Android game developer says some ads were able to bypass Google Play to install third-party apps
Remember the HT Coin Android malware issue that we reported about a couple of weeks ago? The HelloTalk app displayed notifications, which when tapped, downloaded a malicious APK and installed in on the user's phone.
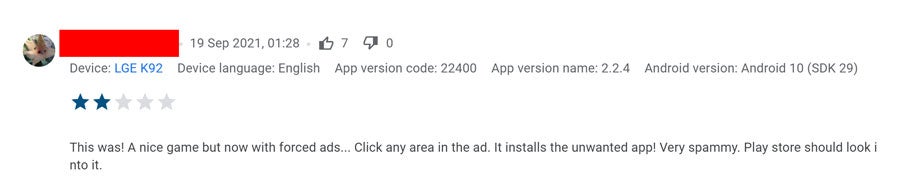
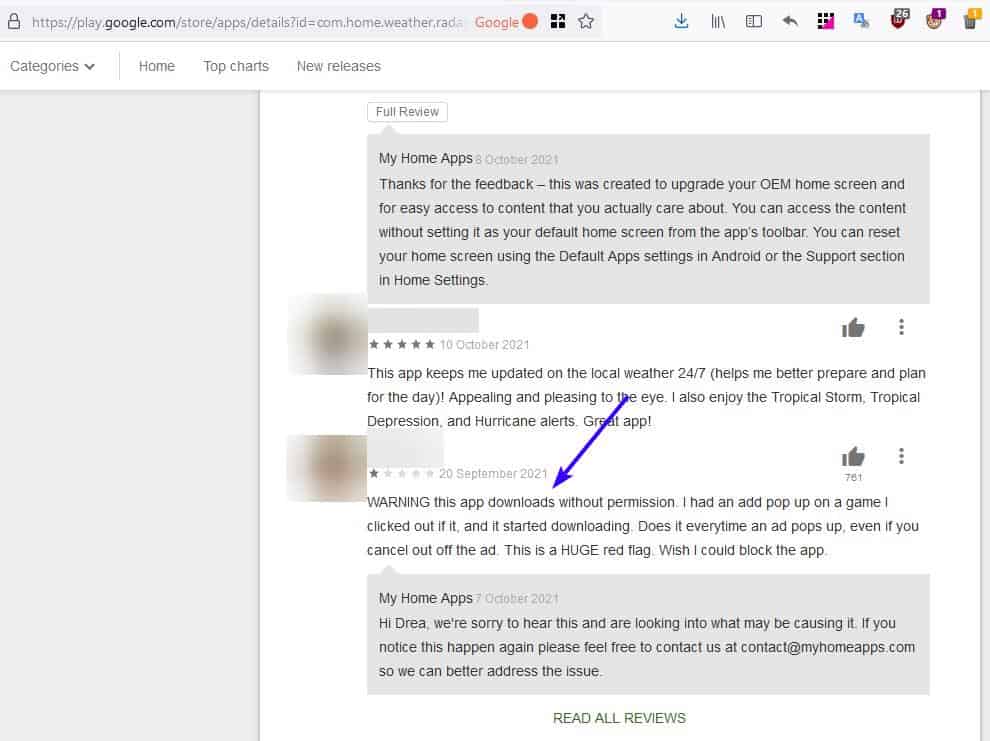
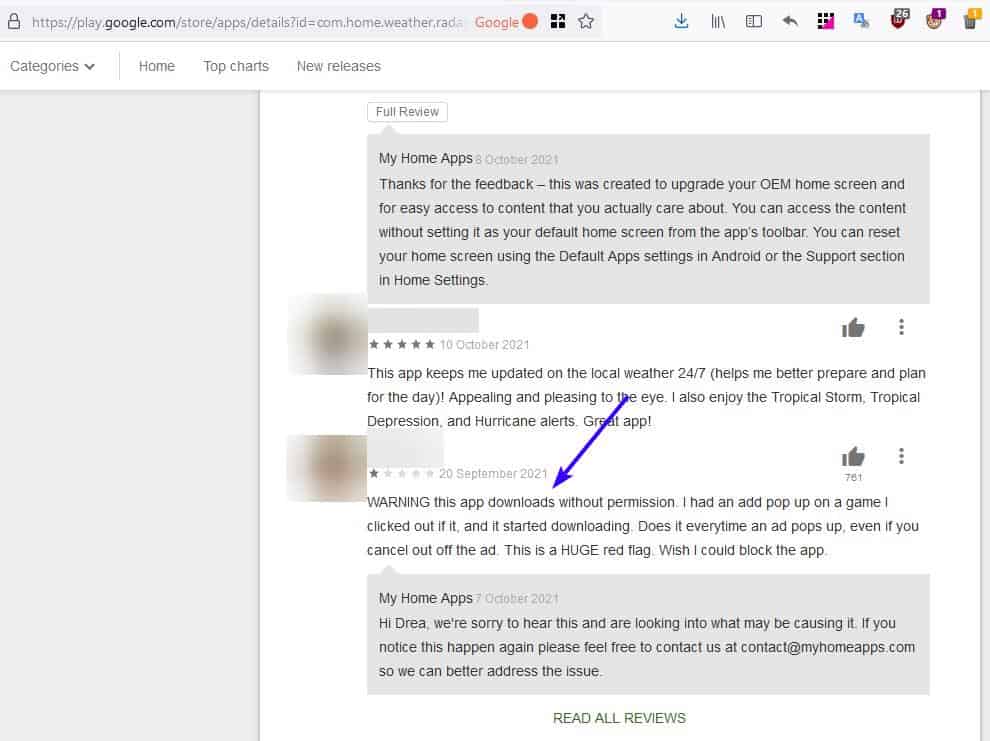
A few days ago, a game developer (Rifter Games) shared their troubles on reddit's r/androiddev. According to them, some of their users recently started leaving negative reviews for their game. Other users had upvoted the reviews, which in turn grabbed the developer's attention. The users alleged that the game displayed some ads, which when interacted with, resulted in a third-party app being downloaded, and installed without the user's consent.
What was alarming here is the manner in which the app in question was downloaded. You see, the ad didn't open the Google Play Store, or prompt the user to click the install button. Instead, the malware was downloaded directly when the user touched the ad, i.e., it bypassed Google Play completely. That is eerily similar to the other problem that we saw, isn't it?
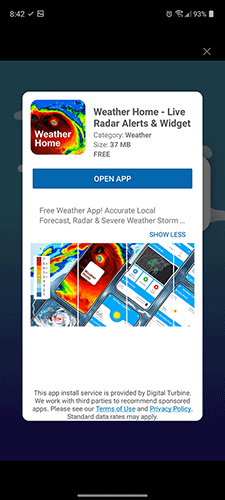
The game developer contacted the users, and as them to provide additional information, and managed to get some screenshots related to the issue. The images show what appears to be an interstitial ad, aka a full-screen ad, that promotes an app called Weather Home -Live Radar Alerts & Widget. It has an X button at the top, but did those users tap it to close the ad? The second image clearly indicates that the app is being downloaded.
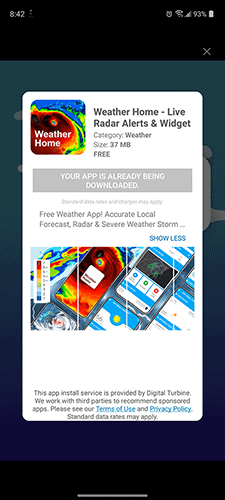
The game developer says they reached out to their ad providers, seeking an answer to their issue. They were informed that the technology behind the app install, i.e. the one that bypasses the Google Play Store, belongs to a company called Digital Turbine. If you observe the screenshots of the ads closely, you'll notice the wording at the bottom reads, "This app install service is provided by Digital Turbine." What is DT? It is a digital advertising company that provides DSP (demand-side platform), and recently acquired an app monetization company called Fyber.
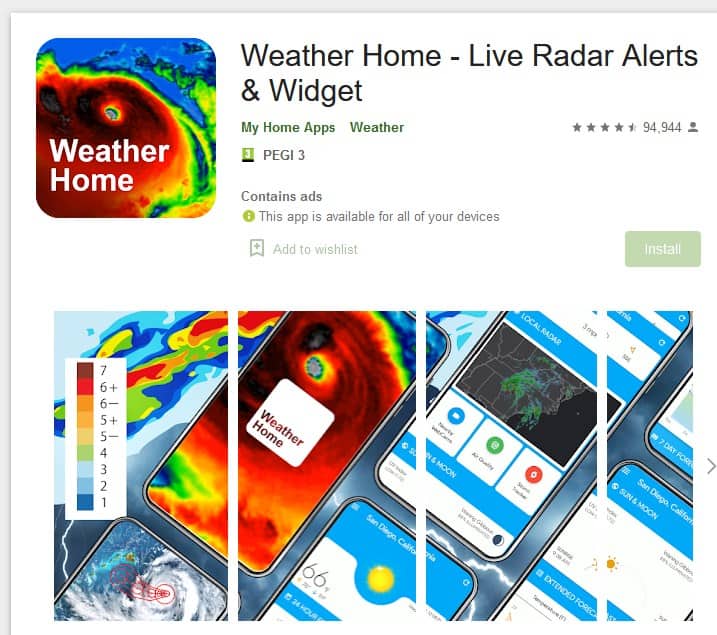
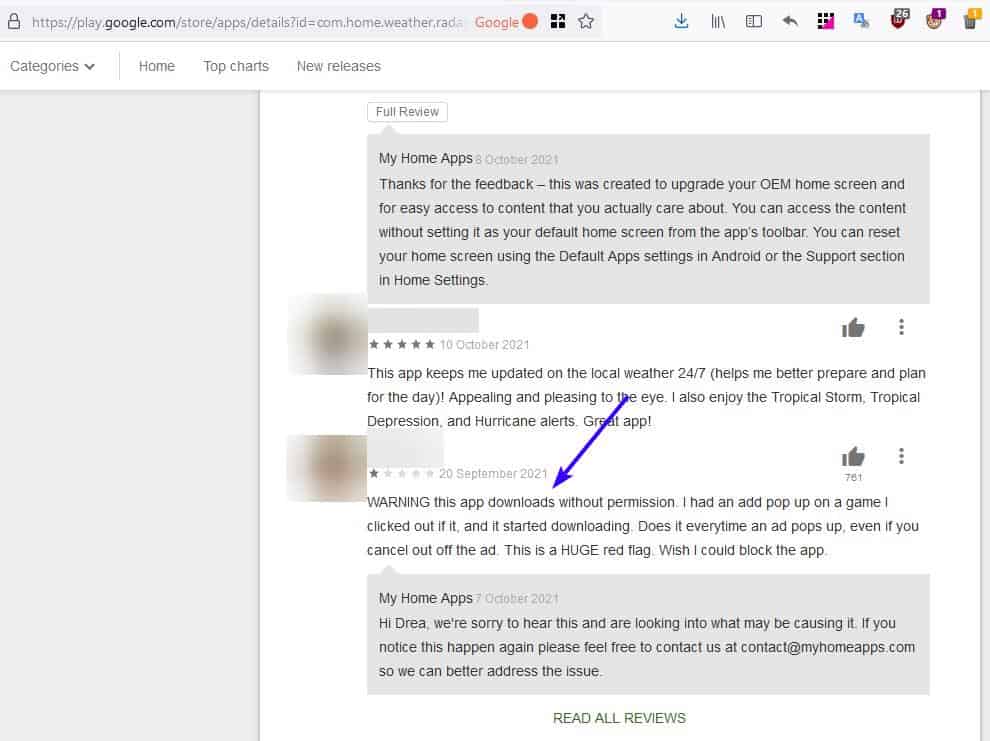
Shouldn't Google Play Protect prevent this app install, or at least flag the app in question? This is where it gets interesting. The weather app that was downloaded, is available on the Google Play Store, which is probably why it didn't get flagged. Some of the app's recent reviews say that the user did not choose to install the app, and that it was installed automatically. Whether the app is safe or malicious remains a mystery, but the bigger issue is the way it got installed.
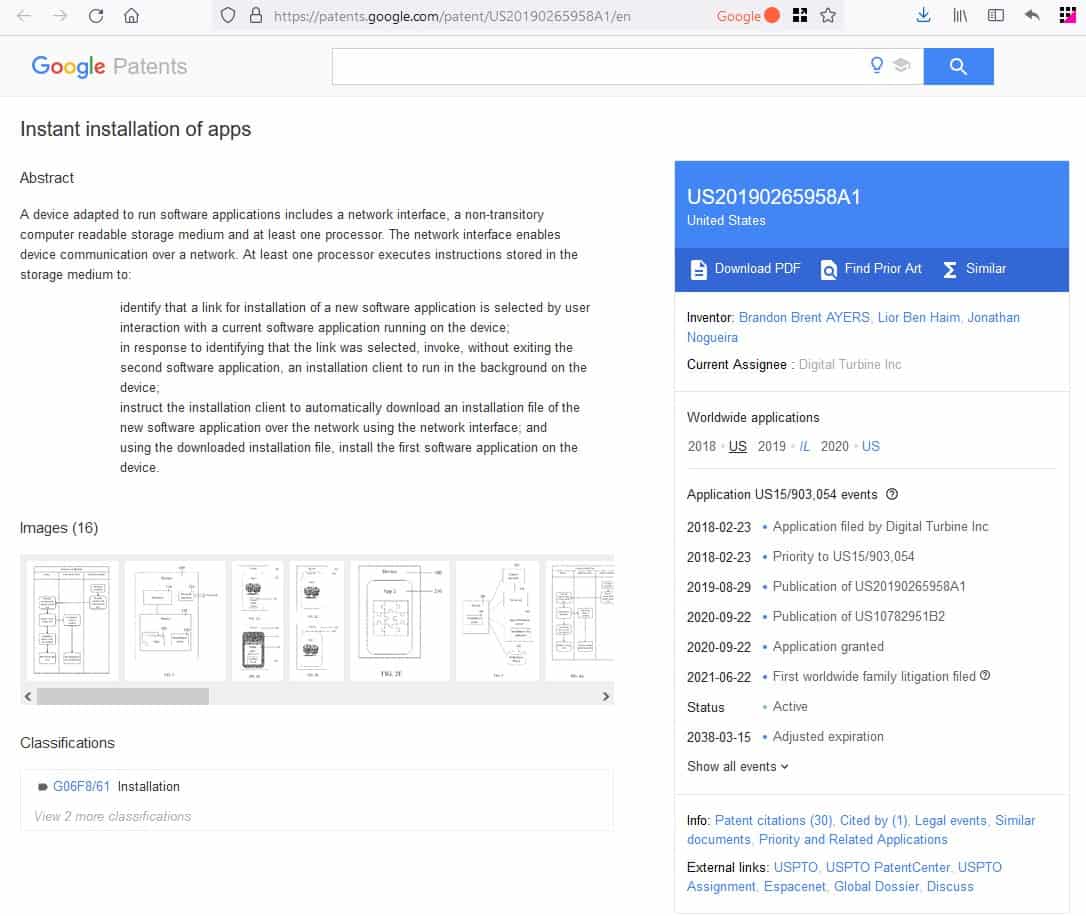
Believe it or not, this company has patented the technology to serve app downloads by bypassing Google Play. (Reference: 1, 2)
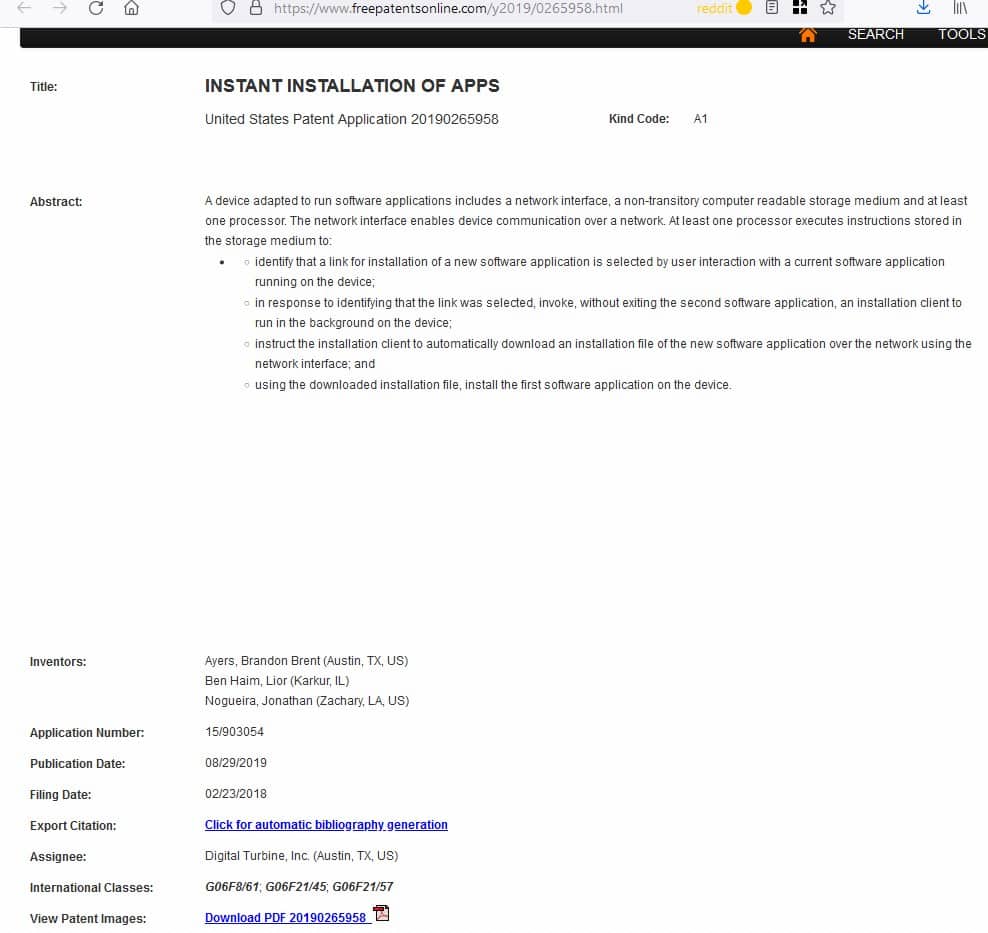
Here's an extract from the patent's page.
Embodiments described herein utilize an installation client on a device in order to install apps on a device without redirecting the device to an app store. The content provided to the device includes links (denoted here “instant install links”) which indicate that the associated app should be installed by the installation client and not via an app store. When an instant install link is selected, the installation client is invoked to run in the background. The installation client downloads the installation file for the app associated with the instant install link to the device. The new app may then be installed on the device using the installation file.
A comment on that reddit thread by u/omniuni explains more about this. Many phones, especially carrier-locked variants, ship with an app called DT Ignite (reference: Android Central). This is a system level app, that carriers can use to push bloatware apps to your device. That's how the ad managed to install the app on the users' phones, because DT's app allows it.
The user says Digital Turbine replied in context to the post. The company is apparently looking into the issue to figure out how the app download started when users tapped the X button. So, it appears that users did tap the X button after all, but the ad initiated the app download anyway. The user says that Digital Turbine's representative assured them that all app packages were verified before and after they are installed, and are registered with Google Play. The download is delivered via a secure connection.
A security issue related to this has been filed on Google's Issue Tracker portal. This case may not have been malicious, but it is definitely creepy and poses a serious privacy and security issue for users. What if a malware somehow slips through this method?
Malware and mobile ads aren't a new combination. If you use a mobile browser without an ad-blocker, you may come across different kinds of ads. Some of these may claim your phone is infected with a virus, and gives you an option to install a free antivirus. These are nothing but scareware tactics to fool the user into that their device is at risk, and when they tap on the ad, it turns out to be the malware.
You can protect yourself from trackers and ads by using a system-wide ad blocker like Adaway (has a non-root option) or Blockada or DNS66, or a DNS solution like (AdGuard, NextDNS). If that's not a viable option, I recommend using a browser like Firefox with uBlock Origin to help prevent ads, though it won't disable ads in other apps.
What do you think about silent app installs via ads?






















DNS66 is a great app for blocking ads on android mobile as well as android TV. Its available on play store.
Lessons to draw from this:
– Don’t buy carrier-locked phones ;)
– Support LineageOS and its derivatives, they are the Linuxes of the mobile world
I have a Pixel 3Xl and while using the Chrome browser on the phone maybe a year ago, something managed to get in. I couldn’t stop it via the X control and of course, it kept popping up new scare warnings.
If I remember correctly, I had to go to the apps screen and force close Chrome. Then I deleted it and switched FF when I need to browse, which I don’t do on the phone very often.
I’ve also been using Blockada for maybe a year. Works great to remove most of the annoying ads, pop-up’s, pop-overs and so forth.
I don’t understand why Google doesn’t force some standardization on advertisers, such as don’t allow them to move the control elements around on the screen (sometimes the close X is on the upper left, upper right, lower right, etc.).
Then probably half the time you have to push the X multiple times to get it to respond.
Same thing when a Youtube video pops up and starts playing. I often have to mash the pause button 3-5 times to get the video to stop playing. This is done on purpose, yes? Sheese.
Mom’s phone suddenly has apps that she say she didn’t install suddenly appearing…I thought she might have install them accidentally at first…then this appears.
Ugh, that sucks.
This is equivalent to Windows Update installs update without user concerns with no way to prevent it.
Cheap phones usually have malware system app like this, as far as I know Xiaomi phones have this shit malware. It shows ads all the time without way to unsubscribe.
It’s such a tragic situation that whenever someone finds a workaround from corporate tyranny, instead of keeping it for dark days, they instead abuse it for ads to get money. It’s so damn tragic.
In the end “you can’t beat the system” corrupt as it is.
https://www.bleepingcomputer.com/news/security/study-reveals-android-phones-constantly-snoop-on-their-users/
One of the best decisions ever was to dump Android.
According to a certain stupid madainsecurities Android is the best, better than desktop.
@Yash
You can end your crusade against madaidan now. I think you are referring to this bit:
“A common argument for rooting is that Linux allows root, but this does not account for the fact that the average desktop Linux system does not have a security model like Android does. On the usual Linux system, gaining root is extremely easy. This is why Linux hardening procedures often involve restricting access to the root account.”
source: https://madaidans-insecurities.github.io/android.html#rooting
This is about gaining root privilege, which is provably easier on Linux than it is on Android. The article @ddk linked to is about data collection by Google, the phone manufacturer or third parties. What does that have to do with root access? That’s right, NOTHING.
@Yash, you don’t know what you are talking about, mixing up unrelated topics, you are even confusing security with privacy. Ouch.
Just because a Whonix developer does not share most of your suggestions or choices does not mean that you have to develop a vendetta in response.
I wasn’t referring to article shared by @ddk, but the words – ‘One of the best decisions ever was to dump Android’ in sarcastic way. The article from where this sarcasm is drawn is not from the article you highlighted, but from – Security and Privacy Advice – https://madaidans-insecurities.github.io/security-privacy-advice.html
Quotes – ‘The desktop security model is very broken. It was not designed with security in mind — security was only a poorly implemented afterthought. However, there are some operating systems that are less bad in this regard. If you can, stay away from desktop and stick to mobile devices.’
About the other stuff you wrote, it can be best summarised in one word which you mentioned at the beginning – Crusade, Fourth to be exact. Unnecessary words when end goal is same – privacy. But, yeah, I guess a certain security researcher’s words which are totally false are more important than having a critical thinking.
@Yash
Yes, and? Android and iOS are much more locked down than desktop operating systems, it’s a FACT. You are never refuting any arguments of madaidan whatsoever, instead preferring ad hominem smear campaigns. That will convince many, I am sure.
Prison is also locked down if that is the way to do things. Android and iOS are the worst offenders in privacy and security. But okay if you say they’re better because of madainwhatever, well good for you.
> Many phones, especially carrier-locked variants, ship with an app called DT Ignite (reference: Android Central). This is a system level app, that carriers can use to push bloatware apps to your device.
A familiar had a phone (some rebrand from a generic chinese product sold in Argentina) that came with an app called Asrock something. One day the app decided to install Adware, and every 3 or 4 touches to the screen a new browser window appeared loading a page with health related products (drugs, candys, some diet).
The solution i found was to factory reset the phone and without connecting it to the network, uninstall the app using adb. Otherwise, at the very moment you connect it to the network, the Adware app is installed.
I recently started using the new “AdBlock Browser” from eyeo gmbh, the people that make the AdBlock Plus extension for PC browsers.
For the first time I am actually able to use a browser on a mobile device.
Honestly, just use Firefox or Kiwi with uBlock Origin. They’re much better.
@Dave
> eyeo gmbh
That company again. I suggest you do some research regarding how they finance their operation, namely how their whitelist came to pass.
> For the first time I am actually able to use a browser on a mobile device.
Bromite, Brave, Firefox + uBlock Origin
Thank me later.
@ironheart
You’re right about Bromite, I’d also advocate Netguard for Android
Speaking of Android, Google will soon add a very useful function to Chrome for Android: “Page Zoom”, this feature allows you to set a custom zoom for each page, it is basically the same function available in the desktop version of Chrome:
https://i.redd.it/gkc4b37xgts71.gif
https://redd.it/q5d9je
.
‘What do you think about silent app installs via ads?’
Rest assured, this is all done to protect users from malware and to provide world class security – Pathetic excuse again from Google team.
Not surprised, afterall that’s what Google does. Of course they will implement new policy in future to *try* to stop this.
Play Store has been a joke for too long now. Most apps are fake, but okay its all done for *security*. Nothing is done to milk every quid from privacy of users.
I got off Android a long time ago after 2 phones were instantly locked, frozen and taken over by preinstalled malware right off the bat, I mean from the very first use. Happened with Samsung Galaxy and an LG model. Purchased directly from the manufacurer. Had to completely wipe and reinstall. NEVER again.
Really peeps, look for alternatives, something like this put out by a mega corp ad agency isn’t ever going to be secure.
@ddk
Get a Pixel and install GrapheneOS. GrapheneOS only comes with Android system applications and respects your privacy.