Google Chrome Canary gets experimental Encrypted Client Hello (ECH) support
Google Chrome Canary users may enable experimental support for Encrypted Client Hello (ECH) now. Encrypted Client Hello, also referred to as Secure SNI, improves the privacy of Internet connections. It is rather technical, but broken down to its core, ECH protects hostnames from being exposed to the Internet Service Provider, network provider and other entities with the capability of listening in on the network traffic.
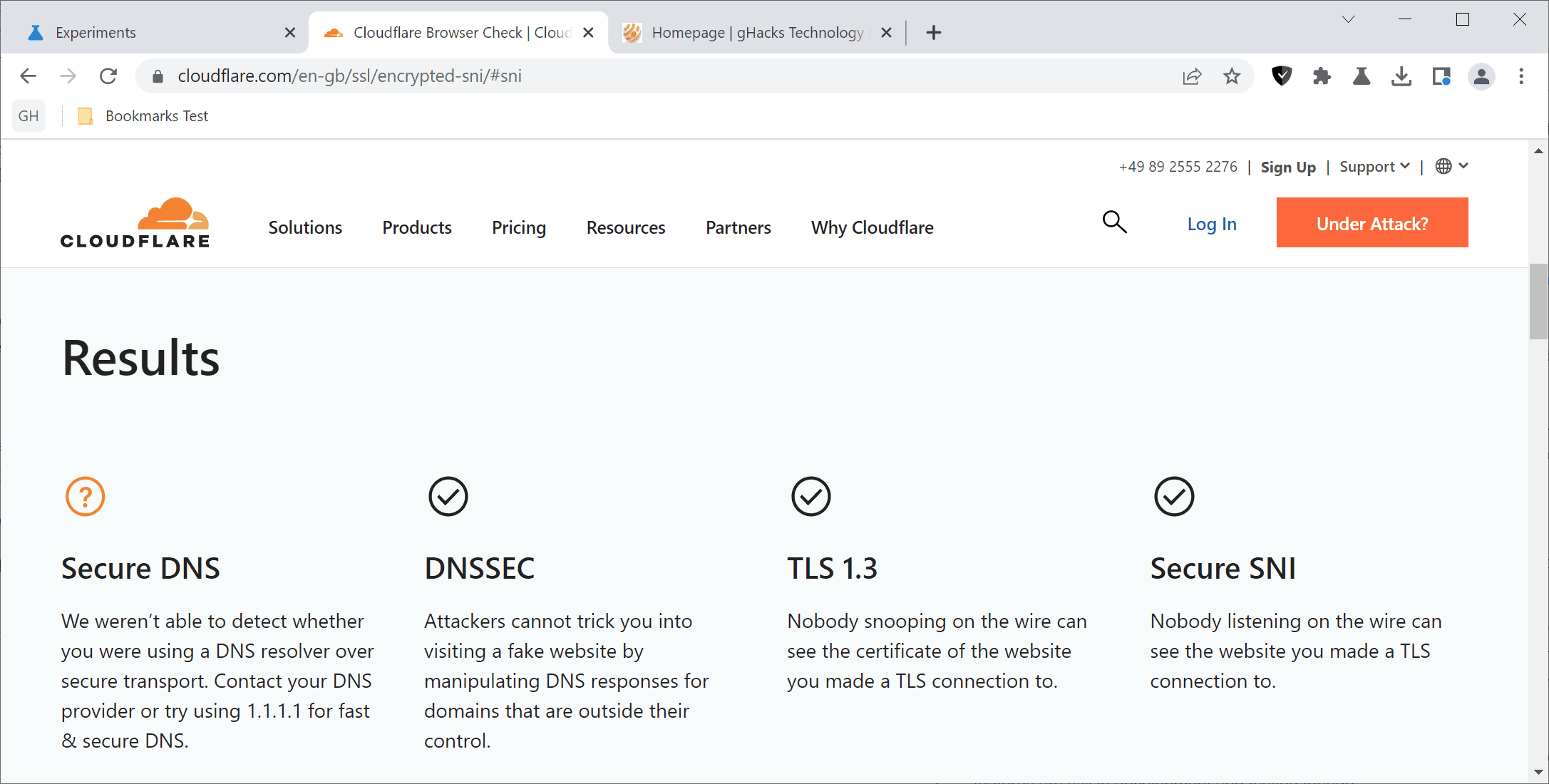
You may check if ECH is enabled in your browser using Cloudflare's Browsing Experience Security Check website.
The introduction of ECH support in Google Chrome Canary marks the beginning of a wider rollout among most Chromium-based browsers. While experimental flags may be removed without further notice at any time, it seems unlikely that ECH support will not be rolled out to Chrome Stable and other browsers based on Chromium. Mozilla added support for ECH in 2021 already in Firefox.
Chrome Canary users who want to give this a try need to make the following adjustments in Chrome Canary:
- Load chrome://settings/help to make sure that the latest version of Chrome Canary is installed. Chrome checks for updates and will install any that it finds. A restart is then required to complete the updating.
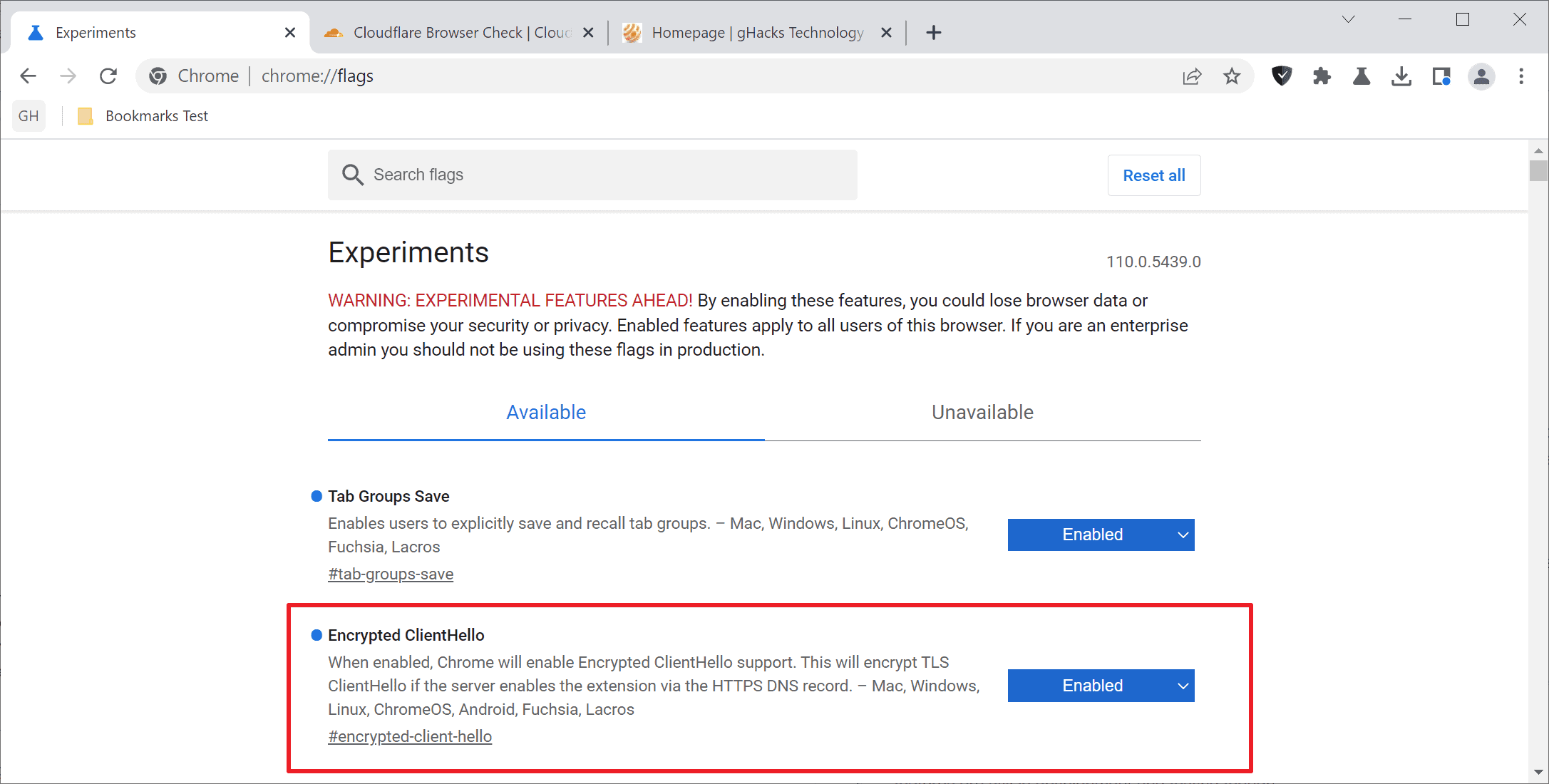
- Load chrome://flags/#encrypted-client-hello in the browser's address bar.
- Set the status of the Encrypted ClientHello flag to Enabled.
- Restart Google Chrome.
Encrypted Client Hello is enabled in Chrome after the restart. You may undo the change at any time by setting the status of the flag to Disabled using the step by step instructions above. Use Cloudflare's test page or any other test page to find out if the feature is working as advertised.
Google describes the feature in the following way:
"When enabled, Chrome will enable Encrypted ClientHello support. This will encrypt TLS ClientHello if the server enables the extension via the HTTPS DNS record"
Web servers need to support the feature, which means that it does not work on the majority of sites visited in Chrome Canary at the time of writing. The feature is available for all supported operating systems, including Windows, Mac, Linux, Android and Chrome OS.
Now You: do you use Secure DNS, ECH and other security/privacy features? (thanks ISO8601 for the tip)


















How to enable ESNI in Firefox:
about:config
network.security.esni.enabled > true
For Firefox versions >85:
about:config
network.dns.echconfig.enabled > true
network.dns.use_https_rr_as_altsvc > true
The first-paragraph sentence ” Encrypted Client Hello, also referred to as Secure SNI, improves the privacy of Internet connections” is confusing.
First, I think you want “Encrypted SNI” (=ESNI), not “Secure”.
Second, “previously referred to as” would be clearer than “also referred to as”. ECH replaces ESNI.
Details: https://en.wikipedia.org/wiki/Server_Name_Indication#Encrypted_Client_Hello
Google doing something that increases user privacy? That doesn’t sound like them. They probably still get you telemetric data, somehow.
Google thinks that the user privacy does not apply to Google’s capturing and use of your personal data. However, they will gladly help you protect yourself from anyone who is not paying them to use the information they have about you.
Of course this serves the purpose of motivating those who can no longer get access to your data to pay Google to use it for them.
This flag is already available in Chrome Stable:
https://uploads.disquscdn.com/images/d92200633cb76da8536d835a8269b0115c37d134cb1e724397c82abd170b8ac9.png
The flag was added in June in Chrome Canary:
https://chromium-review.googlesource.com/c/chromium/src/+/3698827
.
Very interesting upcoming feature, I wonder when Edge Chromium will release this great advance as well. Thanks for the article.
This is already available in Edge, go to the flags page and enable this one:
“Support for HTTPS records in DNS”
edge://flags/#dns-https-svc
@Leopeva64, thanks for the information!
“Support for HTTPS records in DNS”
edge://flags/#dns-https-svcb
This does not work with latest Edge Chromium.
How to enable SNI protection at Edge Chromium:
https://techcommunity.microsoft.com/t5/discussions/you-can-now-enable-encrypted-client-hello-encrypted-sni-or-esni/m-p/3600372
Speaking of Chrome Canary, the “Live Caption” feature now supports five more languages in this version, and in the future there will be an option to “live translate” those captions:
https://redd.it/z3rtwt
.
is there a point in turning it on if no server actually use it?
A lot of websites use CDN’s like CloudFlare to speed up their websites.
I would imagine if someone is using CloudFlare DNS on their device (such as 1.1.1.1 or 1.1.1.2 – or their DNS-over-TLS/DNS-over-HTTPS equivalents), then they will likely be directed to the closest CloudFlare CDN to them (which are spread out worldwide) and in which case the CloudFlare servers are going to support Encrypted Client Hello (ECH).