Windows Defender: Vulnerable Driver Blocklist protects against malicious or exploitable drivers
Vulnerable Driver Blocklist is a new security feature of Windows Defender on Windows 10, Windows 11 and Windows Server 2016 or newer devices that protects against malicious or exploitable drivers.
Announced by Microsoft's Vice President of Enterprise and OS Security, David Weston, on Twitter, the Microsoft Vulnerable Driver Blocklist is a new security feature that is enabled by default on Windows 10 in S mode devices and on devices that have the Core Isolation feature Memory Integrity, which Microsoft may also refer to as Hypervisor-protected code integrity (HVCI), enabled.
Memory integrity, or HVCI, makes use of Microsoft's Hyper-V technology to protect Windows kernel-mode processes against malicious code injections. The feature was not enabled on existing devices when it first shipped, but it appears to be enabled by default on devices with new installations of Windows.
Some users reported issues with certain devices with HVCI enabled, and that disabling it resolved the issues that they experienced.
The core idea behind the new protective feature is to maintain a list of drivers that will be blocked by Windows Defender because the drivers have at least one of the following attributes:
- Known security vulnerabilities that can be exploited by attackers to elevate privileges in the Windows kernel
- Malicious behaviors (malware) or certificates used to sign malware
- Behaviors that are not malicious but circumvent the Windows Security Model and can be exploited by attackers to elevate privileges in the Windows kernel
Microsoft cooperates with hardware vendors and OEMs to maintain the blocklist. Suspected drivers may be submitted to Microsoft for analysis and manufacturers may request that changes are made to drivers that are on the vulnerable blocklist, e.g., after patching an issue.
Devices that run Windows 10 in S mode and devices with HVCI enabled protect against these security threats once the feature is rolled out to devices.
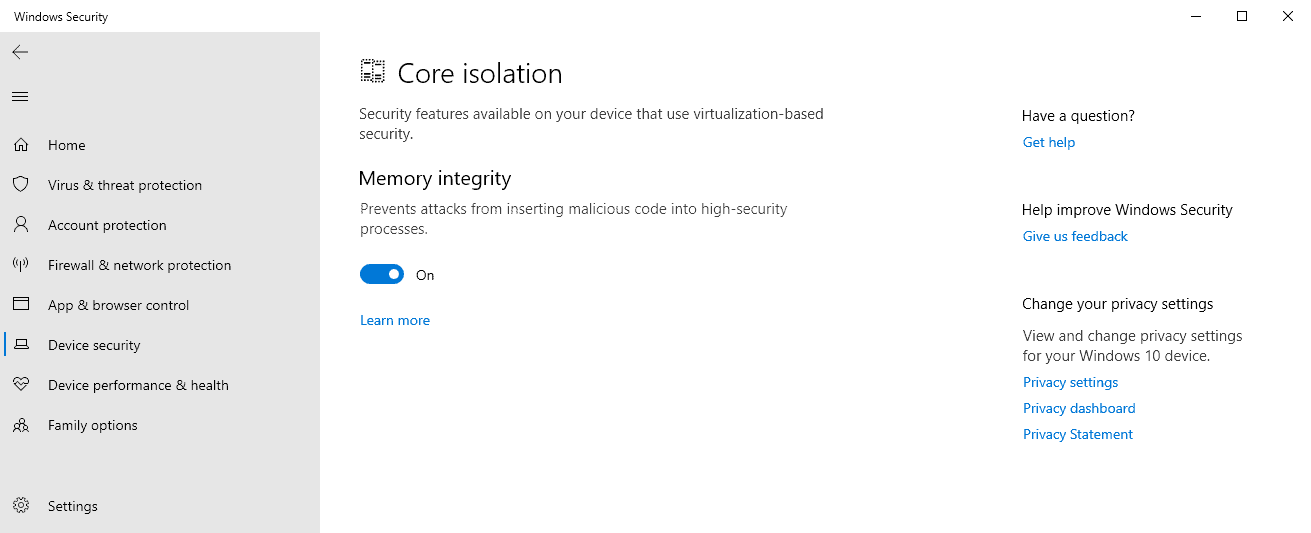
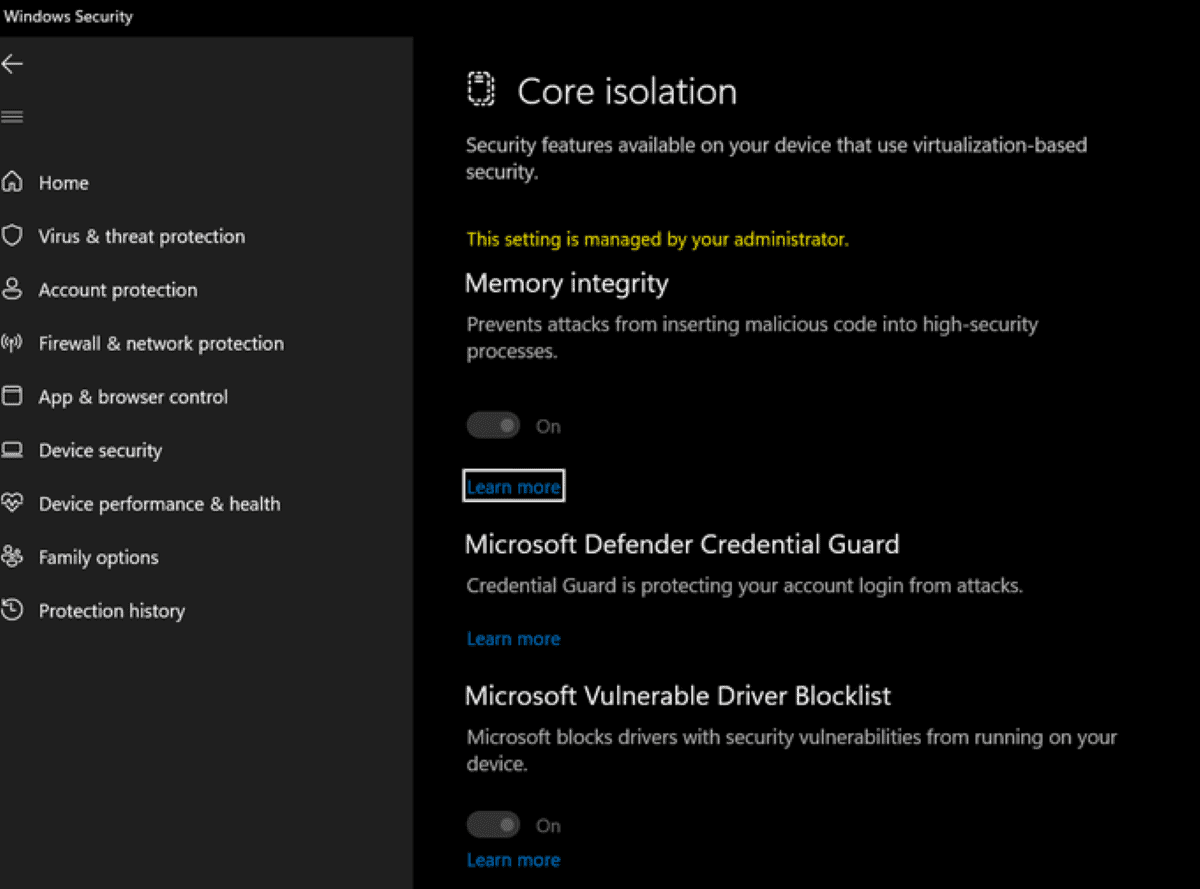
Windows users and administrators may enable the Memory Integrity prerequisite in the following way on non-Windows 10 S-mode devices:
- Select Start and then Settings, or use the keyboard shortcut Windows-I to open the Settings application.
- On Windows 10, go to Update & Security > Windows Security. Select Open Windows Security.
- On Windows 11, go to Privacy & Security > Windows Security > Select Open Windows Security.
- Select Device Security from the sidebar on the left side.
- Activate the "core isolation details" link.
- Toggle the Memory Integrity setting to On to enable the feature.
- Restart the device.
Windows administrators will see the new Microsoft Vulnerable Driver Blocklist on the Core isolation page of Windows Security once the feature becomes available. The feature can be toggled on or off, and also managed through other means. David Weston notes that turning it on will enable a more aggressive blocklist.
Microsoft states that it recommends enabling HVCI or using S mode, but that administrators may also block the drivers on the list using an existing Windows Defender Application Control policy. The documentation lists an XML file that contains the blocked drivers ready for use.
Now You: is memory integrity enabled on your devices, if you use Windows Defender?


















Who cares its Microsoft……Talking …Windows 11…A joke……
Money Baby…………$
New Windows security feature blocks vulnerable drivers
By Sergiu Gatlan
March 28, 2022 02:02
https://www.bleepingcomputer.com/news/microsoft/new-windows-security-feature-blocks-vulnerable-drivers/
Quoting the notes:
This feature will also cause legitimate programs not to work, such as Cheat Engine and Process Hacker, as their drivers are blocked.
“Blocking kernel drivers without sufficient testing can result in devices or software to malfunction, and in rare cases, blue screen,” Microsoft also warns.
“It’s recommended to first validate this policy in audit mode and review the audit block events.”
This is great for Enterprise customers sometime in the 1st half of 2022, but I hope Home users will not be ignored.
I too cannot enable this due to the same Western Digital driver problem for MyPassport backup and Win10Pcap. Both are incompatible on my Windows 10 Pro Dell computer.
Good intentions, but I’m still blown away by Microsofts scummy and childish behavior towards Process Hacker/dual use drivers.
I cannot enable this function because of a 8-6-2019 version of BrUsbSib.sys, a Brother printer driver. Nothing newer seems to be available from Microsoft or Brother. I am considering deleting the driver because I assume it’s used for USB connectivity, but I set the printer up for wireless operation.
You are correct, it’s for USB serial connection, and the device works fine without it.
No thank you! Defender will end up being the wall garden instead of the MS Store. Soon Microsoft will have 100% control of your device and you will need permission to do something simple as installing a font.
I think that MS development team will destroy MS Defender as they did with the W11 taskbar. :[
My PC says …
“Standard hardware security not supported.”
In other words … MS wants you to buy a newer platform …
In other words Microsoft blocking legit drivers of older hardware. Want to use your printer from 2020? Blocked now. You will need to purchase a new printer every 2 years.
While I agree Microsoft want people to buy new computers to run Windows 11 (by requiring 8th generation chips and higher), this in not what’s happening in your case.
One of my machines is a 5th generation Broadwell machine and says “Your device meets the requirements for enhanced hardware security” and has done for years. On that machine, the following are all enabled in the device firmware:
1) Intel Platform Trust Technology (PTT) firmware-based TPM 2.0
2) Secure Boot
3) Virtualization
Then, Memory Integrity (HVCI) is enabled in Windows Security settings. However, it may not be possible to enable Memory Integrity due to crappy drivers – like Western Digital installs when you plug an external USB drive in:
https://community.wd.com/t/unable-to-enable-core-isolation-memory-integrity-due-to-western-digital-driver-windows-10-2004/252131
That said, even though the device meets the requirements for enhanced hardware security – and it’s running the latest Windows 10 21H2 (19044.1620) – I am not yet seeing “Microsoft Defender Credential Guard” or “Microsoft Vulnerable Driver Block List” in the Windows Security settings, as per the screenshot in the tweet.