Bitwarden's Latest Update Takes Security to the Next Level

The recent security breach that affected LastPass has caused ripples across the industry. Norton Password Manager suffered a password stuffing attack, while Bitwarden users have been targeted by phishing ads.
Many users are worried whether hackers break into their password vaults. They are encrypted with zero-knowledge, they should be safe, right? The answer is not that simple, as there are other factors that affect the outcome, one of which is the cryptography system that is employed by the service. A key component of this is KDF.
What is KDF?
KDF stands for Key Derivation Function, it is a cryptographic algorithm that derives secret keys from values such as passwords, master keys, etc,. This is how password managers create an encryption key, from your master password, to protect your password vault.
The function also has other uses. You may be familiar with the terms hashing, salt, pepper, etc. Most websites don't just store (hashed into a value) passwords at their face value, usually they add a random string to passwords to protect them from dictionary attacks, this process is called salting. This data is then hashed and stored, so even if a hacker manages to gain access to the passwords, they won't be able to use the data since the salting process changed the hashes of the original password, so it can't be cracked as easily.
KDF does a similar thing, this depends on the number of iterations it is set to, aka as rounds. e.g. 100,000 rounds to rehash the values. It stretches your key, thus slowing down the process of guessing the password, making it more expensive and difficult to compute. In a nutshell, the higher the number of iterations, the harder it is for hackers to brute-force your decryption key to get into your password vault. The commonly used KDF algorithm is PBKDF2, though there are others like Argon2, Scrypt, Bcrypt.
A Senior Security Engineer at Yahoo, Jeremi Gosney argued that a strong, unique master password will protect users more than a high count of KDF iterations can, but also said that the latter will also help secure users who don't use a very strong password.
Let's look back at the LastPass data breach. The password manager service had set the default iterations count to 100,000 for new accounts, but many old accounts were stuck at 5,000. Security experts had criticized the company for sticking with this, and said that even 100,000 iterations wasn't good enough. This was not the only reason for the LastPass data breach, they had more issues related to the security of their systems, how they got breached initially, not encrypting user data such as URLs, etc. But, what we have learned from recent incidents, is that we have to be extra careful to protect our data.
Bitwarden to increase its server-side iterations to 600,000
It is important to note that there are 2 kinds of iterations done by Bitwarden; one on the client side (that is, your computer), and the other is done on the server side. A white paper published by the password manager service indicates that it does 200,001 rounds, i.e. 100,000 + 1 using PBKDF2 SHA-256 on the client side, and 100,000 on the server's side.
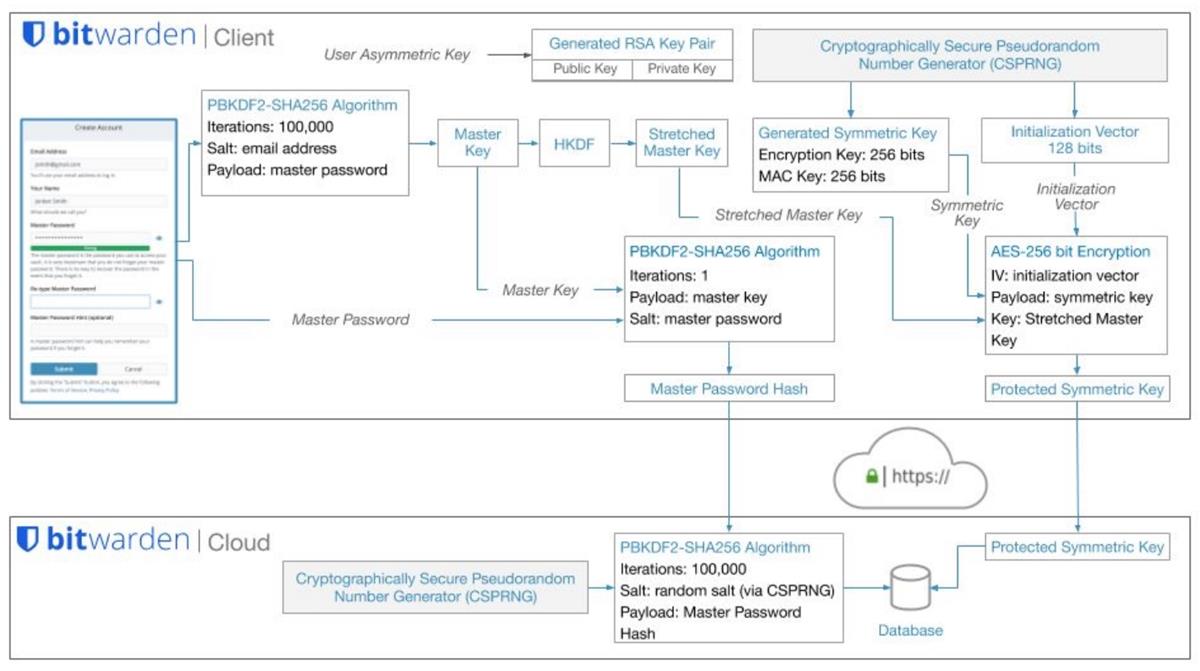
Wladimir Palant, the creator of AdBlock Plus, has pointed out that Bitwarden was not actually running 100,000 on the server side for the encryption key, it is only done for the master password. The client-side on the other hand handles both. Now, here is the thing. Bitwarden's default KDF iterations is actually pretty low, it sits at 5,000 server-side iterations. Palant said this flaw meant that the security level of Bitwarden is identical to what LastPass had.
Security expert, Dmitry Chestnykh, had mentioned this problem in 2020, yet it still remains unresolved. Many users have asked the company to address this issue. As a matter of fact, users have been requesting better algorithms, such as Argon2, since March 2018.
Bitwarden replied to a user on Mastodon, saying that they would increase the count to protect user data. It is not clear whether this will affect existing user accounts, the company has responded to queries that it is working on it. But you don't have to wait for them to act, you can change it manually right now.
Warning: You are advised to export your vault (backup) before trying the following. Users who have the Bitwarden browser extension users or the mobile app can go the Settings > Export Vault. The desktop client lets you do the same from the File menu > Export Vault. Once you change the KDF iteration count you will be logged out of all clients. That's because the encryption key is changed. Using a high KDF count will cause your password vault to open more slowly. Please refer to the official support page for more information.
How to change the KDF iterations count in Bitwarden Password Manager
1. Login to your Bitwarden vault.
2. Click on your profile in the top right corner.
3. Select Account Settings.
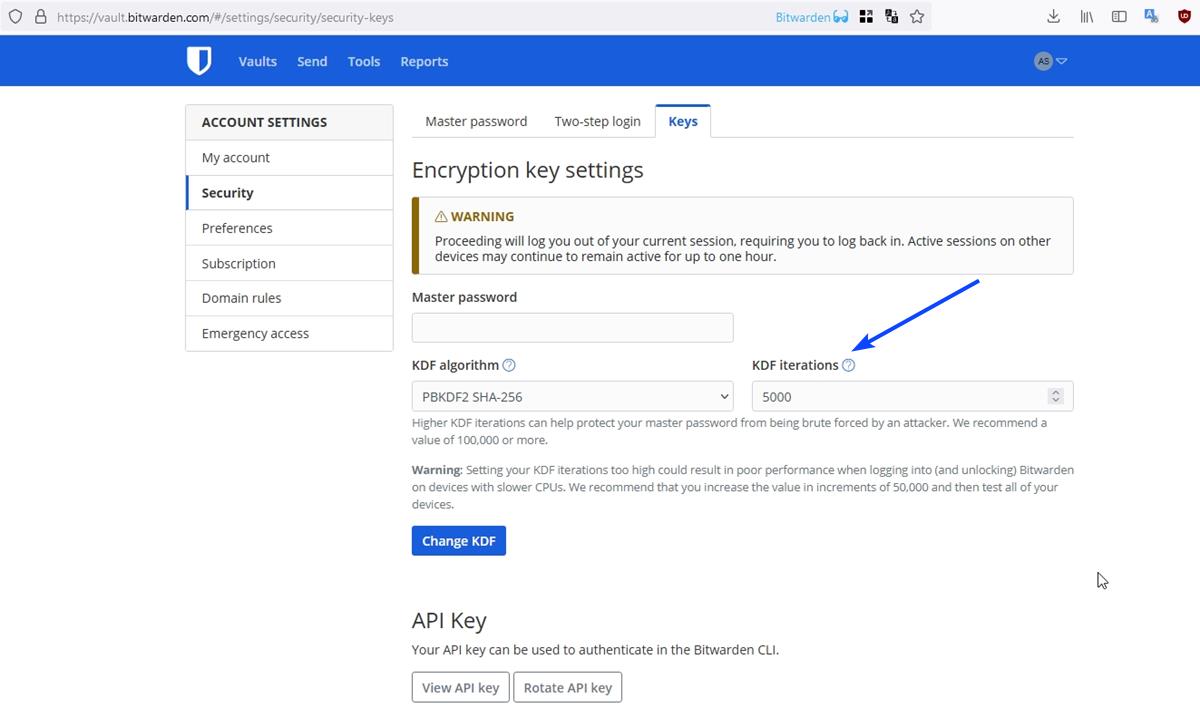
4. Switch to the Security tab. The URL is https://vault.bitwarden.com/#/settings/security/security-keys.
5. The option that we are looking for is the KDF Iterations. It is set to 5000 by default, even though a note below the box states that the recommended value is 100,000 or more.
6. Click on the box and type 600,000. Enter your master password in the corresponding field.
7. Hit the Change KDF button.
Note: You will be logged out of your account, and a message will pop up to indicate that your encryption key has changed.
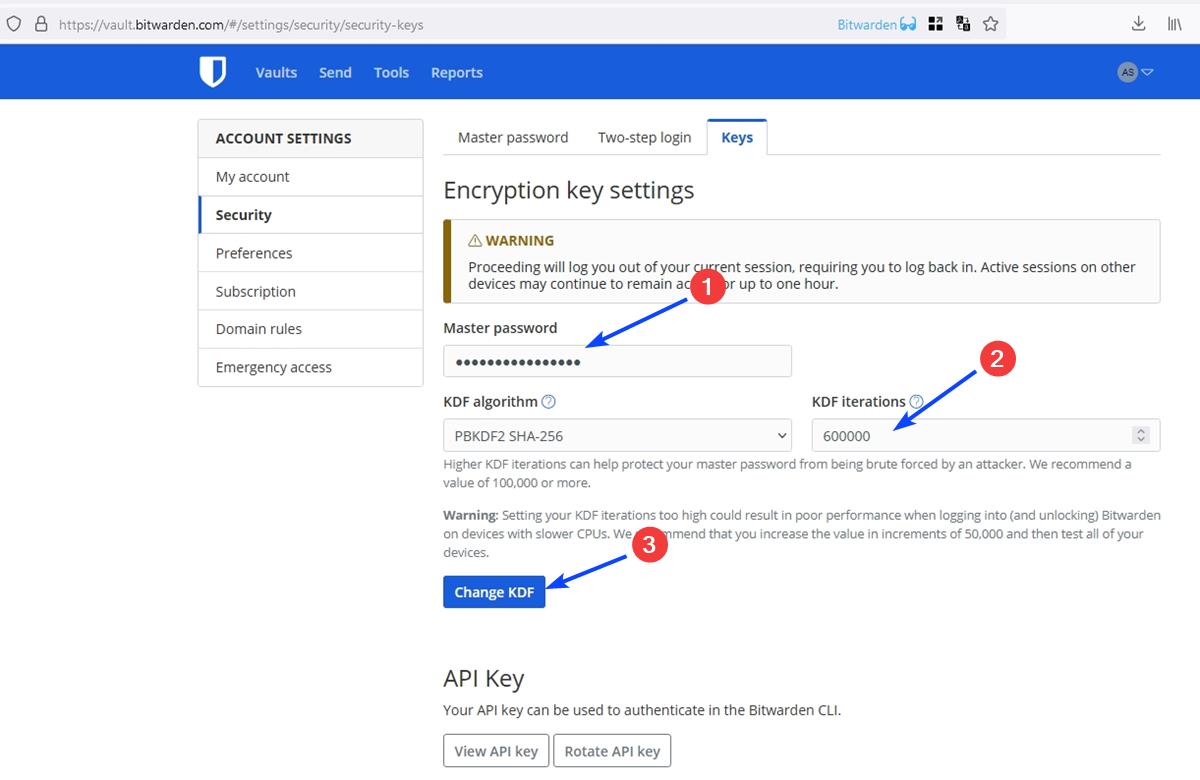
Why 600,000? It is the number of KDF iterations that the Open Web Application Security Project (OWASP) recommends. Until recently, OWASP actually recommended 310,000 as the default number of iterations. But that seems to have nearly doubled over the past week. Even Bitwarden's message on Mastodon does mention that the initial plan was to set the KDF iterations to 350,000, but then they decided to go with 600,000.
While you are at it, I'd also recommend changing the clipboard behavior of Bitwarden's browser extension. Click the add-on's button > Settings > Options > Clear Clipboard. By default, this is set to never clear the clipboard, change it to 1 Minute or whatever suits you. (h/t Techspot)
I also recommend reading Palant's recent article about how password strength works.

















It should be noted that you get far more attack protection by using even slightly longer passwords because password strength increases exponentially with length. Increasing iteration counts only increases the strength linearly.
So, you’re much better off just making your password a few characters longer.
After that operation we should change password (new can be same as old) and check checkbox below to rehash all entries with new key ;)
What really amazes me is that nothing was ever really done about it. Now that it has been discovered, suddenly it can be done in a jiffy.
I find that very puzzling.
Without getting into all sorts of conspiracy theories about the NSA, CIA etc having something to do with this, I still have my questions as to why this gross oversight was allowed to continue.
Let me keep it simple with the bittorent company in question and agree that there is gross negligence here.
What baffles me as much as the gross negligence is the fact that, despite the Lastpass example, the company in question is able to continue its detrimental policy towards users with impunity.
@Ashwin I don’t see advertising because I use an ad blocker. If I did see advertising for Bitwarden I would not act on it because I am already a Bitwarden user. The phishing is aimed at potential Bitwarden users. Current Bitwarden users would be unlikely to respond. Your wording “Bitwarden users have been targeted by phishing ads” is therefore inaccurate.
“Using a high KDF count will cause your password vault to open more slowly.” – just the first time, right, not every time?
I set mine from 100000 to 600000 just today and didn’t notice any difference yet. I also decided to turn on the two factor feature and scanned the bar code to my Microsoft Authenticator app on my phone. I do believe that the two factor feature only comes with the paid version if I’m not mistaken. There are no slow downs at all on my end.
Changing iteration should be done increasingly, not all at once. More iterations means more memory, so if you are running an old device, you should go slow, let’s say by 50k or so and check if that’s still work for you.
Also, higher iteration means less speed, it means that decrypting your vault is gonna take a little longer, depending in many factors, but iteration is one of them.
And yes, yes yes, you should increase your KDF iterations manually, don’t wait until they do for you. It doesn’t matter if you have a very strong password, it’s safer and you will be saving a nightmare.
FWIW, KeePass currently is set at 60,000 AES KDF iterations out of the box.
But it also offers the (better, IMHO) option of using Argon2 instead. And also the option of ChaCha20 instead of AES encryption, if that floats your boat, and it does mine.
Note that “iterations” are a different thing with Argon2; the number will be more like 2 or 4. Read the set-up info here:
https://keepass.info/help/base/security.html
I would still recommend Bitwarden – and not messing with the defaults – for noobs and non-techies that don’t have special security requirements. But use strong passwords. Always.
+1
So that’s Bitwarden and Lastpass having lousy security baselines. Anyone know how Keeper is doing?
Keeper now uses 1,000,000 PBKDF2 iterations. We posted a blog with additional details:
https://www.keepersecurity.com/blog/2023/01/09/how-does-keeper-protect-your-data-security-and-transparency/
FWIW I have/had two Bitwarden accounts and both of them had server side iterations set to 100k by default with an option of increasing them.
Bitwarden is soon to have Argon2 implemented.
I confirm, Bitwarden KDF iterations set by default to 100,000 :
“Higher KDF iterations can help protect your master password from being brute forced by an attacker. We recommend a value of 100,000 or more.
Warning: Setting your KDF iterations too high could result in poor performance when logging into (and unlocking) Bitwarden on devices with slower CPUs. We recommend that you increase the value in increments of 50,000 and then test all of your devices.”
It is NOT “set to 5000 by default” but to 100,000
5000 was the old default many years ago. My account was actually so old that it still was set to 5000.
Same. I had my account for like 10+ years and mine was still set to 5,000 as well. I had to change mine manually.
This ‘warning’ makes no sense. It’s the key *derivation* function, i.e. setting the key (which is why it logs you out everywhere when you re-dirive it), not something that gets processed 600,001 times every time. Yeah, maybe don’t do the reset on a machine with a tiny processor, but it shouldn’t slow you down every time once it’s done the first time. Right?
Well, for you, the client, is not a big deal with actual desktop or smartphone cpu performances but … think about «the server» part! Lots and lots of “free clients” served by bitwarden with exponentially better key derivation functions!
So, in this scenario better is worse and thats why!
The key must be derived from the master password each time you decrypt the vault. So it may not need to re-compute the key every time you open the app, but it does need to do so each time you login.
The main purpose for having a large number of iterations is to make it more expensive (in terms of both time and processing power) to determine if a given password will generate the correct decryption key for the vault. There would be no value to this if it did not make the process more expensive each time the vault was decrypted.
More expensive is a relative here, it may only add a few tenths of a second to the time it takes to calculate the key. For the vault owner, who enters the password correctly on the first attempt, this probably isn’t even noticeable. However, for a bad actor who must test every possible password it can mean the difference between testing hundreds of millions passwords per second to just a handful.
Even the fact that you’re re-encrypting the vault with a new key doesn’t really add any overhead to the process. Once you have the key, encrypting the vault takes about as long as decrypting it does when you login the next time.
I didn’t noticed any lag when increasing iterations to 600k and I’m using budget devices. So this would apply to really old devices.
Just remember the password using your mind or even in a piece of paper, it’s more useful.
This is outdated advice that is irrelevant to the modern Internet.
I have in excess of 100 records in my vault. Good luck remembering a different complex password, mostly 24 characters long) for every record. Got that? Now, knowing any of the websites they relate to may be hacked at any time, get in the good security habit of changing passwords regularly. is you memory keeping up? The memory degenerates over time. Memories deteriorate over time.
Paper? There is such a thing as house fire.
Well, that thing, the memory password, is still a useful habit for pasword managers master passwords. And because the best pasword generators use that seed words thing this means you can use a memorized poetry or a loved quote and so on.
Combined with a lesspass browser addon is ever better but pasword managers like bitwarden is more potent in features so just use both in paralel!