Microsoft Edge 102 fixes 31 security issues
Microsoft released a new stable version of the company's Edge web browser on May 31, 2022. Microsoft Edge 102 is a security update first and foremost, that addresses 31 different security issues in the browser.
Most of the security issues affect Chromium, the core of the Edge browser, which it shares with Google Chrome and several other browsers, including Vivaldi, Brave, and Opera. Some security fixes are Edge specific, as they address issues in components that are unique to Microsoft Edge.
Microsoft lists three security issues that are exclusive to Edge:
- Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability -- CVE-2022-30128
- Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability -- CVE-2022-30127
- Microsoft Edge (Chromium-based) Spoofing Vulnerability -- CVE-2022-26905
Two of the vulnerabilities have a severity rating of moderate, one, CVE-2022-26905, a severity rating of low. None of the issues appear to be exploited at this point, as Microsoft makes no mention of that on the CVE pages.
The official release notes list four new policies that Microsoft added to Microsoft Edge 102. These are:
- AllHttpAuthSchemesAllowedForOrigins - List of origins that allow all HTTP authentication
- OutlookHubMenuEnabled - Allow users to access the Outlook menu
- NetworkServiceSandboxEnabled - Enable the network service sandbox
- UserAgentClientHintsGREASEUpdateEnabled - Control the User-Agent Client Hints GREASE Update feature
No new features are introduced in Edge 102 according to the release notes. Microsoft may introduce features in Edge updates that it does not list in the release notes.
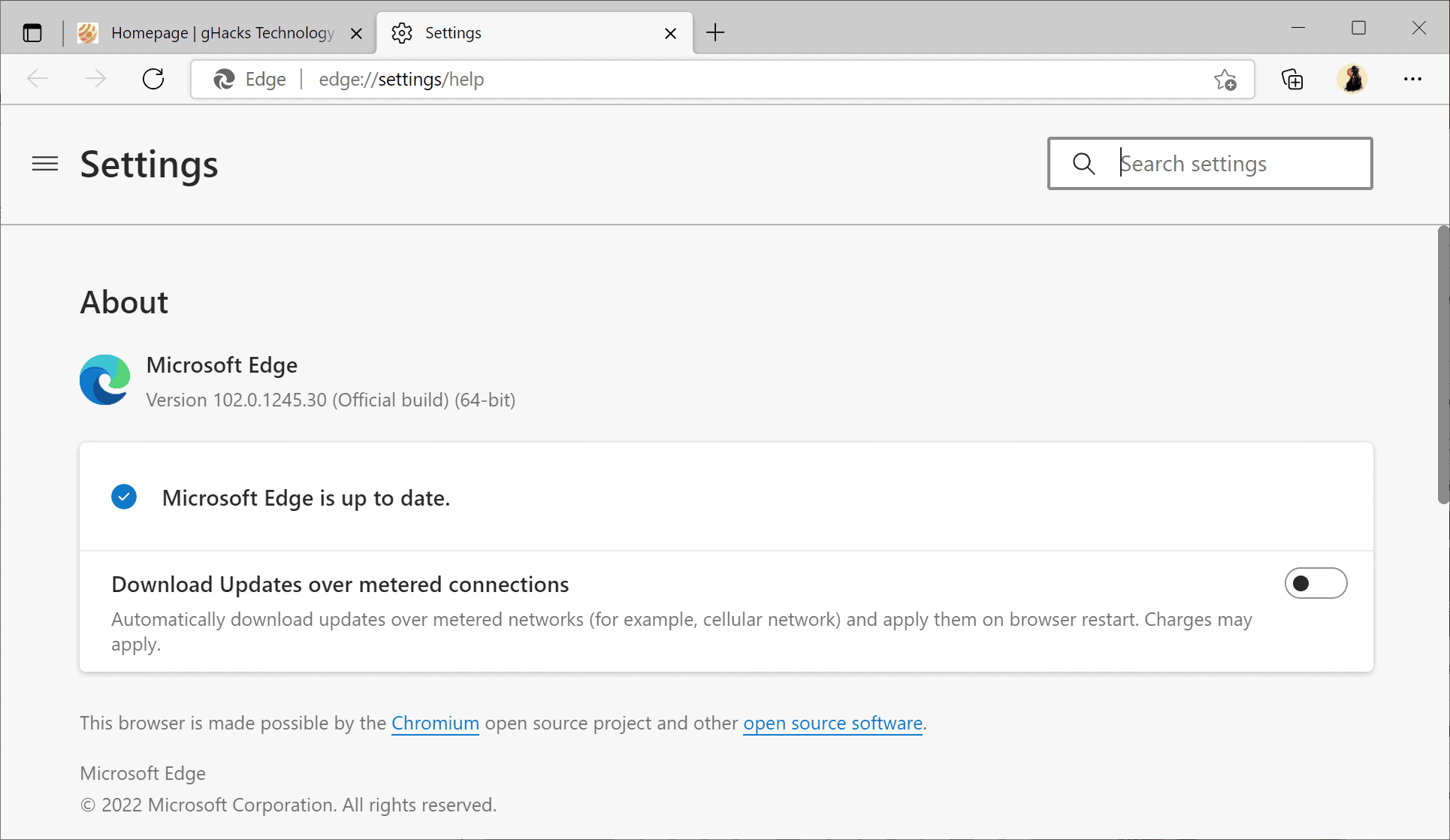
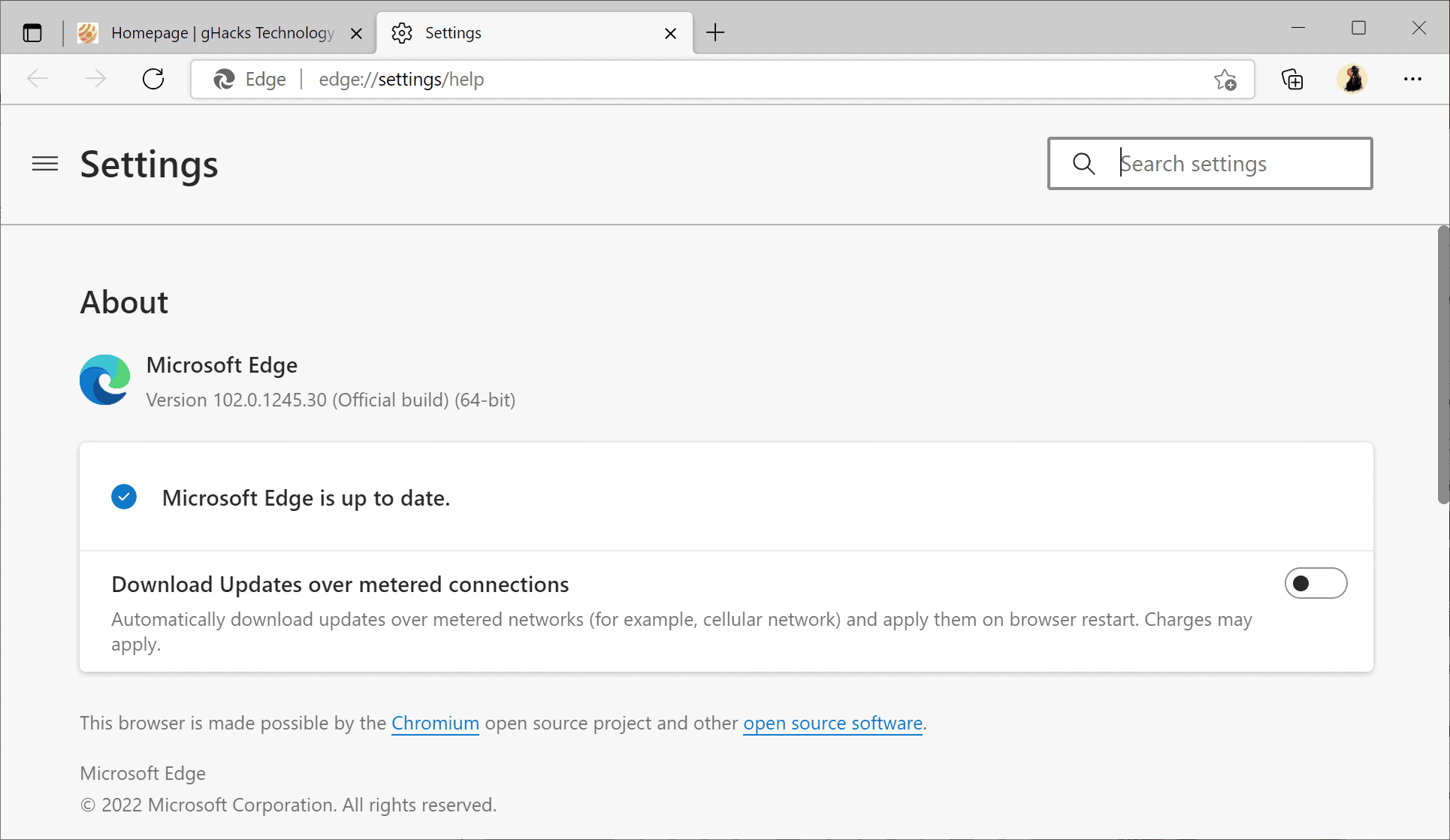
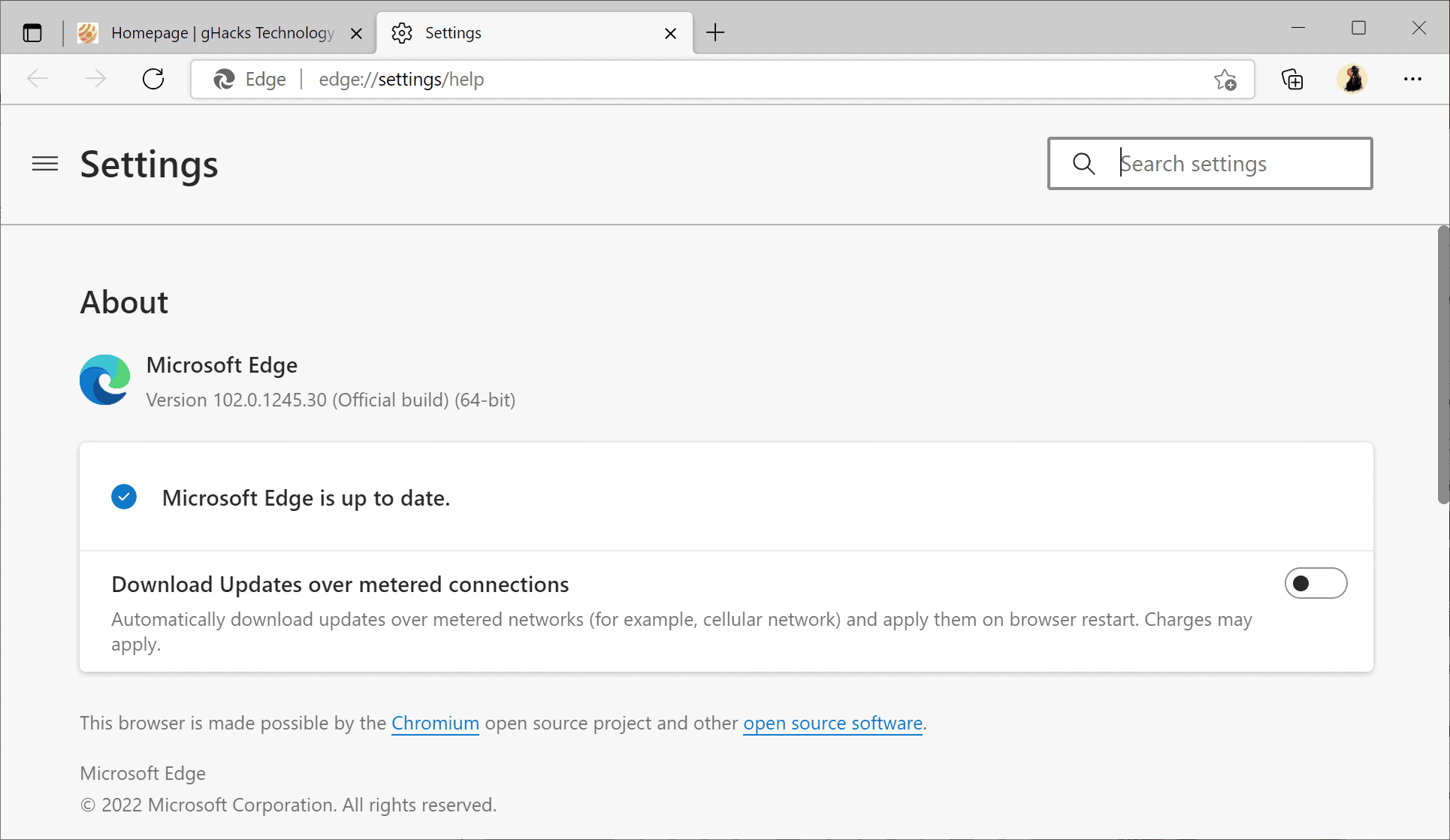
Microsoft Edge is updated automatically by default. Edge users may speed up the installation of updates on desktop systems by selecting Menu > Help and Feedback > About Microsoft Edge, or by loading edge://settings/help directly in the browser's address bar.
The page that opens displays the current version of Edge. Microsoft Edge runs a check for updates whenever the page is opened; any update that is found is downloaded and installed automatically. A restart is required to complete the update.
















So Microsoft fixed these 31 security issues or maybe Google, and Microsoft just merged the code?
I suppose that Google did it, and Microsoft just took them.
Is there any hope of Microsoft fixing the absolutely awful spell checker in Edge?
Chromium-based …enough said
Pretty sure Firefox has a lot more security problems than any chromium based browser.
> Pretty sure Firefox has a lot more security problems than any chromium based browser.
[https://rationalwiki.org/wiki/Anecdotal_evidence]
Pretty sure that is anecdotal evidence and Firefox is patched regularly. Just as any of the 4 major browsers.
@Anon
I am pretty sure the security comes down to the user.
If you dig a hole then don’t complain if you fall into it.
never had a security incident on firefox or indeed on any of the browsers i have used but then again i don’t browse like a click junkie visiting iffy sites.
Hmm chromium security.?
Gets patched continuously to give the false perception of it being secure when the reality is that is has perpetual sloppy code which is continually vulnerable to every single exploit going in the wild and even as we speak there will be an exploit just waiting to attack.
No such thing as 100% browser security and A versus B arguments are pointless.
Name a more secure browser then. I am still waiting, have asked the question many times by now.
You can troll but you have NO alternative that is any better.
> Name a more secure browser then
[https://rationalwiki.org/wiki/One_single_proof]
How to achieve a logical fallacy in the first six words. Besides that such rhetoric are deceptive:
It depends on your use case. If onion routing is your thing, then obviously stock Tor browser is the best browser for the TOR protocol.
And thus the entire argument crumbles to dust! It is the use case! Let people decide for themselves and don’t drag them into your cult please.
@Hitomi
The only cult-like behavior is when you lose your grip of reality. As I said: Irrelevancy is not security. A comparison of the base code of Firefox vs. Chromium browsers shows that Firefox lacks various exploit mitigations which Chromium browsers do have. Also, the most used browser is also the one most studied by the bad guys. All of that should be logical, but it isn’t for people like you who want to push a false narrative.
By the way, how you route your traffic has no bearing on e.g. a memory corruption exploit. How dumb is this? Are you mistaking privacy for security? Because it’s not the same thing, security is the resistance against exploits and nothing else.
> Name a more secure browser then
ask stupid questions, win stupid prizes: I dare you to objectively quantify the overall security of browsers – you can’t
@whatashitshow
Who talks about “quantify”? I sure didn’t. However, you either have certain exploit mitigations in place, or you don’t. If you don’t, you can’t claim that your shite is more secure.
> Who talks about “quantify”? I sure didn’t
You sure did. You claim one is more secure overall but to do that, which you can’t, you need to compare them, and to draw any conclusions you need to quantify each part to the same universal standard (which doesn’t exist)
Here is a real security engineer
https://old.reddit.com/r/firefox/comments/lbu6q2/why_do_people_say_chromiums_sandbox_is_better/glxjrjg/
> “How does that wash out in the end? It’s really hard to say and pretty much impossible to quantify.”
PRETTY MUCH IMPOSSIBLE TO QUANTIFY
What isn’t impossible to quantify, is that your repeated nonsense in every Firefox article is a meme
> PRETTY MUCH IMPOSSIBLE TO QUANTIFY
LOL, yeah. If anything, it is a matter of the code quality. You know the difference between quality and quantity, right? I don’t follow a checklist approach where browsers have to nominally support certain features and then calculate a result, i.e. Browser A supports X number of features while Browser B supports Y number of features, then compare. This is retarded.
Whether you call my comments a meme or not is meaningless, because I am not the one pushing the bullshit narrative that irrelevancy is the same as security. Actual comparisons of the base code support my argument that Chromium has various exploit mitigations up and running that Firefox either has not or only has alpha implementations of.
I realize that I am pissing on the parade of those who desperately want to sell irrelevancy for security, which is a complete mummer’s farce. Learn to deal with it.
>Here is a real security engineer
[https://rationalwiki.org/wiki/Argument_from_authority]
Now to the post in question from the link:
> this is continually changing though as the Gecko hardening team continues to make improvements
> Firefox contains significant amounts of code written in Rust. Those components are significantly less vulnerable to specific types of security bugs than if they were still written in C++
So the link states that the security is ever improving as the browser reaches with each updated a higher level of maturity and more parts are rewritten in Rust. Do all parts need to be rewritten in Rust? No. Only the essential ones.
So thank your for proving that Firefox is ever evolving and actively patched.
@Hitomi
> Do all parts need to be rewritten in Rust? No. Only the essential ones.
Obvious problem with your narrative: None of the most attacked parts of Firefox is actually written in Rust.
I am sure you will get over it
@Hitomi
> I am sure you will get over it
Stop pushing false narratives.
All Chromium-based browsers will become useless by end of the year with manifest v3.
as of June 1st
https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=chrome
– 95 CVE’s in 2022 for chrome
https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=chromium
– 89 CVE’s in 2022 for chromium
https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=firefox
1 so far in 2022 for firefox
nothing for gecko, 3 for blink
chromium base browsers are the new Adobe Flash
that’s disgusting .. I have just changed to Firefox and it’s brilliant
thanks roger, great links – seems like chromium is not very secure