefox Nightly?
Worked perfectly, thank you so much! Now I can finally update firefox :)
Am using Firefox version 55.0.1 and am getting the warning that the addon “could not be verified for use in Firefox and has been disabled” but all my old addons are still working just fine. Thanks for this hack.
Updated code to work on Fx54+ (it is needed because of the new XPIInstall.jsm introduced in Fx 55 — a consequence of Mozilla enabling WebExtensions permissions system, upon installing and checking add-ons):
//
try {
Components.utils.import(“resource://gre/modules/addons/XPIProvider.jsm”, {})
.eval(“SIGNED_TYPES.clear()”);
}
catch(ex) {}
try {
Components.utils.import(“resource://gre/modules/addons/XPIInstall.jsm”, {})
.eval(“SIGNED_TYPES.clear()”);
}
catch(ex) {}
Better:
//
["Provider", "Install"].forEach(name => {try {
Components.utils.import(`resource://gre/modules/addons/XPI${name}.jsm`, {})
.eval("SIGNED_TYPES.clear(); this;").eval(String.raw`"verifyZipSignedState" in this && (uuidg => {
var signedState = AddonManager.SIGNEDSTATE_NOT_REQUIRED;
var re = /\x06\x03U\x04\x03\x14[\s\S](\{[0-9a-f]{8}-[0-9a-f]{4}-[0-9a-f]{4}-[0-9a-f]{4}-[0-9a-f]{12}\}|[a-z0-9-\._]*\@[a-z0-9-\._]+)0\x82\x02"0\r\x06\t/i;
var bsp = Cu.getGlobalForObject(XPIProvider), til = bsp.eval("TemporaryInstallLocation");
var getId = file => {
var result, is = {close() {}}, sis = {close() {}};
var uri = bsp.getURIForResourceInFile(file, "META-INF/mozilla.rsa");
try {
is = Services.io.newChannelFromURIWithLoadInfo(uri, null).open();
sis = Cc["@mozilla.org/scriptableinputstream;1"].createInstance(Ci.nsIScriptableInputStream);
sis.init(is); var str = sis.readBytes(sis.available());
var match = str.match(re); if (match) result = match[1];
} catch(ex) {}
sis.close(); is.close();
return result || uuidg.generateUUID().toString();
}
verifyZipSignedState = function verifyZipSignedState(aFile, aAddon) {
if (aAddon.id || aAddon._installLocation == til)
return Promise.resolve({signedState, cert: null});
var root = !AppConstants.MOZ_REQUIRE_SIGNING && Services.prefs.getBoolPref(PREF_XPI_SIGNATURES_DEV_ROOT, false)
? Ci.nsIX509CertDB.AddonsStageRoot : Ci.nsIX509CertDB.AddonsPublicRoot;
return new Promise(resolve => {
var callback = {openSignedAppFileFinished(rv, zipReader, cert) {
zipReader && zipReader.close();
resolve({signedState, cert: cert || {commonName: getId(aFile)}});
}};
gCertDB.openSignedAppFileAsync(root, aFile, callback.wrappedJSObject = callback);
});
}
})(Cc["@mozilla.org/uuid-generator;1"].getService(Ci.nsIUUIDGenerator));`);
} catch(ex) {}});
yes, i’ve noted this behaviour in some webextensions, fast solved moving off config-prefs.js in \defaults\pref, installing the webextension and replacing the script
Note that using the code I have posted above will sadly prevent some WebExtensions from being installed (Firefox will tell the user it thinks the add-on is corrupt :p).
Thanks! Now I can finally install pre-release uBlock Origin builds.
Oh my God, thanks so much for this! Now i can update FF to 55.0.1, i was waiting Waterfox for their release, but now i can use the official one. I’m started to be boring from Mozilla, they broke something every major release
I never heard of Waterfox so I checked info on it. It is Win 64 bit so that knocks me out.
Still, you have to have absolute faith in the people standing behind the security of your browser.
Can you say that for Waterfox?
I am on FF 54 and this hack is still working on my unsigned extensions. I have a strategy for the long run. When FF comes out with a version that stops my must-have extensions, I will stop updating FF and switch to Chrome as my every day browser. I will only fire-up FF when I have to use those extensions until the new FF will get those (which will probably be never). It is a pain but a workable one I hope.
waterfox claims on his website that unsigned addons works, i hope that it will also with build 55.
Indeed, and that means Waterfox accepts unsigned add-ons *without* of course having to use the add-on signing requirement override mentioned by this article.
What I can say is that I had tested Waterfox and that indeed it blocked none of my un-signed add-ons (the above oveeride was of course *not* installed).
I don’t see why this Waterfox acceptation of unsigned add-ons should disappear with coming versions.
FF 55 is coming, and there isnt any working solution to install custom addons… this will be sad
Hi,
My name is Johir Haque. I read your article and had done it. But now what happened that my browser is not connecting with internet. What should I do now. I am currently running 54.0 (32 bit)
Waiting for your answer.
N:B: – I am always keen to make changing for my personal use.
Thank you.
Hello Johir,
I really cannot figure out how such settings (whatever Firefox version) can possibly have a relationship with the browser’s Internet connection, unless that connection would depend of an add-on which itself would be blocked by the work-around, which is hard to imagine.
Hello i have installed 55 beta 1 and seems to be that Mozilla doesnt like this method. There is any workaround to restore this?
What I will explain hereafter was valid for Firefox 52 and remaind valid for Firefox 52.2.0 ESR :
1- The work-around provided by this article describing config.js and config-prefs.js : some add-ons require these two files to be removed for the install to operate correctly. In such cases,
– rename config.js to config.js.bak and config-prefs.js to config-prefs.js.bak ;
– restart Firefox and proceed to the add-on’s install ;
– rename rename config.js.bak to config.js and config-prefs.js.bak to config-prefs.js ;
– restart Firefox.
2- In some cases the work-around, even operated as mentioned, is not enough : even if the following setting is announced as obsolete it is sometimes required additionally to the work-around in order to have the add-on’s signing requirement overridden correctly :
// disable add-on signing requirement — obsolete but still listed (reset puts it to “true”)
user_pref(“xpinstall.signatures.required”, false);
Best therefor is to leave this setting to false, won’t harm when unused.
This, as I said, is tested/valid until Firefox 52+ and Firefox 52+ ESR. I don’t know if Firefox 53+ has changed in such a way that the ‘trick’ doesn’t work anymore, but it could be that what I mention above is the culprit. Best is to test, of course.
I used the above config.js file in Firefox ESR 52.5.0 x86 and an unsigned extension (the Classic Add-ons Archive, aka ca-archive) was still blocked from being installed. When I checked about:config, xpinstall.signatures.required was already there and set to true. I changed it to false and the installation was allowed to proceed. (The xpinstall.signatures.required=false setting survived a browser restart, so it wouldn’t be temporary unless you manually changed it back to true.)
Тhis does not work with Firefox 53.0.2 (64-bit). Any workarounds?
Worked a treat. I was able to restore 3 FF extensions deprecated by extension signing. Brilliant !
Hello this files/metod block install Disconnect 5.18 (on WebExtension) and Evernote Web Clipper 6.9+ (on WebExtension).
Any fix for install without delete this files?
Please, update the article reinforcing that is needed to copy the two slashes in first line of config.js.
Some people, like the one in previous comment, are ignoring it.
Thanks for your article
However, it not work for me. I follow those step. I cannot open the firefox till removed those .js.
Do you know the issue?
Doesn’t work with 51, they disabled processes.
https://blog.mozilla.org/futurereleases/2016/12/21/update-on-multi-process-firefox/
Beyond Firefox 50, we have more work to do to enable multi-process Firefox for users with as yet unsupported extensions. In Firefox 51, if all testing goes according to plan, we’ll be enabling multi-process Firefox for users with extensions that are not explicitly marked as incompatible with multi-process Firefox.
Mac OS X path is wrong.
It should be as follow:
config.js put in path /Applications/Firefox.app/Contents/Resources
config-prefs.js put in path: /Applications/Firefox.app/Contents/Resources/defaults/pref
@jhousedj
I use Firefox ESR (currently 45.X) only and maintain each install version separately (internet\Mozilla Firefox\45.0\) as well as separate profiles. Luckily for you there hasn’t been a break so I was able to update with channel updates without screwing up the versions / directories.
I’ve encountered ambiguous results in the past so I recommend trying again. I remember that I had to have the file EXACTLY as stated (I do not recall what changes I had made or why, perhaps comments) so make sure you don’t have an extra line break, a byte order mark, are missing the comment slashes on the first line, a 7th line, etc or some other obnoxious difference in the config.js file.
Firefox 50 did not require an update, 51 Beta 10 fails to apply the update, 52 and 53 updated fine. All my profiles are highly customized to negate lots of stupid nonsense Mozilla has wrought on Firefox the past few years and I can assure you if my config wasn’t correct the whole GUI falls to crap.
I know it’s infuriating how a lot of these companies don’t get it though trust me, getting it will become a prevalent leadership quality again in the coming years.
Have any of you gotten this workaround to work in FF 50 or higher? Am getting standard “some extensions could not be verified” behavior.
Double checked following and still no joy:
1.) Did you edit the correct file?
2.) Did you edit the correct file with the correct changes?
3.) Did you save the correct file after correctly editing it?
4.) Did you open Firefox?
5.) Did you open the version of Firefox you edited the file for?
6.) Did you open the correct version of Firefox with the correct profile?
7.) Did you restart Firefox before expecting the changes to take place?
8.) Did you have multiple Firefox instances running and restarted the correct one?
Any ideas ??
Run firefox as administrator and pay attention to // at the beginning of the config.js
Waterfox (x86, x64, Linux) … the real deal … FF extensions etc work a treat; for any that don’t, download them [*.xpi] & change the “max version” to 99 or whatever. The .xpi files can be opened with winrar, the changes required being in the install.rdf file
No restrictions at all. Waterfox is a smidge behind FF in relation to updates, but it’s what FF was before FF stopped listening to users
Hi. I tried to do this on Debian and it didn’t work. I copied the files verbatim into /usr/lib/firefox-esr and /usr/lib/firefox-esr/defaults/pref but nothing seems to have changed — I haven’t seen the issue with other extensions being uninstalled. I get the same ” (Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0)
My browser console output was “1483223313930 addons.xpi WARN Download of file:///home/nicolas/stupid%20firefox%20extension%20crap/(I named it the exact same thing as the original .xpi).xpi failed: [Exception… “Component returned failure code: 0x8052000b (NS_ERROR_FILE_CORRUPTED) [nsIZipReader.open]” nsresult: “0x8052000b (NS_ERROR_FILE_CORRUPTED)” location: “JS frame :: resource://gre/modules/addons/XPIProvider.jsm :: AddonInstall.prototype.loadManifest< :: line 5466" data: no] Stack trace: AddonInstall.prototype.loadManifest<()@resource://gre/modules/addons/XPIProvider.jsm:5466 < TaskImpl_run()@resource://gre/modules/Task.jsm:315 < TaskImpl()@resource://gre/modules/Task.jsm:276 < createAsyncFunction/asyncFunction()@resource://gre/modules/Task.jsm:250 < AddonInstall.prototype.onStopRequest()@resource://gre/modules/addons/XPIProvider.jsm:5802"
Really makes no sense. I set the booleans in about:config to false as well. I think I need to just give up and install the developer version but I'm going to give it one last try and copy the .xpi file into the profile directory to see if starting Firefox with it already there can bypass the verification somehow. But it doesn't appear to even be LOADING the .js…
Thanks
Worked like a snap.
I turned on the unsigned addons before in about:config before, why do I need to make a javascripst now!?
Screw security lock that can not be opened by a user. That’s a freaking jail.
if you can’t get this working (just a few very easy to follow steps) you probably don’t really want to disable signing requirement.
A note for all who encountered problems using the method described, like the user who encountered the error message saying “Configuration Error”, “Failed to read the configuration file. Please contact your system administrator”:
Make sure the files config.js and config-prefs.js EXACTLY and ONLY contain the contents as described in the instructions (including the comment lines of the code snippets). Do *not* add own comments and so on to these files. I added own C-style comments to the files and wondered why I didn’t work. Actually everything works now.. You must follow the instructions precisely (also regarding the paths… they refer to the installation directory and not to your profile directory).
Then it worked fine for me (Firefox 50.0.2; 32bit; Win 7)
This worked for me today firefox 50 win 7… I copied the “//” and it works, thanks.
Dave, thanks for your confirmation that the trick is still working.
I’ve been using this trick to block Firefox’s Add-on Signing requirement ever since it appeared in August 2016.
I’ve just noticed one issue, here, now with Firefox 50 and with several add-ons, but maybe not all add-ons are concerned, the ones which posed a problem had in common of being of a format free of the install.rdf file.
With these add-ons, installing them (either from AMO either from their download to my computer) issued a refusal and the message “The add-on is corrupt”.
I tried to find the reason, maybe one of my settings, or another add-on incompatibility? I opened a new ‘dummy’ Firefox folder to be sure : same issue! … of course same issue once I remembered the above trick and its two files I had in the Firefox install foder & subfolder … . I closed Firefox, removed config.js and config-prefs.js, restarted Firefox and installed the problematic add-on with no issue this time. Closing Firefox, putting back the two scripts and all was fine
I’ve built from there on 2 batch files, one to add and another to remove the two scripts quickly. From now on I’ll have to proceed that way for new (or for some) add-ons. Takes another minute or so but those two scripts are worth it.
Unfortunately it does not work for me in Firefox 50.
1.) Did you edit the correct file?
2.) Did you edit the correct file with the correct changes?
3.) Did you save the correct file after correctly editing it?
4.) Did you open Firefox?
5.) Did you open the version of Firefox you edited the file for?
6.) Did you open the correct version of Firefox with the correct profile?
7.) Did you restart Firefox before expecting the changes to take place?
8.) Did you have multiple Firefox instances running and restarted the correct one?
Does not work in Firefox 49.0.2 ((
worked for me
Wow……………searching for weeks, found this and it works!!!!!!!!!
Thanks, you guys are great!!!!!!!!!!!
In regards to the randomized names for the XPI files, you can actually figure out which is which by going to the following URL in Firefox: about:support
Thank you VERY much for sharing this tip. I tested it on Ubuntu Trusty with Firefox 49 and it works perfectly. Saves me from having to rebuild Firefox again.
Critical: ***existing extensions*** will NOT be enabled.
If you’re not able to track down the installer XPI file and the author of the extension has either intentionally closed access to it (e.g. the Paste & Go extension) but you’ve installed it then it will likely still be available in your Firefox profile.
Full Windows Path (change your user account):
C:\Users\[Windows User]\AppData\Roaming\Mozilla\Firefox\Profiles\Mozilla Firefox 45.0 ESR
Short Windows Path
%APPDATA%\Mozilla\Firefox\Profiles\
Unfortunately Firefox randomizes the XPI file names though they still retain the *.xpi extension (at least on Windows).
Sorry, a slight erratum : the issue I mentioned appears with Firefox 49.0.1 , not sure for 49.0 … in fact I encountered the issue this very afternoon for the first time and I had forgotten that I updated FF from 49.0 to 49.0.1 yesterday …
Version 49.0 lasted 7 weeks (instead of 6) and I must have installed an add-on with the scripts installed under FF 49.0 but I’m not absolutely sure.
I’ve just discovered a little problem with at least Firefox 49.0 — I say 49.0 because I don’t recall the following issue with previous versions of Firefox.
I wanted to install a new Firefox add-on from AOM and the install completely corrupted my Firefox profile folder, in fact it removed all the extensions in the extensions folder! Same when I downloaded the xpi and performed the ‘Install Add-on From File…’.
I exited Firefox, copied back my backuped Profile folder, removed both config.js and config-prefs.js from the install folder, started Firefox and installed the new add-on normally … of course I thexn exited Firefox and re-installed both js files …
That’s it.
Martin could you or someone tell me what effect upgrading to FF new release 49.x have on the add-on override that I accomplished a few weeks back for Adobe Acrobat X with the help of this thread?
At that time I set FF to notify me of updates but not to auto install. Well they’ve notified me a few times already and I’ve said ask later. So now I’m wondering if I should install FF updates and if I do will my Adobe Acrobat be disabled again?
Can you advise me on this and/or point me in the right direction. I don’t want to lose the use of my Adobe Acrobat X again.
Thanks!
P.S. If it matters, I’m currently using uBlock Orgin, Ghostery, NIS and CCleaner to try and keep my web browsing safer
I have not tried this with Fx49 so cannot really say. What you could do is download a portable copy of Firefox (http://portableapps.com/apps/internet/firefox_portable), copy your profile to the portable folder and run it.
This may come useful for future updates as well as you can test it this way whenever Mozilla releases a new update.
Thanks Martin for your response. I will follow your recommendation. Can I install the portable copy of Fx49 on my win7 machine that I recently performed the add-on override on, and that has the adobe acrobat product installed?
If so, would I have to create a virtual machine/window and to perform this test there on my desktop? Never tried to create a virtual machine b4. If this is what’s required is there a link that would tell a semi-technical layperson like me how that’s done that you could link me to? Also would adobe acrobat as currently installed also be available in a virtual machine/window for test purposes? I believe my Win 7 Ultimate 64 bit desktop, with an Intel 17-4970K CPU 4.0 Ghz could handle it. Do you agree? However I only have 8 gig of ram currently installed on this machine.
I do have two other machines I could possibly test it on. An older HP that’s running Win XP Pro SP3 with all the updates that were once available. Its has my 2nd licensed installation of Adobe Acrobat X program on it. Not sure if using XP & Acrobat to test how Win 7 & Acrobat would work w/FF 49 would work, would it?
My other option is a Lenovo Lap top also running Win 7 Ultimate but it doesn’t have a copy of adobe acrobat X running on it. I’m assuming I could install one from my original Adobe Acrobat X CDs, do all or the necessary updates, and test without licensing it, if this software offers a short window that it will run b4 licensing is required? I don’t remember if that was possible with this software.
Does any of these sound like viable options of how to perform the test you recommend? Or am I overly complicating this and there’s an embarrassingly easy way to accomplish your recommendation? Is so what would that be?
Let me know and thanks again for your help.
You can download, unpack and run portable Firefox from any location. No need to use a virtual environment. The portable installation uses profiles that you find in the portable folder which means it runs independent from any installed copy of Firefox and its profiles.
This is absolutely AWESOME!
Worked like a charm after I remember to reinstall the disabled add-ons. Many thanks :)
Was worried at first – still disabled, then remembered to reinstall. It works GREAT. many thanks :)
step 2 . where do you place this file on a mac?
James, you put it in defaults\pref of the Firefox program folder (that is mentioned under step 1).
I have to be doing something basic wrong, but I cannot get this to work on Mozilla Firefox, Portable Edition from PortableApps.com
Where should I be putting the files? The root FirefoxPortable folder? One of the app folders? The profile folder like user.js?
Running Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:48.0) Gecko/20100101 Firefox/48.0 (en-US) with the “correct” installation of the described method will accept unsigned add-ons ‘again’.
Before I have reported the method isn’t working. My error was not adding all of the content of config.js. I missed the first line with ‘//’ … which seems to be important as well!
Big thanks to the author .. Thanks Martin!
Thank you very much! I was looking for such a solution for quite some time.
This doesn’t work. ImageHostGrabber is still deactivated and can not be reactivated.
gosh!
Did you try and reinstall the extension?
What I find interesting… Mozillazine (not a Mozilla site) seems to have removed/deleted the few threads/posts which even mentioned this “hack” (to them–simple user customization to the rest of us) for some unspecified reason(s). Just one reason why I found Mozillazine no longer worth going to (on any kind of regular basis) quite some time ago. (Now, it’s possible they just moved it around enough–making it harder to find, but given the WTF rant/posts there, this seems less likely than them simply being removed.)
Me, I prefer to be inside the tent, relieving myself outwards.
I’d really like the internet not to be the perfect rumour machine.
Sadly, no.
Mozillazine’s forum continues as the place where the most experienced and helpful Mozilla contributors dwell.
I linked here from there.
Already this response thread here is full o errors.
After placing these 2 files in the FF sub-directories you must “remove” the blocked add-on and then install it fresh. The magic of this hack happens during the reinstall of the add-on.
In response to j_norton: True, I’m confused about the differences between Extensions and Add-ons. The Adobe acrobat program I use appears in Firefox under both categories. I don’t recall doing anything intentionally to install it in either location (extensions and add-ons). When I installed my copy of Adobe Acrobat 10 on my new computer last year I was assisted by Adobe’s tech support and I just followed their commands on what to do. My copy of this software (and all software I run) is a fully licensed and registered copy of the program that I purchased from the manufacturer or a licensed retailer.
I feel I have every right to run this software as I have in the past. If it is vulnerable partially because the manufacturer no longer supports it (not that it wasn’t vulnerable when they were supporting it) I choose to run it, after weighting my options, knowing that and take other precautions with firewalls, anti-virus, anti-malware, programs, cleaners and 2nd opinion software, etc. I do watch what’s happening on my system to the best of my ability. Yet, I definitely would welcome a more secure solution butt he only upgrade path that I’m offered from adobe is their cloud based DC version that I’m not impressed with and don’t want. I’m testing other pdf conversion desktop software but haven’t yet found a suitable solution. The search continues..
Do you feel my thinking on this point is flawed? And since you say that Extensions and Add-ons are two different animals do you have any thoughts on why my adobe acrobat app is installed in both areas of FF? Let me know if you can shed in any further light. Thanks for all your feedback
P.S. As I stated in another post that never showed up I did get a version of this workaround to work for me, although I know its likely temporary. Thanks again
Hi J_norton. Thanks for your response. How do I “remove the blocked add-on? I longer see the delete button next to it either in the Plug-Ins listing or the Extension listing. Under the plug-ins I can “never activate” but no delete is present. So could you please tell me what I need to do to remove the block add-on.
Thanks!
jan1ce, you are referring to plugins, not extensions which we call add-ons here. Plugins have nothing to do with unsigned addons that we are talking about. FF blocks plugins which make the computer vulnerable. So leave your plugin as “never activate” until you find and install a newer version that is not vulnerable.
Please help if you can. I’ve followed these instructions closely but it hasn’t worked for me. I’m running Firefox 48.01 32 bit with 64 bit Win 7 Ultimate. I’m also one of those whose add-in had been already blocked before I discovered this workaround. The only blocked Add-in that I desperately need is the by Adobe Acrobat 10. I know its old but it’s worked very well over the years and I’m not currently in a position to upgrade. And I don’t want the web based DC version.
I used the notepad++ to create the file requiring an editor and the notepad for the other and deposited them in the respective sub-directories as instructed. Its step 3 that I having trouble with. It merely states “install unsigned add-ons in Firefox stable or beta”. How do you do that? My Adobe Acrobat pdf add-in is already installed and blocked by Firefox. Although I do have my original disk from circa 2012, I searched for an .xpi files on it but couldn’t find them. (I did find install a bunch of api files installed on my C drive, do they count or help in anyway?)
I’ve taken a several additional steps trying to fix this as well , including
1) I did a “repair” of my adobe acrobat installation thru add and remove programs to try and correct any possible problems that way.
2) Additionally I re-downloaded and re-installed the most recent update the adobe acrobat X. Although, the update was already installed it seemed to go thru the update process again. For a minute I was hopeful, but when I go back to Firefox add-ons in my browser my adobe acrobat is still blocked with no ability that I can see to reactivate it.
Last time this happened I found instructions to edit the FF about:config file and that worked ( mostly) up until now. But as you probably know that edit doesn’t appear to be working anymore.
Another thing I tried was viewing and editing the extensions.xpistate string from the FF about:config file. All I did here was to change “true” value following the adobe acrobat entry to “false”, but when that didn’t work I changed it back to true. Here’s a copy of the text in the “extensions.xpistate” string I’m referring to from FF about:config file :
{“app-profile”:{“amznUWL2@amazon.com”:{“d”:”C:\\Users\\Janice\\AppData\\Roaming\\Mozilla\\Firefox\\Profiles\\1vbmhb06.default-1447476414264\\extensions\\amznUWL2@amazon.com.xpi”,”e”:true,”v”:”1.11″,”st”:1465017297053},”jid1-sNL73VCI4UB0Fw@jetpack”:{“d”:”C:\\Users\\Janice\\AppData\\Roaming\\Mozilla\\Firefox\\Profiles\\1vbmhb06.default-1447476414264\\extensions\\jid1-sNL73VCI4UB0Fw@jetpack.xpi”,”e”:false,”v”:”2.1.4″,”st”:1455494951615},”printedit@DW-dev”:{“d”:”C:\\Users\\Janice\\AppData\\Roaming\\Mozilla\\Firefox\\Profiles\\1vbmhb06.default-1447476414264\\extensions\\printedit@DW-dev.xpi”,”e”:false,”v”:”17.1″,”st”:1471301977853},”uBlock0@raymondhill.net”:{“d”:”C:\\Users\\Janice\\AppData\\Roaming\\Mozilla\\Firefox\\Profiles\\1vbmhb06.default-1447476414264\\extensions\\uBlock0@raymondhill.net.xpi”,”e”:true,”v”:”1.8.4″,”st”:1470596866229},”{8F6A6FD9-0619-459f-B9D0-81DE065D4E21}”:{“d”:”C:\\Users\\Janice\\AppData\\Roaming\\Mozilla\\Firefox\\Profiles\\1vbmhb06.default-1447476414264\\extensions\\{8F6A6FD9-0619-459f-B9D0-81DE065D4E21}.xpi”,”e”:true,”v”:”1.13″,”st”:1451189898963}},”app-system-defaults”:{“e10srollout@mozilla.org”:{“d”:”C:\\Program Files (x86)\\Mozilla Firefox\\browser\\features\\e10srollout@mozilla.org.xpi”,”e”:true,”v”:”1.1″,”st”:1471893125199},”firefox@getpocket.com”:{“d”:”C:\\Program Files (x86)\\Mozilla Firefox\\browser\\features\\firefox@getpocket.com.xpi”,”e”:true,”v”:”1.0.4″,”st”:1471893125198},”loop@mozilla.org”:{“d”:”C:\\Program Files (x86)\\Mozilla Firefox\\browser\\features\\loop@mozilla.org.xpi”,”e”:true,”v”:”1.4.4″,”st”:1471893125194}},”app-global”:{“{972ce4c6-7e08-4474-a285-3208198ce6fd}”:{“d”:”C:\\Program Files (x86)\\Mozilla Firefox\\browser\\extensions\\{972ce4c6-7e08-4474-a285-3208198ce6fd}.xpi”,”e”:true,”v”:”48.0.1″,”st”:1471893125200}},”winreg-app-global”:{“web2pdfextension@web2pdf.adobedotcom”:{“d”:”C:\\Program Files (x86)\\Adobe\\Acrobat 10.0\\Acrobat\\Browser\\WCFirefoxExtn”,”e”:true,”v”:”1.2″,”st”:1471937213867,”mt”:1443109322000},”{C1A2A613-35F1-4FCF-B27F-2840527B6556}”:{“d”:”C:\\ProgramData\\Norton\\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\\NIS_22.5.4.24\\coFFAddon”,”e”:true,”v”:”2016.7.0.62″,”st”:1466097628714,”mt”:1466097628714}}}
As you can probably tell I’m technical skills are limited. I’m an independent accountant not an IT person. Could you please help me with some suggestions that could get my adobe acrobat X plug-in working again?
This would be most appreciated! Thanks in advance.
Jan
P.S. I thought I submitted this earlier but didn’t see it show up. If this is a duplicate please delete one. Thanks!
Thank you, thank you. I am very much dependent on a add-on that I have been using for many years and is no longer maintained by the developer and is unsigned. This hack worked perfectly. Please keep an eye on the idiots at Mozilla in case they break this hack.
thank you.
But there is an error in this guide.
if you are on a mac the main installation folder is /Applications/Firefox.app/Contents/Resources
inside Resources you can also find defaults/pref.
I really like firefox, but I don’t like when they try to change things for power user (this is like SIP on apple computer… but there is actually an official way to disable SIP).
I still need to find an alternative that is not chrome, because I’m not sure this workaround will work in future version… maybe the developer edition is ok (still they can disable it in that version too)…
Maybe it’s time to find a new browser.
The best option is Firefox ESR (Extended Support Release).
Override add-on signing (advanced users)
You can temporarily override the setting to enforce the add-on signing requirement by changing the preference xpinstall.signatures.required to false in the Firefox Configuration Editor (about:config page). Support is not available for any changes made with the Configuration Editor so please do this at your own risk.
But the method does not work on Stable or Beta versions of Firefox.
True .. and I’m surprised with FX48 that prefs set to true on my installation (see avove) stops running the unsigned add-on. I thought with beginning of FX48 that pref doesn’t have any effect anymore.
Confused :>
installed on 48
but error:
“Could not read configuration file. Please contact System Admin”
any solution??
Same as with me, see above.
Can you add your directories you use FX, please.
NB: I posed I can use unsigned add-ons (at least one I personally generated), my FX 48 is installed on “Mozilla Firefox for Linux Mint mint – 1.0”
Dont have any of this nonsense in pale moon which i regard as a better browser than firefox.Pale moon has its own add on site and the add ons work.
Seems to me that extension developers for firefox are continually playing cat and mouse with mozilla.
Last time i tried firefox two thirds of the themes would not work or were incompatible with the latest firefox.Extension developers will just say bugger it one day.
Thank you, this trick worked for me. Now I’ll wait for the extension developer to get his work signed, or maybe never.
Cool Previews lives another day!
Thanks
To add to my previous post:
Just added an unsigned addon to FX 48 (without this proposed settings) and the addon installed and got activated with the comment: “{addon} could not be verified to use in Firefox. Proceed with caution.”
There is not problem using the add-on!
Tried to install the method on Firefox_beta (Version=49.0) but failed with “Could not read configuration file. Please contact System Admin”
Also changing chown from root to user didn’t helped.
The files are installed in:
/opt/firefox_beta/config.js
/opt/firefox_beta/defaults/pref/config-prefs.js
with
/opt/firefox_beta/firefox-bin
What’s wrong?
It doesn’t work with already disabled unsigned add-ons.
Try reinstalling them, just install over the top of the old one – you shouldn’t lose any settings (i.e it should replace all the files but any custom extension preferences or files should be intact eg about:config entries, or UBO filters, or scrapbook entries etc). Let us know if that works.
Still doesn’t work.
No idea if you need to do it every release. I would think not, seeing as the files are custom (an update should not edit or remove them). I suggest before the next FF update, that you close FF and copy your profile folder as a backup.
Pale Moon Commander in a FF? I mean we’re 20 versions on since the split … what’s so important in PMC that you need? I’m intrigued
Thanks, it worked. Pale Moon Commander add-on is working in Firefox again.
Do you know if I have to add config.js and config-prefs.js after every Firefox update ?
Nice find Martin.
Then, what stops malware from doing this same thing? Wasn’t stopping it the main justification for making extension signing mandatory?
NO. Mozilla in their “infinite wisdom” decided to force add-on developers to use another way of coding their add-ons supposedly to streamline Firefox more. All that has done has disabled a whole bunch of very useful add-ons which are not being kept up with by those developers.
Nunya, what you are saying is true, so true, it’s been, is and will continue to be the exclamation of many, many users. Consequently it’s becoming some sort of incantation every time an article concerns Firefox, mainly its extensions. I believe that, after the time of revolt arises a new conduct towards what we cannot change. This is, anyway, how I see the Firefox scenario. It’s driven us mad, now what about considering what we’ll do with reality? Many say : “I’ll quit Firefox”. Too easy, more the expression of exasperation than that of rationalism. Let’s compare what we have with alternatives and, IMO, Firefox, even 57+, will remain a most interesting browser, even if I, you, many of us cry and yell on Mozilla’s decisions, Firefox may not be, no longer be as great as we knew it, or it may be better (not IMO but some believe so), Firefox, compared to competitors, does have a solid, a worthy policy and architecture. We have to wait and see now that we know Mozilla’s decisions are irrevocable. I’m on 52 ESR but as I often say it’s for the liberty of being more an observer and less an actor as long as 52 ESR allows it. I may be enchanted by the ’57 revolution and, who knows, in 1 or 2 years legacy add-ons be no more than a tender souvenir in the new Webextensions + Electrolysis era. I wouldn’t swear of anything.
I look after several systems running quite old versions of firefox, the owners don’t believe what I say about vsn 52 and insist that theirs is the last trustworthy one. It has to be said I’ve yet to see any major failing that would convince me to ‘upgrade’ if I believed the same. I am intending to stick with this ESR version, with updates disabled (and the browser firewalled away from the update site just in case) until standards have progressed to the point I’m missing out on something critical. Then I will investigate PaleMoon or more likely Watefox (is that the best one?) as an alternative. I will be very very unlikely to ever let them install one of their RUSTy strangled chrome-clones on my system.
Hi Dave,
I switched to Waterfox. Palemoon did just have Gecko updated from 28 to 52 however they do not have multi-process support. With it Waterfox uses more RAM though it’s much more responsive with my heavy work loads/number of tabs that I use for general purpose and web development. I can’t say for certain how long it’ll be before the newer Gecko engines can finally be merged in to Waterfox without breaking customization though it seems to be a much greater consideration from the lead Waterfox developer than from what I’ve gathered reading about Palemoon. Palemoon would be great for a quick deployment for less technical users who do light browsing though Waterfox is much more up to the task of heavier work-loads presuming you have sufficient amount of RAM (and aren’t forced to run a page file).
In any modern browser, any extension has whatever power you give it *during runtime of the browser*.
The modern browser is powerful because it runs active code and, given time, all hacks are possible.
To slow down the discovery of hacks, limiting the access of extensions APIs is a
reasonable move.
Sadly for Moz Corp, official owners of Firefox, the original Firefox Addons community evolved as an anarchistic mob, where the user learned to work out how to establish trust in those monkey patch writers by involvement in the community. Hence no restrictive APIs (such as those for Chrome, IE) had been developed by the time Mozilla Corp decided that a Firefox user would be better off placing their trust in a centralised authority rather than an anarchic community. I impute no motive in this move, btw. Moz Corp are opaque and getting more so every day.
This pretend-style certificating is the only way for Moz Corp to enforce their central trust model right now.
Enjoy this temporary respite from the takeover.
When the new Firefox engine is released, many more addons will be
broken for good
The argument used is that if malware has access to the system already, there is nothing that it cannot do. While it could use access to plant an unsigned add-on in Firefox, it could do other malicious things as well with far greater consequences.
what about a software installer could it not add the config.js so it can install its addon that when updated downloads malware bypassing standard checks for malware been the installer was legitimate with a legit addon a common pup.
the malware authors just need you to install the legit app there unsigned addon or signed addon does the rest. mozilla wants to lock addons to there website same as chrome. if the addon signing was really about security there would have been a better made.
@martin would this be doing the same thing https://www.youtube.com/watch?v=PF_q8g5pKJI with the config file?
I don’t think it is the same method that is shown in the video. The author states it is version specific.
If software installers can add the file, they can add other files on the system as well and do more damage. Sure, it is a possibility.
Chrome!
“How to override the Firefox Add-on Signing requirement”
When I read this in Ghacks RSS feed I remained stunned. I read it again and felt it as :
>>>>>>>>>> !!!!!!!!!! How to override the Firefox Add-on Signing requirement !!!!!!!!!! >>>>>>>>>>
So easy to perform and yet : how on Earth did the finder discover that one?!
I’ve had several small add-ons that had to be removed because of the signing requirement. There are other add-ons on AMO I wish to modify for my tastes. Generally speaking this “trick”, “work-around” is great news because it appears as oxygen, as a mental relief, as an horizon of freedom. A psy would maybe say that my enthusiasm is relevant of a deep inner suffering not consciously measured because we adapt ourselves to reality but showing up now that liberated :)
Many thanks Martin for discovering the finding and sharing it, perfectly well describes that even a grandma could get a non-signed add-on back on track. Fantastic. You know what? I’m happy.
@ Tom Hawack
Psychology AND Philosophy in one post. :-)
Seriously, where do these wizards discover such clever work arounds.
Thanks Martin !
Question:
Should I install these scripts into my current version of FF 47.0.1 and then upgrade to 48 – or first run the update and then insert the scripts – or does it even matter ?
I have a number of older add-ons which are no longer supported by the author and do not want to risk losing them.
Yes it’s the best thing to do, exactly what I’ve done.
The code in the script remove the ability for Firefox to discriminate between signed addons and unsigned simply.
So installing it before those change will already be in your profile folder when you will update.
One thing to take care if like me you use more than one profile you must copy those 2 fils to each other folder profile to have it work in all profiles. Just copy/paste those 2 files in the new profiles and you’re ready. ;-)
1. Install FF 48.0 but don’t run it when you Finish installation.
2. Now, use the scripts correctly
3. It is better to reboot and then open Firefox.
4. Now, your Add-ons should work fine.
To be safe, it is better to take Bkp of unsigned Addons before installation.
Thanks very much for the feedback.
I use Mozbackup and will make complete backup of my profile, including extensions before following your steps above.
Very handy information. Thank You!
Thanks Martin : )
Now I can use a stable version again
Better option is to use pale moon.
Yet better is use Waterfox !!!!!!!!!!!
Updates are a smidge behind FF, but it works like FF did :-(
Firefox Community Edition
:’|
Best option is Firefox Developer Edition.
I think that better option is to use Cyberfox ;)
@ Nel
+ 1 :))
Great and especially for foreign users like me that don’t use the English version of Firefox since the “unbranded” build is ONLY available in English.
Right, and these unbranded builds had other issues last time I checked (automatic updating not working).
I would imagine most people with enough clue to reverse FF-dev’s “Only what we allow” enforcement would see automatic ‘updating’ to be about as far as you can get from desirable anyhow!
The last thing I want to do on my machine is give permission for random authors to replace my programs with anything they feel like trying on a few million victims..
I like a machine where I KNOW what is running, I research any detected bugs and I apply patches as and when those bugs are a nuisance. Otherwise, even under best case, everything I run will slowly metamorphose the usual pieces of originally sketchy code running under virtual systems on virtual processors, at about the speed of a tadpole in treacle.
Under worst case, I could wake up one morning and (not) find that one of my applications has transformed into a rootkit because some smart-alec has got hold of the developer’s key along with access to their update server..
Universal auto-update = please run whatever you feel like on my machine. whenever you feel like doing so.