Google Chrome will use its own Root Store in the future
Google plans to transition from using the operating system's Root Store to the Chrome Root Store, that is maintained by Google and included in the Chrome browser.
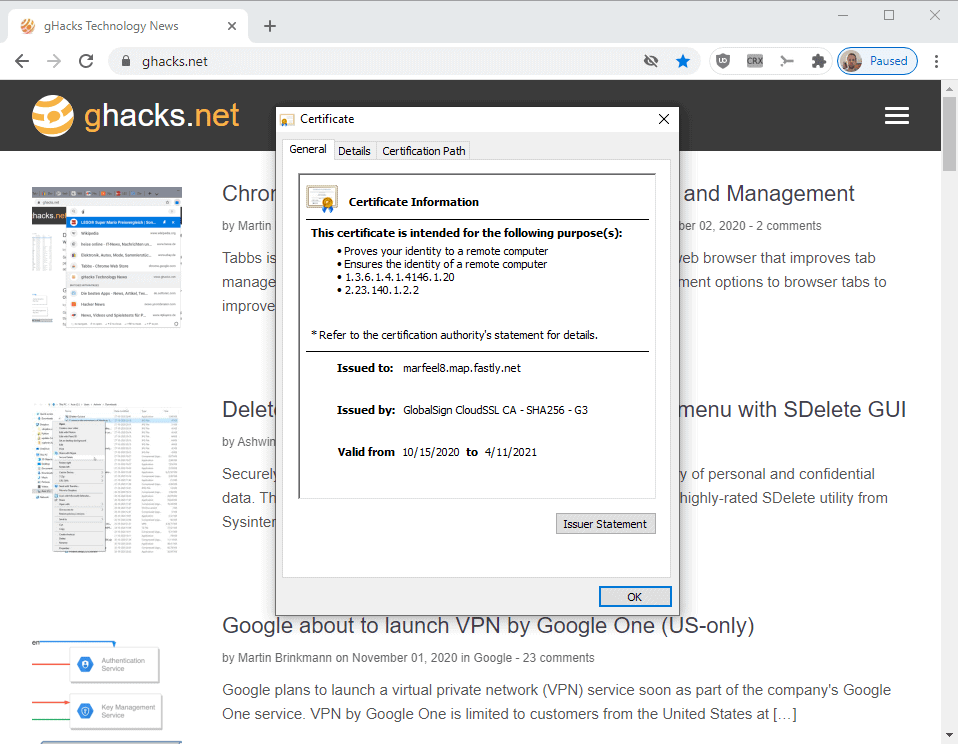
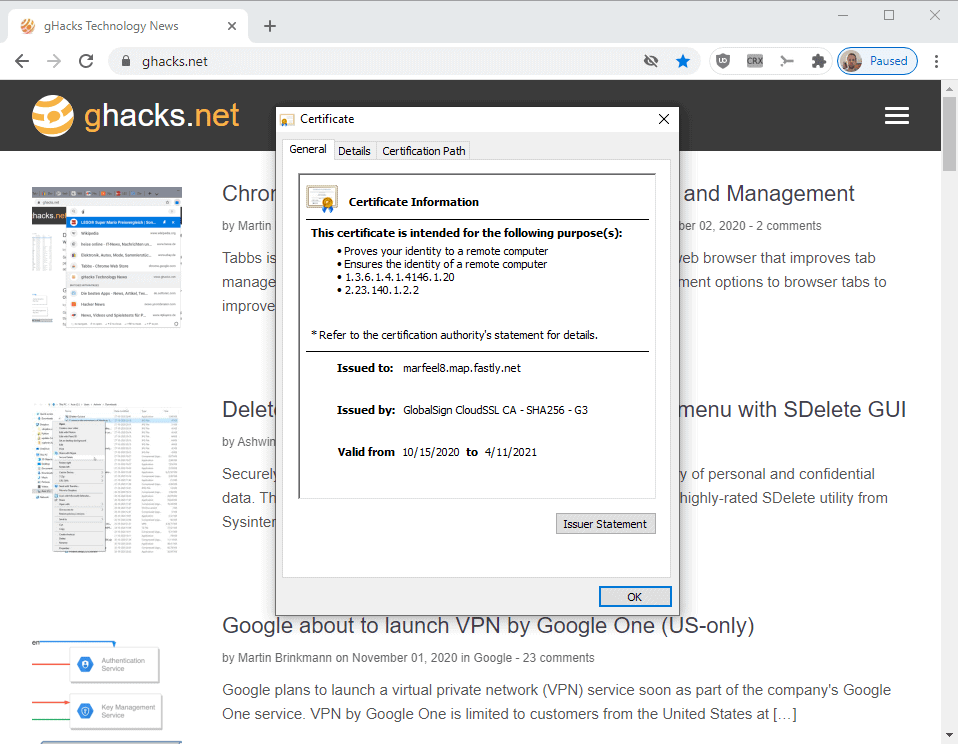
Google Chrome uses the operating system's Root Store currently to access Certification Authorities (CA). All operating systems maintain a list of root certificates that the operating system and applications that run on it use for various purposes.
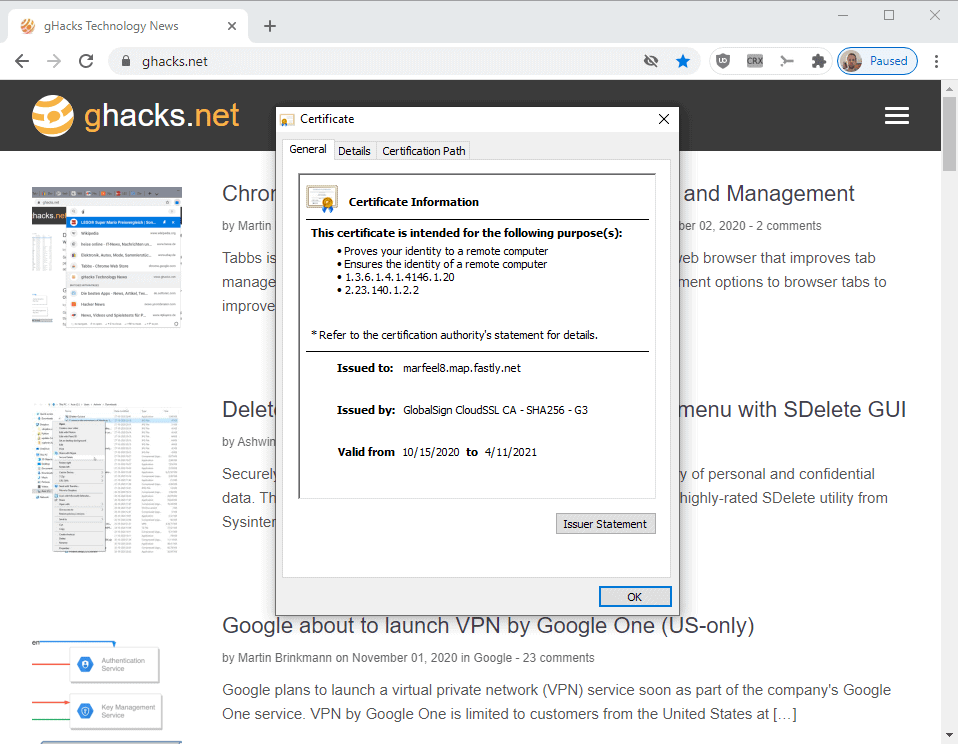
The browser uses these to establish secure connections to websites, and to determine the authenticity of a site.
Google wants to transition away from using the operating system's Root Store for verification purposes; one of the main reasons for doing so is to ensure that the same root certificates are available on all platforms the browser is compatible with.
This will ensure users have a consistent experience across platforms, that developers have a consistent understanding of Chrome's behavior, and that Chrome will be better able to protect the security and privacy of users' connections to websites.
The exception to the rule is Apple's iOS operating system as it prevents Chrome and other third party programs from using their own Root Stores.
Chrome on all other supported platforms, namely Windows, Linux, Mac OS X, Android and Chrome OS will be transitioned to its own Root Store.
Google has selected a number of Certification Authorities for inclusion in the Transitional Root Store. Some of these were picked based on their reliability and performance in the past to promote "interoperability on different devices and platforms" and to minimize compatibility issues.
Google used public and verified information, such as information from Mozilla's Common CA Certificate Database, to verify Certification Authorities.
Certification Authorities that have not been selected by Google may request inclusion by following a procedure outlined on this page on the Google website.
Google is not the first company that introduces its own Root Store in its browser. Mozilla switched to its own Root Store in the past in the organization's Firefox web browser, for very much the reasons that Google is highlighting. Browser makers get more control over the Certification Authorities that the browser trusts, and may react quicker to security or privacy issues than was the case in the past.
Firefox includes options to use the operating system's Certificate Store instead of the browser's one through policies.
The transition to its own Root Store will add more to the workload of administrators, provided that Chrome is used by the organization. For users, not much will change provided that the transition is smoothly.
Now You: What is your take on the change? Do you check certificates and Root Stores on your devices?


















Whoever controls the certicate stores also controls who can add certificates, and who can intercept the encrypted communications, locally or remotely. There are more stakes behind this now and in the long run than just “to ensure that the same root certificates are available on all platforms the browser is compatible with.” Is the current worldwide interception by Cloudflare and similar ok or not ok ? Or more directly by Google-approved or Google-unapproved state actors ? By a third-party who can add certificates on the machine one uses (employer, school, parents of minors…) ? By a third-party who can coerce through various means, even why not against compensation, certificate installation ? By installed software with user agreement or not, Google approved or not, malicious or not, and all combinations of those ? Lots of important questions left without much discussion in the hands of the entity that controls the stores.
@dostiers
Thank you.
I trust mozilla even less then I do M$, in a technical sense. I only trust either to do what it is their own best interest, not mine.
Dave:
about:config search for: security.enterprise_roots.enabled and set to true It may already be.
Finally! I’ve been waiting for Google to do this for many years now. And with Google VPN on the way, this is all great news.
This is probably o.k. for non-technical users but it is very common among developers and businesses to use their own CAs and it becomes a nightmare trying to configure every application to include your cert. Hopefully they will leave a configurable to use the operating system’s store or it will certainly hurt enterprise adoption.
Can you please elaborate on this further?
Like explain to me exactly how to make FF use my OS certificates?
“Firefox includes options to use the operating system’s Certificate Store instead of the browser’s one through policies.”
On linux it is easy to edit ca-certificates.conf but has anyone any idea how to edit the the cert database in firefox then import it to another firefox?
I’d like to keep ~10 root certificates not more. “Distrusting” them (the chinese and the whole asian region) takes forever on each device.
An article about it?
>“Distrusting†them (the chinese and the whole asian region) takes forever on each device.
wow, why? this means your machine can’t execute anything signed with a certificate issued by an asian CA? i mean sure, remove shit like darkmatter, but ban an entire continent?
Why not? Can you trust them especially in china or turkey? Why should we tolerate them?
When the time comes (mandatory CAA check or DANE) it won’t bother me anymore.
Stv: Can you trust non asian CA ? I’ve heard rumors of privacy being in a bad state there…
Rumors vs facts.
So i think the new edge will not follow this, because, i don’t see why Microsoft will let Google take away their selection of trusted CA.
And i don’t think it’s a good idea, Google want to control internet, but in the end it’s the admin sys who have to support these change, when i configure windows 10 and remove a trusted authority, i expert ALL the applications in the system to follow my choice, and i don’t except application to select their own trusted root without my permission.
Just no. Microsoft controling the OS and all browsers on it is a very bad idea.
Each browser should control their certificates, if user has an issue with the certificates of a browser, he could try another.
Their latest disgusting bug.
Windows 10 bug: Certificates lost after feature upgrade? We’re working on fix, says Microsoft
Microsoft confirms that upgrading to a newer version of Windows 10 sometimes results in lost certificates.
zdnet.com/article/windows-10-bug-certificates-lost-after-feature-upgrade-were-working-on-fix-says-microsoft/