Microsoft: Windows 10 makes EMET unnecessary. Study: Nope
Microsoft plans to discontinue support for its Enhanced Mitigation Experience Toolkit in July 2018, and won't release a new version of EMET either.
This makes EMET 5.51 the last release version of the anti-exploit security software for Windows. The reason given by Microsoft was that Windows 10, Microsoft's new operating system, includes all the mitigation features "that EMET administrators have come to rely on" as well as new mitigations that are not part of EMET.
Microsoft stated openly that Windows 10 includes security features so that it is no longer necessary to run EMET (and thus for Microsoft to support it).
Windows 10 and EMET
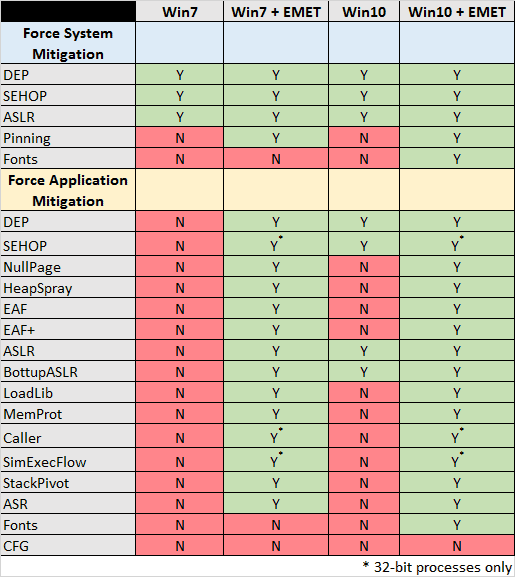
EMET protection is divided into system-wide protection, and application-specific protection.
Data Execution Prevention (DEP), Structured Exception Handler Overwrite Protection (SEHOP),
Address Space Layout Randomization (ASLR), Certificate Trust (Pinning), and Block Untrusted Fonts (Fonts) fall in the first group.
Data Execution Prevention (DEP), Structured Exception Handler Overwrite Protection (SEHOP), Null Page Allocation (NullPage), Heapspray Allocations (HeapSpray), Export Address Table Access Filtering (EAF), Export Address Table Access Filtering Plus (EAF+), Mandatory Address Space Layout Randomization (ASLR). Bottom-Up Randomization (BottomUpASLR), ROP Mitigations (LoadLib,
MemProt, Caller, SimExecFlow, StackPivot), Attack Surface Reduction (ASR) and Block Untrusted Fonts (Fonts) in the second group.
Will Doorman at Carnegie Mellon University's Software Engineering Institute created the following table that lists for each mitigation whether it is included in Windows 7 or 10, or in Windows 7 or 10 with EMET installed.
If you look at the table, you will notice quickly that vanilla Windows 10 does not offer the same level of protection as Windows 10 with EMET running.
The same can be said for the comparison of vanilla Windows 10 and Windows 7 that is running EMET.
While it is true that Windows 10 supports several application mitigations out of the box so to speak, DEP, SEHOP, ASLR and BottupASLR to be precise, it is clear that the operating system does not include all protective features that EMET offers. Protective features in this regard mean application mitigations such as HeapSpray, EAF, MemProt or ASR.
As far as the supported options by Windows 10 are concerned, they are not enabled by default and need to be enabled in the Group Policy Editor.
The researcher comes to the conclusion that Microsoft's implication that users don't need EMET if they run Windows 10 is not true.
Microsoft strongly implies that if you are running Windows 10, there is no need for EMET anymore. This implication is not true. The reason it's not true is that Windows 10 does not provide the application-specific mitigations that EMET does.
He notes furthermore that Windows 10 does ship with additional protective measures, but that programs need to take advantage of them, and that this does not account for all the protective measures that EMET offers.
His recommendation is to use EMET if possible and if application-specific mitigations are configured by system administrators or users. If that is not possible for whatever reason, the next best thing is to configure mitigations that can be applied to Windows 10 without EMET. (via Deskmodder)
Alternatives to EMET are Malwarebytes Anti-Exploit (also available in Malwarebytes Premium), and HitmanPro.Alert.
Now You: Do you run anti-exploit software?




















ProcessExplorer (sysinternals) says that nearly all processes on my W7 run with ASLR. According to the graph they should not?
Yeah, I’m a bit puzzled too. Almost all my process have ASLR. Maybe they tested Win7x86?
how can I use EMET on windows 10?
The latest version of EMET that has been released is compatible with Windows 10. Simply install it and configure it as you would do on previous versions of Windows.
I think part of the reason for EMET retirement is b/c MS wants users to use MS products that conveniently take advantage of Windows 10 built in migrations. There is currently no equivalent free alternative, MBAE and Hitman free versions have crucial features behind a pay subscription.
I will continue to use EMET until it is doesn’t work anymore or it becomes a liability. I would not be surprised if MS purposely breaks EMET compatibility with a future Windows 10 update. Windows 7 and 8 will probably work with EMET for the rest of its EOL though at the very least b/c MS obviously wants users to move on from those versions and probably won’t bother to break EMET on those
I hope MS open sources EMET so that someone takes over who wants to continue development or at least create maintenance updates. From what I read EMET is just a convenient GUI that takes all those settings that can be individually enabled manually if you know what you doing. I think that what MBAE and hitmanpro does. If EMET is not open source, I hope some one create their own completely free version.
I believed the propaganda spouted by Microsoft on W10’s superior security and even repeated it. Now I am totally embarrassed.
Thanks for posting this Martin and thanks to the Will Doorman at Carnegie Mellon University’s Software Engineering Institute. That is an excellent piece of work. Everyone who uses EMET needs to see it. Having invested so much money into its development and proving it to be an absolute necessity in today’s computing environment, why are they abandoning it? They see no revenue stream, reduce costs at any cost, or have they lost the ability to recognize the value it brought to their customers.
Microsoft LYING about Windows 10?? No such thing! ;)
They didn’t lie. Windows 10 will probably add all the important features from EMET by the time Microsoft stops supporting it in 2018. And in the real world, the most likely scenario is that only a subset of EMET’s functionality is actually useful. EMET also increases the compatibility issues with software (even the popular ones) so that needs to be taken into account as well.
Yuliya, is there proof that this is the same OS for fifteen years? Sounds unbelievable to me. As a consumer, I need to rely on a companies integrity that they are standing behind their product and telling users the truth. I would think that if this was an out and out lie, they would have been called on this before. Anybody else?
Oh, really? Remember when Win10 was launched (or after each major update), Microsoft always lying about Win10 bein the most secure Windows/OS? But how come? It’s the same OS for 15+ years. It barely changed, and that’s the main reason why it is so popuar – backwards compatibility. They added layers on top of layers of fluff, but underneath it’s the same. The biggest change was Vista, which broken many things.
They can’t mitigate anything without destroying compatibility, hence why EMET will never be a part of Windows. Claming that Win10 is as good as WIndows+EMET is a big fat lie.
Claming that Win10 is in any way more secure than Win7 is fundamentally wrong. Win10 is a more complex than Win8; which Win8 is a more complex OS than Win7. A more complex OS means more surface to attack. And allways, complexity will beat security.
Here I’m running HitmanPro.Alert, hoping it would prove efficient should it encounter a nasty intruder. By the way I admire the developer’s patience when he has to deal over at Wilders Security Forums with users who aim at adding the application with other similar tools such as EMET and encounter problems, day month year after year and complain the same. Between no protection and an army’s help to cross the road, the diversity of human nature.
Concerning Microsoft’s statement regarding Windows 10, as usual the day’s lot of blabla. The company must have a brain-storming staff dedicated at one sole purpose : find, find, invent, imagine, anything, true or not, as long as it improves the image of Windows 10.
Thank you, Will Doorman from Carnegie Mellon University’s Software Engineering Institute for pointing a company’s approximations. And thanks, Martin, for a most valuable article as always.
It would be interesting to know whether those Application-Specific Protections would however apply to software that has been converted to UWP applications.