Secure File Deleter is a freeware tool that you can use to shred sensitive data
We store a lot of personal information on our computers; if you don't organize your files, you may be surprised at what you can find on your system. The importance of data will of course vary based on its cotent, e.g. financial statements, medical records, contracts or receipts.
When you no longer need such data, you shouldn't just delete them as you would normally. Many offices have a paper shredder to prevent their data from being misused.
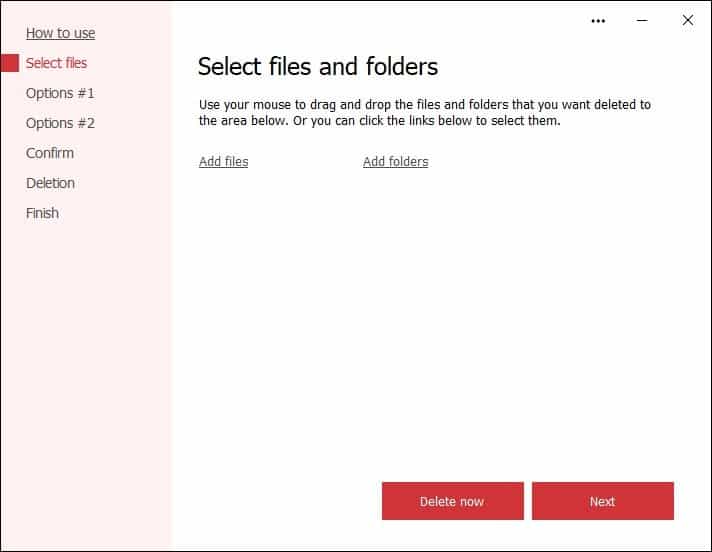
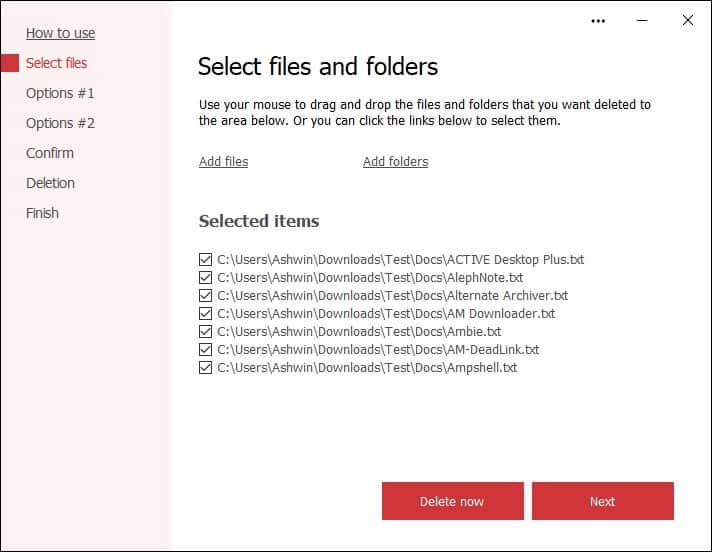
You can have a similar tool at your disposal, a digital one for protecting your documents and files. The program I'm talking about here, is called Secure File Deleter. The tool's interface doesn't have toolbars or a lot of buttons. Let's begin by picking some files to shred.
There are multiple ways to do this, the easiest of which is to drag and drop the files on to the program's interface, or drop them on the desktop icon if you don't have the tool opened. You can also click the add files button in the application's GUI, to browse for the files.
If you want to delete all files in a directory, choose the Add folders option. Do remember that this option will delete subfolders, so pay attention to what you are doing.
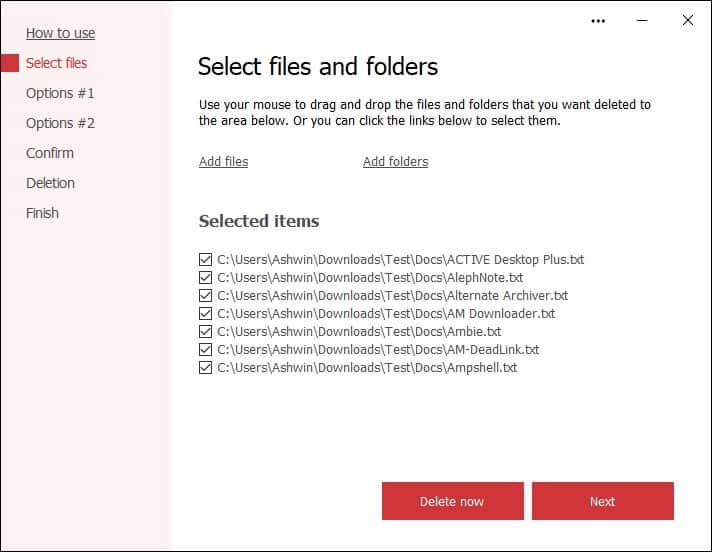
Secure File Deleter places a shortcut in Windows Explorer's shell menu, to use it just select some files, right-click on them and Send To > Secure File Deleter. The secnd menu item opens the program with administrator rights. The application lists the added items on the right pane. If you changed your mind and want to keep some files, you don't have to start over, just uncheck the files before hitting the Next button.

It is time to choose the deletion settings. In order to remove all traces of the file, the program will overwrite it with random data. The value for this option is set at 5, as in 5% of data will be overwritten, the idea is to corrupt the file making it literally unusable. This setting isn't enabled by default. Â The next option, Delete File Usage Data, erases some advanced properties of the files, such as when it was created, modified or accessed. The last setting on the page empties the file before deleting it from the MFT (Master File Table).
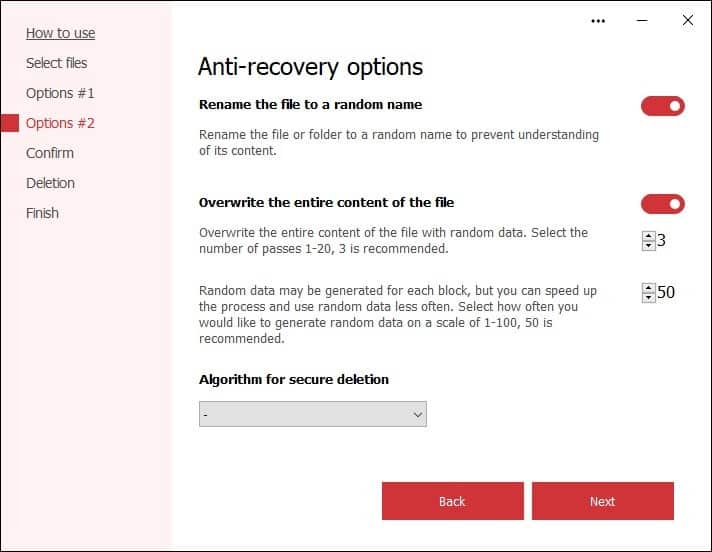
Click the next button, and you will be given more options, these help in preventing recovery of the data. Secure File Deleter renames your files by assigning random names, before erasing the contents. The utility also overwrites the file multiple times, called passes, with random data. This is common in many file deletion programs. Secure File Deleter does three passes by default, and I wouldn't recommend setting a higher value for this as it won't impact the outcome.
The last option on the page is for selecting the algorithm used for shredding the files. Unfortunately, this is locked behind a paywall aka a Premium version, so free users cannot access it. These are standard military algorithms which are used for highly sensitive data, that you don't want to fall in the wrong hands. This maybe a bit overkill, so the other options should be sufficient for most people.
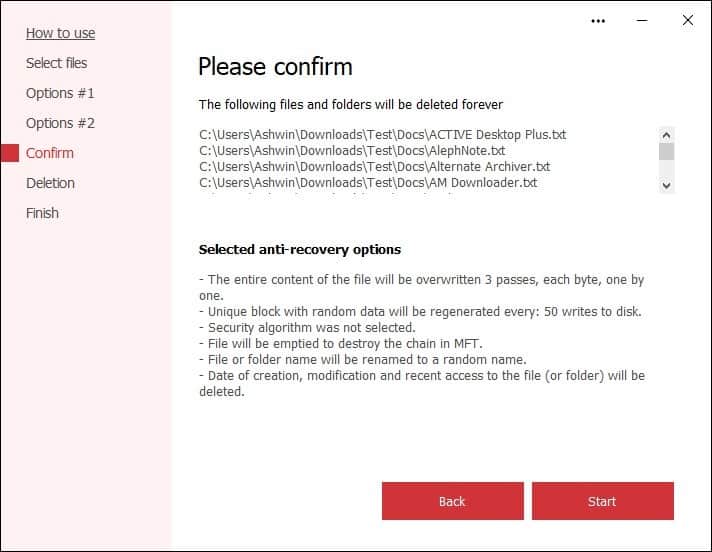
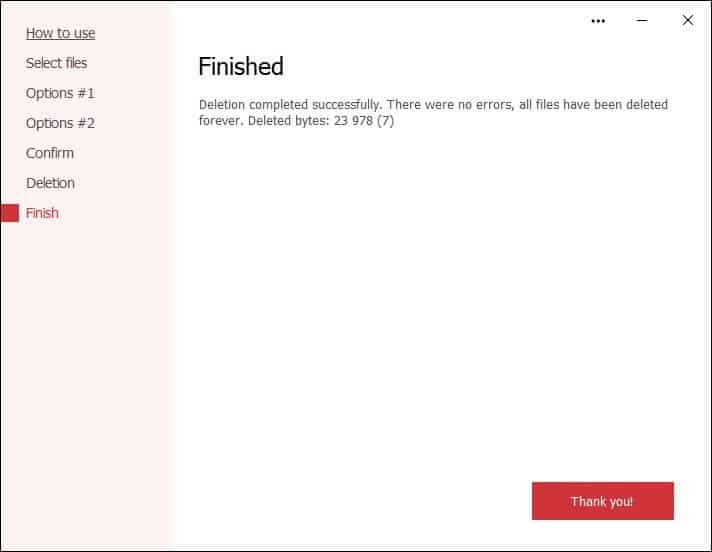
When you click next, Secure File Deleter will display a confirmation page that has a summary of all the settings that you have selected. If you'd like to make some changes, hit the back button. Click the Start button to begin the shredding process, it takes a couple of seconds, and tells you whether the files were deleted successfully.
As with any file deletion tool, I'd advise using Secure File Deleter with care. You don't want to delete something that's important, because you can't recover it.
You may also check out SDelete, a free tool by Microsoft or Perma-Delete, two of the many alternatives to delete files securely.
























What does “empty file to destroy MFT chain” actually mean??
Files smaller than around 1 kB is actually not stored on a separate cluster on the disk drive, but inside the MFT itself and is not something every file eraser is able to remove.
Also, a really great free program that also works with SSD is https://www.oo-software.com/en/safeerase-hard-drive-data-secure-deletion.
When you are much more than really serious about deleting your data spend a few dollars and buy the pro version.
https://www.oo-software.com/en/download/current/oosafeerasepro
@Paul(us) The SSD secure deletion is pure marketing hype and can not be achieved by software.
The Firmware in an SSD drive makes it impossible to guarantee a secure deletion unless the entire drive is wiped using the manufacturer’s drive wipe utility.
Their “SolidErase” technology apparently simply fills the SSD with garbage then deletes it (they give few details, unsurprisingly).
This does NOT guarantee secure file deletion due to the way SSDs work.
I Still Use CyberShredder ;)
I like File Shredder Tool by NoVirusThanks which is 100% free with no ads or nags. It does all that Secure File Deleter does and more. Also, it has a simple/great, idiot proof GUI.
One of the best things about FST is that it randomly renames the filenames before they’re shredded so they can’t be discovered later. Software that just shreds the file will still leave the filename, which can be viewed by software like KickassUndelete.
TIP: If you use KickassUndelete (or the like) and find filenames leftover from your previous shreds, then use “Moo0 Disk Wiper” to get rid of them. It’s also free.
File Shredder Tool was last updated in 2016, but it still works and is available at the NoVirusThanks site:
https://www.novirusthanks.org/download-free-software
The above info is for HDDs. IDK about SSDs.
I find it much easier, faster, and more secure to purchase a new SSD [at the prices these days one can’t afford not to] slip mine out, install the new one, etc., etc. And my mind is so much more at ease.
Of course, some machines make this method impracticable if the SSD or an old HDD is buried beneath loads of other parts.
Use a Linux distro on USB with GParted and wipe?
Or
https://www.tenforums.com/tutorials/85819-erase-disk-using-diskpart-clean-command-windows-10-a.html
Loved this list:
https://www.lifewire.com/free-data-destruction-software-programs-2626174
Does overwriting a file actually work on SSDs?
AFAIK, it does not. Emptying bin is about just as efficient as the tools described here, unless mistaken
Obvioulsy, the more you write to disk, the greater the chance to actually overwrite existing data, but th’at’s about it.
This article should focus more on nand data map and the way various “secure erase” programs handle it. This is far from useful and I can’t see how it belongs here.
@archie do you know any software to safe delete a single file at ssd files? :]
@John G. Due to the way SSDs work it’s not possible to securely delete a single file.
If you REALLY need to remove a file:
Copy the SSD files to an HDD excluding the file(s) want to destroy.
Use the SDD manufacturer’s secure drive wipe utility and hope it actually does what it is supposed to do. You can’t check.
Copy the files back.
If you ever think you may need to store sensitive information on an SSD, encrypt the SSD.
@DrKnow thank you for the good provided info! :]
is it customable like Eraser? I use Eraser for daily tasks and nwipe (developed from DBAN code) before selling laptop.
I expected that this software would be able to wipe empty disk space, however it doesn’t. :[
There’s an extremely tiny and very old tool I still use called “Dummy File Creator” which is great for securely wiping SSDs which conventional secure-delete tools don’t work on.
Simply create a dummy file with random data the same size as your free space and then delete it.
This is guaranteed to securely wipe both magnetic and solid-state drives.
https://www.mynikko.com/dummy/
This is also why I prefer getting self-encrypting drives (SEDs) whenever possible. SEDs have a nifty feature called “instant secure erase” which when used changes the drive’s internal encryption key, effectively rendering all data encrypted with the previous key permanently unrecoverable in an instant. I don’t wipe whole drives that often, but when I do this saves so much time.
@beemeup5 after discussing this article with one friend of mine, he said me that he uses a very small software to write the entire disk with files, without NET requirements:
https://www.cylog.org/utilities/filldisk.jsp
According to the info, “FillDisk is a simple utility that fills up a disk with data. It starts with 1GB files, then drops to 512MB, 256MB and so on until it fills up completely the disk with files.”, please, could you post what’s your opinion about it? :]
Dummy File Creator requires .NET Framework 2.0 so unless you’re using Windows XP or older any recent version of Windows can run it out of the box.
FillDisk would be a good option for quickly wiping the free space of magnetic drives, however the problem is this is not guaranteed to work with solid state drives. This is because FillDisk does not have a random-fill option and only uses zero-fill for the files.
SSD controllers are like black boxes in how, when, and where they ACTUALLY write data to their nand flash. Some SSD wear-leveling algorithms use compression on written data, which means if a drive detects a contiguous data stream of only zeroes it may not even write the data and instead “reserves” the space in the file table. The operating system would check the file table and see something like “File A is 2.6 GB in size and occupies blocks D98 to E24”. When the OS tries to read any part of File A the SSD will return the value of zero because that is what’s “supposed” to be there however the SSD may not have actually written all zeroes to every block reserved by File A.
Normally this is not a problem because the process is entirely transparent to both the OS and the user, but this could be a security hazard should someone obtain physical access to the SSD and uses dedicated hardware to read the raw data directly from the nand flash bypassing the SSD’s controller.
You can read more about recovering data from SSDs here:
https://web.archive.org/web/20201112121238/https://www.forensicfocus.com/articles/recovering-evidence-from-ssd-drives-in-2014-understanding-trim-garbage-collection-and-exclusions/
(Article is slightly old but most information is still relevant today.)
FillDisk is typically used in conjunction with CyLog’s other software CyberShredder which replaces file data with random data before deleting them, but again the problem is an SSD’s wear-leveling algorithm which basically never overwrites currently occupied blocks and instead writes to less used blocks making secure deletion of single files impossible. CyberShredder “could” work on SSDs if it could delete all files at the end after filling them with random data, but because it deletes files one at a time as it goes, this allows free space to appear on the file table, which is literally free real estate to the SSD controller so now you’re essentially trying to bail out water from a boat with a hole that keeps getting bigger.
@beemeup5 thanks, a really good answer that helped me a lot! :]
@beemeup5 thanks, just simply amazing sofware! Very good info about SEDs too! :]