NortonLifeLock says some Norton Password Manager accounts were compromised
A month ago, LastPass suffered one of the biggest security breaches we have seen in the world of password managers. And now, NortonLifeLock has revealed that some of its user accounts have been compromised by hackers.
NortonLifeLock says some user accounts were stolen
Gen Digital (formerly called as Symantec and NortonLifeLock), owns the Norton brand of products, along with Avast, AVG, Avira, CCleaner, to name a few. Interestingly, almost exactly a year ago, Norton found itself in the news for the wrong reasons, when Norton 360 Antivirus was discovered to install a crypto miner.
The Norton Password Manager breach is quite different compared to LastPass'. In the case of the latter, it was an issue related to the company's own security systems, first some account(s) belonging to the developer environment were hacked, which led to some stolen code. The threat actors then used the code to breach the company's servers and gained access to the storage servers, which in turn led to the password vaults of users being stolen.
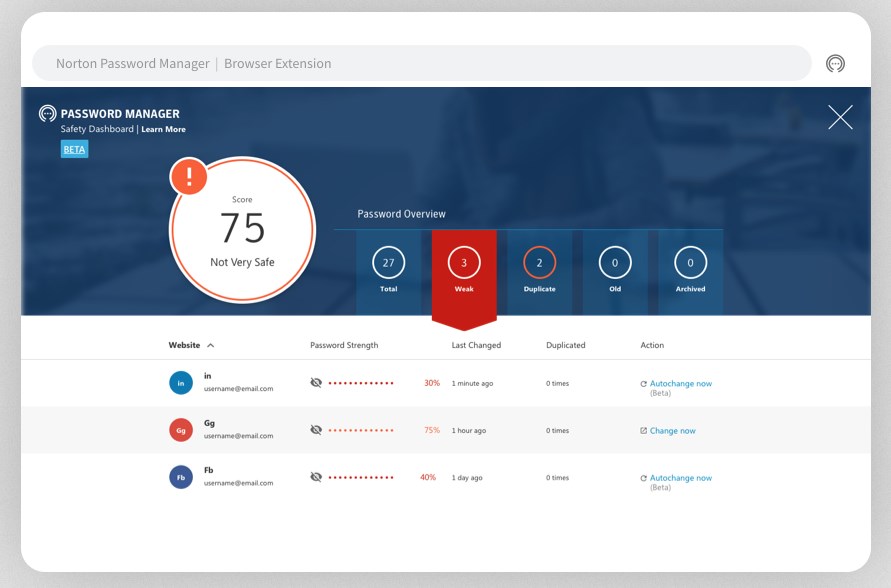
Image courtesy: Norton/Gen Digital
Norton's story is different. This is what the company had this to say in a letter shared with the Office of the Vermont Attorney General:
"Our own systems were not compromised. However, we strongly believe that an unauthorized third party knows and has utilized your username and password for your account. This username and password combination may potentially also be known to others."
Note: The source link doesn't seem to work anymore. I managed to access a cached version of the page, but was unable to download the PDF available there to view the statement.
So, how did the attackers gain access to the accounts?
NortonLifeLock states that hackers bought stolen credentials from the dark web, and attempted to use the data to log in to Norton customer accounts around December 1, 2022. The company detected an unusually high volume of failed login attempts on December 12th, which it began investigating. It concluded the investigation on December 22nd, arriving at a conclusion that hackers had used credential stuffing attacks to compromise an unknown number of user accounts.
Unlike brute force attacks where hackers try to guess the passwords of accounts, credential stuffing is a way of injecting already stolen passwords to gain access to accounts. NortonLifeLock has warned users that the breach may have resulted in the attackers viewing the user's first and last names, phone number and mailing address. This is where it gets even more serious, Norton warns that the hackers may have also gained access stored in the private vaults of Norton Password Manager. So anything from personal notes, addresses, or other sensitive data, could have been stolen.
The company noted that the risk of user accounts being stolen is higher when people use the same password for multiple accounts, including Norton customer account and the master password. This is likely the cause of the breach, some users may have used the same password that they used as their Norton Password Manager's master password, with accounts on other sites which may have been compromised and later sold.
Based on this, NortonLifeLock may not be the one to blame entirely for this data breach, because customers used weak passwords. But I think Norton could have also warned users earlier about the issue earlier. It should have enforced a rule that requires users to enable two-factor authentication (2Fa), and also to use a strong password. For context, LastPass was criticized by security experts because it allowed users to use weak passwords, and old accounts which had weak passwords were not prompted to set a strong password. Password managers should educate people about the importance of using strong and unique master passwords, i.e. not recycle them with other accounts.
NortonLifeLock released a statement to Bleeping Computer, it says that the firm secured "925,000 inactive and active accounts that may have been targeted by credential-stuffing attacks." The company says that its systems are secure and have not been compromised. It has reset the passwords for the affected accounts, and is advising users to enable Two-factor authentication on their accounts, and also to enrol for a credit monitoring service to prevent against identity theft and credit card fraud.
Such attacks could happen to any cloud based password manager, that's why it is important to use a unique master password. Nevertheless, I'm going to once again recommend KeePass Password Manager, if you want an offline, free and open-source password manager. There are many great forks available for Windows, Mac, Linux, iOS and Android. My preferred ones are KeePassXC, KeePass2Android and KeePassium on iOS.
Do you use Norton Password Manager?
Haha. Enjoy your cloud services everyone. What you get for keeping private information on someone else’s server. The entire purpose of the cloud is to exploit you, steal your data and money.
Certainly MS Defender and Norton quality control center seem drown in the worst dark hole of incompetence and lack of vision, they were good in the past however nowadays they don’t know how to protect their own users, not only this, even MS Defender destroys their user’s computers. When I arrive home I will install Panda Cloud free version because I won’t trust Defender anymore. Thanks @Ashwin for the article! :]
this is the reason why not to put your sensitive data on the cloud. I do not trust any of password managers. I keep my passwords on a USB and encrypted locked in a safe..
Well, there we go again.
I don’t use Norton products nor any of those owned by ‘Gen Digital’. How could I use any software of a company which distributed a crypto-miner infected antivirus?
Concerning password strength and singleness I’m afraid education is not enough. Code cannot check a password’s singleness (fortunately!) but it certainly can REFUSE week passwords. Irresponsibility is on both sides. Many companies are basically cowards, afraid to frighten potential customers by requiring basic security behaviors. And many users are totally disconnected from Web realities, likely those whom, because of an oyster’s IQ, perceive privacy and security only in real life’s tangible dangers. To summarize, combining a company’s cowardliness with a user’s idiocy is dynamite.
For those who do not know what Tom is making a reference to, here is the article about that: https://www.ghacks.net/2022/01/05/norton-360-antivirus-installs-a-crypto-miner-on-pcs/