
How to defeat most keyloggers on public computers
Keyloggers can generally be classified as either software or hardware keyloggers. Software keyloggers are running as a background task on the system while hardware keyloggers are little devices that are most of the time connected between pc and keyboard recording every keystroke in their own memory.
Things to do before you sell your digital camera
Many people sell their old digital camera when they buy a new one. Those cameras are often sold on sites like eBay and it is a wise move to make sure that all photos in the internal memory and on external smartcards are not readable anymore. This might not be a big problem if you simply took some pictures of landscapes all the time but it soon becomes one if you took personal and private pictures with that camera.

Check a system for rootkits with Gmer
Gmer is primary a free rootkit scanner which offers additional functionality such as offering an Intrusion Prevention System and a Firewall. The interface looks very user friendly but the settings, options and the results require at last basic knowledge of rootkits and other means of harming the system to apply and interpretate them in the correct way. Gmer does notify the user if it spots something suspicious and displays those results in red in the main window. The two screenshots below show two typical scan results after performing a scan of your computer with Gmer.

Flash Cookies explained
Flash cookies are a new way of tracing your movement and storing a lot more information about you than with normal cookies. One major disadvantage of flash cookies is that you can't locate them in your browser. They are not shown in the list of cookies that you can see when you take a look at the cookies that are currently saved in your web browser. Normal HTTP cookies can't save more than 4 Kilobyte of data while Flash cookies can save up to 100 Kilobyte. If you want to try out how they work you could do the following.
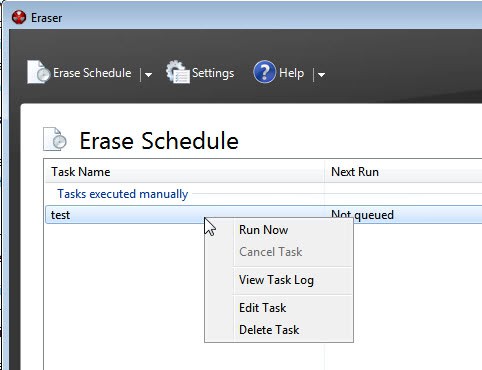
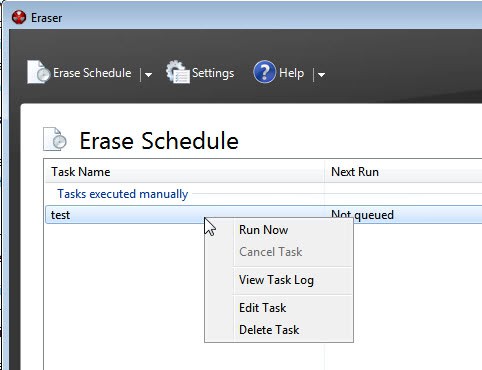
How to erase file information on unused disk space
We all know that it is important to securely delete all files on a hard drive before giving it to someone else. This holds especially true if you plan on selling the hard drive on Internet sites such as eBay. I know that some users buy used hard drives on eBay purely for the thrill of trying to find data that was deleted on that drive. This could get you in a world of trouble if you think of the private information that you save on your computer.
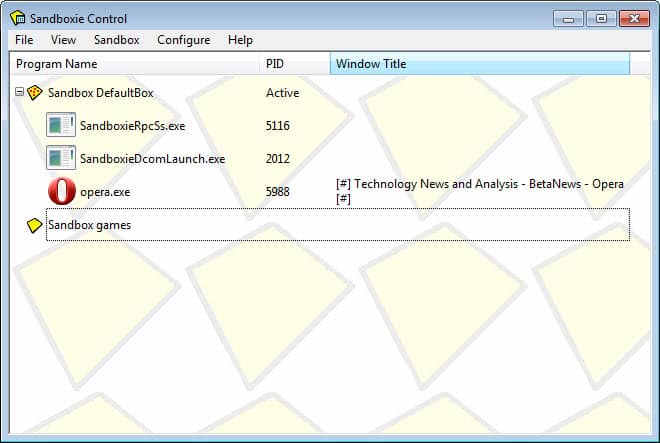
A Sandbox for Applications
Sandboxie does what virtual machines such as VMware Player, Virtual Box and Microsoft Virtual Pc do with the difference that it works on the application level and not the operating system one. Instead of running a virtual operating system that makes it safe to try and test software it lets you run software in a sandbox on your current operating system with the same result. The normal process in an operating system is that applications can read and write date from the system.
How Logistep catches file sharers
It is no secret that companies like Logistep are monitoring p2p networks to sue file sharers who are offering software from clients like Zuxxez, a German company who recently sued 500 British p2p users claiming that they illegally distributed the game Dream Pinball 3D. The website Torrentfreak got their hands on a copy of one of those letters that have been send out which details the process of how Logistep determines which users are illegally distributing the game.

Private Torrent Sites are being infiltrated
I read an rather obvious article over at the TorrentFreak blog that was entitled "Piracy Investigators Infiltrate Private Torrent Sites" which confirmed that piracy investigators have been getting access to private torrent sites by either joining them when they were still open for registration or being invited from a man in the inside. It was always pretty obvious to me that private could not really mean private if the site owners did not know each of the users personally. This system was bound to fail right from the beginning and the article on TorrentFreak only confirms this.

The Compact Disk Eraser
Let me ask you a question: What do you do with old CDs and DVDs that have data on them ? Do you simply throw them away, recycle them ? What do you use to destroy the data on the disks ? If you never thought about this matter before and have a stash of used disks lying around you might want to take a look at the compact disk eraser. The disk eraser is a handy compact tool that wipes out CDs and DVDs environmentally friendly keeping the disks intact. You slide the disk once or more through the disk eraser creating a wide strip that can't be polished out.

What is your Security Concept?
Many novice users use the software that comes preinstalled with their purchased computer and rely on these to be safe from the dangers that lurk on every corner in the Internet. Trojans, Malware, Spyware, Phishing and worse are threats that every user should know about and be able to deal with. It is pretty easy to detail my security concept, it is not the most secure on earth but even those are not secure at all. If you want security do not connect to the Internet at all, that is my advise.

AVG Anti Rootkit free
Rootkits received a publicity boost with Sony's rootkit infested CDs that was supposed to be some kind of copy protection. Since then rootkits have become an ever growing threat on the Internet in line with Viruses, Trojans, Phishing and Spam. The major problem with rootkits is that most users think that their virus scanner protects them from rootkits as well which is most of the time not the case. Rootkits are much harder to detect by normal means and software that can scan systems for rootkits should be used by inexperienced users to be able to detect at least the most common ones.

Send Windows to Nirvana with an animated cursor
One of the many disadvantages of every new Windows edition is the fact that the operating system becomes more and more bloated. Microsoft adds new features to Windows which could then be used to exploit the system.Instead of concentrating on fast efficient systems they produce heavy systems that look shiny but have problems under the surface. Recently a vulnerability in Windows Animated Cursor Handling was discovered. In order for this attack to be carried out, a user must either visit a Web site that contains a Web page that is used to exploit the vulnerability or view a specially crafted e-mail message or email attachment sent to them by an attacker.
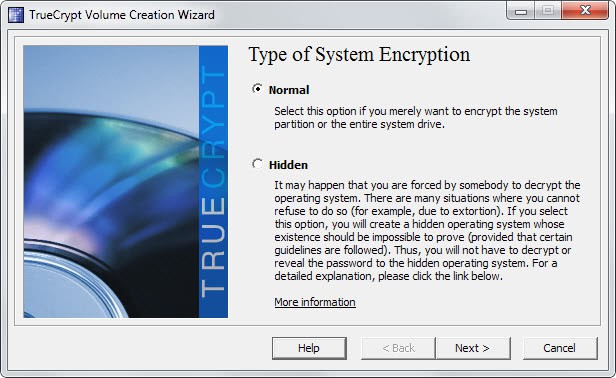
Create a secure data safe with True Crypt
This article is going to show everyone, even the inexperienced, how to create a data safe that can store as much personal information and files as you want using the open source program True Crypt. True Crypt makes it very easy to encrypt almost every piece of hardware including partitions, hard drives, usb keys and other storage devices. Once everything is setup you would mount the True Crypt container using the password that you have selected while creating the encrypted container. This is actually the only password that you have to remember, everything else can be kept in the encrypted container for safety reasons.

About Weak Passwords
I came upon the article "How I would hack your weak passwords" yesterday and pondered if I should write an article about it. I decided that it would be worth it. The author of the article details how he would try and find out your passwords and get access to all of your accounts in the end. His first approach would be to use the most common used passwords by users on the net. He needs information about your personal life for some passwords but those information can be obtained pretty fast through social engineering. Trying those "top 10" passwords would already cover a large percentage of online users, statistically speaking that is.

Can't delete virus? Try Killbox
You might have come upon this problem during scans for viruses and Trojans on your system. A malicious file was identified by your favorite virus scanner and it prompts for action. You can delete, move, rename or move the file into quarantine. It is however not possible to delete malicious files when you choose to delete them because they are currently in use and can't be therefor deleted.
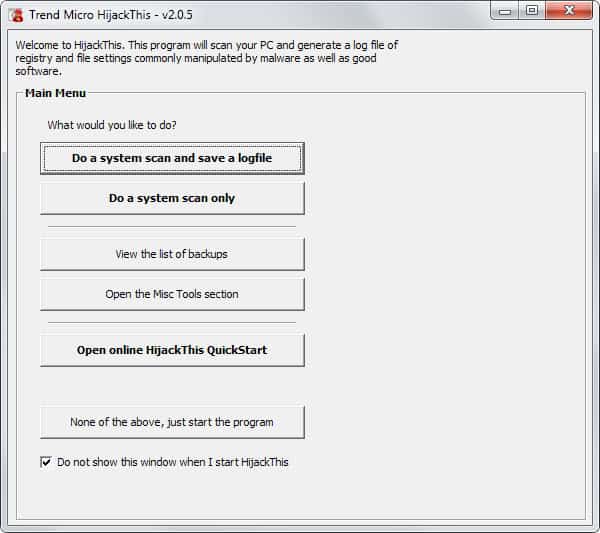
HiJack This review
HiJack This is a very sophisticated security analyzer that generates an advanced report of various registry settings and files in your computer. The difference to many other security analyzers such as trojan scanners is that Hijack This makes not difference between "good" and "bad" settings but displays everything that it founds in its security log. It is then up to the user to find potentially harmful files and settings and remove them from his computer.

Reveal Saved Internet Explorer Passwords
It is very convenient to save login passwords for internet sites such as forums, blogs or paysites to login quicker to those websites. That is, it is great until you can't remember the password anymore but would like to know it again. This could be the case if you want to switch from Internet Explorer to Firefox or Opera for instance. Protected Storage Pass View does not only reveal passwords that have been saved in Internet Explorer while accessing protected sites or using the auto complete form but also passwords that have been saved in Outlook Express and MSN Explorer.

Japanese P2P Trojan deletes Files
A new kind of Trojan was discovered recently which targets only Japanese file-sharers. When executed the Trojan displays manga-like images with a reminder which differs depending on which image is displayed. The text however looks similar and always asks the user to stop using P2P networks. One of the messages for instance reads ""Ah, I see you are using P2P again...if you don't stop in 0.5 seconds, I'm going to kill you." Talk about a threat boy, jeeze."

20 Minute Guide to Pc Security
20 minutes to increase the security of a computer, wow that must be a good guide. The guys at itsecurity have written a security guide that indeed covers the basics of PC security. I do know from first hand experience that many users do not follow simple PC security guidelines, e.g. they probably have a anti-virus solution but never update it.
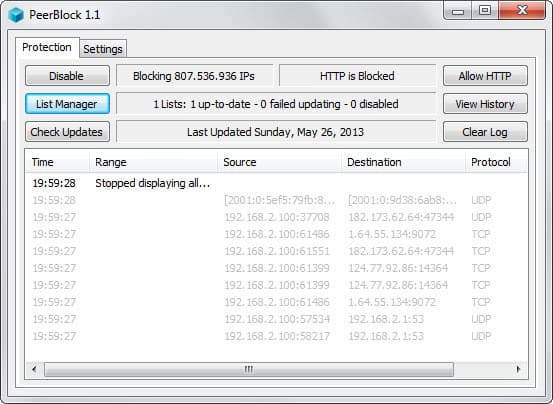
Block IP addresses with Peer Guardian
Why would you need another program to block IP addresses if you already have a firewall ? A good question that can be answered easily. Peer Guardian uses a database of bad IP addresses and blocks them automatically as soon as the IP is added to the database of blocklist.org. A single user would have to know that a new IP (range) poses a thread and add it manually to his firewall.

Autostart programs when a usb drive is connected
USB Virus Scan is a nice little command line utility that performs predefined operations if a usb drive is connected to your computer. It is able to distinguish between various drives which means that you can add custom operations for the drives that you own and a general option for drives that are not recognized. The tool uses the volume serial number of the drives to identify them and perform the operation.

Test your Anti-virus program
Do you know that your anti-virus solution is working ? You could try to test your anti-virus program against the EICAR (European Expert Group for IT-Security) test file to see if it reacts the way it should. All you need to do is create the testfile and scan it with your virus scanner. If the scanner detects something it is working as intended, if it does not you should consider changing immediately to a more reliable one.
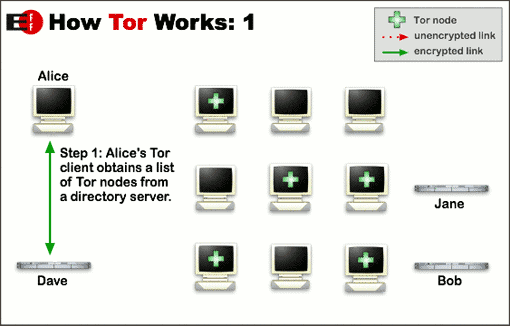
Use the Foxtor Extension for anonymous surfing
There are times when it is safer to remain anonymous on the internet - be it that you want to write something about your current company on the web, live in a country that does everything to prevent it's citizens from accessing unbiased information or simply for the reason that you do not wish that someone could track what you are doing on the internet. In an ideal world every user should have the right to read and publish on the internet without the fear of loosing his job or life. The world however is not ideal and tools like FoxTor exist to help those people out.

Use Password Grids to Remember Passwords
Most internet users have serious troubles with passwords: they either choose to use the same password on all sites, use passwords that can be easily guessed by looking at the persons background or write all their passwords down to be able to look them up if they forget them. Only a few users use high quality passwords that they are able to remember.

Data Retention laws on the uprise
Well what do we have here ? FBI director Robert Mueller wants that service providers record their customers online activities with the same lame excuses that men like him come always up with: Protecting minors and terrorism. Let me get something straight here. Terrorists are not uneducated, they know how to build explosives, they know how to work with computers. They especially now about encryption.

What you should consider before selling a video game system
Thunder7 recently told me that he bought a used Xbox and discovered that the hard drive was full of music files from the previous owner. The original Xbox uses an internal 20 gigabytes hard drive to store save games, patches, music and images. The new Xbox 360 and Sony's PS3 will also utilize a hard drive and the following tip is also valid for them.
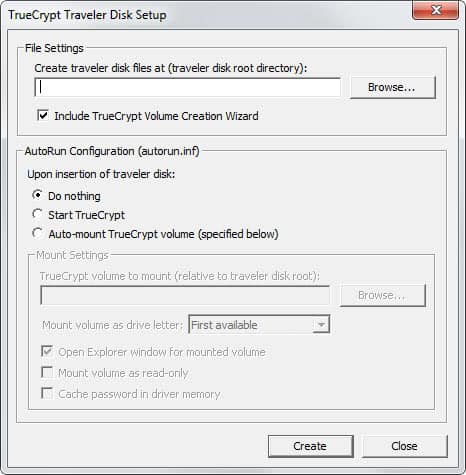
Create a secure USB Data Safe
I'm going to show you how to create a secure usb data safe that can be used to store sensitive data. Secure means it is encrypted and will only be encrypted if you need the data that is saved on the stick. This method is also working with other removable media such as zip drives and hard disks.

System Safety Monitor 2
System Safety Monitor 2 is available in a free version from the developers website. The tool basically works as a firewall preventing malicious software to be started automatically. The free version runs in paranoid mode which means you have to allow or disallow every process and get nagged quite a bit at the beginning. Once the majority of rules are established the software runs a lot smoother and seems to come forth only when you tend to install a new program or change existing ones.

Find out if a process is malicious
You see lots of processes when you start your taskmanager, svhost.exe, csrss.exe, winlogon.exe and many more. A user who never dealt with those executables before has a hard time figuring out which are safe and which could be malicious because normally you can't say which program is using those files. A question like "Is svhost.exe a virus, is it safe ?" is normal and can be answered using the methods described below.
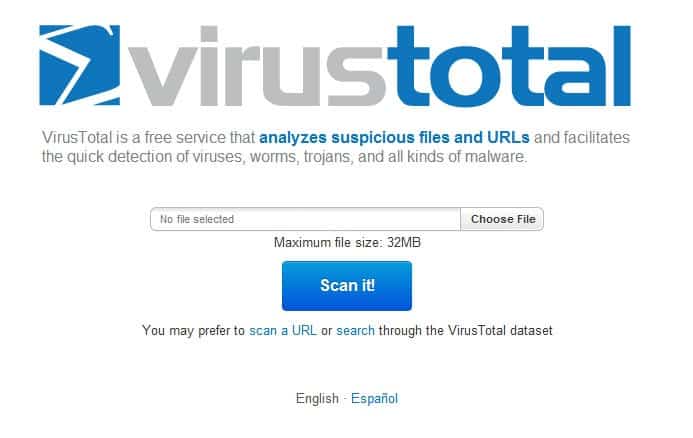
Free Online Security Scan Websites
Many sites offer to scan your computer for viruses online which should be seen as a last resort because this method has advantages but also disadvantages. If you scan your system online you can be sure that the latest virus definitions are used while scanning your system and that the script that is running was not compromised by a virus or trojan running on your system.

Tor Servers Seized in Germany
More than ten dedicated servers have been seized by the German police last Thursday. Some servers were running a version of the popular anonymising software Tor (The Onion Routing) which leads to the conclusion that those Tor Servers were most likely configured to run as Exit Nodes as well as normal nodes. As you may know a request runs through different Tor Servers with each only knowing the adjacent servers but not the starting node (you) and the destination. Only the last node in the chain knows the destination.

Freenigma Extension to encrypt your mail
Freenigma offers a free firefox extension that adds cryptography functionality to Yahoo, Gmail and MSN. The team says it is working on adding other emails services, as of now, only the three services mentioned are supported. You have to signup at their website to recieve an invitation before you will be able to download the extension. They state that it could take a few hours the most before you recieve the invitation. Mine arrived about ten minutes after I completed it.

Lock your Devices with Device Lock
Device Lock allows you to close open USB and firewire ports as well as other device ports that make it possible to run external devices on your computer. With all the live cds and programs that run from USB such connections to the pc have become a greater security risk than ever before. System administrators as well as security concerned end users should disable every means of accessing the pc or running software from devices that could access it.
Relakks Revisited
Relakks had a few problems shortly after their start due to the amount of users that registered the service right after it was introduced. Connections have been really slow and I had no chance to further test the service and write about my experience with it. I'am currently writing this article while being connected to Relakks and everything is working fine so far. I'am able to open websites and surf the internet without problems. I'am able to check my email and download files using Relakks.
My first experience with Relakks
I signed up with Relakks yesterday and was satisfied with this clean and easy process. I had to provide only some information like name, email, password and username and was able to log on to their system. My status was inactive at that time because I did not make a purchase yet. I decided to try the service for one month and had to provide my credit card details in order to do so. One month would cost 6$ which is a good price if they live up to their promises which are a) anonymous internet experience and b) maximum speed.

Relakks the first commercial darknet
The Pirate Party is a swedish party that has three main goals: Protected Privacy, Free Knowledge and Shared Culture. They are making a bid for the Swedish parliament in the upcoming election and just introduced the worlds first commercial darknet called Relakks. Let us take a look at the definition of Relaks from the website:
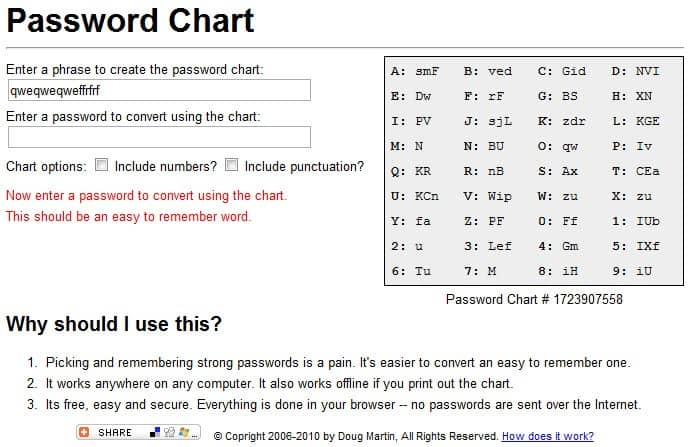
Make your passwords stronger with a password chart
Password chart is an online service that helps you improve the quality of your passwords. The principle is pretty easy: You enter a phrase at the beginning which will be used to create the password chart. An example would be "Make your passwords stronger with passwordchart.com" or "https://www.ghacks.net/ is gr3at". The password chart will be displayed on the right side of the screen changing while you are adding new chars to the phrase. You can opt to add numbers and punctuation for increased security, they will be added to the chart on the right.
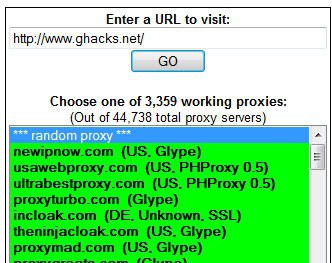
Free Web Proxy List, Custom Proxy Server Guide
A web proxy is becoming more and more important in todays internet. Schools and Companys tend to block sites pretty quickly nowadays, especially when the blocking is directed at just a few websites and not every website in that category. Web Proxys might be able to sneak past this policies and display the site in your browser even though it is banned in the network.
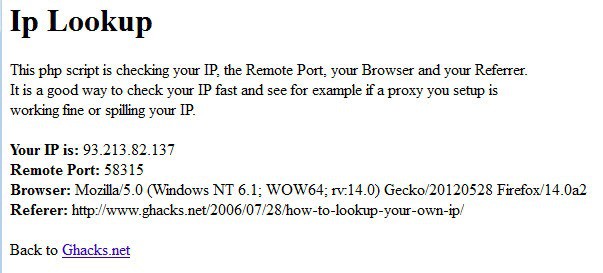
How to lookup your own IP
I have written a small php script that lookups your IP, your browser, the refering site and the remote port. The website has no ads at all and loads pretty fast. This might be useful for those who are using proxys and want to check if those proxys are spilling their IP address or not. The RIAA for example is identifying downloaders by their IP address.

IceSword the better Rootkit Revealer?
IceSword is a new contender for the title of the best rootkit revealing and removing program out there at the moment. It is rather hard to find a working download of IceSword but as always I provide a fast way to download the latest version of Icesword named IceSword1.18.rar. Click the link to download the rootkit scanner from rapidshare. In contrast to other rootkit scanners like Blacklight Icesword can not be run automatically. Icesword only provides perhaps the most powerful utilities to scan your system for rootkits and other information.

