Another Chrome emergency update to patch 0-day vulnerabilities is now available
Google released another security update for the company's Google Chrome web browser that brings the version of the browser to 94.0.4606.71. Google Chrome 94.0.4606.71 is a security update that fixes two vulnerabilities that are actively exploited in the wild according to Google. The update is the third update that Google released this month to address 0-day security issues in Google Chrome that are exploited in the wild.
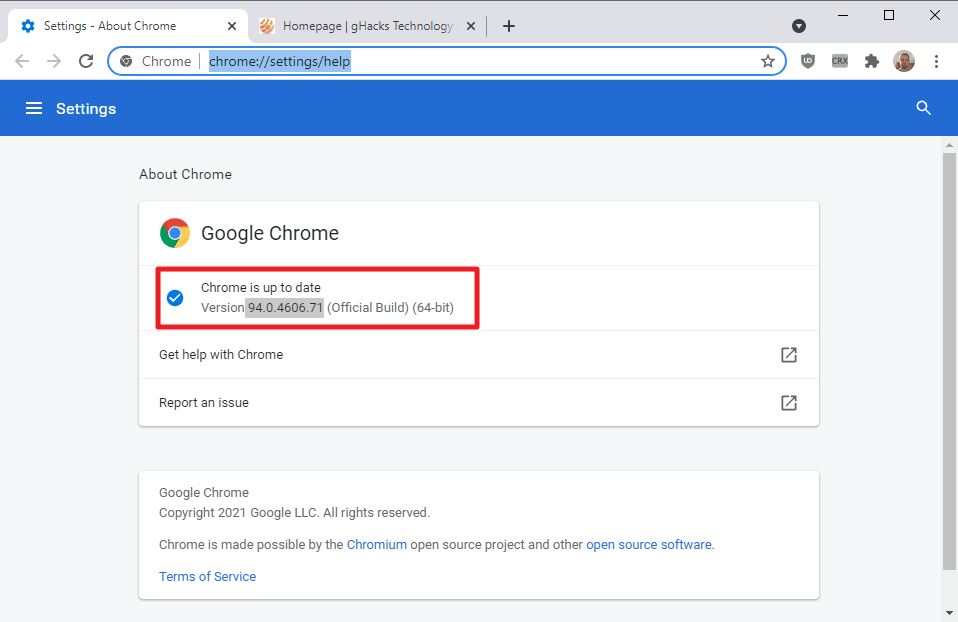
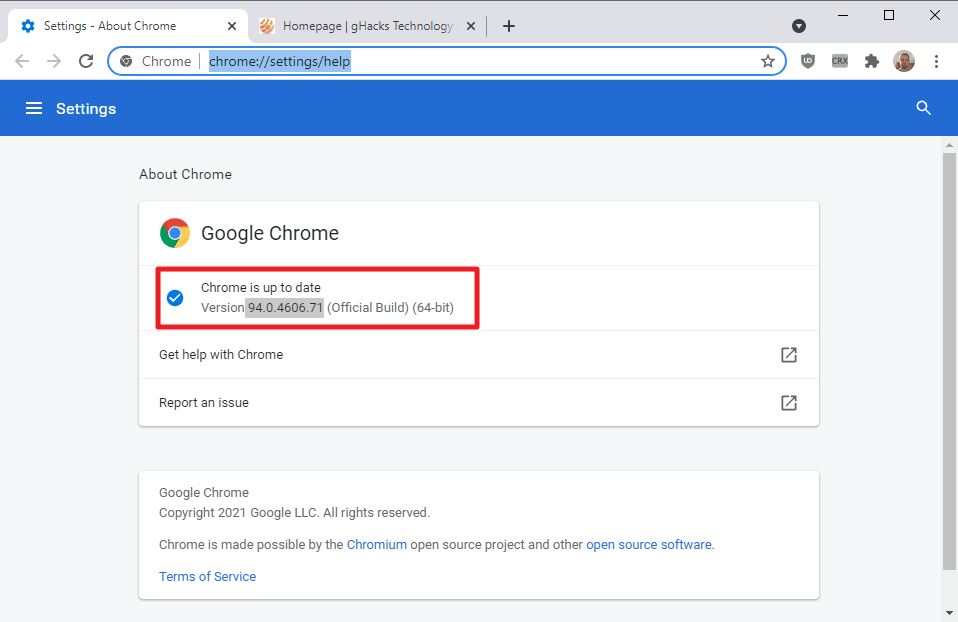
Google is rolling out the update to all Chrome installations, but users may want to speed up the discovery and installation of the update by loading chrome://settings/help in the browser's address bar, or selecting Menu > Help > About Google Chrome from the menu.
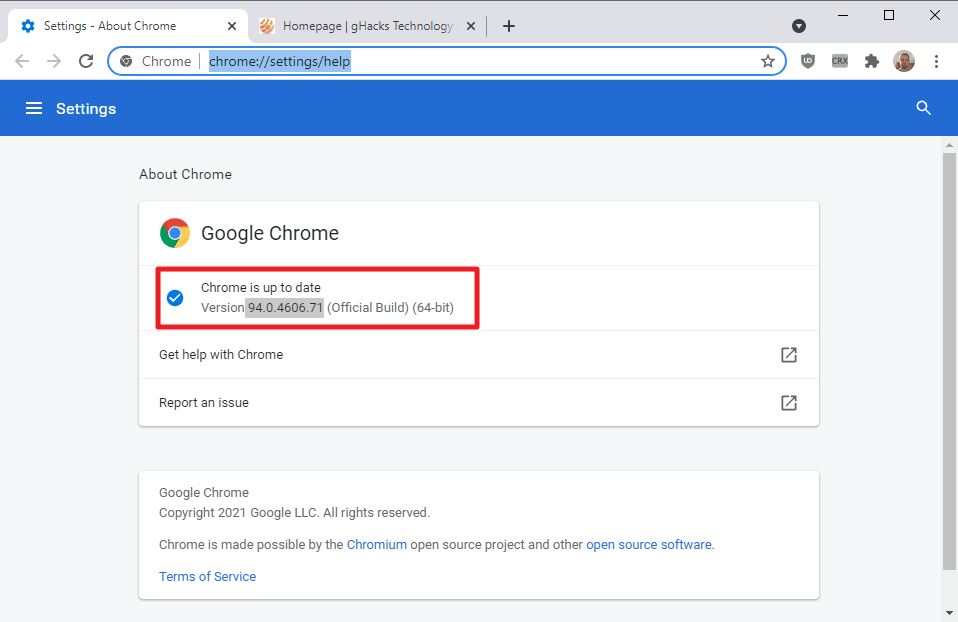
Chrome displays the installed version on the page that is loaded and will run a check for updates. Updates that are discovered during the check are downloaded and installed automatically. The new Extended Stable channel has been updated as well.
Google published information about the update on the Chrome Releases blog:
- [$20000][1245578] High CVE-2021-37974 : Use after free in Safe Browsing. Reported by Weipeng Jiang (@Krace) from Codesafe Team of Legendsec at Qi'anxin Group on 2021-09-01
- [$TBD][1252918] High CVE-2021-37975 : Use after free in V8. Reported by Anonymous on 2021-09-24
- [$NA][1251787] Medium CVE-2021-37976 : Information leak in core. Reported by Clément Lecigne from Google TAG, with technical assistance from Sergei Glazunov and Mark Brand from Google Project Zero on 2021-09-21
Google notes on the page that it is aware of exploits targeting the vulnerabilities CVE-2021-37975 and CVE-2021-37976.
Google is aware the exploits for CVE-2021-37975 and CVE-2021-37976 exist in the wild.
Both security issues are rated as high, the second highest severity rating after critical. Google did not provide additional information on the issues, e.g. how they are exploited or how widespread the attacks are.
Google released another emergency security update for Chrome last week, patching another 0-day vulnerability that was actively exploited at the time according to the company. Two additional 0-day security issues were fixed on September 13, both of which were also exploited in the wild.
Chrome users may want to update the browser as soon as possible to secure the system against potential attacks.



















Chrome is a big target, not surprising it’s going to get attention from bad people. What is surprising is how much is catching Google off guard and having to push out emergency patches.
FIREJAIL
https://firejail.wordpress.com/
https://wiki.archlinux.org/title/Firejail
Description: sandbox to restrict the application environment
Firejail is a SUID security sandbox program that reduces the risk of
security breaches by restricting the running environment of untrusted
applications using Linux namespaces and seccomp-bpf. It allows a
process and all its descendants to have their own private view of the
globally shared kernel resources, such as the network stack, process
table, mount table.
Isn’t this what the Chromium sandbox is for? AFAIK, all these exploits mean that an exe can run in the corrupted memory space. So, if Chrome is run in another sandbox, or there is some sort of behavior blocking program, AV, or software restriction policy, the problem should be mitigated, right?
The Firefox sandbox has a more permissive sandbox, judging by process explorer, and so exploits would be worse?
Many thanks for the informative heads-up Martin.
Remember the ‘teabag’ security of macromedia/adobe flash player?
There’s a crown waiting for either Google or Microsoft this year.
Again no details including the window of vulnerability. At this point chromium based browsers are the weakest security leak in any setup whether it be Linux or windows. Worse than IE6 days, just better hope hackers don’t target you individually or as part of a wider organization bc it seems any efforts in regards to browser hardening routinely fail.
I did not know of the new Chrome Extended Stable option as described at
https://support.google.com/chrome/a/answer/9027636?hl=en
As nice as it is to see holes being patched, the neverending flow of the patches is getting real old now.. Why is chrome leaking?? Too many features? Not enough quality control? Too many chefs in the kitchen? It’s a sad state of affairs when mighty google has to BRIBE hackers/devekopers/smartpeople to find the vulnerabilities. Why? If I find 10 holes in chrome, I will not report 10 holes. I will report ONE, and collect my money. Next month I will report the second one etc etc.. Yeah, people are s**t, deal with it. Or better: MAKE A GOOD BROWSER TO START WITH, YOU MIGHTY TURD.
Thank you.
Speaking of Chrome, the “new” menus with the “Windows 11 style” are now available in Chrome Canary:
https://www.reddit.com/r/chrome/comments/pz2pk7/these_are_the_new_chrome_menus_with_the_windows/?utm_source=share&utm_medium=web2x&context=3
.
Wow more exploits,Chrome is having a bad day.
a bad day? more like an unprecedented bad year
https://docs.google.com/spreadsheets/d/1lkNJ0uQwbeC1ZTRrxdtuPLCIl7mlUreoKfSIgajnSyY/edit#gid=2129022708
@karl
Uh, as the software gets more complex year after year, more security issues pop up. That is so surprising, you know.
And you seem to neglect the fact that 80% of the web population use Chromium. Do you know how much scrutiny it really gets compared to other irrelevant browsers? Of course it is the prime target, and therefore, logically, more security issues are revealed. The fact of the matter is, the security standards of the competitor are much worse than those of Chromium, and said competitor is lucky that almost nobody actually uses it, as otherwise it would have even more issues reported of itself revealed than is already the case.
> you seem to neglect the fact that 80% of the web population use Chromium
I didn’t forget anything. Why are you such an apologist? This 80% figure is nothing to be proud of, if anything, it’s a liability
@karl
> if anything, it’s a liability
If anything, it tells you what people actually want to use after they have freely made their choice. Windows is used by 90% of all PC users, Android by 80% of all smartphone users. And yet the world is still spinning, despite the “liability” of having a clear market leader in each case. Same for Chromium. You seem to underestimate how quickly the tech giants behind these products actually respond to security issues, I don’t feel insecure by using Chromium at all.
You should worry more, as a Firefox user (I assume), as your security is merely a pseudo-security via obscurity.
Sure software get complex but it doesn’t discount the fact that current make Chrome stable version seem like Chrome Canary. Plus it also affects every Chromium fork out there as well which in turn increases pressure on them to fix it immediately and then do it again in the same week and again and again.
@Yash
It doesn’t affect forks in a major way. Forks have the most “issues” when they merge in a new major version of Chromium, e.g. the jump from Chromium 93 –> Chromium 94, as the code changes are more extensive in major jumps. Security patches come with minimal code changes and are usually merged in very quickly.
I received a correspondent Brave update mere hours after Google Chrome was updated. Nothing dramatic.
Thank you.