Stuxnet Rootkit Remover
Stuxnet is family of new threats that have emerged in mid July 2010. The majority of infected computer systems are located in Iran, Indonesia, India and the US
The rootkit is distributed by direct attacks, email, infected executable files and the recently discovered lnk shortcut security vulnerability in Windows.
Stuxnet uses the aforementioned .lnk technique to install additional malware components.
It first injects a backdoor (Worm:Win32/Stuxnet.A) onto the compromised system, and then drops two drivers:
Trojan:WinNT/Stuxnet.A - hides the presence of the .lnk files
Trojan:WinNT/Stuxnet.B - injects (formerly) encrypted data blobs (.tmp files) into memory, each of which appear to serve different purposes as the Stuxnet deployment system infrastructure (drivers, .lnk files, propagation, etc.).
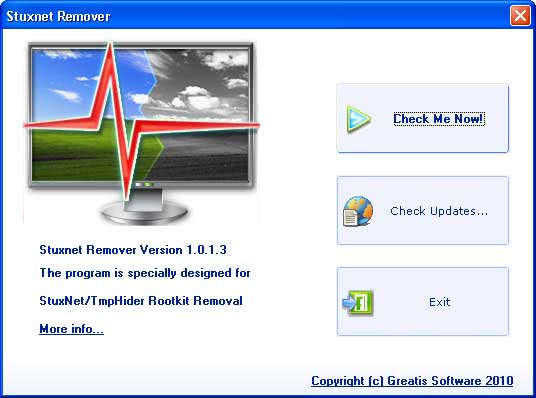
Stuxnet Rootkit Remover
Stuxnet Rootkit Remover has been designed to detect and remove active infections on Windows systems. The software scans the system for infected files including the ones listed below
C:\WINDOWS\system32\drivers\mrxcls.sys
C:\WINDOWS\system32\drivers\mrxnet.sys
C:\WINDOWS\inf\mdmcpq3.PNF
C:\WINDOWS\inf\mdmeric3.PNF
C:\WINDOWS\inf\oem6C.PNF
C:\WINDOWS\inf\oem7A.PNF
The software detects and removes malicious LNK and TMP files stored in removable media as well if removable devices are connected to the PC at the time.
~WTR4132.tmp
"Copy of Copy of Copy of Copy of Shortcut to.lnk"
"Copy of Copy of Copy of Shortcut to.lnk"
"Copy of Copy of Shortcut to.lnk"
"Copy of Shortcut to.lnk"
~WTR4141.tmp
The program needs to be installed before it can be started.
The Check Me Now button in the main interface scans the system for active infections, and removes infected files if any are found on the PC.
The video demonstrates how the program is used.
Many antivirus solutions detect Stuxnet variants by now including the free Microsoft Security Essentials. Stuxnet Remover however is a handy tool if the computer has already been infected with the malicious software. It also serves the purpose of detecting the rootkit if it is already on the computer system.
Stuxnet Remover is available for download at the developer's website. The rootkit scanner is compatible with all Microsoft operating systems from Windows XP to Windows 7.
The project page states that it only supports 32-bit editions, but it tested fine on a 64-bit system but may not be fully compatible with 64-bit versions of Windows.























P.S
Microsoft has issued a special out-of-band fix for August 2.
http://blogs.technet.com/b/msrc/archive/2010/07/29/out-of-band-release-to-address-microsoft-security-advisory-2286198.aspx
Thanks, good to know!
Tjis is a very small partly solution as the family of Trojans/Rootkits having a ball is large (late to the party is the well known bank robber Zeus Botnet)
Malicious links exploiting CVE-2010-2568
Exploit:Win32/CplLnk.A
Exploit:Win32/CplLnk.B
Stuxnet
TrojanDropper:Win32/Stuxnet.A
Trojan:WinNT/Stuxnet.A
Trojan:WinNT/Stuxnet.B (initially called
VirTool:WinNT/Rootkitdrv.HK)
Trojan:Win32/Stuxnet.A
Worm:Win32/Stuxnet.A
Worm:Win32/Stuxnet.B
Sality
Virus:Win32/Sality.AU (initial detection provided by
generic signature Virus:Win32/Sality.AT)
Vobfus
Worm:Win32/Vobfus.H
Worm:Win32/Vobfus.P
Chymine
Trojan:Win32/Chymine.A
TrojanSpy:Win32/Chymine.A
TrojanDownloader:Win32/Chymine.A