Mozilla starts to enable TLS 1.3 on Firefox Stable
Eagle-eyed Firefox users and administrators may have noticed that Mozilla dropped a new system add-on on systems running the stable version of Firefox recently.
First spotted by Bleeping Computer creator Lawrence Abrams, the add-on's only purpose is to enable support for TLS 1.3, the next major Transport Layer Security protocol version.
TLS 1.3 is considered to be faster and more secure than previous versions of the protocol. The new protocol version was finalized on March 21, 2018 and it needs to be supported by web browsers and Internet services.
Firefox users who run beta or nightly versions of the web browser may know that TLS 1.3 is enabled in those versions already.
Tip: you can manage TLS 1.3 manually in Firefox (and Chrome).
TLS 1.3 on Firefox Stable
Mozilla rolls out the system add-on gradually to the Firefox Stable release channel population. The organizations started with 10% of the population and monitored the effect closely.
The current level of distribution reached 50% of the entire population.
Check if TLS 1.3 is enabled
While you can check for the existence of the system add-on on about:support as it is listed under Firefox Features on the page, you may also do the following to verify the maximum TLS version in Firefox:
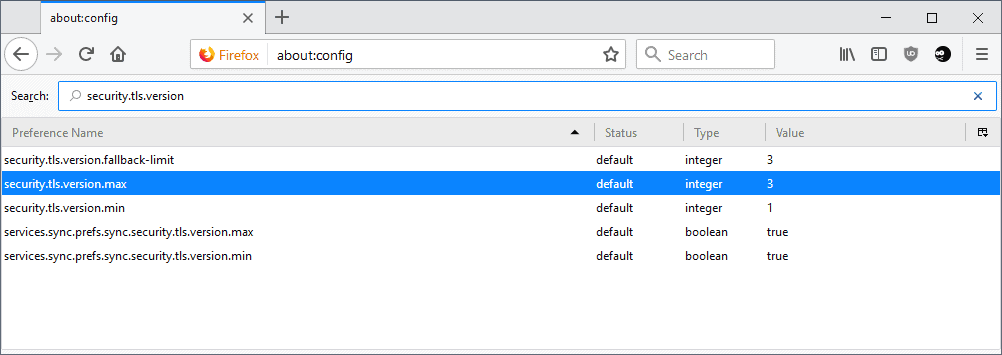
- Type about:config in the browser's address bar and load the internal address.
- Confirm that you will be careful if a warning message is displayed.
- Search for security.tls.version
The preference security.tls.version.max determines the highest TLS protocol level that Firefox supports actively. If it is set to 3, TLS 1.2 is support. The system add-on raises the value to 4 which in turn adds support for TLS 1.3 to the web browser.
Tip: you can raise the level manually right away if it is set to 3. Just double-click on the preference and change the value to 4 to add support for TLS 1.3 to Firefox right away.
You can run a check for supported protocols and security features on SSLLabs. You should notice that TLS 1.3 is supported by the browser if the security.tls.version.max preference is set to 4.
Google Chrome Stable supports TLS 1.3 by default as well already. Mozilla's rollout will reach the entire Firefox Stable population eventually so that all versions of Firefox that are supported by the organization support the new protocol version.
Interested users can follow the rollout on Bugzilla.
Chrome Version 66.0.3359.106 (Official Build) beta (64-bit) TLS 1.3 Default.
I’ve enabled TLS 1.3 for some time now here on Firefox (security.tls.version.max = 4) and encountered very few domains inaccessible and for those, I skip them. Either a site sticks on plain non-encrypted http, either if follows the best encryption available.
Having a system add-on just for that surprises me but after all, understandable.
Users have to be, IMO, demanding in terms of privacy and security and behave accordingly. Respectful with the admins, gentle and kind, but demanding: some lazy places just won’t optimize as long as long as users seem to not care and start moving when they check their logs and correlate their security practice to the number of defections.
Running stable Firefox (59.0.2 – 64 bit) on an old Linux Mint, my about:config shows :
security.tls.version.min;1
security.tls.version.max;4
security.tls.version.fallback-limit;3
ssllabs.com shows my browser is TLS 1.3 compatible, of course.
If you look at Mozilla’s telemetry, only about 1.5* % of traffic is lower than TLS 1.2
see: https://github.com/ghacksuserjs/ghacks-user.js/issues/167
That was 9 months ago. If you take the metrics link in the first post, and change the value from Nightly56 to Nightly60 (the dates will auto change) – i.e click the nightly link and drop down appears .. then the current values indicate that approx 0.91% now uses lower than TLS 1.2
Since I set my minimum pref value as 3 (i.e TLS 1.2) about 9 months ago, I have only ever encountered about 3 or 4 sites that I could not load due to this (I just flicked them open in a secondary browser). These were sites I came across whilst researching – old PoCs, stuff like that – definitely not mainstream everyday sites.
I think Chrome and Mozilla flip these sorts of things when samples get down to about 0.3% or lower (because even 0.3% is still tens of millions of breakages, and no one likes to blink first for bad experiences). Be a trend setter, and hang out with us cool kids :) block TLS1.0 and 1.1 .. go on… you can do it