PSA: Raivo OTP for iOS was acquired by Mobime a few months ago
Raivo OTP, a popular authenticator app for iOS, has been acquired by a company called Mobime. The acquisition took place a few months ago, we won't be recommending the app any longer.
Why are we talking about Raivo OTP now?
Long story short, recently, I was having an issue with a feature in Raivo, and looked it up. That's when I found out that Raivo had been acquired by Mobime. Wait, what? When did this happen? Apparently, the news was "announced" via the developer's Twitter account in July this year.
Seriously? This is how you announce the news, on Twitter of all things? Why not just update the app, to show a pop-up about the news like, "Hey! We have some exciting news to share!....". Not everyone uses Twitter, right? And that's not even where I found out about it, I stumbled about it on a reddit post.
If someone who is tech-savvy as me found this out months later, I wonder how many other users have yet to hear of this acquisition, which is why I'm writing this post to make people aware about the change.
Such acquisitions almost never benefit the user. We have seen that happen with Nova Launcher which was acquired by Branch, Avast's acquisition of Piriform CCleaner and the I don't care about Cookies browser extension, and most recently with Simple Mobile Tools which was acquired by ZipoApps.
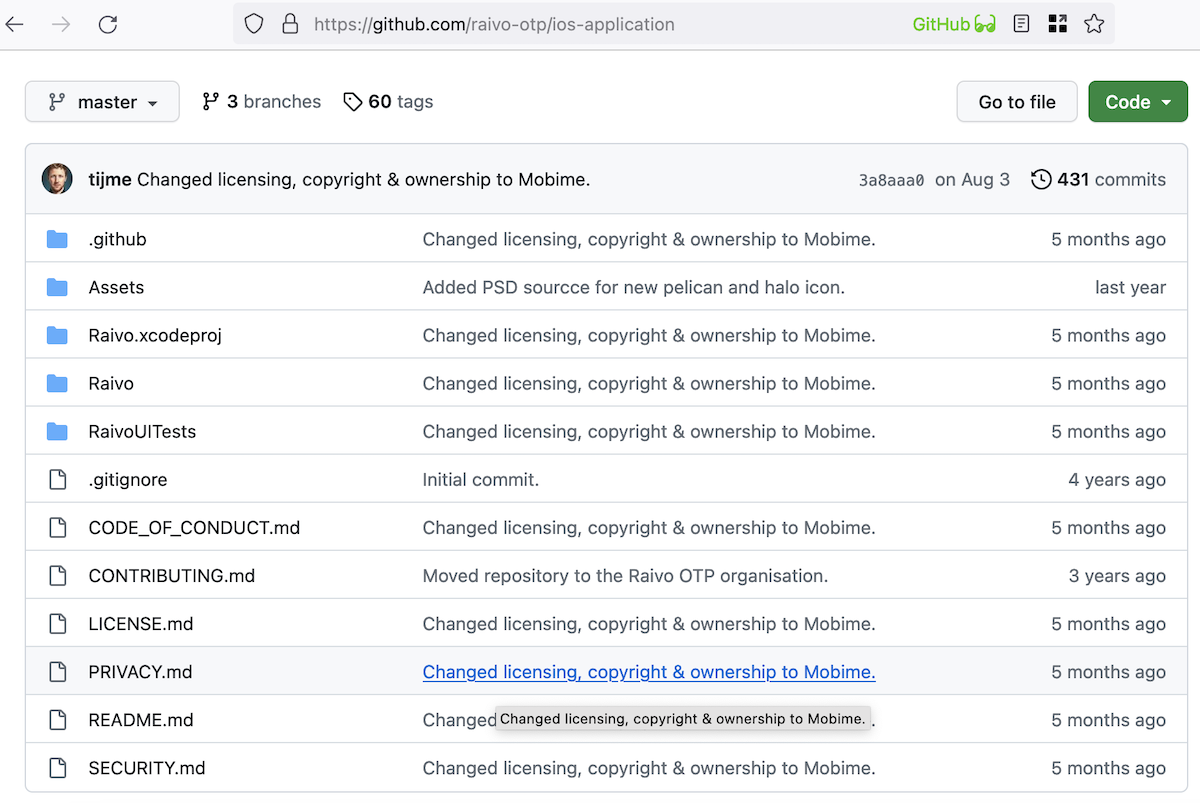
Raivo OTP remains open source, but I honestly can't tell what has changed in the background. This is what a comment from the original developer, Tijme Gommers, says about the situation.
It seems like Mobime has taken over the app, but has not made an official announcement about it. Here's the company's catalog of apps for iOS, iPadOS and macOS. Quite a few of those have expensive in-app purchases. Mobime's privacy policy is available on the company's website. Raivo's privacy policy is available here. The last commit to the app's GitHub repository is from August 3, the same date, when Gommers posted the above comment. Yeah, that is not very convincing, is it? While we have no evidence of malicious intent with Raivo, I think some users would agree that it is not wrong to hit the panic button. It's time to move on. If you disagree, well, that's your choice.
For those of you who are worried, the first thing to do is get your data from Raivo's app. So don't delete it yet.
How to export your 2FA tokens from Raivo OTP
1. Open Raivo OTP and tap on Settings.
2. Select "Export OTPs to ZIP Archive."
3. Choose an offline folder using Files. e.g. Downloads.
4. Open the Files app, go to the folder where you saved the archive, and extract it using the password that you had set in Raivo. You will need the JSON file in this folder, as that's what it required to import the 2FA (two-factor authentication) tokens for your online accounts.
Note: Now, you can delete Raivo from your phone safely. Go to your iPhone Settings > tap on your profile > iCloud > Manage Account Storage. Scroll down to Raivo and delete the data from iCloud.
Where do we go from here? No, don't go to Authy, I can't really recommend it after the Twilio breach. I'm not particularly a fan of Google Authenticator and Microsoft Authenticator, mostly due to privacy concerns.
I have done some research about some other authenticator apps, and have found that there are 2 popular alternatives for Raivo. They are ente, and 2FAS.
ente Auth
ente Auth - 2FA Authenticator, is a free, open source app. It is a cross platform app, i.e. it is available on both iOS and Android. The app's interface is quite good, but lacks a grid view. It's so annoying to scroll a list of accounts, well, thankfully the search bar makes this a bit easier.
But let's set it up from scratch. ente will offer to set up the app as a new user, or an existing user. Choosing the former, asks you to create an account. The good news is, you can skip this requirement, and use it offline. The downside with that is you cannot have online backups without an account. It's not like you're going to be adding new accounts every day, just export a backup and put it in a password-protected archive, and upload it to a cloud drive of your choice, or store it locally.
We are going to use the option that says "use without backups". This will let you scan a QR code to add accounts, or to enter a setup key. If you're migrating from a different app, select "Import Codes". It supports plain text, ente Encrypted file, Raivo OTP, Aegis Authenticator, and Google Authenticator.
Select Raivo OTP, and browse to the folder that has the JSON file that you extracted. That's it, ente is ready to use. If you want to set up 2FA for more accounts, just tap on the + button in the bottom right corner, and use the QR code option to scan a code with your iPhone camera.
Note: I also tested ente on Android, and it works similar to the iOS version.
Download ente Auth - 2FA Authenticator from the Google Play Store or F-Droid, or the iOS App Store. The app's GitHub can be found here.
Pros
- Free and open-source
- Available for iOS and Android
- Easy to import tokens from other apps
- Supports FaceID
- Can export data to an encrypted text file.
Cons
Need to sign up for an account for online backups (not required to use the app).
2FA Authenticator
2FA Authenticator also called 2FAS, is another free, open source app that you can consider. Like Ente, 2FAS is also cross-platform, you can download it for iOS or Android. The interface is aesthetically pleasing, and while there is no grid view, it does have an option for a compact view.
Like ente, 2FAS has an easy way to import your 2FA tokens to its app. It supports Aegis, Raivo OTP, LastPass, Google Authenticator, andOTP, and Authenticator. To import the data from Raivo, tap on the option that says Raivo, and select the JSON file that you extracted.
2FAS has a cool feature, it has a browser extension that acts as a companion to the mobile app. Install it and pin the icon to your browser's toolbar. You will need to use the 2FAS mobile app to scan a QR code displayed by the browser add-on, to pair them. App > Settings > Browser extension > Pair with Web Browser.
Once you have done that, sign in to a website that you have enabled 2FA for. When the site asks you to enter the TOTP, just click on the browser extension's button. This will send a push notification to your phone. Tap on it, and select the site from the list, and it will autofill the 2FA code on the page. That's pretty cool, you don't have to manually type the TOTP.
According to some comments by the developers, 2FAS iCloud Backup is not end-to-end encrypted completely even when Advanced Data Protection is enabled, i.e. it does not encrypt some fields. The problem here is that iCloud Backups are enabled in the app by default. I just disabled the cloud backup in 2FAS and use it. You can do that even before setting up your account tokens in the app.
I also recommend disabling the Crash reports, which are also enabled by default. The option can be found under Settings > About > Send anonymous crash reports. That's an odd place to put that option.
Download 2FA Authenticator (2FAS) from the Google Play Store, or iOS App Store. Get the browser extensions for Chrome, Safari and Firefox. The apps' source code can be found on GitHub.
Pros
- Free and open-source
- Available for iOS and Android
- Web browser extension
- Easy to import tokens from other apps
- Beautiful UI
- Can export backup (. 2FAS format)
Cons
- Online backups are enabled by default.
- Crash analytics are enabled by default.
- Backups are not completely end-to-end encrypted (can disable online backups).
- 2fas has some optional NFT. Some users may not like that.
The 2FAS app is highly regarded by many privacy enthusiasts, even among the Bitwarden community. Speaking of which, you could use Bitwarden for TOTP too, but it's not free. Besides, personally, I would prefer to use an offline authenticator app for 2FA codes, and also not use the same app for TOTP and passwords. Use 2 apps, each with a different password / passcode.
Which one is better?
That is a difficult question, one which comes down to personal choice. You can't go wrong with either one. As for me, I like 2FAS more because it has a better interface, and the browser add-ons are quite convenient to use.
If you read my article about the best authenticator apps for Android and iOS, you may be aware that I was a big fan of Raivo OTP. I used Raivo for everything, including my work accounts, finding that an app that you trust so much has been sold quietly is honestly a nightmare.
Thanks for the tutorial.
Hi Ashton, I think your preference for 2FAS is further supported by the iOS App Privacy section nutrition labelling.
2FAS only collects diagnostics (plus has a much larger number of users on iOS).
Whereas, ente Authenticator iOS App Privacy nutritional labelling advise confirms that it collects: Contact Info + User Content + Identifiers. Ente does not have the user base either – there are not nearly as many iOS users when compared with 2FAS.
I really appreciate your informative article, as I was wondering why privacy forums such as Privacy Guides no longer list Raivo anymore and now I understand why. Thank you ?
So on a Privacy basis, 2FAS is much better for your privacy ?
Can’t import the zip into ente Auth directly. Have to unzip beforehand, but the file doesn’t accept my Raivo-code??? Tried many times but it doesn’t work….
You need to use the JSON file that you extracted from that ZIP archive.
Thanks for the heads up Ashwin. 2FAS looks like a good option.
Any idea if’s export function uses a standard JSON file or is it some proprietary option? In case would like to migrate elsewhere in the future.
Thanks
Tom, the app saves it in a .2fas format which is protected by a password. But I can use the file to import the tokens in it to Ente by providing the password.
Much appreciated!