Security experts blast LastPass for misleading users about stolen password vaults and data
LastPass suffered two data breaches in a span of 3 months. The first hack occurred in August, while the 2nd one happened sometime later.
Martin's write-up explains what LastPass' statement had to say about the recent security incident. The situation could actually be a lot worse. Many security researchers have blasted the company for misleading its users about the stolen password vaults.
Wladimir Palant, the creator of AdBlock Plus was among those who slammed the statement. He says in an article on his blog, that by releasing the update right before the holiday season, LastPass wanted to make sure the news flew under the radar. That's a sneaky move.
Palant called the statement as "full of omissions, half-truths and outright lies", and that the company had tried to draw focus to the 2 hacks as two separate incidents, to cover up the fact that they are related to each other. As a matter of fact, LastPass has not revealed when the 2nd attack took place, and Palant says that this could have happened in September itself. He also points out that the hackers could have collected all IPs associated with a user, website URLs which were unencrypted, to profile their activity.
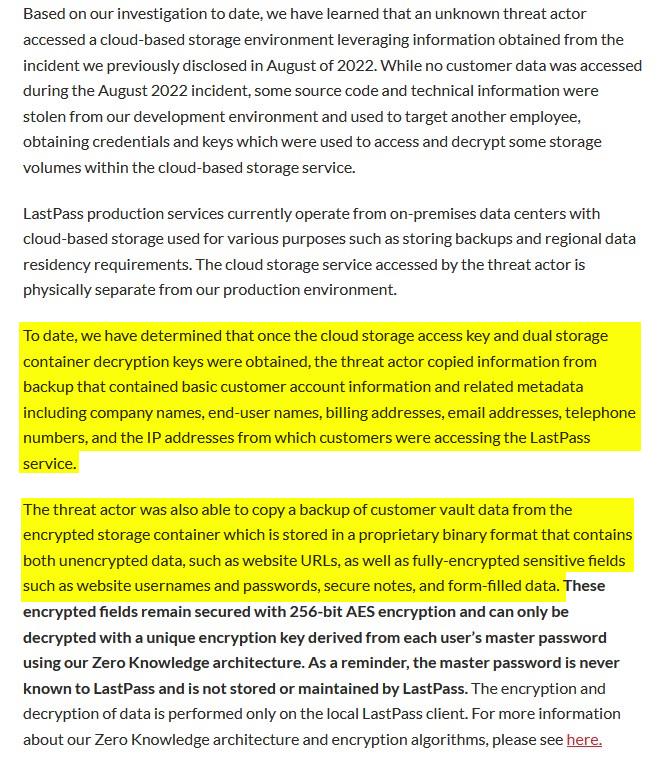
Here's the primary issue, LastPass claims that its Zero Knowledge architecture and 256-bit encryption will protect user data from being accessed by hackers, because "it would take millions of years to guess your master password using generally-available password-cracking technology."
This claim has been criticized by Palant, and Jeffrey Goldberg at 1Password. They say that it may take a long time for hackers to guess the master password, only if LastPass had forced its 12-character minimum password requirement. While the rule came into effect in 2018, it was only mandatory for new users (default setting), existing users were never asked to change their password. So, thousands of users could actually been using a weaker password.
This is really important, because most people would not be using a master password generated by a password generator, and this greatly increases the risk of their vault being breached. The fact that LastPass only hashes passwords with 100,000 iterations (PBKDF2) was also criticized by the researchers. The company had been using 5,000 iterations as the default value, which is incredibly low. Goldberg says it may cost just $100 for a hacker to run ten billion guesses to crack the passwords hashed with PBKDF2 (100,000 iterations).
Jeremi Gosney, a Senior Engineer at Yahoo, called "LastPass's claim of "zero knowledge" is a bald-faced lie." He also says that users assume that their vault is stored in an encrypted database which is protected, but this is not the case, and that LastPass stores your vault as a plaintext file, and that only some of the fields are encrypted.
When I wrote about the hack, I speculated that the only customer information that were stolen would be the things that you'd find on an invoice, because that's how LastPass had described the incident. I was quite shocked by the disclosure from the company when they admitted the threat actors gained access to users' password vaults and other data. I know people who were using it on a daily basis, and I've spoken to them about migrating away from the service. The Verge observes that this is in fact the seventh time that LastPass has been breached.
Let's face the truth, such hacks could happen to any cloud based password manager. Even though every company employs its own security protocols, no service is 100% foolproof or hacker proof. In the end, the quality of the security system, and how prepared they are to handle such threats make all the difference.
In this case, there is no doubt that LastPass made an absolute disaster of managing the post-hack process. Why did they hide the nature of the original attack? Why not acknowledge that the hackers managed to access crucial employee data, and that it could lead to further repercussions? Did they end their security audit prematurely or not conduct a thorough scrutiny? Why didn't they disclose the fact that user's vaults could have been stolen earlier?
The decent thing to do, the professional thing to do, would have been to admit their mistake the moment they realized their servers had been breached. They should have warned users as soon as possible to change their passwords, to protect their online identities, bank accounts, etc. Users may not have been pleased to hear the news, but they would have applauded the responsibility and effort to notify them.
Instead, all the users got was a vague statement that possibly arrived months later, and casually admitted that LastPass had been hacked, and that users could potentially lose access to their priceless accounts, and that the company wasn't to be blamed for this. I'm guessing they took their time while working on the legal side of things, to find some loopholes or safety net to protect themselves from potential lawsuits.
I got the "Update on Recent Security Incident" mail from LastPass on December 28th, a whole week after they originally announced it on their blog. I deleted my primary account a couple of years ago, but I never had important passwords saved there, I just had some test accounts there, but they contained fake information. But if I were a regular user, I'd have been upset by the delay in notifying me about the risks, and the awful way the issue has been handled.
If anything, these shenanigans have only made it worse, and it will lose the trust of your users. I don't think that LastPass can recover from this mishap, and it's time to ditch it for your sanity, and the security of your accounts.
If you want a free alternative, there are two good options to consider, and both support importing your passwords. Speaking of which, I strongly recommend changing all of your passwords (or at least weak ones, those without 2FA) that were saved in LastPass.
Bitwarden is a cloud-based password manager that is available across all major platforms (Windows, macOS, Linux, Android and iOS). It even has browser extensions for Firefox and Chrome. Bitwarden has an optional premium subscription that costs $12 a year, that's not a typo it actually costs just $1/month, and it gives you some extra features like YubiKey and FIDO2 (for 2FA), 1GB storage space for file attachments, emergency access, etc. Don't want to pay for it? That's fine, the free version is just as good, and you can even self-host it on your own server if you're tech-savvy.
KeePass is the other alternative that I recommend, it's an open-source, offline password manager available for Windows, Linux and macOS. There are many unofficial ports too, the most notable one for desktops is KeePassXC, it has a nice UI, some additional features, and a browser extension for Firefox and Chrome, which is useful for autofill.
There are quite a few KeePass forks available for Android and iOS that you can use on your phone, some of these mobile apps support cloud storage services like Google Drive, OneDrive, Dropbox, etc., so you can use it like a regular cloud-based password manager by placing your encrypted vault in your cloud drive. I prefer Keepass2Android on Android and KeePassium on iOS.
Is it safe to store your KeePass vault on a cloud storage server? Yes, you should use a strong unique password for your cloud account, and enable 2FA for it. That's already 2 layers of security, the encrypted vault with its own unique password acts as a third layer, it's safe to use it this way.
Note: I know that 1Password is a popular paid alternative, but I haven't used it, so I can't comment on its quality.
You should use a strong and unique master password instead of a pronounceable one, though passphrases are considered secure too. For best results, use your password manager's password generator to get a secure one. Make sure it has a some numbers and special characters, and a mix of lower and upper case letters. All you need to do is memorize the password, keep typing it a few times, and within no time it should be just as easy to remember as regular passwords. You can even write it down and store it securely, maybe put it in a plastic wrap and stick it somewhere where it can't be found by others easily, or place it in a safe, or hide it discreetly inside a book.
Deleting your LastPass account:
Please take a backup of your LastPass Vault before deleting your account, otherwise you will lose access to your passwords, notes, etc. You may export the contents to a CSV or XML file. KeePass, Bitwarden and other password managers allow you to import the file's contents, and save them in their own vault.
Refer to this support page for further details.
Note: TOTP codes cannot be exported directly, you will have to set up a different authenticator app manually. Aegis for Android, and Raivo OTP for iOS are my preferred apps, they are free and open-source. You may also consider using the Microsoft Authenticator (Android, iOS) or Google Authenticator (Android, iOS) apps, though they are not open-source, they are safe to use. Authy suffered a data breach a few months ago, which is why I'm not recommending it.
You can delete your LastPass account from this page.
WARNING: Once you delete your account, you cannot recover any data from it. Only do so after migrating your data to a different app.
Lastpass breach is costing me 1500€ between my wife’s and my VISA card being stolen a from it’s vault and unauthorised transactions on the Playstation Store being made. Can’t figure out how they got behind a two factor authentification that exists on the card.
Obviously the only people to be able to crack down on it is Sony but they do not take any action or reply to emails or phone calls.
I work in the security field.
While this article is informative, it is missing some important components. I did my own research and I am familiar with most password mangers. When choosing a password manager, I consider a vendor’s direct experience as well as their technology and future plans. In 2016, I switched to a vendor who offers passwordless login and have never looked back. With this solution, every login uses a fresh master password. It is now 2023 and this vendor is the only one to offer a passwordless password management product.
Bitwarden is open source meaning their source code is public and hackers may consider decoding. Thus, it is important to consider the potential security risks before deciding to use an open source password manager. If you truly believe in open source, perhaps you could ask your financial institution to start using open source code for their systems. I guarantee you will not sleep well that night!
Reading the source code might make some people (those who can read source code) feel safer about using Open Source. However, having the source code doesn’t allow hackers to crack strong passwords that are properly encrypted. Having the source code means people can determine if their encryption algorithms are correctly implemented.
They should rebrand as LostPass.
Hi Ashwin, thank you for the well-written article. May I point out however that neither me nor Jeffrey Goldberg actually say that not enforcing password length is the issue here? That’s merely some negligence on top. The issue is rather that human-chosen passwords are nowhere near random. And this makes them far easier to guess than LastPass’ estimates suggest.
Btw, I’d appreciate it if the link to my blog would actually link to my blog article rather than LastPass’.
I’m a former LastPass user. I switched away when they came up with the mind-bogglingly stupid idea of requiring you to click on a link in an email to access your vault—you know, the vault where the password to your email account is stored. Now they’ve been economical with the truth about the recent hack, and we’ve learned that their claim of zero knowledge was false. This, I think, is the most serious problem. Aside from the fact that LastPass’s users should be able to trust them implicitly (and clearly cannot), their failure to encrypt the URLs means the hackers now have a treasure trove of information that could give them important clues as to which accounts are most likely to be high-value targets, and may provide all sorts of opportunities for phishing and possibly even blackmail.
Having said that, there are a couple of points that occurred to me.
First of all, LastPass has never compelled nor encouraged anyone to use a weak master password, and so if any user did, it’s a personal choice that user made. Even enforcing a 12 character minimum wouldn’t stop someone using password1234 as their password if that’s what they wanted to do. There are plenty of things to blame LastPass for, but poor choices by users shouldn’t be one of them.
Secondly, 10 billion guesses for $100 sounds like a good deal, and 10 billion guesses would probably be enough to crack many people’s passwords, since most people don’t use strong passwords, but it wouldn’t get an attacker very far against even a moderately strong password. For example, there are about 2 x 10^14 possible eight character alphanumeric passwords, so it would cost an attacker about $2 million to try them all. If you include all the characters (except space) on a standard US keyboard there are about 6 x 10^15 possible eight character combinations, so it would cost the attacker around $60 million to try them all. If the attacker believed that the target had used a four word XKCD type password (e.g. correcthorsebatterystaple), and believed that the words were all drawn from a particular word list containing 10,000 words, there would be 1 x 10^16 possible combinations, and it would cost $100 million to try them all. Of course, if the attacker was right about what kind of password they were looking for, they might hit the right combination early in the search. On the other hand, in most cases it’s very unlikely that the attacker would know what type of password it is, so they might waste a lot of time and money trying out possible passwords that are nothing like the actual password they are after. It seems unlikely that the LastPass hackers will spend significant sums of money trying to crack the passwords of ordinary users. They might try common passwords on every account, and spend a bit more on trying to get into accounts they deem high value, but an unimportant user with a reasonably good password should be safe, unless LastPass has messed up in the implementation of their encryption, in which case all bets are off.
Keep advertising, praising and paying all the cloudy-password-managers, Nuts.
I don’t know why people save their passwords with apps like Lastpass. Why just not use your in-browser password manager. They’re secure enough to not worry about.
It’s generally believed (among security pros) that browser password storage is *NOT* as safe as a dedicated manager like LastPass or Keypass. There are too many tools that can yank passwords out of the Chrome password store for example. Never keep your passwords in your browser.
Because their favourite YouTube e-celeb told them to do so. People nowadays cannot think for themselves anymore.
What exactly is a “threat actor” and what exactly is the process of
“leveraging information”??
Which pronunciation is recommended if you want it to sound really important — LEVVERaging or LEEVERaging?
..obscurantic jargon.
Let’s all hope Jennifer Lawrence doesn’t use LastPass.
What does that even mean, lol.
Its fappening.
LOL It’s a reference to when her iCloud account was hacked years ago exposing some unflattering nude photos she had saved there. Other celebrity accounts were hacked as well but she received the most news coverage over the issue.
@Mothy
Thanks for sharing the reference. This year looks like it is saying goodbye with a bang lol.
Anyone who keeps their passwords somewhere accessible in a cloud either has nothing valuable to protect or is too naive for their own good.
I keep mine encrypted on my own PC. Everything has a different password. The encrypted files contain abbreviations of passwords, not the actual password. Only I would know what the abbreviations mean. A couple are not saved anywhere.
Look at how many bitcoin accounts get hacked so frequently. There should be none. If crypto can get stolen almost at will it seems, why would your dinky cloud password file be safe? The only thing actually saving most is my belief that few actually have anything worth stealing. If you actually had real money, why would you save the password to it online with strangers?
It is not healthy to be so paranoid. With proper configuration, many password managers are secure enough. Lastpass just happens to not be a good company.
@Tony
“Lastpass just happens to not be a good company.”
A good company? What a naive thought! There are 3 kinds of companies- bad, worse and worst, and all of them exploit for profit the extreme naiveté and stupidity of the masses.
Excellent article, ASHWIN, and I mean it. Documented.
“They [Palant, and Jeffrey Goldberg] say that it may take a long time for hackers to guess the master password, only if LastPass had forced its 12-character minimum password requirement. While the rule came into effect in 2018, it was only mandatory for new users (default setting), existing users were never asked to change their password. So, thousands of users could actually been using a weaker password.”
Indeed. Makes me jump to password requisites upon Websites’ registration and, until FIDO takes the relay, sites themselves should make strong passwords an obligation especially if they don’t provide 2FA.
What more to add to the article besides an implicit conclusion : avoid LastPass and if you use it, recover your data, delete that data before closing your account and switch to a new password manager without forgetting to modify your credentials, which may be problematic when they are numerous, or at least modify those for accounts free of 2FA.
I’d add : for HCD (Highly Confidential Data, in my words) I use NO password manager, whatever they be, even local : I have in mind Credit Cards, bank accounts and a few others.
Bitwarden here. Should I switch to a local vault I’d consider KeePassXC, that I discover here, given it’s browser extension for Firefox and Chrome, “which is useful for autofill” and it certainly is.
Very nice and instructive article. I’m backing up this page (as i do with several Ghacks articles) with another excellent extension : SingleFile :=)
Thank you, Tom. The reason why I didn’t suggest deleting the LastPass account is because some people might do it before importing their passwords to another service, in a fit of rage, or panic. Readers may skimp through the article, missing the important step of backing up their vault. That could be disastrous.
Migrating to a different program and changing the passwords is a safer option. Once they do that, then they can delete their LP account.
You’re right, maybe I should mention it in the article, perhaps in bold text to ensure folk don’t miss it. I’ll have a word with Martin and decide on this.
I use the SingleFile extension too, it’s really useful.
@Ashwin, my comment was in no way a critic of your article, should it be for the sole reason that writing an article differs from commenting it in that advice is to be handled with extra precaution given it may be considered by readers as an incursion in objectivity so to say or into their own subjectivity (happens often!). Your article states the facts, the risks, no point in forcing the reader to a conclusion if the reader is blind to the conclusions that prevail. I added my own touch because i’m a commenter, I wouldn’t had if i were an article’s author. A commenter has the privilege to add his own, personal, sometimes excessively personal reasoning. :=)
I didn’t view it as negative at all, in fact it was a very good suggestion. I have discussed it with Martin, and we will be updating the article to include the steps to delete the account, as well as how to backup the data, alternative TOTP apps, etc.
I know you are a regular here, and your comments are always constructive.
Hi,
I’m not tech savvy and most of the things discussed seem like scribble scrabble to me. In other words, I don’t understand your type of technical linguistic information. I do have an issue with an Android that’s older, not on front street, less than comparable to most high tech like any I product. However I have an issue I can get any recognizable information to solve. I had a particular major support engine email address for over 5byears that had a program built by that developer for that company. I have been locked out of both with recovering either looks super slim. What can I do that is simply enough for me to understand and apply to my device to recover my accounts without being bombarded by things that may take more than a quick moment to comprehend and apply? Every inquiry to that company is answered by a pre recorded or written response, ” you are no longer being watched,” and what does that mean? I can never get a name, direct contact information and the help directions from that companies community has not yet uncovered whatever my phone’s problem is. How at the very least can I retrieve some if not all information from email, phone line associated with the email directly and all other apps developed for that company, and my games? Can anyone help? Goo
Thanks @Ashwin for the good advices! Also thanks for the article by the way. :]
Always good to see you around here John :)
How many times has ghacks recommended LastPass, five, ten, a hundred? Sure, if you want ALL your passwords leaked in one go, passwordmanagers are amazing! Kinda like losing your wallet, passport, ban account, car keys and home keys at the same time, endless fun! What makes it even funnier is that LastPass LIED about their safety and lied about everything in between too. Still continue lying. Now why would we assume other companies don’t?
If you have a major disaster at home without a cloud account?
If you need ease of sharing with different devices?
If you are overseas on holiday and your devices are at home and you need access for some reason?
What if this and what if that, there are many reasons to lower your security, and while valid for some, they may not be as valid for others. I would rather trust KeePass, and if you really need it uploaded to someone else’s computer, use 7zip to compress and encypt it. Now at least if something happens, you can only blame yourself.
Keepass only works so long in Australia’s flood or bushfire zones… unless you save it to cloud, of course.
Well, Bitwarden for example is open source, and you can find it on GitHub.