Microsoft Windows Security Updates April 2022 overview
Microsoft has released security updates and non-security updates for client and server versions of its Windows operating system and other company products, including Microsoft Office, on the April 12, 2022 Patch Tuesday.
The updates are already available via Windows Updates, other update management products and services, and as direct downloads. Our overview assists home users and system administrators in understanding the updates and getting the information they need to update products that they use.
The guide includes direct download links, links to support websites, information about critical updates, known issues, and other bits that are important when it comes to updating.
You can check out the March 2022 Microsoft update guide here.
Microsoft Windows Security Updates: April 2022
The following Excel spreadsheet includes the released security updates for Windows and other company products. Just download it with a click on the following link: microsoft-windows-security-updates-april-2022
Executive Summary
- All supported client and server versions of Windows are affected by at least 4 critical security issues.
- Windows clients with known issues: Windows 7, Windows 8.1, Windows 10 version 1607, 1809, 1909, 20H2, 21H1, 21H2, and Windows 11
- Windows server versions with known issues: Windows Server 2008, 2008 R2, 2012, 2012 R2, 2016, and 2022
- Other Microsoft products with security updates: .NET Framework, Azure SDK, Active Directory Domain Services, Azure Site Recovery, Microsoft Edge, LDAP, Visual Studio, Microsoft Office, and others.
- Windows 10 version 20h2 Pro and Home are reaching end of servicing next month.
Operating System Distribution
- Windows 7 (extended support only): 41 vulnerabilities: 4 critical and 37 important
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Windows 8.1: 51 vulnerabilities: 7 critical and 44 important
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24497
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-22008
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24491
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Windows 10 version 1909: 68 vulnerabilities: 8 critical and 60 important
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24497
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-22008
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-24537
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24491
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Windows 10 version 20H2, 21H1 and 21H2 : 72 vulnerabilities, 9 critical and 63 important
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24491
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-24537
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-23257
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-22008
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24497
- Windows 11: 69 vulnerabilities, 9 critical and 60 important
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24491
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-24537
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-23257
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-22008
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24497
Windows Server products
- Windows Server 2008 R2 (extended support only): 51 vulnerabilities: 4 critical and 47 important
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Windows Server 2012 R2: 66 vulnerabilities: 5 critical and 22 important
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24497
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-22008
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24491
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Windows Server 2016: 86 vulnerabilities: 8 critical and 78 important
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24497
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-22008
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-24537
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24491
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Windows Server 2019: 93 vulnerabilities: 0critical and 28 important
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24497
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-22008
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-24537
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24491
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Windows Server 2022: 98 vulnerabilities: 0 critical and 28 important
- Windows LDAP Remote Code Execution Vulnerability -- CVE-2022-26919
- Remote Procedure Call Runtime Remote Code Execution Vulnerability -- CVE-2022-26809
- Windows Server Service Remote Code Execution Vulnerability -- CVE-2022-24541
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24491
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-24537
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-23257
- Windows Hyper-V Remote Code Execution Vulnerability -- CVE-2022-22008
- Windows SMB Remote Code Execution Vulnerability -- CVE-2022-24500
- Windows Network File System Remote Code Execution Vulnerability -- CVE-2022-24497
Windows Security Updates
Windows 7 SP1 and Windows Server 2008 R2
Updates and improvements:
- Fixed a Windows Media Center issue that had users configure the application on each start.
- Fixed a memory leak that was introduced in the November 2021 cumulative update. It caused a decrease in performance on domain controllers.
- Fixed an issue that could cause Event ID 37 to be logged during password change scenarios.
- Fixed an Access Denied error when writing a service principal name alias and Host/Name already exists on another object.
- Fixed a domain joins failing issue in environments that use DNS hostnames.
- Fixed an issue that prevented the changing of expired passwords when signing in.
Windows 8.1 and Windows Server 2012 R2
Updates and improvements:
- Fixed a Windows Media Center issue that had users configure the application on each start.
- Fixed a memory leak that was introduced in the November 2021 cumulative update. It caused a decrease in performance on domain controllers.
- Fixed an issue that could cause Event ID 37 to be logged during password change scenarios.
- Fixed a domain joins failing issue in environments that use DNS hostnames.
- Fixed an issue that made Windows go into BitLocker Recovery after servicing updates. (monthly-rollup only).
- Fixed an issue that prevented the changing of expired passwords when signing in. (monthly-rollup only).
- Fixed an issue that caused a Denial of Service vulnerability on Cluster Shared Volumes. (monthly-rollup only).
Windows 10 version 20H2, 21H1 and 21H2
- Support Page: KB5012599
- Fixed an issue that caused a Denial of Service vulnerability on Cluster Shared Volumes. (monthly-rollup only).
- Plus, everything that was mentioned in the preview update here.
Windows 11
- Support Page: KB5012592
Updates and improvements:
- Fixes are listed on the preview update's release page here.
Other security updates
2022-04 Security Only Quality Update for Windows Server 2008 (KB5012632)
2022-04 Security Monthly Quality Rollup for Windows Server 2008 (KB5012658)
2022-04 Security Monthly Quality Rollup for Windows Embedded 8 Standard and Windows Server 2012 (KB5012650)
2022-04 Security Only Quality Update for Windows Embedded 8 Standard and Windows Server 2012 (KB5012666)
2022-04 Cumulative Update for Windows 10 Version 1909 (KB5012591)
2022-04 Cumulative Update for Windows Server 2016 and Windows 10 Version 1607 (KB5012596)
2022-04 Cumulative Update for Microsoft server operating system version 21H2 for x64-based Systems (KB5012604)
2022-04 Cumulative Update for Windows Server 2019 and Windows 10 Version 1809 (KB5012647)
2022-04 Cumulative Update for Windows 10 (KB5012653)
.NET Framework
2022-04 Security and Quality Rollup for .NET Framework 4.8 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012122)
2022-04 Security and Quality Rollup for .NET Framework 4.8 for Windows 8.1 and Windows Server 2012 R2 (KB5012124)
2022-04 Security and Quality Rollup for .NET Framework 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012129)
2022-04 Security and Quality Rollup for .NET Framework 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2 for Windows 8.1 and Windows Server 2012 R2 (KB5012130)
2022-04 Security and Quality Rollup for .NET Framework 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2 for Windows Embedded Standard 7, Windows 7, Windows Server 2008 R2, and Windows Server 2008 (KB5012131)
2022-04 Security and Quality Rollup for .NET Framework 3.5 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012136)
2022-04 Security and Quality Rollup for .NET Framework 2.0, 3.0 for Windows Server 2008 (KB5012137)
2022-04 Security and Quality Rollup for .NET Framework 3.5.1 for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2 (KB5012138)
2022-04 Security and Quality Rollup for .NET Framework 3.5 for Windows 8.1 and Windows Server 2012 R2 (KB5012139)
2022-04 Security and Quality Rollup for .NET Framework 4.5.2 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012140)
2022-04 Security and Quality Rollup for .NET Framework 4.5.2 for Windows Embedded Standard 7, Windows 7, Windows Server 2008 R2, and Windows Server 2008 (KB5012141)
2022-04 Security and Quality Rollup for .NET Framework 4.5.2 for Windows 8.1 and Windows Server 2012 R2 (KB5012142)
2022-04 Security Only Update for .NET Framework 4.8 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012143)
2022-04 Security Only Update for .NET Framework 4.8 for Windows 8.1 and Windows Server 2012 R2 (KB5012144)
2022-04 Security Only Update for .NET Framework 4.8 for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2 (KB5012145)
2022-04 Security Only Update for .NET Framework 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012146)
2022-04 Security Only Update for .NET Framework 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2 for Windows 8.1 and Windows Server 2012 R2 (KB5012147)
2022-04 Security Only Update for .NET Framework 4.6 and 4.6.2 for Windows Embedded Standard 7, Windows 7, Windows Server 2008 R2, and Windows Server 2008 (KB5012148)
2022-04 Security Only Update for .NET Framework 3.5 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012149)
2022-04 Security Only Update for .NET Framework 2.0, 3.0 for Windows Server 2008 (KB5012150)
2022-04 Security Only Update for .NET Framework 3.5.1 for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2 (KB5012151)
2022-04 Security Only Update for .NET Framework 3.5 for Windows 8.1 and Windows Server 2012 R2 (KB5012152)
2022-04 Security Only Update for .NET Framework 4.5.2 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012153)
2022-04 Security Only Update for .NET Framework 4.5.2 for Windows Embedded Standard 7, Windows 7, Windows Server 2008 R2, and Windows Server 2008 (KB5012154)
2022-04 Security Only Update for .NET Framework 4.5.2 for Windows 8.1 and Windows Server 2012 R2 (KB5012155)
2022-04 Security Only Update for .NET Framework 3.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2, 4.8 for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2 (KB5012324)
2022-04 Security Only Update for .NET Framework 3.5, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2, 4.8 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012325)
2022-04 Security Only Update for .NET Framework 3.5, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2, 4.8 for Windows 8.1 and Windows Server 2012 R2 (KB5012326)
2022-04 Security Only Update for .NET Framework 2.0, 3.0, 4.5.2, 4.6 and 4.6.2 for Windows Server 2008 (KB5012327)
2022-04 Security and Quality Rollup for .NET Framework 3.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2, 4.8 for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2 (KB5012329)
2022-04 Security and Quality Rollup for .NET Framework 3.5, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2, 4.8 for Windows Embedded 8 Standard and Windows Server 2012 (KB5012330)
2022-04 Security and Quality Rollup for .NET Framework 3.5, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1, 4.7.2, 4.8 for Windows 8.1 and Windows Server 2012 R2 (KB5012331)
2022-04 Security and Quality Rollup for .NET Framework 2.0, 3.0, 4.5.2, 4.6 and 4.6.2 for Windows Server 2008 (KB5012332)
2022-04 Cumulative Update for .NET Framework 3.5 and 4.8 for Windows 10 Version 21H1, Windows Server, version 20H2, Windows 10 Version 20H2, Windows 10 Version 2004, Windows 10 Version 1909, Windows 10 Version 1903, Windows 10 Version 1809, and Windows 10 Version 1607 (KB5012117)
2022-04 Cumulative Update for .NET Framework 4.8 for Windows Server 2016 and Windows 10 Version 1607 (KB5012118)
2022-04 Cumulative Update for .NET Framework 3.5 and 4.8 for Windows Server 2019 and Windows 10 Version 1809 (KB5012119)
2022-04 Cumulative Update for .NET Framework 3.5 and 4.8 for Windows 10 Version 1909 (KB5012120)
2022-04 Cumulative Update for .NET Framework 3.5 and 4.8 for Windows 11 (KB5012121)
2022-04 Cumulative Update for .NET Framework 3.5 and 4.8 for Microsoft server operating system version 21H2 for ARM64 (KB5012123)
2022-04 Cumulative Update for .NET Framework 3.5 and 4.7.2 for Windows Server 2019 and Windows 10 Version 1809 (KB5012128)
2022-04 Cumulative Update for .NET Framework 3.5, 4.7.2 and 4.8 for Windows Server 2019 and Windows 10 Version 1809 (KB5012328)
2022-04 Security and Quality Rollup for .NET Framework 4.8 for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2 (KB5012125)
Servicing Stack Updates
2022-04 Servicing Stack Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB5012672)
2022-04 Servicing Stack Update for Windows 10 (KB5013269)
2022-04 Servicing Stack Update for Windows Embedded 8 Standard and Windows Server 2012 (KB5013270)
Known Issues
Windows 7 SP1 and Windows Server 2008 R2
- (Old) Updates may show as failed and may be uninstalled because the machine is not on ESU.
- Expected behavior.
- (Old) Certain operations such as rename may fail on Cluster Shared Volumes.
- Perform the operation from a process with administrator privileges.
- Perform the operation from a node that does not have CSV ownership.
Windows 8.1 and Windows Server 2012 R2
- (Old) Certain operations such as rename may fail on Cluster Shared Volumes.
- Perform the operation from a process with administrator privileges.
- Perform the operation from a node that does not have CSV ownership.
- (Old) Issues with apps using the " Microsoft .NET Framework to acquire or set Active Directory Forest Trust Information". These may fail, close, or may throw errors messages such as access violation (0xc0000005).
- Install out-of-band updates for the .NET Framework version that the app in question uses. Microsoft has links to these on the support page.
Windows 10 versions 20H2, 21H1 and 21H2
- (Old) Custom installations may not receive the new Microsoft Edge web browser, while the old version may be removed.
- Workaround described on the support page.
- (Old) Some devices can't install updates after installation of KB5003690 (June 21, 2021). Error PSFX_E_MATCHING_BINARY_MISSING is displayed.
- Workaround instructions are available here.
- (Old) Connections may fail to authentication when using smart card authentication in Remote Desktop Connections.
- Resolved according to Microsoft, should not be experienced anymore.
- (NEW) After installing the January 11, 2022 updates or later updates, recovery discs on CD or DVD created using the Backup and Restore tool (Windows 7) may be unable to start. Recovery discs created earlier are not affected.
- Microsoft is working on a resolution.
Windows 11
- (NEW) After installing the January 11, 2022 updates or later updates, recovery discs on CD or DVD created using the Backup and Restore tool (Windows 7) may be unable to start. Recovery discs created earlier are not affected.
Microsoft is working on a resolution.
Security advisories and updates
ADV 990001 -- Latest Servicing Stack Updates
Non-security updates
Microsoft Office Updates
You find Office update information here.
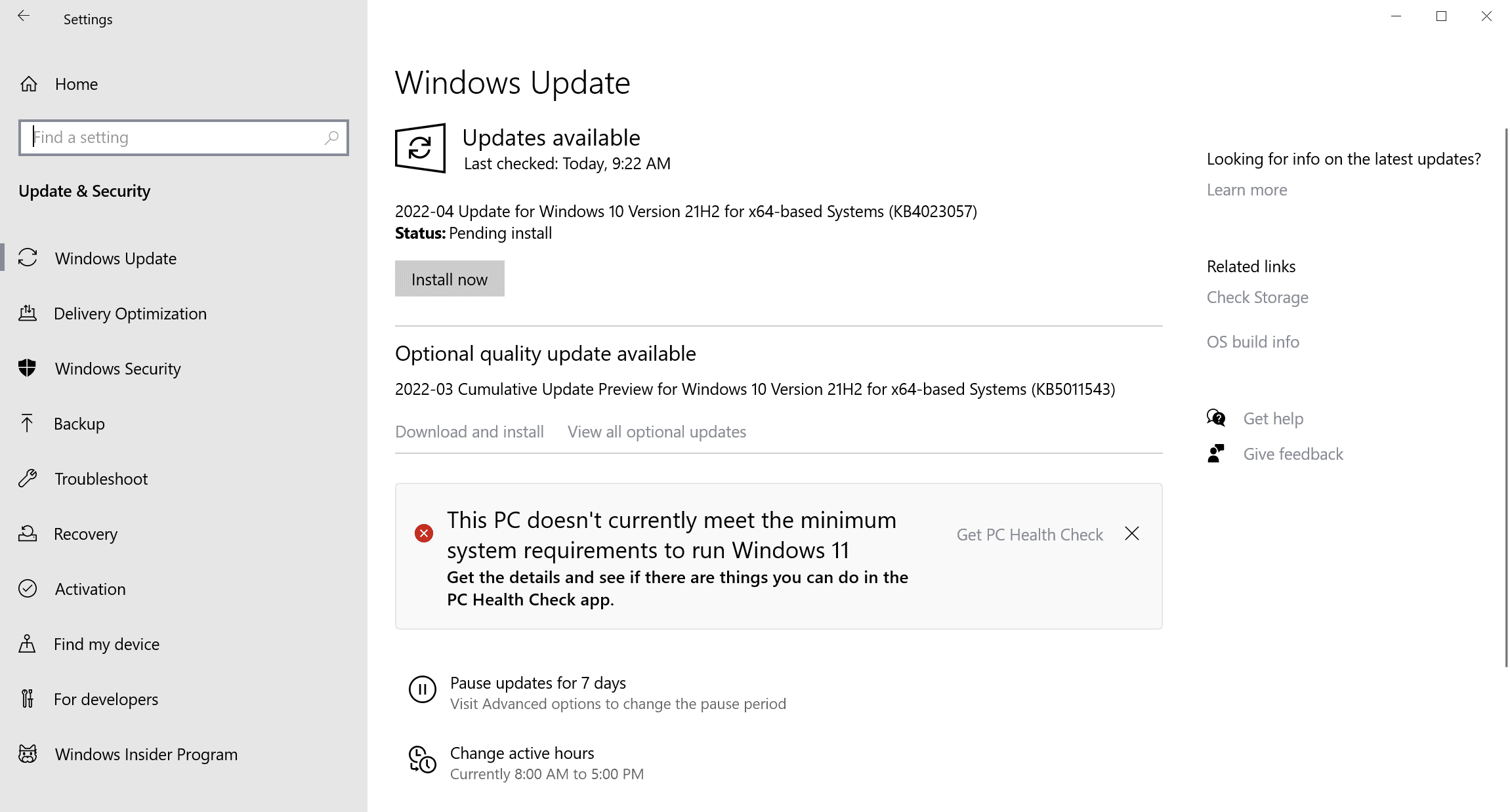
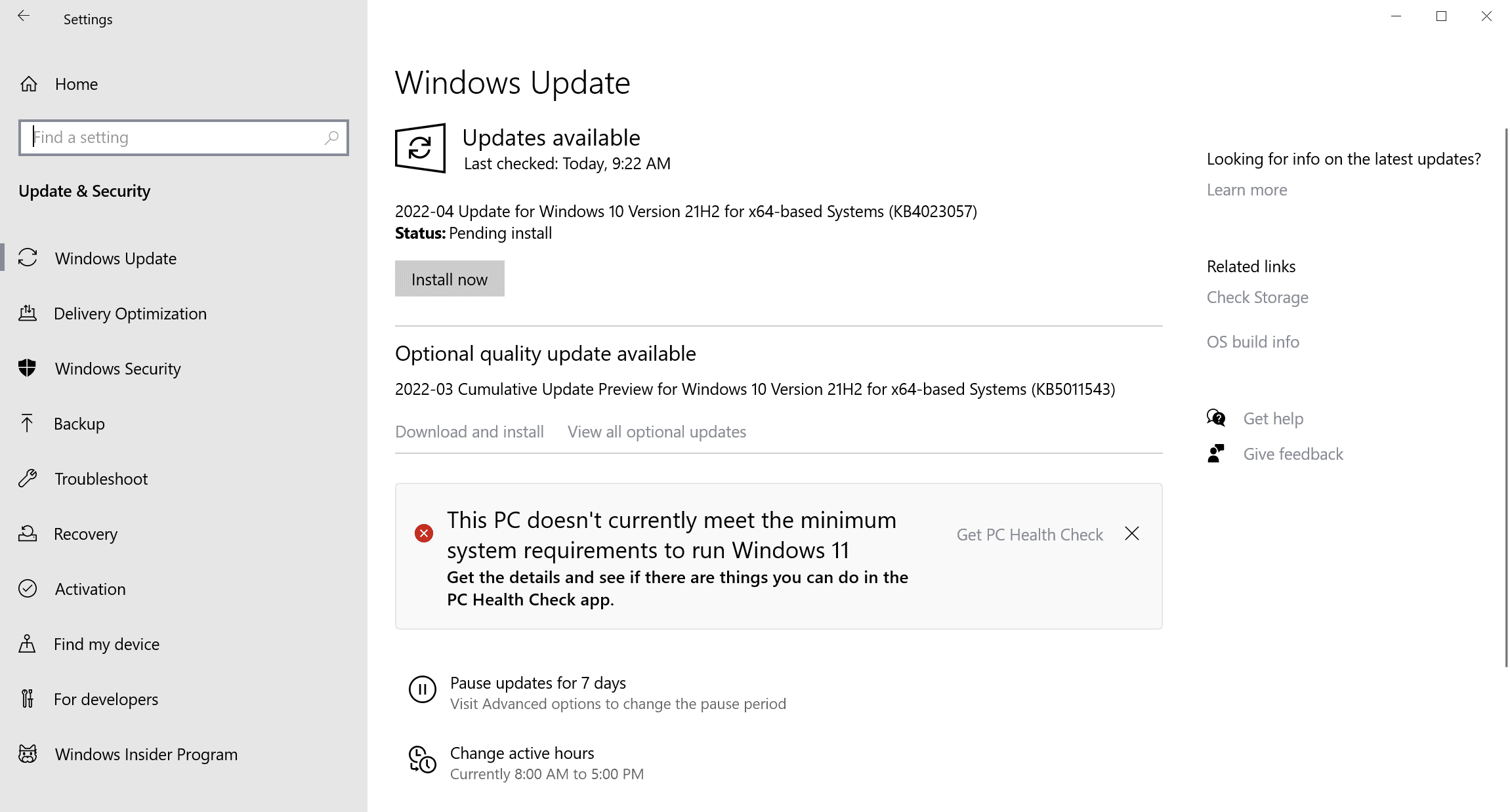
How to download and install the April 2022 security updates
Critical updates are downloaded and installed automatically on most Home Windows devices. On other systems, administrators may need to download and install updates manually, or allow updates to be installed after reviewing them carefully.
Home users may use the following method to check for updates manually (and speed up the installation of updates in the process):
- Select Start, type Windows Update and load the Windows Update item that is displayed.
- Select check for updates to run a manual check for updates.
Direct update downloads
Below are resource pages with direct download links, if you prefer to download the updates to install them manually.
Windows 7 and Server 2008 R2
- KB5012626 -- 2022-04 Security Monthly Quality Rollup for Windows 7
- KB5012649 -- 2022-04 Security Only Quality Update for Windows 7
Windows 8.1 and Windows Server 2012 R2
- KB5012670 -- 2022-04 Security Monthly Quality Rollup for Windows 8.1
- KB5012639 -- 2022-04 Security Only Quality Update for Windows 8.1
Windows 10 (version 20H2)
- KB5012599 -- 2022-04 Cumulative Update for Windows 10 Version 20H2
Windows 10 (version 21H1)
- KB5012599 -- 2022-04 Cumulative Update for Windows 10 Version 21H1
Windows 10 (version 21H2)
- KB5012599 -- 2022-04 Cumulative Update for Windows 10 Version 21H2
- KB5012592 -- 2022-04 Cumulative Update for Windows 11
Additional resources
- April 2022 Security Updates release notes
- List of software updates for Microsoft products
- List of the latest Windows Updates and Services Packs
- Security Updates Guide
- Microsoft Update Catalog site
- Our in-depth Windows update guide
- How to install optional updates on Windows 10
- Windows 11 Update History
- Windows 10 Update History
- Windows 8.1 Update History
- Windows 7 Update History

















Does anyone know why Win10 ver. 22H2 does not get security updates?
Did you forget the servicing stack update?
Latest Windows 7 SSU is still March 2022 but 8.1 was updated this month
Servicing Stack Update for Windows 8.1 (KB5014025)
I failed to apply KB5012599.
https://www.ghacks.net/2022/04/14/browsers-are-crashing-with-error-code-0xc0000022-after-installing-the-april-2022-windows-updates/#comment-4519567
Running 21H1.
My browsers seem to work OK, but my system has crashed twice in the last 2 days.
Please Martin speech about windows enterprise “autopatch” program starting in July 2022. Its not clear about updates on virtual environment
Vivaldi got corrupted after these updates, can’t open it anymore. Or is this an Vivaldi bug?
@Sebas a friend of mine got some troubles with Chrome, uninstall the update should fix the problem, as my friend did.
@John G Thank you.
Why do people complain about Windows 11, when Windows 10 has full support and security patches for a couple more years?
Early adopters, enjoy the fruits of impatience!
Look at all those sweet, sweet, “Remote Code Execution Vulnerability” fixes.
Good old M$, fixin’ the backdoors when they’re found by others. Oh! I mean bugs, silly me. :D
> “Remote Code Execution Vulnerability” fixes.
Fixin’ the backdoors when they’re found by others. Oh! I mean bugs, silly me. :D
Ancient and modern saying: “There is no end to evil in the world”.
Even when “noble and well-intentioned” are put forth to the world, there are always those who harbor malicious intent to plot “unexpected outrages.”
There is no end to lies, and crime is no different.
There is no end to the struggle between good intentions and bad intentions.
Through scientific insight and technological innovation, evolution and elimination are inevitable in digital technology, and no program can be perfect.
Pouring one’s heart and soul into “perfect” will not produce anything worth the cost (human investment and time). In short, it is a waste of time.
The lesson (conclusion) learned from history is that the best countermeasure is to “quickly fixed bugs as they are discovered”.
End users should “apply security patches as they are released” without delay.
I switched to Linux because of now Windows 11 Pro users require to sign in or sign up during internet setup
It’s only Windows 11 Home that requires internet to sign-up. Win 11 Pro can still be setup with offline account.
https://www.ghacks.net/2022/02/18/windows-11-pro-edition-will-require-microsoft-account-for-future-installs/?amp
Lmao, the start search window now respects the OS light/dark mode on LTSC 21h2. It used to be light, regardless of your choice: https://i.imgur.com/QaPn79g.png
I honestly find the fact that someone at Microsoft is concerned about the looks of their OS, despite how inconsistent the whole thing is, rather hilarious.
The search window will only be on dark mode if you have internet access, since the code that checks for it isn’t local, that’s the real “lmao”.
After applied this update it seems that W11 is again slow if AMD CPU is present, no matter what kind of CPU, as it is also confirmed with at least four friends of mine. Thanks for the article! :]
Hmm, no slowness so far on my Legion 7 Pro with AMD 5800H after applying the updates.
What type of slowness are you getting?
What spec and CPU do you have?
@Jimmy there is a noticeable lag when open file explorer, almost two seconds when opening folders. Here Athlon 3.2Gh, however at least three friends also have it on their AMD, and other one friend that has solved the issue restoring the system, he also had some Chrome crashes after applied the cumulative update. I will restore to previous update when I arrived home, because I use now an old notebook with Ubuntu just to solve several printing issues with the college printer and W11 home.
I have no idea. Today I have purged the only W11 installation which I had, on my tablet, and installed LTSC on it as well (: