Latest Posts
See allBrave Search: Answer with AI takes over, but you can turn it off
Brave Search's new Answer with AI feature is now available. The feature replaces AI Summarizer, which was used on Brave Search previously to provide summaries based on user queries. In a nutshell: […]
Dear Microsoft, why cannot I uninstall Microsoft Edge on Windows?
It is April 2024. The deadline for compliance with the Digital Markets Act was in March 2024. Still, even with all the latest updates installed, I cannot uninstall Microsoft Edge from any […]
Proton acquires encrypted note-taking app Standard Notes
Proton has announced that it has completed the acquisition of the encrypted note-taking app, Standard Notes. The company says that the privacy-focused Proton has been expanding its portfolio steadily overtime, evolving from […]
Disney Plus' password-sharing crackdown begins in June
Disney CEO Bob Iger has confirmed that the company will start implementing new rules to prevent users from sharing their accounts with other people. Disney Plus' password-sharing crackdown will begin in June. […]
Brave
See all articles
Brave Search: Answer with AI takes over, but you can turn it off
Brave Search's new Answer with AI feature is now available. The feature replaces AI Summarizer, which was used on Brave Search previously to provide summaries based on user queries. In a nutshell: […]
Brave no longer installs VPN Services on Windows for everyone
Brave Software released a new stable version of the company's web browser this week. Besides more AI and several improvements, it is also introducing a change regarding the installation of VPN services […]

Brave Browser 1.63 launches with vertical tabs on right support and more AI
Brave Software released a new version of its Brave Browser to the public. Brave Browser 1.63 includes several new features and improvements of existing features. Highlights include that vertical tabs may now […]

Brave Browser 1.62: strict fingerprinting protection and HTTPS Everywhere changes
Brave Software released a new stable version of Brave Browser earlier today. Brave Browser 1.62 is a feature and security update for the Chromium-based web browser. The update is available already and […]
Microsoft Edge
See all articles
Dear Microsoft, why cannot I uninstall Microsoft Edge on Windows?
It is April 2024. The deadline for compliance with the Digital Markets Act was in March 2024. Still, even with all the latest updates installed, I cannot uninstall Microsoft Edge from any […]

Microsoft Edge fixes 0-day vulnerability: confirms all Chromium-based browsers vulnerable
Microsoft released a security update for its Edge web browser that address several security issues, including one that is exploited in the wild. Google released security updates for its Chrome web browser […]

You can now zoom images easier in Microsoft Edge thanks to new Magnify feature
Microsoft added a new feature to its Edge browser recently that improves how you zoom images in the browser. Most websites restrict the width of content and this impacts images as well. […]

Microsoft Edge's latest AI tool sends open websites to Microsoft
Microsoft Edge's latest AI feature helps users put open tabs into groups for improved management. Tab Groups, introduced in Microsoft Edge in 2021, is a useful feature to improve tab organization in […]
Vivaldi
See all articles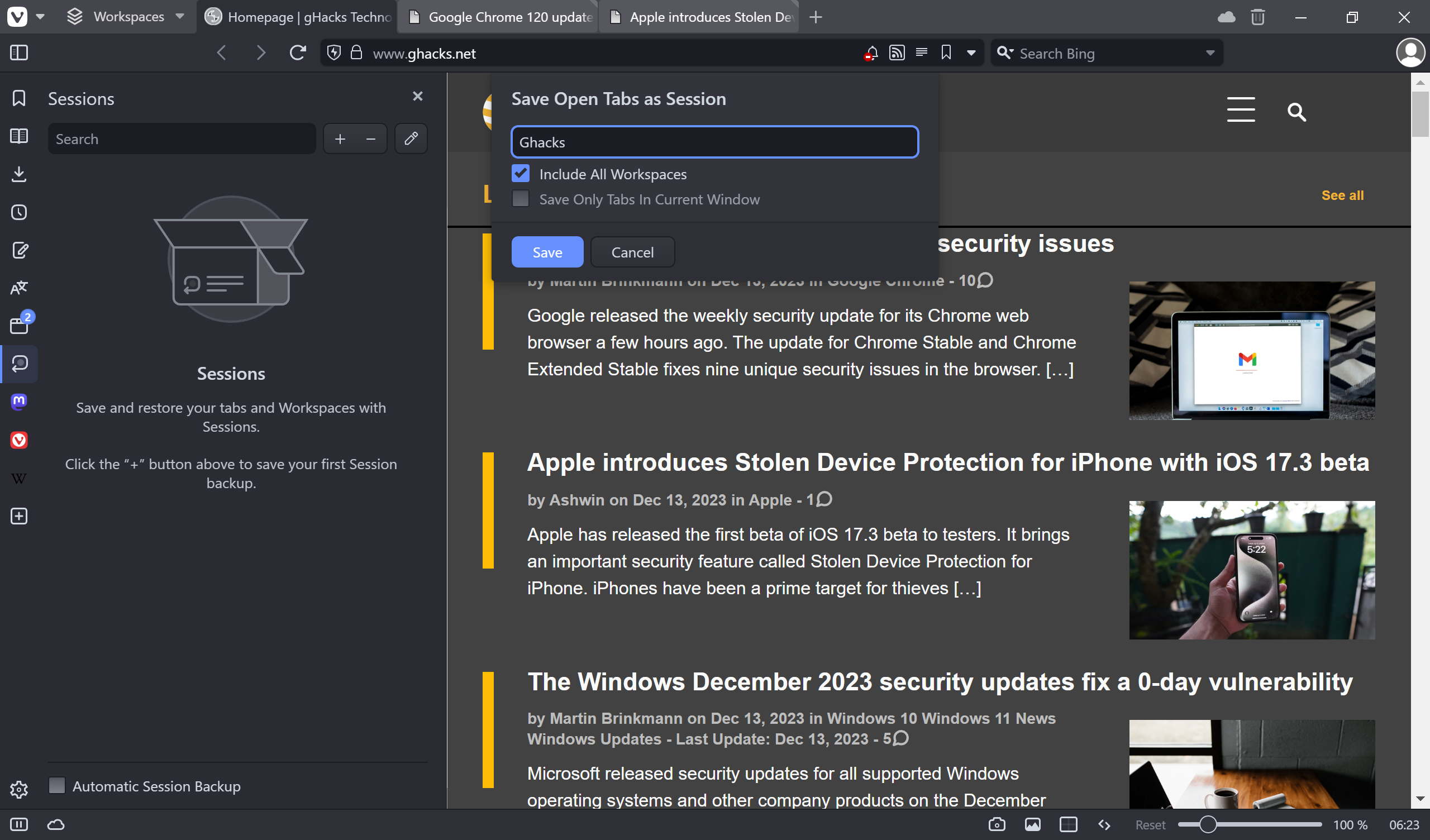
Vivaldi update brings Session Panel, full History sync and more
Vivaldi Technologies has just released a new major version of the Vivaldi web browser for desktop and notebook operating systems. The latest major update of 2023 is packed with new features that […]

Vivaldi Browser 6.4 released with address bar, popout video and calendar improvements
Iceland-based Vivaldi Technologies released Vivaldi 6.4 for all supported platforms today. The new version of the Chromium-based web browser adds volume controls to its popout video feature, gives users more control over […]

Vivaldi for iOS and iPadOS released
Vivaldi for iOS and iPadOS has been released, after a beta testing period of four months. Let's take a closer look at the browser. In case you missed it, I reviewed the […]

Vivaldi says no to Google Topics in its browser
Google's euphemistically named Privacy Sandbox or Ad Privacy feature is a topic of hot debate. While it is true that it is changing tracking on the Internet fundamentally by getting rid of […]
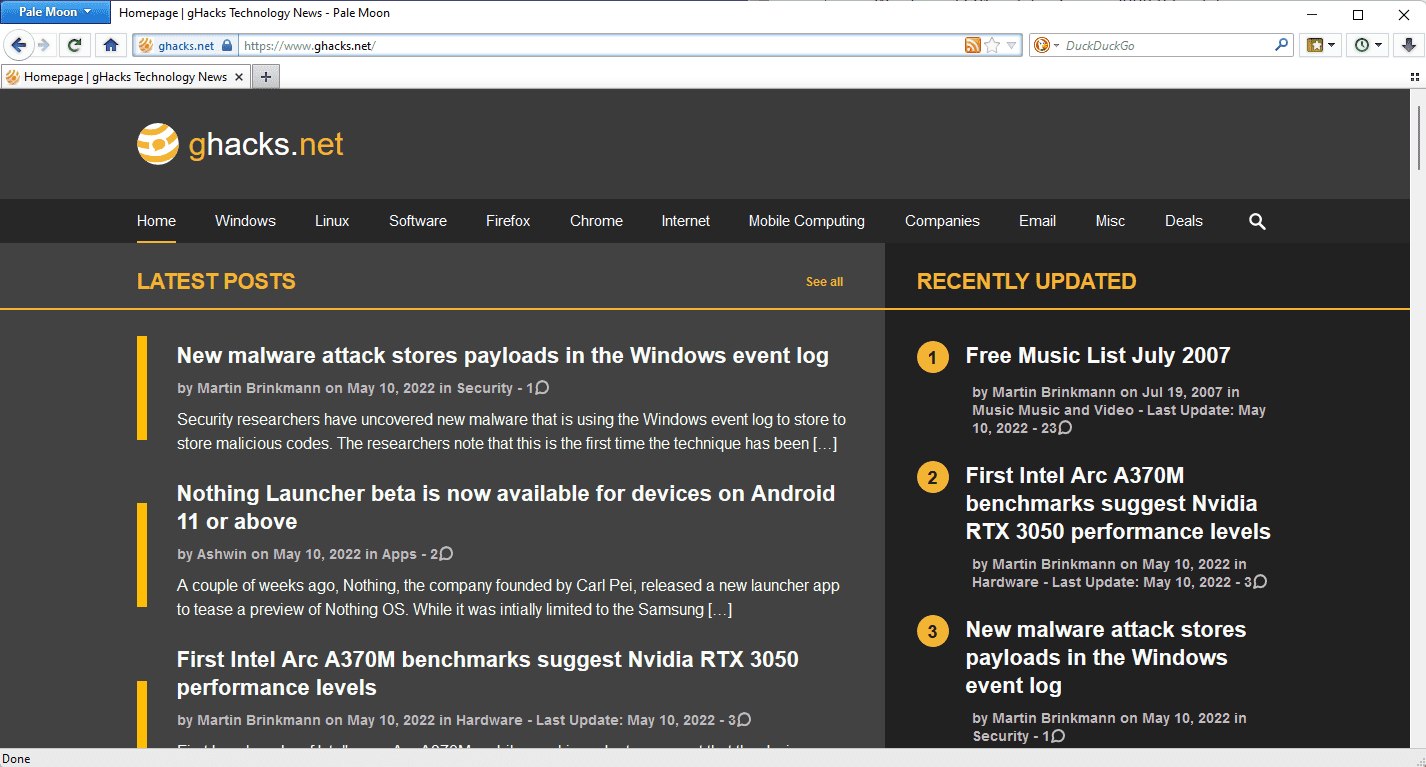
Pale Moon
See all articles
Pale Moon 32.1.0 launches with major web compatibility improvements
The developers of the open source web browser Pale Moon have released version 32.1.0. The new version is a significant release for the project, as it improves web compatibility by enabling Google […]
Pale Moon 31 is out now
Pale Moon 31 is the latest version of the desktop web browser. The new version of the browser comes after Pale Moon 29.4.6; this is done to avoid confusion regarding the Pale […]
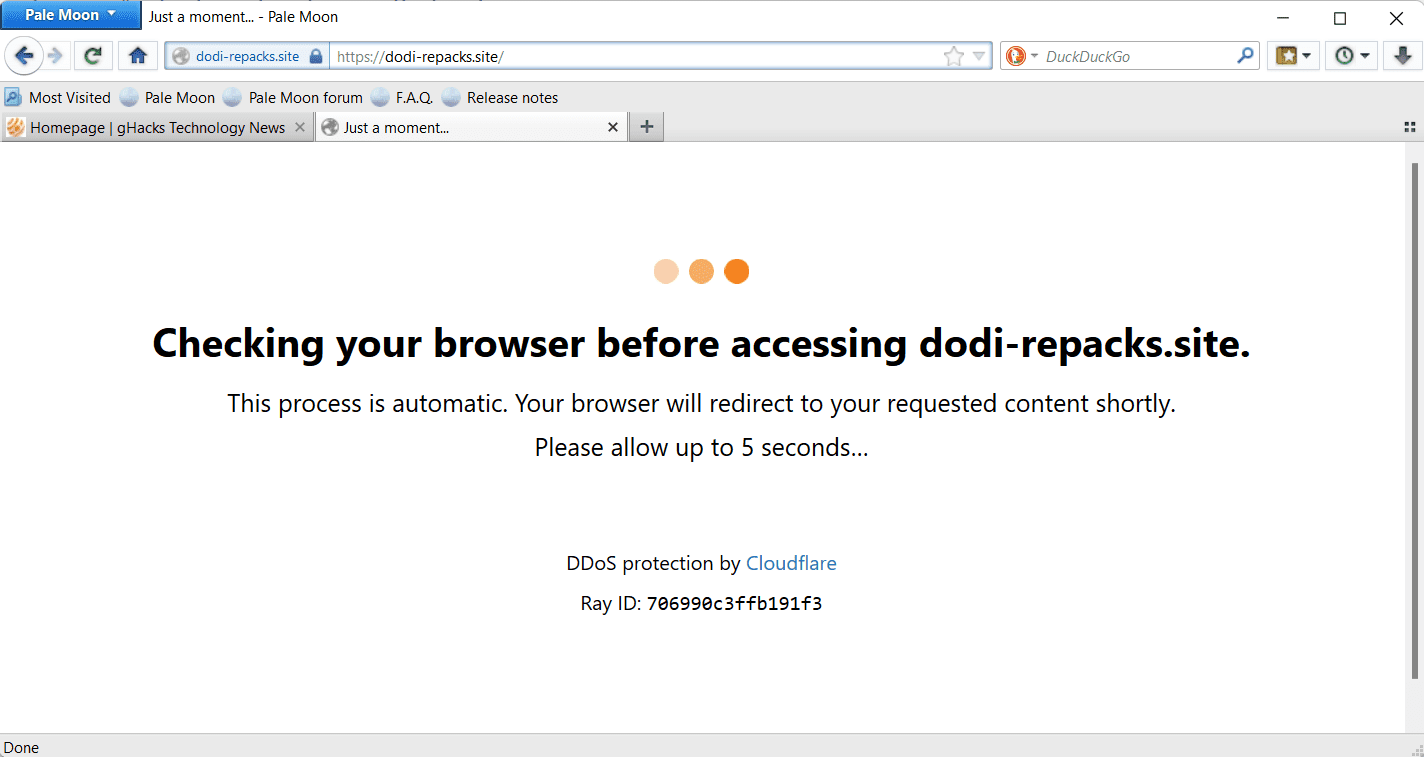
Fix Pale Moon browser not passing Cloudflare's "Checking Your Browser" verification
The Pale Moon web browser runs into an infinite "checking your browser" loop on sites that use Cloudflare's browser integrity check feature. I confirmed the issue in the latest release versions of […]
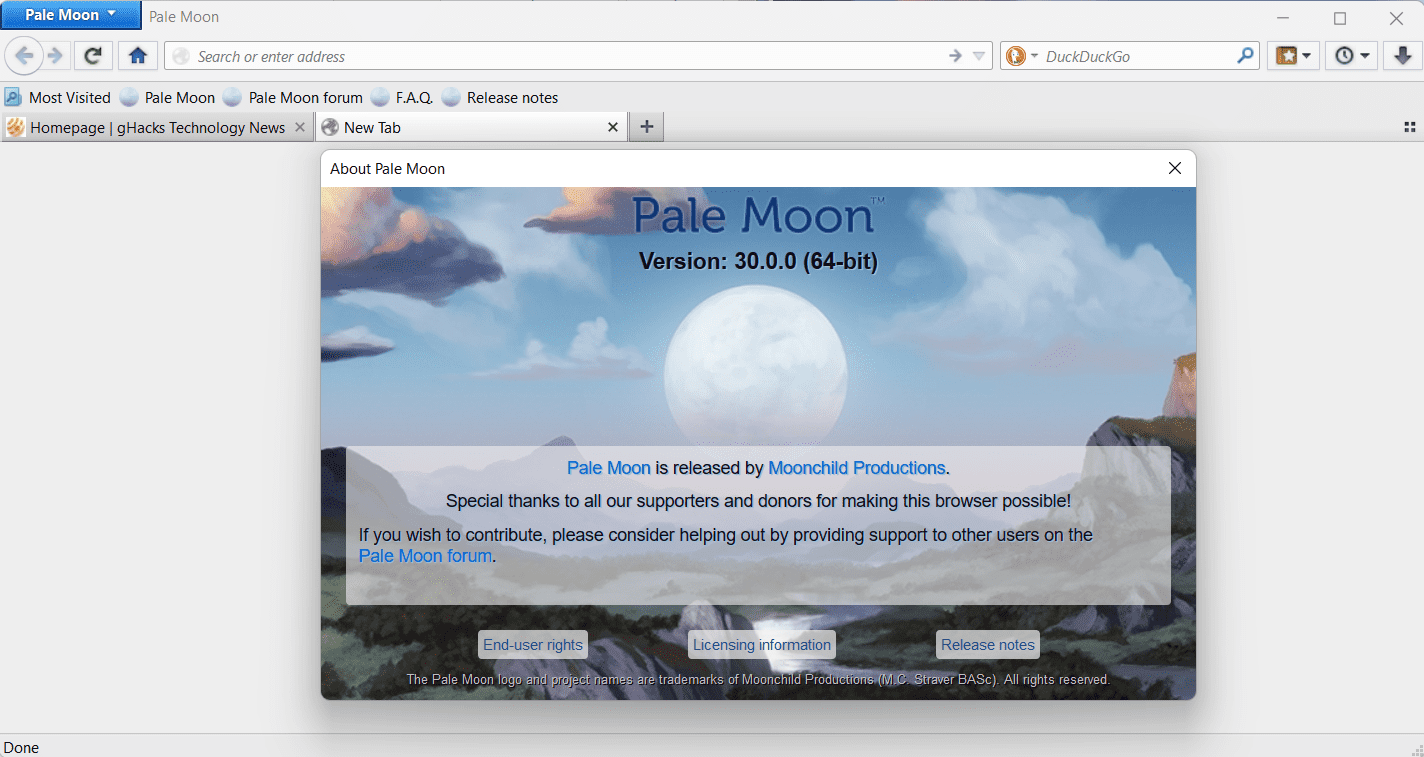
Pale Moon 30.0 out with important changes
The developers of the Pale Moon web browser have released Pale Moon 30.0 to the public for all supported operating systems. Pale Moon 30.0 is a milestone release that includes several important […]
Internet Explorer
See all articles
Internet Explorer 11 is still not dead and will live another day
Microsoft ended support for its Internet Explorer 11 browser on Windows 10 in 2022. The company then explained that it would remove the browser from Windows 10 systems, stating that it would […]
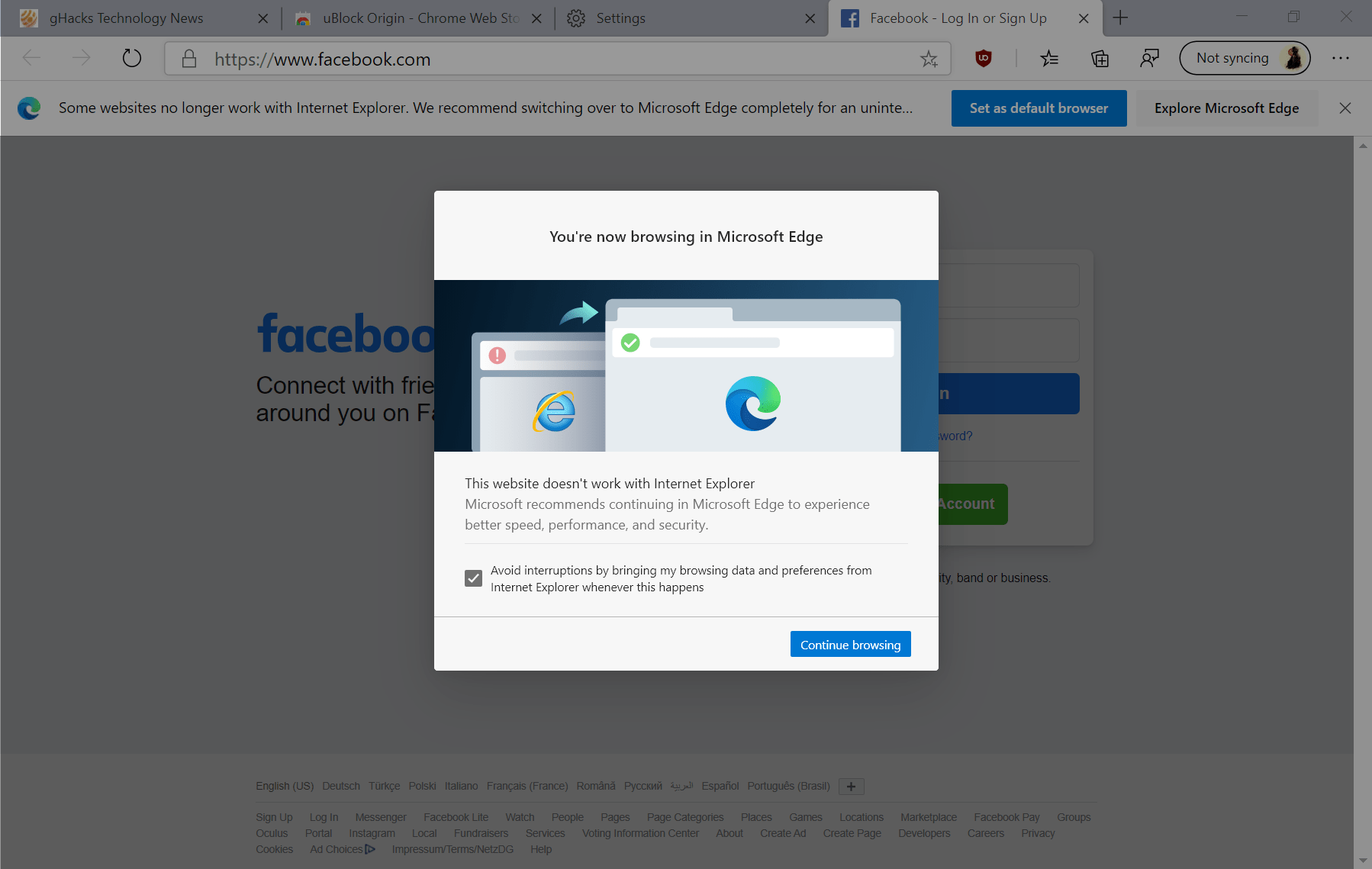
Last Call: Internet Explorer 11 to be Disabled Forever tomorrow
Any user or organisation still using Microsoft's Internet Explorer web browser on Windows 10 devices will find themselves in a precarious situation on February 14th. On February 14th, 2023, Internet Explorer 11 […]
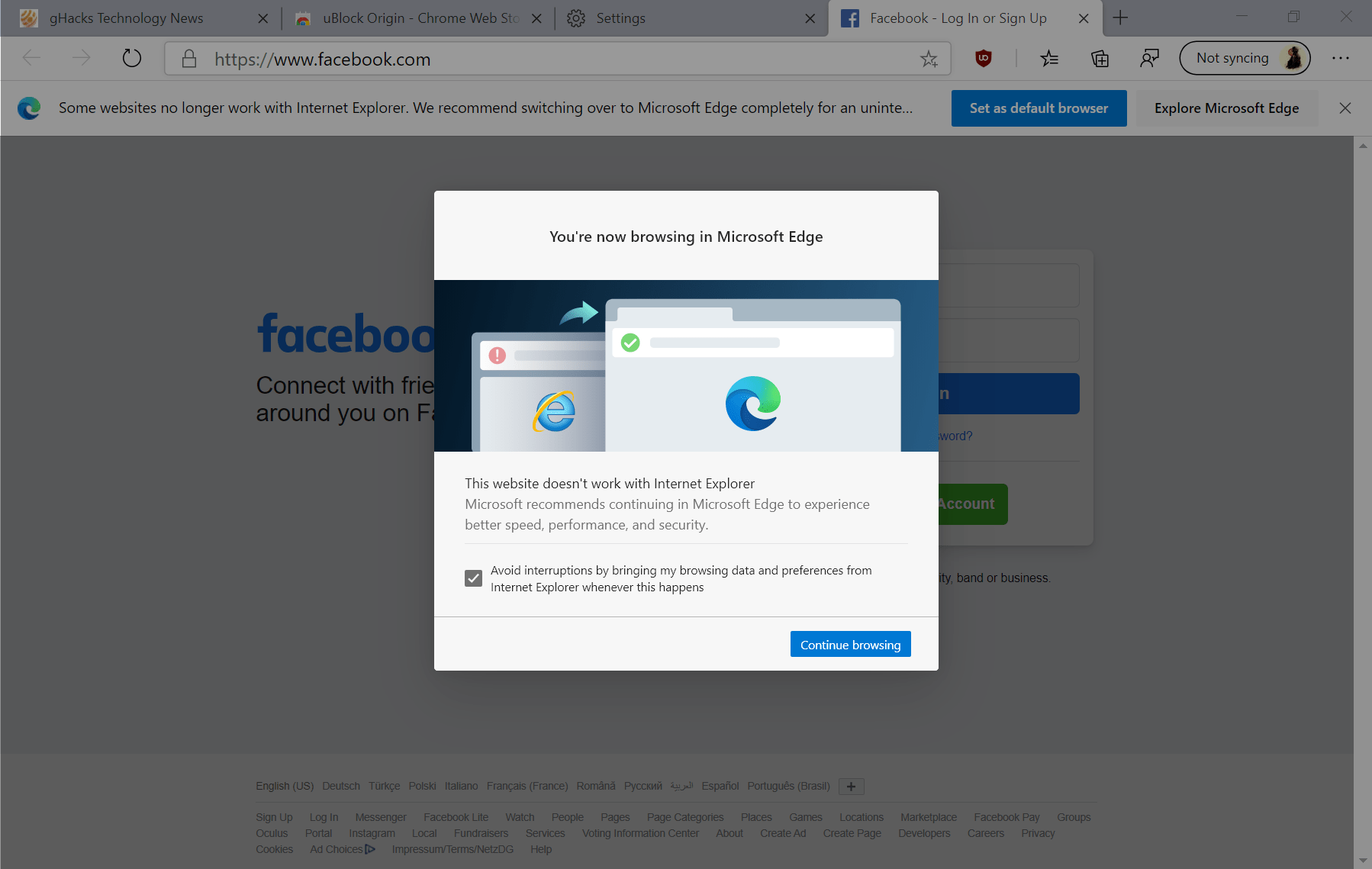
Internet Explorer will be disabled through a Microsoft Edge update in February 2023
Microsoft announced on Friday that a Microsoft Edge update that it plans to release in February 2023 will disable Internet Explorer 11 permanently on select Windows 10 systems. Internet Explorer 11 reached […]
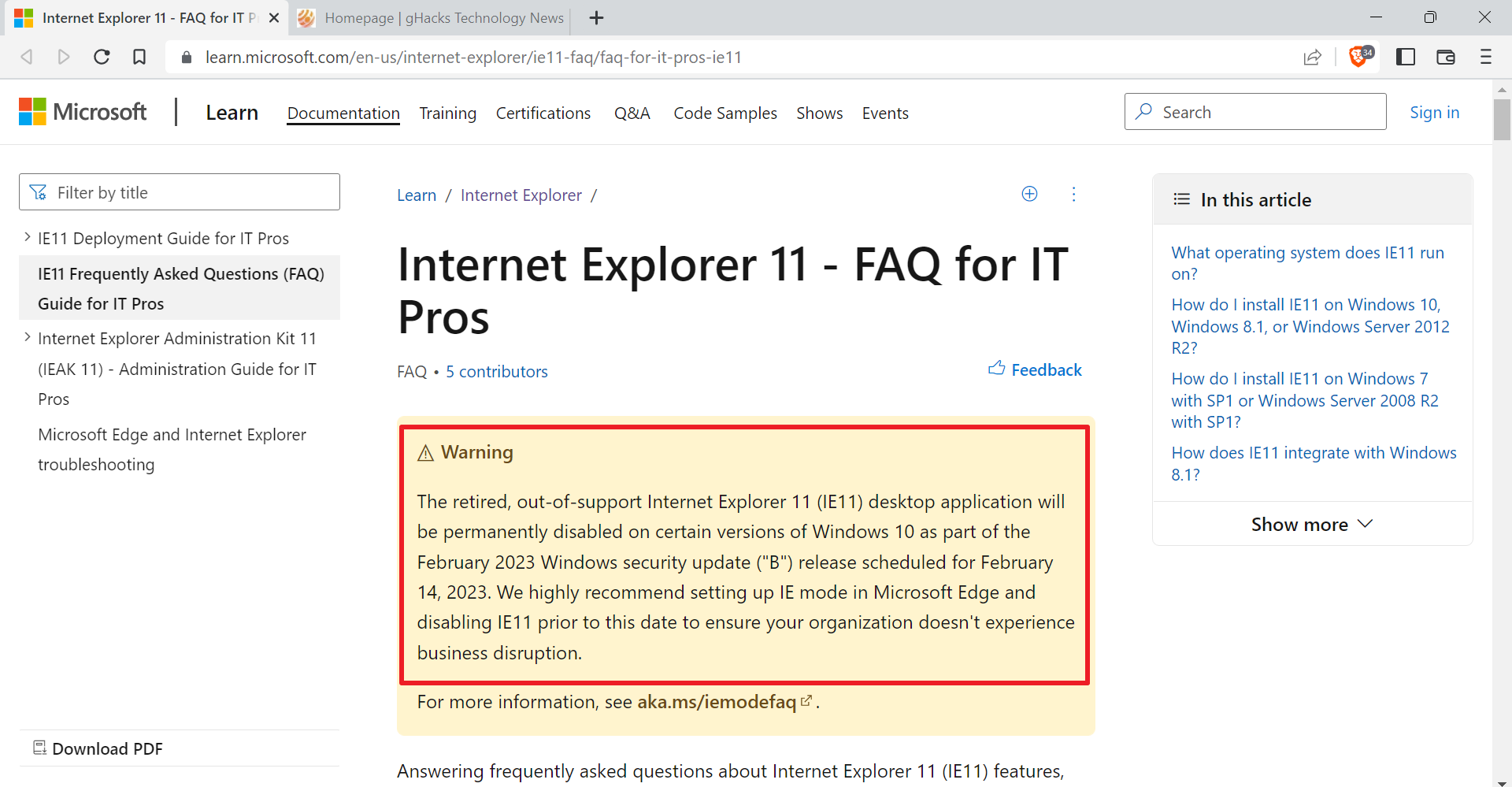
Still using Internet Explorer 11 on Windows 10? It will be disabled in February 2023
Microsoft plans to disable the company's Internet Explorer 11 web browser from certain Windows operating systems in February 2023. The company plans to disable Internet Explorer 11 on these systems, so that […]
Search
See all articles
Brave Search: Answer with AI takes over, but you can turn it off
Brave Search's new Answer with AI feature is now available. The feature replaces AI Summarizer, which was used on Brave Search previously to provide summaries based on user queries. In a nutshell: […]

Google considers charging you extra for AI-powered Google Search features
A report by the Financial Times (via Neowin) suggests that Google is considering charging search users for use of AI-powered search features. The push towards an AI powered future has reached search […]

Marginalia is a search engine that you should check out
Marginalia is not your typical search engine. Major search engines like Google Search or Bing Search are becoming vessels to push advertisement and sites that push advertisement. Yes, that is a generalization, […]

Brave Search finally gets native Image and Video search capabilities
If you tried Brave Search in the past, you may have noticed that it redirected requests to find images or videos to either Google Search or Bing. Today, Brave Software announced the […]
Google Maps
See all articles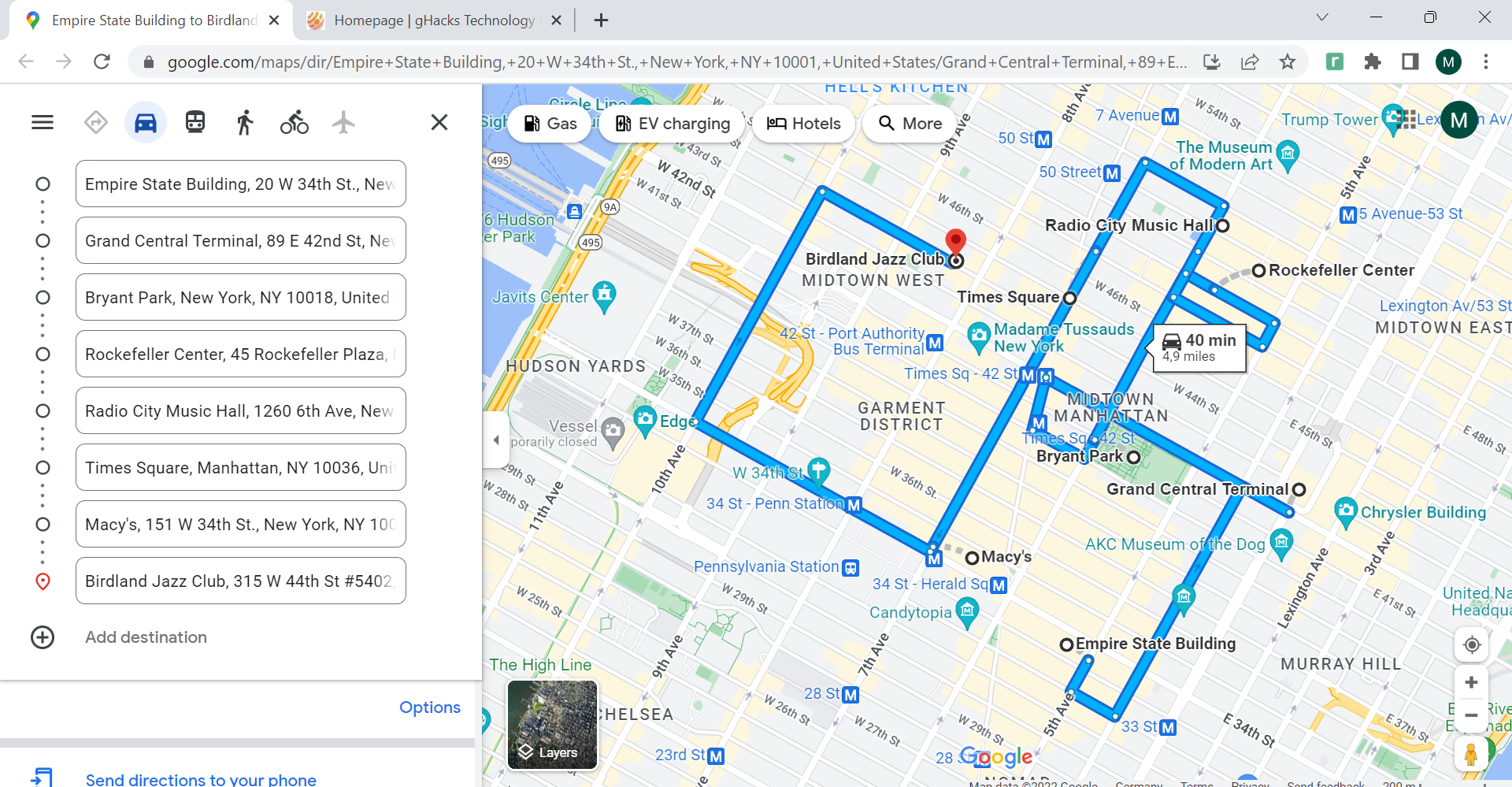
Routora optimizes Google Map multi-stop routes to save gas and time
Routora is a Chrome extension and Internet service that optimizes multi-stop routes on Google Maps to save gas and travel time. Google Maps is a popular choice when it comes to finding […]
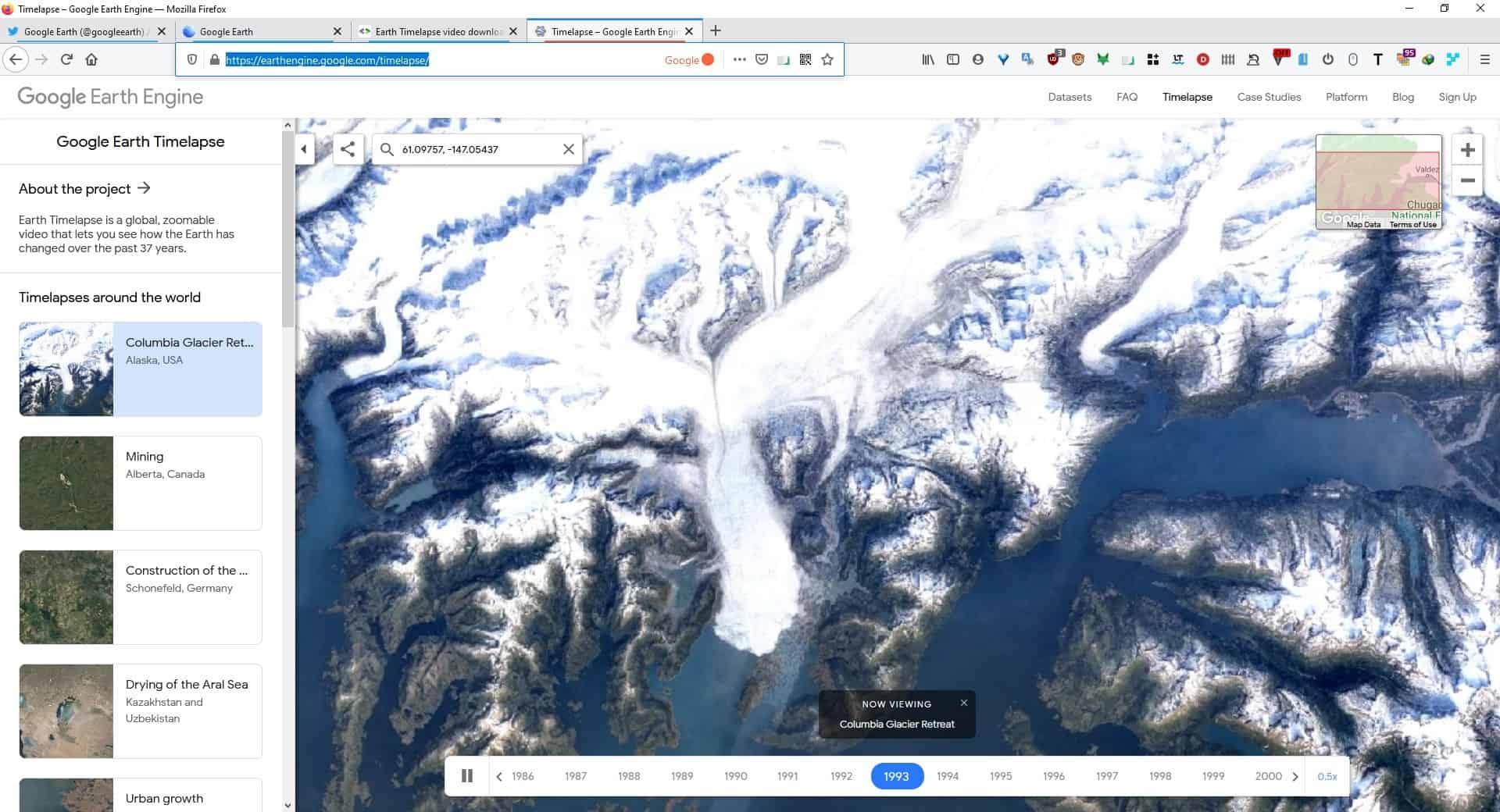
Google Earth's Timelapse feature shows videos of how the planet has changed over 30 years
Google has announced a new feature called Timelapse, for its popular satellite imagery service, Google Earth. These stunning visuals show us how our planet has changed over 37 years, due to natural […]
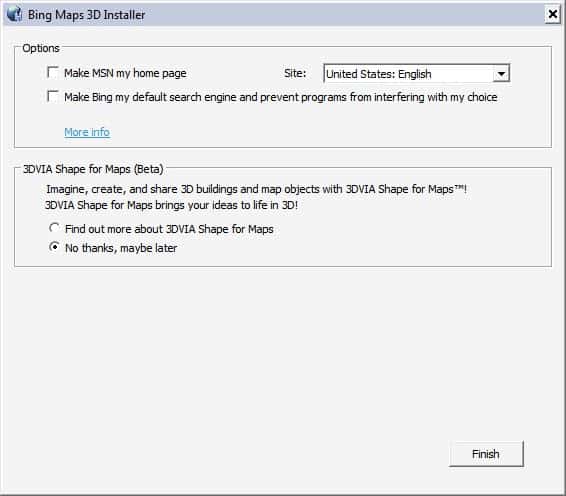
Bing Maps 3D
Bing Maps, which was formerly known as Virtual Earth, is Microsoft's answer to Google Maps. The maps service is directly available on the Bing homepage and offers a 2D mode by default. […]
Local Search Ads on Google Maps
Google Maps users may soon see a new form of advertising when they use the popular mapping service that displays local search ads when the product is being used. The ads will […]
Opera
See all articles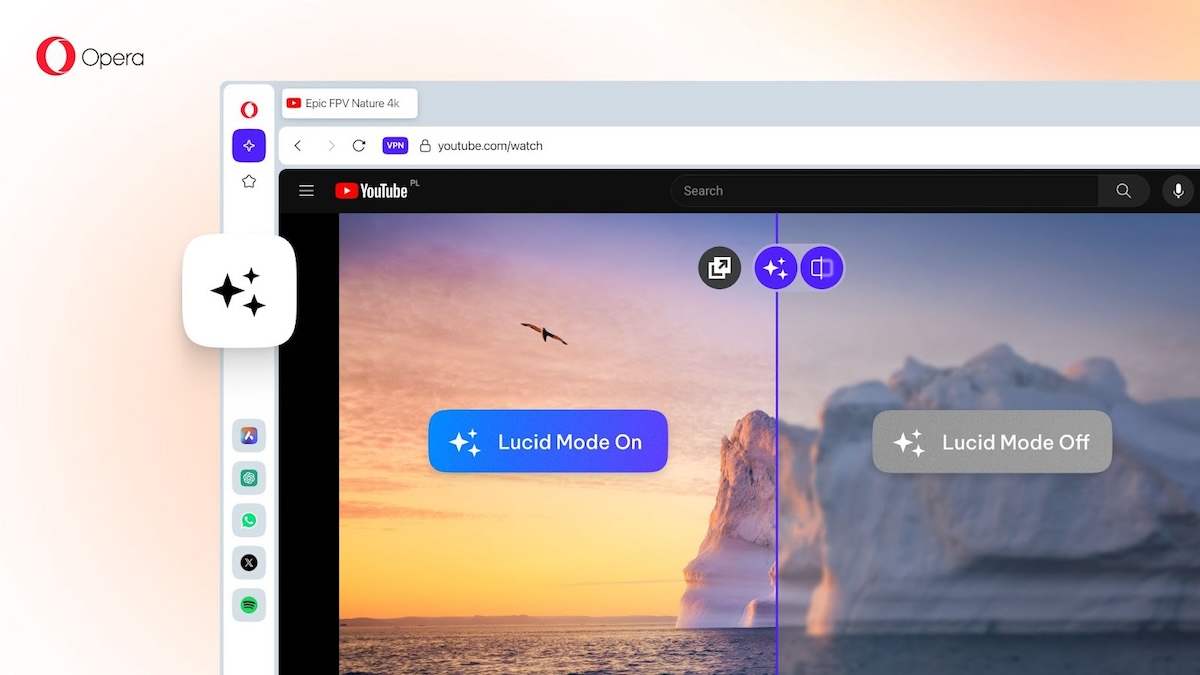
Opera Lucid Mode 2.0 brings refined controls and a comparison slider
About a year ago, I wrote about Lucid Mode in Opera browser. Now, the feature has been enhanced with Lucid Mode 2.0. In case you are not aware of what it does, […]

Please tune it down Opera!
Opera stands out as a popular choice for users seeking a fast, secure, and feature-rich browsing experience. However, one aspect of Opera that can sometimes be bothersome is the startup sound that […]
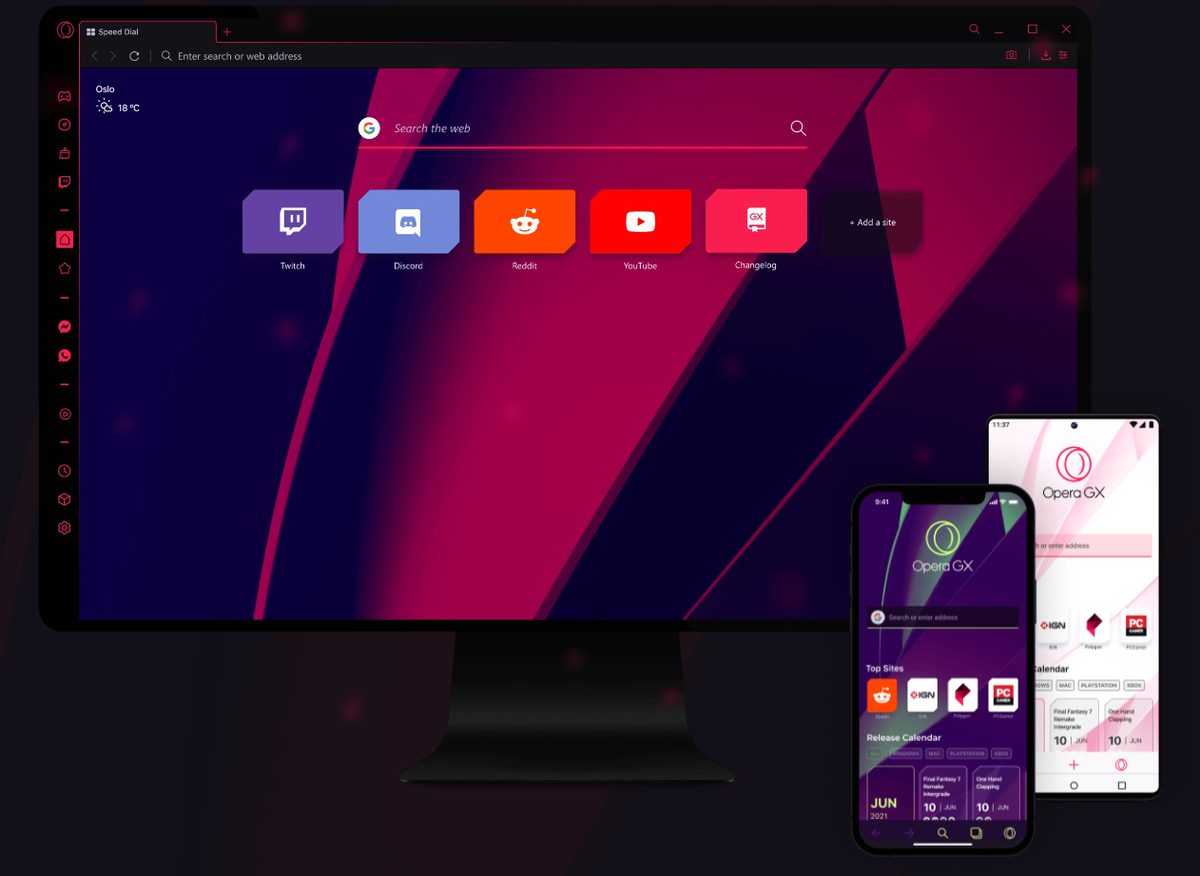
Is Opera GX safe? Let's compare it with Chrome and find out
When it comes to secure web browsing, Opera GX emerges as a formidable contender, boasting a range of features aimed at providing users with a safe online environment. In this comparison, we'll […]

Opera GX browser can now fake your browsing history when you die
Whether the latest feature of Opera Software's Opera GX browser is useful or not is hotly debated already. The company announced the launch of the "fake my history" feature, which replaces a […]