Critical font parsing issue in Windows revealed (fix inside)
Microsoft published an advisory yesterday concerning a recently detected font parsing issue that affects all supported versions of the company's Windows operating system (including Windows 7).
The issue is rated critical, the highest severity rating. Microsoft notes that it is aware of limited targeted attacks and that it is working on a fix to close the vulnerability.
The remote code vulnerability is found in the Adobe Type Manager Library and attackers have multiple options to exploit the issue including convincing users to open a specially crafted document or viewing the document in the preview pane of File Explorer / Windows Explorer.
Two remote code execution vulnerabilities exist in Microsoft Windows when the Windows Adobe Type Manager Library improperly handles a specially-crafted multi-master font - Adobe Type 1 PostScript format.
A workaround has been published by Microsoft that prevents attacks targeting Windows Explorer / File Explorer. Microsoft notes that the workaround does not "prevent a local, authentication user from running a specially crafted program to exploit the vulnerability".
The workaround:
For Windows 7, Windows 8.1 and Windows Server 2008 R2, 2012 and 2012 R2:
- Open a Windows Explorer instance and select Organize > Layout.
- Disable the Details pane and Preview pane options (if they are enabled. You should notice that the panes are not displayed when disabled)
- Select Organize > Folder and search options.
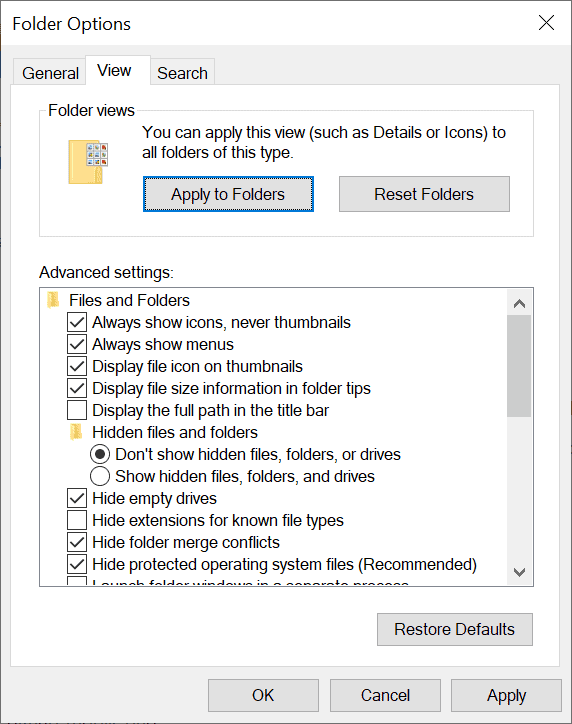
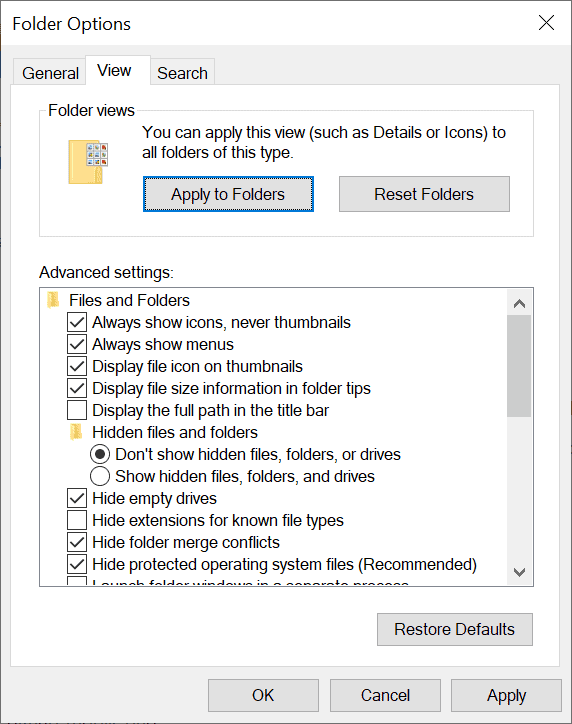
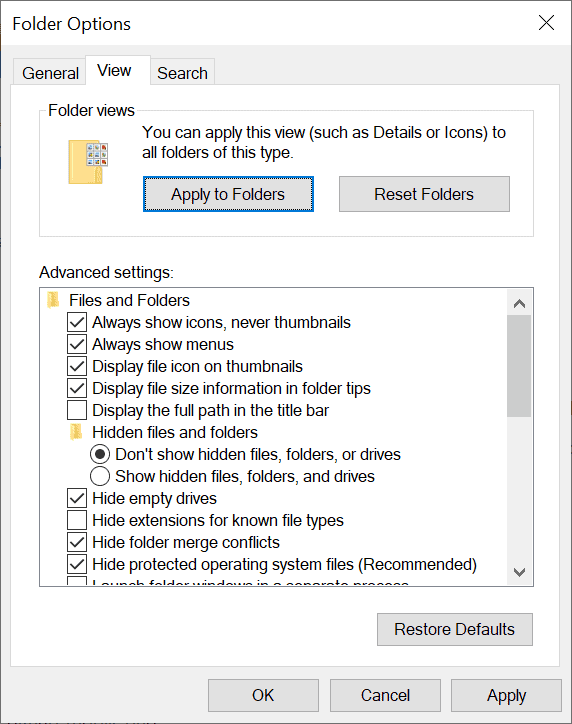
- Switch to the View tab.
- Under Advanced Settings, check "Always show icons, never thumbnails".
- Close all Windows Explorer instances.
For Windows 10, Windows Server 2016 and 2019:
- Open File Explorer and switch to the View tab when it opens.
- Clear the Details and Preview pane so that these are not displayed in File Explorer anymore (if they were displayed previously).
- Select File > Change folder and search options.
- Check Always show icons, never thumbnails in Advanced Settings.
- Close all File Explorer instances so that the changes can take effect.
The changes can be undone once the fix landed in Windows. Just repeat the steps outlined above but instead of clearing or checking the options, you'd do the opposite.
For systems on which the WebClient service is used, Microsoft recommends disabling the service for the time being as it blocks "the most likely remote attack vector through the Web Distributed Authoring and Versioning (WebDAV) client service".
Disabling the service will result in WebDAV requests not being transmitted. Also, any service that depends on the WebClient service will not start.
Here is how that is done:
- Use Windows-R to bring up a Run box.
- Type services.msc and click OK to open the Services Management window.
- Locate WebClient in the Services listing, right-click on it and select Properties.
- Switch the Startup type to Disabled.
- If WebClient is running, select Stop.
- Click ok and close the Services management interface.
Administrators who manage Windows 10 version 1703 and earlier systems, including Windows 8.1 and 7, may also disable ATMFD using the Registry.
Here is the script that you need to run:
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows]
"DisableATMFD"=dword:00000001
Non-ESU Windows 7 systems won't receive the security update according to Microsoft.






















It may be interesting for UBO users to block third-party remote fonts
https://github.com/gorhill/uBlock/wiki/Per-site-switches#no-remote-fonts
It would be interesting to discuss whether this option is effective or not.
It may be interesting for UBO users to block third-party remote fonts.
https://github.com/gorhill/uBlock/wiki/Per-site-switches#no-remote-fonts
It would be interesting to discuss whether this option is effective or not.
> Sampei Nihira: “It may be interesting for UBO users to block third-party remote fonts.”
Blocking remote fonts from being rendered on a webpage is irrelevant to the ADV200006 security vulnerability in question.
Reason: Web browsers like Firefox, Chromium, etc. & even Microsoft’s own Internet Explorer all do NOT use WinOS’s vulnerable Adobe Type Manager Font Driver (atmfd.dll) to render fonts on a webpage.
Thumbnails are best left to specialized programs, not explorer. I hate that you see thumbnails when dragging in 10, waste of space.
“open a specially crafted document”
What kind of document? PDF? DOC?
> Windows Fix: Delete Windows: “What kind of document? PDF? DOC?”
Any kind of document that contains malformed Adobe Type 1/PostScript & the equivalent newer OpenType (OTF) fonts.
For Windows 7, …
Open a Windows Explorer instance and select Organize > Layout.
Should read as “select Tools > Folder Options”.
good thing that i use firefox then. only chrome downloads files automatically without asking the user so those could get exploited easily but others are safe as long as they are careful
@anon
That’s rather interesting crazy talk. Do you have any more to add?
Thank you @Martin for the fix! 😄
Windows 8.1 here. The fix as described would seriously disrupt my workflow and I think that the risk is small for most home users. I will not be applying the fix.
The fix as described DOES seriously disrupt my workflow already.
I already had ‘Details pane and Preview pane’ options disabled, but checking ‘Always show icons, never thumbnails’ is a true bother. I’d love to be sure that “the risk is small for most home users.” because my feeling is that I’ll revert to thumbnails display before sunset.
Any true, authentic techies around? If so: is the risk small for most home users?
@Tom Hawack
Most home users will never be exploited by this threat.
Yet things being as they may with Murphy’s law, your chances of being exploited by this are likely very high, as that’s how the cookie crumbles.
@spork, a dynamic risk probability if I understand correctly with a trend to a higher risk.
Microsoft’s ADV200006 [https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/ADV200006] states several other workarounds than those mentioned in this article,
– Disable the WebClient service
– Rename ATMFD.DLL (ATMFD.DLL is not present in Windows 10 installalations starting with Windows 10, version 1709)
– Setting “DisableATMFD” to 1 in HKLME\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows (Win<=8.1)
Personally (Win7 here) I've always had the WebClient service disabled and I've set "DisableATMFD" to 1, haven't renamed ATMFD.DLL .On that basis I've cleared the 'Always show icons, never thumbnails box' in Explorer. Hoping this mitigation is reasonable.
OpenType fonts (OTF) become unusable of course. None installed here and I'll have to check if any of my applications rely on OTF availability but I don't think so.
Permanent Fix: Switch to Linux
@Sam
Of late, Debian, Fedora Project, Red, SUSE Linux, and Ubuntu (AKA Linux) have all been found to have a “Critical Vulnerability” (CVE-2020-8597) that has gone undetected for 17 years!
This vulnerability has allowed hackers to cause stack buffer overflows and to exploit Linux systems by remotely taking over the code execution of a process and gaining root-level privileges.
So I’m supposed to not have any thumbnails until April 14th? Yeeeeaaaah..that’s not gonna happen. Let me guess how this goes: The masterminds at Redmond will release an emergency patch, which will just disable the thumbnails and hide the preview panels. This will enrage the whole planet. After that, Redmond will release another patch that will revert the first patch but will also break every system that uses Photoshop or anything even remotely affiliated with images. Then another patch will come, which will revert THAT but also will break a million new things. Then Microsoft will say everyone is lying about their issues, but a fix will be available when a new Windows rolls out in 2022, which by then requires a microsoft account to install or use. This new Potato OS will also have the exact same flaw as this one.
I really fear that 10/2004 may do away with the local login and I wish that the Linux Mint/other maintainers would get Linux Kernel 5.6 plumbed into their distros ASAP because my new Windows 10(1809) Home edition based laptop really needs a Linux Mint dual boot option just like all my 7/7 Pro(EOL) laptops have currently. And 7/EOL is not going to get that needed fix as that’s for 7/ESU qualified folks only.
So my keep 7 safe option after 7’s EOL is dual booting that with Mint 19.3 and 7 kept offline when booted into and Mint 19.3 for everyday online usage from now on. And I want to do the same for my new AMD Ryzen 3000H series APU based Laptop that’s currently kept offline under 10(1809) Home but Mint has to have Linux Kernel 5.6/later in order to have the proper Ryzen/3000H series fan/power management driver fixes included. So I’m some weeks/mounts off for dual booting 10 with Mint 19.3 on that laptop.
But I really want Mint 19.3 as my alternative OS option for 10(1809) Home in order to avoid 1903/1909(as long as possible) and the issues there that are not fully fixed and to avoid 2004 until I’m sure that local logins are safe under 2004. But I can not wait for Mint 19.3 to get Linux Kernel 5.6 available and that vetted/certified and offered up via a kernel update from the Mint Repo.
And having an alternative OS boot option is really the best way to deal with Redmond’s forcing that breaks things more often than not. I’m really not going to become one of Redmond’s forced 10 BETA testers and MS can wrap that in their EULA printout and smoke it.
Imagine a magical world where linux could run Windows 7 and 10 as .AppImage =)
“And 7/EOL is not going to get that needed fix as that’s for 7/ESU qualified folks only.”
Any Windows 7 PC with or without ESU can get all Microsoft updates. Just browse to askwoody.com for the script.
I’ve read that but really with all the Zero Days targeting the folks in Redmond’s crappy QA/QC habits I’d rather just boot into Mint 19.3 and keep 7 offline forever after it’s EOL.
It’s just better to move on from 7/EOL and onto something non Redmond based, and I’ll be hopefully soon enough doing that same thing with 10(1809) Home and maybe that staying offline and the newest laptop booting into Mint 19.3 most of the time. And no hoop jumping required trying to keep 10’s mothership connection delayed indefinitely under Mint 19.3.
What are you on about? This issue affects those versions as well…
Windows 7 here. Workaround applied. Thanks Martin.
Me too, thanks Martin
Windows 10 never seizes to disappoint.
God job, Microsoft, if you wanted to make Windows 2000, Vista and 8 look like masterpieces compared to Windows 10, you have succeeded.
You didn’t even get as far as reading the first sentence did you? “all supported versions of the company’s Windows operating system (including Windows 7)”
atmfd.dll was removed in version 2017 Windows build 1703 Redstone 2
“…including convincing users to open a specially crafted document or viewing the document in the preview pane of File Explorer / Windows Explorer”
That’s evidently a huge risk to people who open the “Free Voodoo Pills To Enlarge Your XYZ” emails and carefully follow the instructions on how to handle the attached document.