USB Oblivion, Erase Your PCs Device Connection History
Windows keeps a record of all USB devices that have been connected to the computer in the past. The records are stored in the Windows Registry, and programs like USB Deview display them directly in their interface.
Sometimes you may want to erase information about devices that have been connected to the PC in the past. It is a privacy issue for most users, but there may be other reasons as well.
Maybe you do not want your boss to find out that you connected your mobile phone to the work PC to update it, or copy mp3s from the phone to the work computer.
USB Oblivion is a free portable program for the Windows operating system that can erase all USB-related connection records from a PC it is started on.
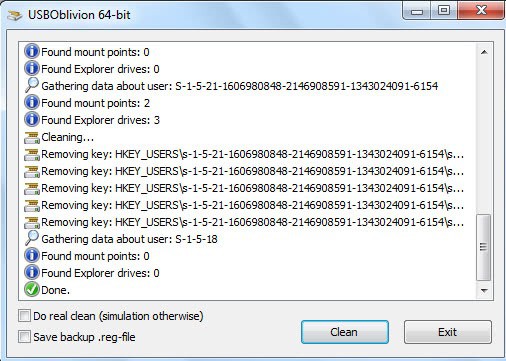
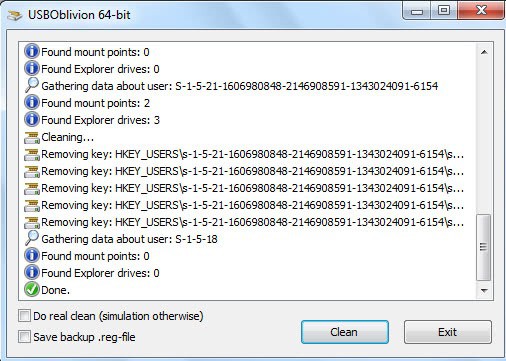
The program offers to simulate the deletion of data first. This basically displays all steps that would be undertaken by the program if it would not be run in simulation mode. That's useful to figure out which changes are made to the system when the program is run in real mode.
You need to check the "do real clean (simulation otherwise) box in the program interface to delete the USB device traces permanently on the system.
The author recommends to eject all flash drives before the program is run to avoid data loss or other issues. USB Oblivion will create a Registry backup file before the information are deleted, so that it is possible to restore the information at a later time if necessary. All you need to do then is to double-click the Registry file to import the information again.
The application is compatible with 32_bit and 64-bit editions of the Microsoft Windows operating system. Interested users can download the program from the project's Google Code page.
While most users will run the GUI version of USB Oblivion, you can also run it from the command line instead. This can be useful if you want to use it in scripts for example, or create a quick shortcut on the desktop or another location to run it unattended.
The most important parameters are the following ones:
- -enable will run in real mode and not simulation.
- -silent will run in hidden mode.
- -auto runs automatically without user interaction.
- -? displays the help file with all commands.


























did entry in system registry and log ? when run usbbaloin
thanks
This is such a wondeful spftware, since i copy a lot of files and data from my Friends PC. the USB would get stuck after reaching half the amount of it copying procedure.
This happened a lot of time:
But after using this tool it was huge relief, it was like i h’ founded a secret tool.
CHEERS
More information about the Windows keeps a record of all USB devices that have been connected to the computer in the past. The records are stored in the Windows Registry, and programs like USB Deview display them directly in their interface.
For even more “ghost” devices, which what these old USB devices get called, try Ghostbuster http://ghostbuster.codeplex.com/
Companies with medium-size and larger networks usually put users’ profiles and program files on a server and download them to the local machine each time a user signs on. Among other things, this lets a user sign on seamlessly to any computer in the network.
The Registry resides on the server, and any competently set-up system will prevent users from editing files on the server. Therefore you can’t use USB Oblivion to remove evidence of the connection of unauthorized devices.
In fact, an attempt to edit a file on the server will raise an alarm in the IT center, which is sure to get you in trouble. It’s less unsafe (to you) to let the system keep its records and take the smaller risk that someone in IT will decide to check them.
Here’s one more. But a command line utility:
http://www.uwe-sieber.de/drivetools_e.html#drivecleanup
shine