Thunderbird 102.5.1 fixes a security issue in the email client
Thunderbird 102.5.1 is a security update for the open source email client that patches a single security issue in the application. The new version of Thunderbird includes several non-security fixes and a Mail extension API update.
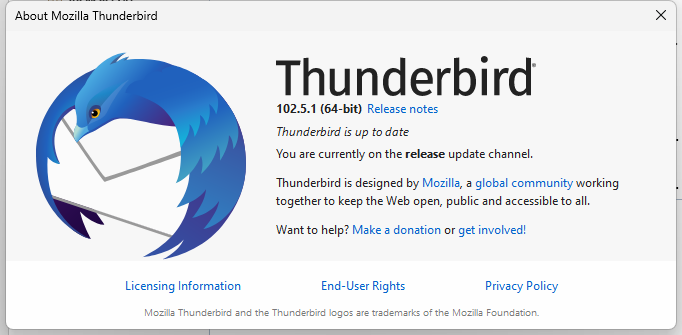
Thunderbird 102.5.1 is already available. Existing users may speed up the installation of the update by selecting Menu > Help > About Thunderbird.
The email client displays the current version and runs a check for updates. Any update found may then be installed to resolve the security issue the non-security issues.
Thunderbird 102.5.1
The single security issue that affects previous versions of Thunderbird has a severity rating of moderate. The official security notice reveals that it could result in the loading of remote content in Thunderbird, even if remote content is blocked by default in the email client.
CVE-2022-45414: Quoting from an HTML email with certain tags will trigger network requests and load remote content, regardless of a configuration to block remote content
The leak requires quite a few conditions and is likely the reason why it has been rated moderate. Users would have to reply HTML emails or quote them using other means, and the HTML email needed to contain either a Video tag with the Poster attribute or an Object tag with a Data attribute, for the leaking to occur.
Thunderbird 102.5.1 addresses two non-security issues as well. The first displayed the calendar picker "behind" the Send Later window. The second issue omitted the copy to again menu after copying a message to a folder with an unicode name on an unicode-enabled IMAP server.
The new Thunderbird release includes a number of WebExtension API defects that were uplifted from development versions of the email client. Thunderbird extension developers may want to check the list on Bugzilla for a full rundown.
Here is the link to the official release notes of Thunderbird 102.5.1 for those interested.
Thunderbird 102 users may want to install the update as soon as possible, even though it seems unlikely that the issue is exploited on scale.
Now You: which version of Thunderbird do you run, if any?
So how can i manage that the image is shown, regardless which TB version i have?
Version 102.5.1 will not show an image in the mail signature, whereas version 102.4.2 will.
That sounds like a pretty big bug with the tag, not moderate.
How often do you quote reply spam mails with malicious links?
Doesn’t have to be spam. It’s common for legitimate email accounts to be taken over.
Again, another sign that you shouldn’t be using outdated software. Many still use older versions of Thunderbird due to aesthetics.