LastPass provides details on August 2022 hack
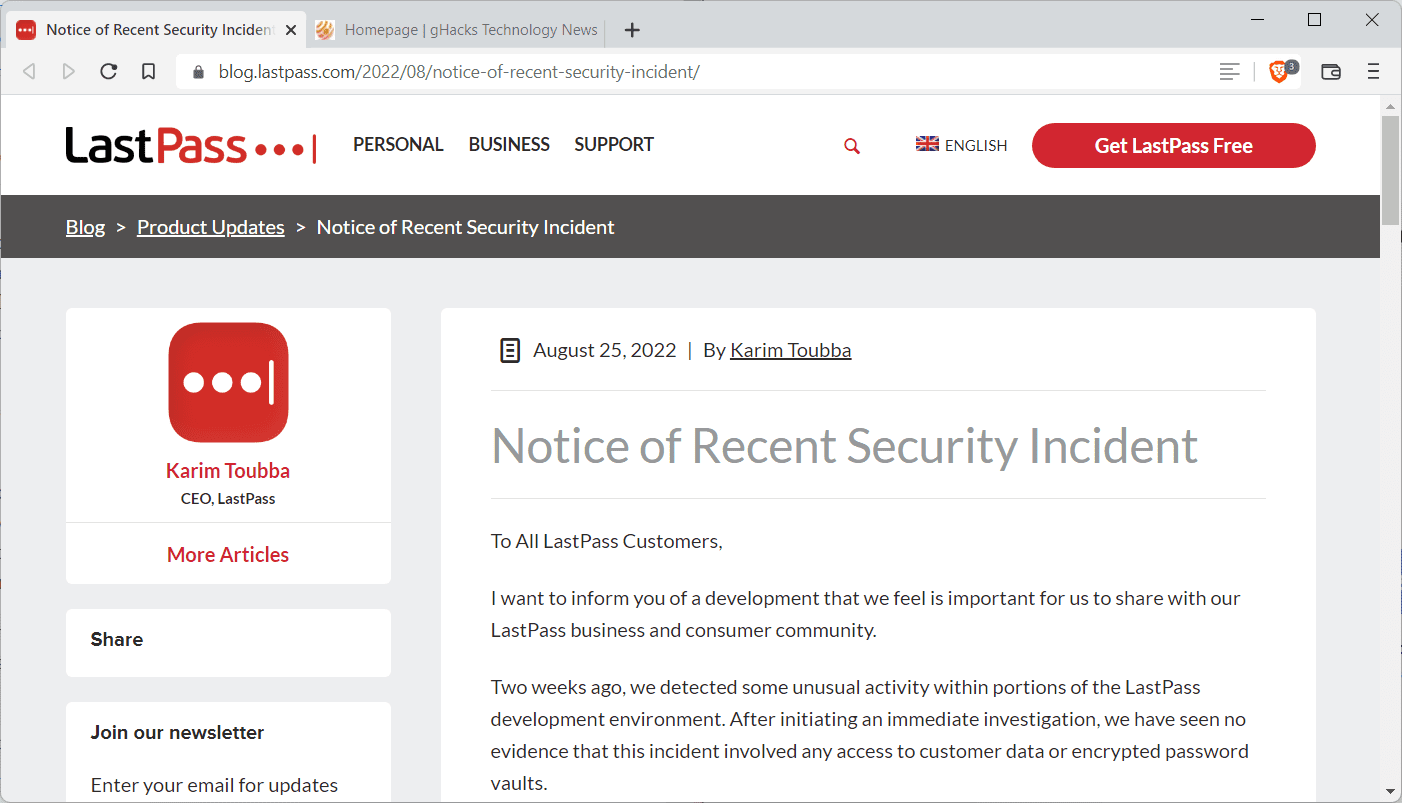
LastPass informed customers about a security breach on the company's official blog in August 2022. This week, the company published additional information about the hack after its investigation.
Back in August 2022, LastPass informed customers that it noticed unusual activity in the development environment. It noticed relatively quickly that a third-party managed to obtain access to "parts of the development environment" through a hacked developer account.
The threat actor obtained "portions of source code and some proprietary LastPass technical information", but could not access production environments or customer data.
LastPass asked the cybersecurity and forensics company Mandiant to assist them in the investigation of the incident. The September 2022 update reveals additional details about the security incident.
The threat actor gained access to the development environment for a 4-day period in August, according to LastPass. When LastPass security detected the incident, it was contained immediately.
No evidence was found that the threat actor had access beyond the 4-day period. Customer data and encrypted vaults were not accessed by the threat actor.
The attacker gained access through a compromised developer account. The account was protected with multi-factor authentication. Developer accounts are limited to the development environment, which prevented the threat actor from accessing customer data, encrypted vaults or production environments. Development environments have no access to customer data, according to LastPass.
Forensics experts analyzed the source code and production builds to determine whether any manipulation has taken place in the four day period. According to LastPass, it found "no evidence of attempts of code-poisoning or malicious code injection".
As a security precaution, developers have no direct option to push source code from development to production. A separate build release team is responsible for that, which reviews, tests and validates sources and changes.
LastPass announced that it has improved security as a consequence.
As part of our risk management program, we have also partnered with a leading cyber security firm to further enhance our existing source code safety practices which includes secure software development life cycle processes, threat modeling, vulnerability management and bug bounty programs.
Further, we have deployed enhanced security controls including additional endpoint security controls and monitoring. We have also deployed additional threat intelligence capabilities as well as enhanced detection and prevention technologies in both our Development and Production environments.
Closing Words
While a threat actor gained access to LastPass's development environment, they did not alter source code or gain access to customer data. Source code and technical information was accessed and obtained though.
Now You: which password management service do you use, if any? (via Born)
They’re lying. I spent a week going through all my websites changing passwords after I was under siege from individuals logging into various websites with my different passwords. Orders were placed and some logins were stopped with 2fa. It was social media, email, and shopping sites.
I believe they know customer data was accessed, but don’t have evidence as to how, and thus, claim it wasn’t touched.
Like I said, I had hundreds of websites that I spent days going through the password reset process and enabling 2fa if possible. Deleting this last pass account. They’re dishonest imo and not taking their security seriously.
Any comments on this alternative to all these super clever feature-stuffed super versatile absolutely confidential cloud PW programs that cost monthly charges?
– Excel worksheet on local W10 PC contains PW data base
– master PW= Excel password to open
– Further PW protection optional using ZIP software additionally
– Excel file with PW can be opened using Apple Numbers on iphone or ipad
The thorny question of where to store the master PW exists WHATEVER solution one uses including the superduper fantastic feature softwares.
Tried Keepass but too viscous and ponderous for my requirements.
Sorry, but the workflow that you are describing is much more ponderous, than investing 20 minutes to get familiar with KeePass.
Why not use Excel? Because it was never designed to be safe. We don’t know how well the PW protection of excel sheets was implemented. In the past this functionallity was easily breachable.
As soon as you add an additional layer of encryption (zipping, etc.) it gets way to complicated to quickly open the database. Esp. if you have to do it multiple times a day.
Again, KeePass was designed to store passwords (and audited, btw). Therefore I trust it a lot more than any closed source software.
Yes, it doesn’t look pretty, but who cares? KeePass + Strongbox (opens keepass files) on IOS is much much much less ponderous, than your current workflow.
Nor password written on the piece of paper is safe.
Don’t use clouds too much, they can rain.
Never fully go cloud or trust it. When your mind is in the clouds, this is what transpires. The brain isn’t getting enough oxygen, much like these LastPass clowns.
LastPass was great, and now they aren’t. I used to use and recommend them, and now I don’t.
KeePass (regular or XC) if you want simple and self-hosted, Bitwarden if you want your p/ws on the cloud.
“UsE a ThIRd-PArTY PAssWorD MaNAGEr tHey Are SAFer thAn BroWser’S PasSworD MaNAGEr”
I see a lot of people saying that, even if Browsers password manager are encrypted, you don’t need to open an account unless you want to Sync, and if you have a password or pin in your device you can’t see passwords without it.
All of 3rd party passwords (minus Keepass) need you an account, trust their servers and all that.
This is exactly why using an extension for password manager is just dumb, especially when you need to provide, email, password, bill information and whatever you have to do to get those apps/extensions working and synching.
No site is 100% immune of being hacked so I won’t consider LastPass’ misfortune as an argument to avoid it.
If I opted for another Password Manager than LastPass it’s before all for easiness, usability and its Firefox extension’s size.
I use Bitwarden, intuitive, easy, excellent reputation, less than 9MB compared to Lastpass’ 39MB. I know techies will state that size doesn’t count when only the features should be considered. I’ve tried Lastpass several years ago and I recall a heavy structure not only in terms of size (though much liter then) but in usability : the thing was so complex, complicated in my view, compared to Bitwarden. Lastpass does maybe include features not found in Bitwarden (no idea) but in my experience Bitwarden, even in its free offer, provides all that I need.
Why not Firefox’s native Password Manager? Was my choice at one time but encountered several bothers (encryption strength, popup appearing and problematic to correctly setup) which made me consider opting for a dedicated extension, though I’m not really excited by any cloud service handling confidential data. Whatever my confidence in Bitwarden’s qualification there is confidential data I never handle to a cloud service, be it encrypted or not.
Another LastPass security breach?! Nothing on “the cloud” is safe. Security or convenience, you can pick only 1.
In the spirit of accuracy, I suggest expanding that statement to “nothing connected to the Internet is secure”.
Cloud really does not come into play at all here. That storage account breached by the bad actor could just as easily have been a local storage array which was not properly protected.
As an old Systems and Infrastructure Engineer turned Cloud Engineer, I guarantee I can secure any Cloud based solution just as well as any on-prem based solution. Remember the breach started by hacking a developer’s environment and stealing code. Raw development code, IMHO, should never contain sufficient information to locate and breach production data storage — regardless of where that storage happens to be located.
The only real security from outsider threats is what we did in DOD SCIF environments. No connectivity to the outside world, equipment running in RF shielded vaults with air-gap inspection corridors, and once something electronic goes in it does not come out.
And this is why I choose offline password management. Not the first time either.
It begs the question: how was 2FA compromised on the developer account to enable access in the first place? It doesn’t seem from a read of this, that the account owner was tricked (or maybe they were?). Unlike at Twilo…