Chrome 103 update fixes 0-Day security issue that is exploited in the wild
Google published a new security update for the stable channel of the company's Chrome web browser that addresses several security issues. One of the security issues is exploited in the wild, according to Google.
Windows users of Chrome will receive the update to Chrome 103.0.5060.114 in the coming days and weeks. Since one of the issues is exploited in the wild, it is recommended to force Chrome to update to protect the device and its data from attacks.
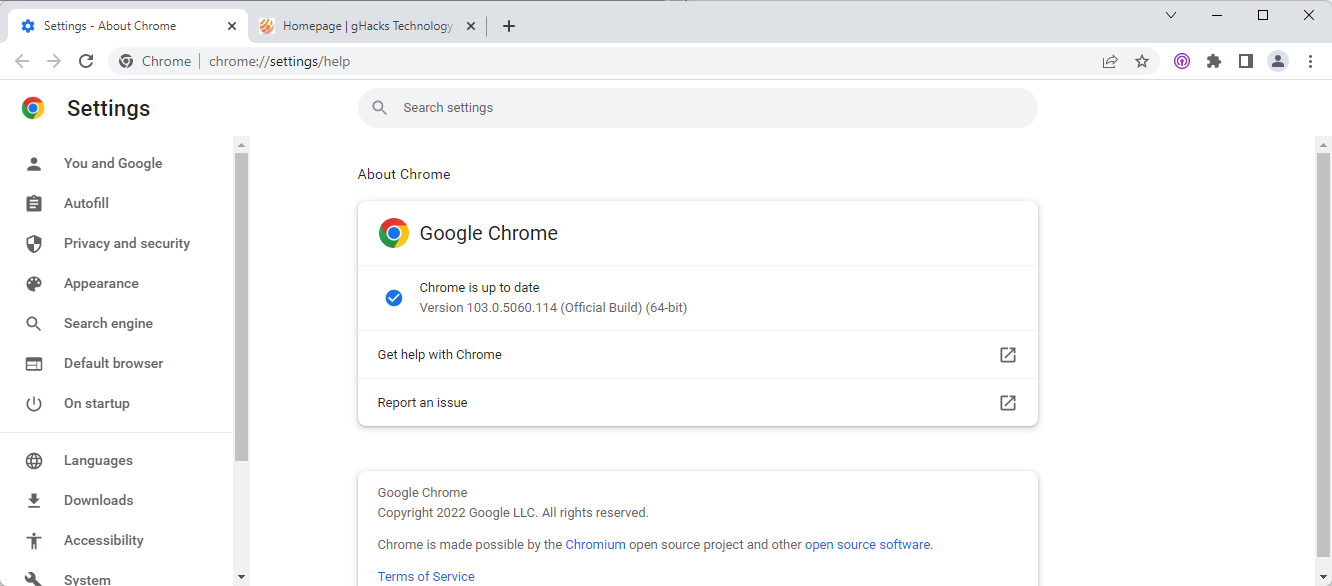
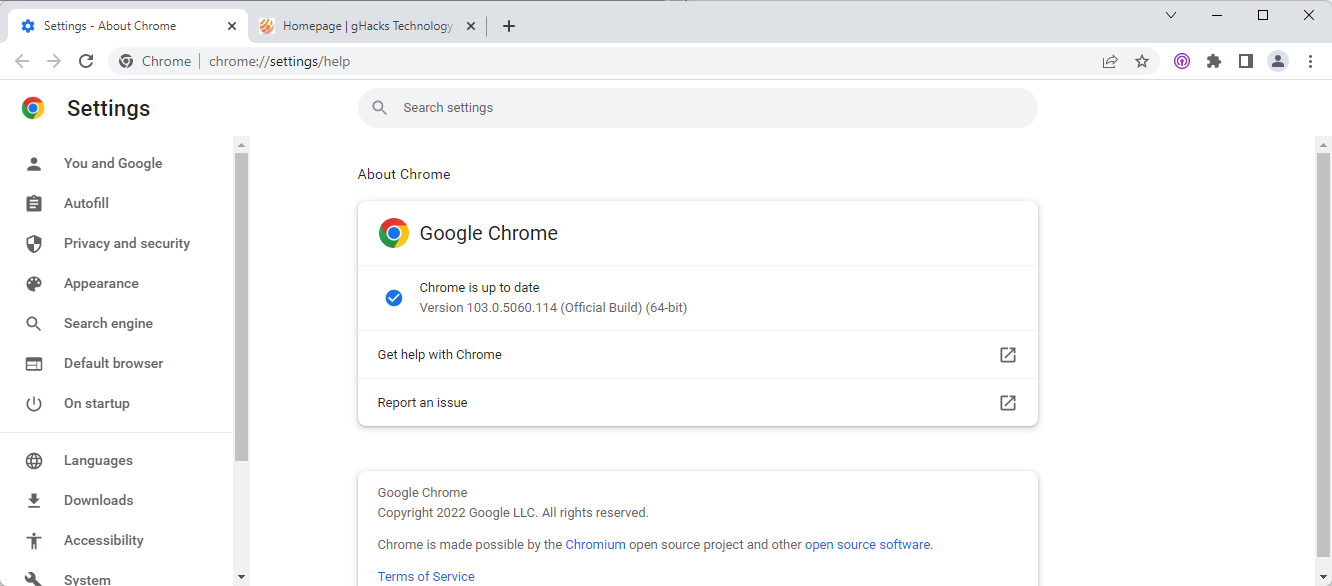
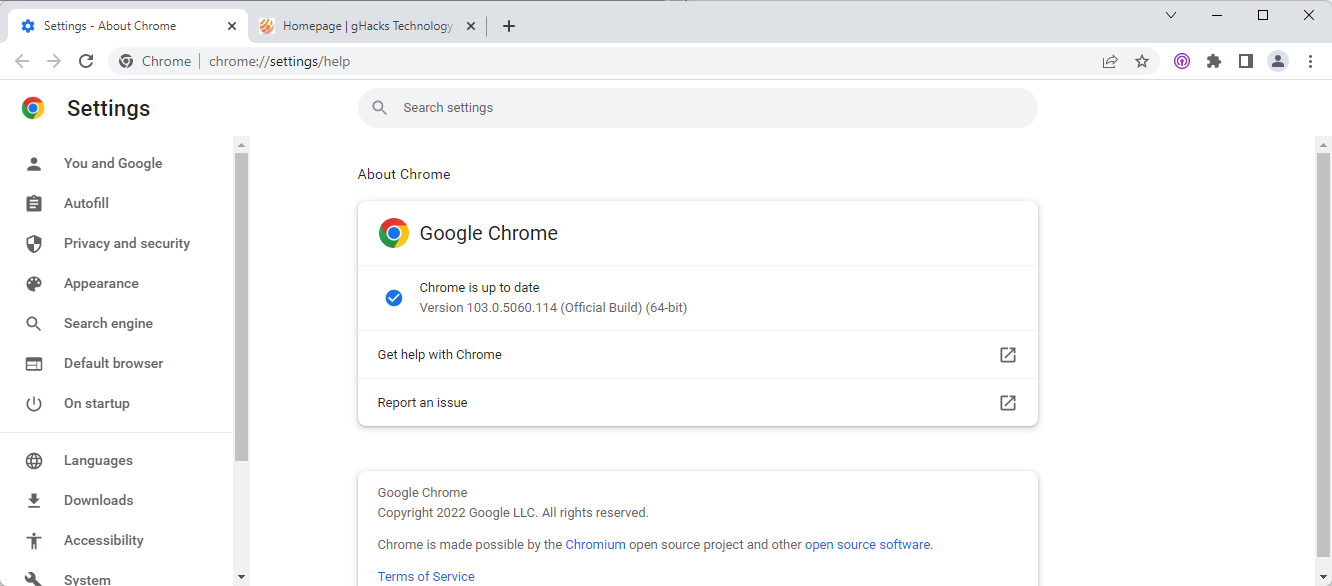
To do so, launch chrome://settings/help in the address bar of the browser, or open the page manually by selecting Menu > Help > About Google Chrome.
Google Chrome displays the current version on the page that opens. A check for updates is run, and any new version is downloaded and installed automatically. Note that Chrome needs to be restarted to complete the installation of the update.
As far as security issues are concerned, Chrome 103's update fixes four in total as revealed on the Chrome Releases website. Only three of those are listed on the page, as Google is not listing issues that it discovered internally.
Chrome 103_0-day security update
The three listed security vulnerabilities are:
- High CVE-2022-2294: Heap buffer overflow in WebRTC. Reported by Jan Vojtesek from the Avast Threat Intelligence team on 2022-07-01
- High CVE-2022-2295: Type Confusion in V8. Reported by avaue and Buff3tts at S.S.L. on 2022-06-16
- High CVE-2022-2296: Use after free in Chrome OS Shell. Reported by Khalil Zhani on 2022-05-19
All three issues are rated with a severity of high, which is the second highest after critical. Google notes that exploits for CVE-2022-2294 exist in the wild. The description reveals that the attack targets a security issue in WebRTC, which stands for Web Real-Time Communications. It is a component in modern web browsers that is used for various communication tasks and services.
Google did not share additional information at the time. Security vulnerability information is locked and only available to certain Google employees and researchers. The main reason for that is that Google does not want other malware actors to use the information to create exploits targeting it. Since Chrome updates take days or weeks to reach the bulk of installations, it is done to protect unpatched devices.
Chrome users should install the update as soon as possible to protect the device against the exploit. It is the fourth 0-day vulnerability that has been patched by Google in the browser in 2022.



















I wonder how many of these security bugs would cease to exist if there was no tracking and ad pushing from all of the Chrome based javascript and blobs?
Edge has nothing to envy to Chrome. Thanks for the article! :]
@John G.
They are based on the same codebase – Chromium. Security issues affecting Chrome will 99.9% also affect Edge.
@Iron Heart that was what I meant. The same security issues. Nothing to envy. :[
Thanks for showing the link for Chrome releases; I could have used it yesterday but sure will do so in the future when required.
Keep it growing, the commies need more APIs and bloat as attack surface :)
Here we go again. I very nearly missed the critical security loopholes within Chrome. ;)
chromium security is a joke, yet more zero-day in-the-wild exploits. welcome to the new adobe flash
@nun-with-a-gun
Name a browser that has superior exploit mitigations then, and not jokes that only superficially dodge security issues due to low market share, as there are far fewer eyes on the code *cough* Firefox *cough*…
>”Name a browser that has superior exploit mitigations then”
63,058 open bugs and Debian often can’t even build a reliable chromium package for 6-9 months at a time – exactly what standard are you basing your “superior exploit mitigations” comment on? How would anyone even know?
14,132 untriaged bug reports at the moment – no one is even keeping track of it all. Just wondering where this sense of confidence in their threat management comes from, because it’s not at all clear from how completely randomly they manage the project publicly.
> security issues due to low market share
The only person who has ever brought this up is Iron Heart. Everyone else knows better. He has claimed chromium is more secure because it has more eyes on it. The reality is that once a certain size is reached, all things are generally equal – linters, fuzzers, engineers on each patch are finite resources
> Are you aware of the size of the Chromium codebase? It’s as large as an operating system. And “open bugs”, well… A bug ticket can be opened for a question even.
Are you aware of the size of the Gecko codebase? It’s as large as an operating system. And “open bugs”, well… A bug ticket can be opened for a question even.
@Andy Prough
> 63,058 open bugs
Are you aware of the size of the Chromium codebase? It’s as large as an operating system. And “open bugs”, well… A bug ticket can be opened for a question even.
> Debian often can’t even build a reliable chromium package for 6-9 months at a time
That seems like Debian’s problem, not Chromium’s.
> Just wondering where this sense of confidence in their threat management comes from
They have one of the best cyber defense teams in existence: https://en.wikipedia.org/wiki/Project_Zero
Of course these guys are looking into the projects of their own company. As I said, a random number of open bug tickets says nothing without knowing the actual content, open bug tickets are sometimes just complaints or questions. High risk security issues in particular would not be discussed in a public bug ticket.
>”As I said, a random number of open bug tickets says nothing without knowing the actual content, open bug tickets are sometimes just complaints or questions.”
How would anyone know? As I said, there are currently 14,132 untriaged bugs – no one is even looking at them, and they go without anyone looking at them or even categorizing them for years. I’m simply questioning the messy management of the project, the same with the poor state of the releases that are usually not up to Debian’s standards.
Project Zero’s most recent blog posting notes that “Many of the 2022 in-the-wild 0-days are due to the previous vulnerability not being fully patched”, and that this problem is similar to prior years. Why are chromium vulnerabilities not getting fully patched? What’s going on with project management that causes continued issues with problems that were already found and supposedly resolved?
I’m not saying chromium is insecure by design, but I am questioning whether it is managed well enough for assurances of security to be taken at face value.
the more the better, you know. so?