German Data Protection Agency: Windows 10 1909 Enterprise Telemetry can be fully disabled
Telemetry has been a hot topic ever since Microsoft released the first version of the company's Windows 10 operating system. Microsoft decided to integrate the collecting of data deeply into the operating system; so deep that the consumer editions Windows 10 Home and Windows 10 Pro did not include options to turn off Telemetry completely. Even Enterprise and Education editions required Telemetry, but these came with a specific Telemetry setting just for these editions.
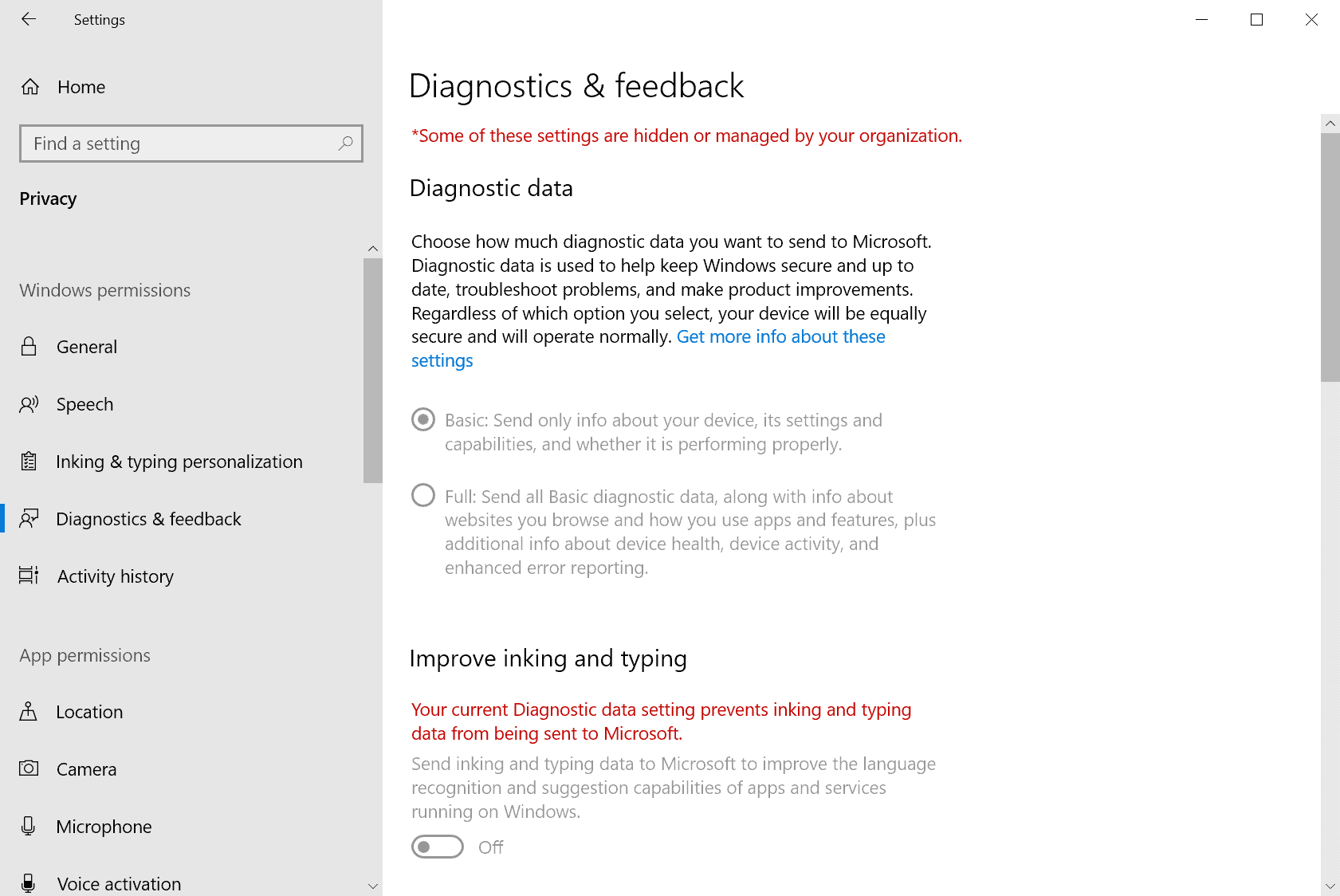
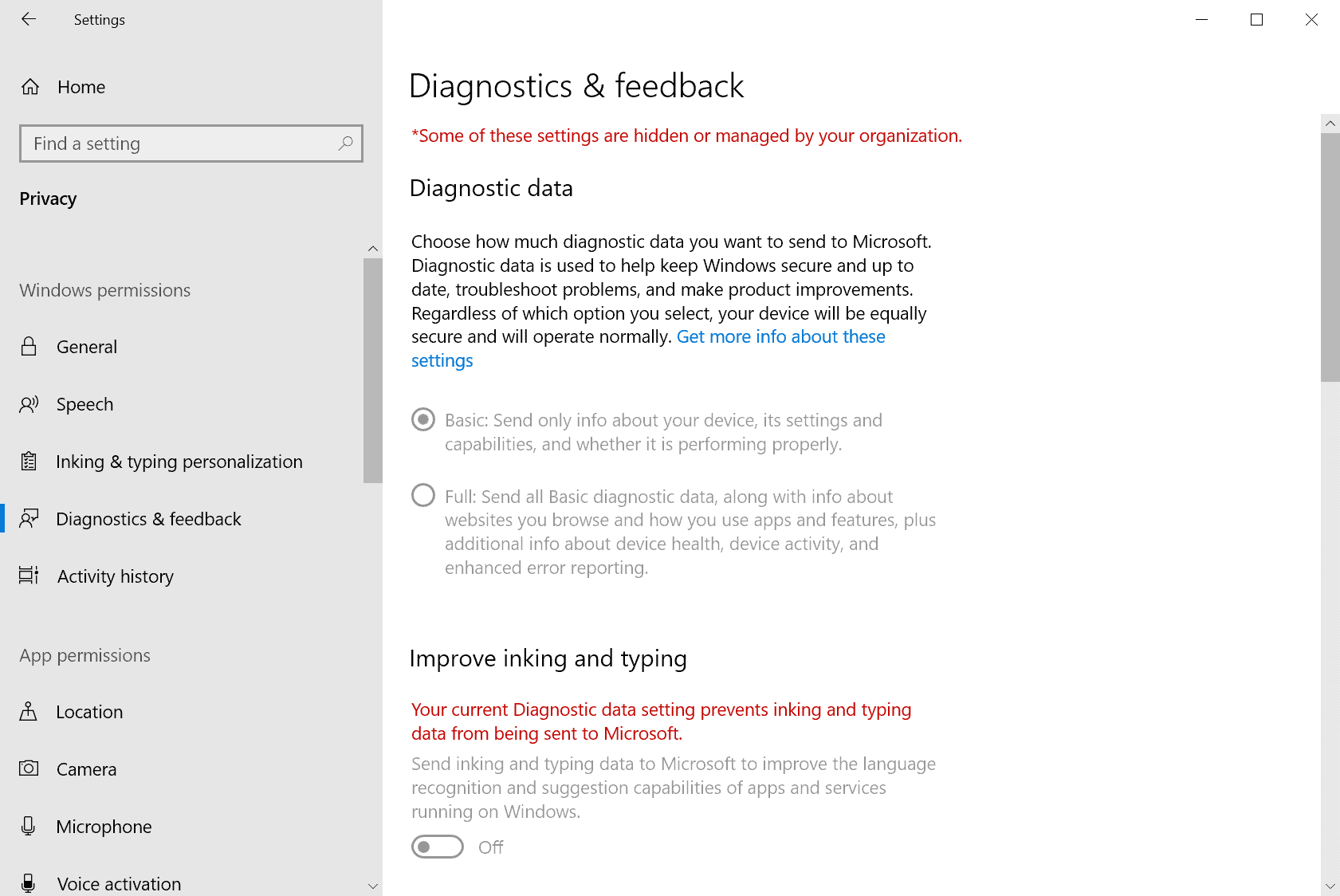
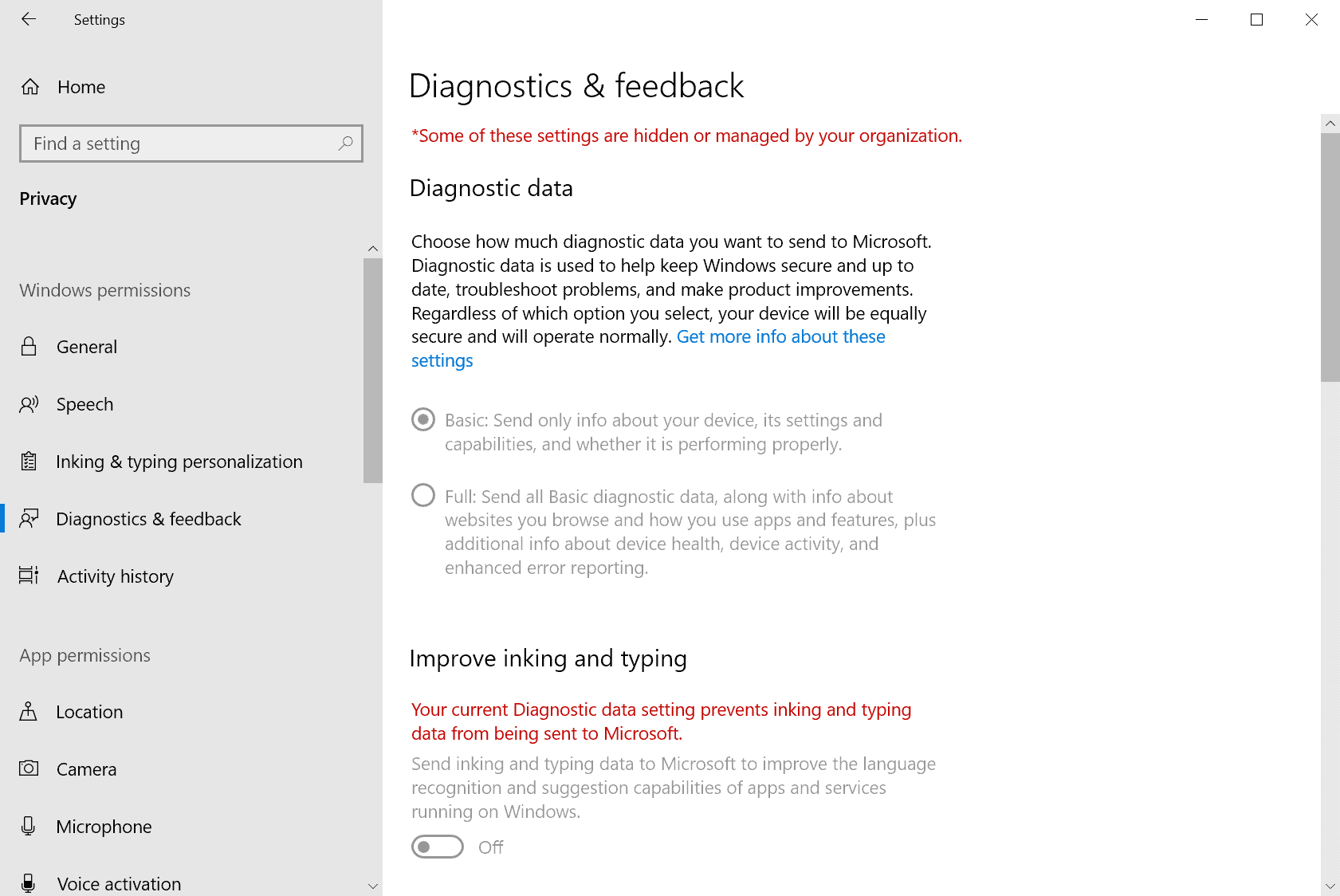
Home and Pro users can select between Full and Basic Telemetry levels; Basic limits the information that is transferred to Microsoft but it does not block the sending entirely. Enterprise and Education editions support a Security Telemetry setting that limits data collection and transferring significantly.
Third-party tools and scripts to tame Windows 10's hunger for data are available and can be used.
The Bayerischen Landesamts für Datenschutzaufsicht -- Bavarian agency for data protection -- published its activity report for 2019 recently. The report includes information about an analysis of data collecting of Windows 10 Enterprise version 1909.
The report, which you can access here (German PDF) suggests that organizations who may buy Enterprise or Education editions of Windows 10 may disable the sending of Telemetry data entirely in Windows 10 version 1909.
Test setup was identical to other tests conducted to find out about the data sending of Microsoft's Windows 10 operating system. A Windows 10 version 1909 Enterprise system was set up in a lab; all traffic, incoming and outgoing, of the system was recorded and analyzed.
The telemetry level of the Windows 10 device was set to Security and tools/settings provided by Microsoft were used to eliminate telemetry activities.
The agency discovered that it is possible to deactivate the sending of Telemetry data on Windows 10 version 1909 Enterprise (and Education) machines completely in the lab environment.
The test results need to be verified in real-world scenarios according to the agency. Telemetry would not be an obstacle in regards to data protection on Enterprise or Education systems running Windows 10 if real-world tests confirm the finding.
The agency notes that the situation is different for Windows 10 Pro (and Home) systems as data collecting cannot be disabled completely in those editions of Windows 10.
Now You: do you run Windows 10? Have you made data collecting or Telemetry changes? (via Deskmodder)



















As a German, I can’t fail to notice how the headline of this article is not actually the conclusion of the assessment.
The actual conclusion was not that “Telemetry can be fully disabled”, it was that even with an Enterprise edition, and a long list of steps taken to reign in the telemetry, Win10 still ended up sending encrypted data, with nobody having a clue what data.
Their final conclusion was more aligned with pragmatic lines, stating that the use of Win10, with their suggested hardened settings, was only possible with a “bearable level of rest risk”.
I don’t know what all this means, seems like marketing stunt taken from Tesla’s BS bag.
MS, a bloated trillion dollar cap monstrosity has a mature OS that works fine, so what else can they do with it beside collect user info (and offer dumb ass apps for kids)? They could just leave it alone, data brokering industry peer pressure won’t allow that, I’d guess.
Gotta wonder with all the amazing blunders made with Win 10 if MS has any idea what data is collected or what to do with it? Probably not but I’ll still do whatever I can to try and stop it.
I read today about a man in Germany pulling a little red wagon with 99 cell phones down streets with no traffic creating traffic jams on Google Maps. Google commented “Thank you for providing valuable input…” Riiiight.
SImilar to browsers, the out of box “experience” is miserable, annoying and downright creepy in some respects. With many, many changes, Windows and browsers can be made fast and unobtrusive but it takes a lot of work.
But from what I’ve seen, this isn’t possible with most versions of Windows10. Even using a separate pi-hole device doesn’t help because MS changes their intrusive telemetry IP’s to which they transmit any data they desire (and can change what they send at any time without your consent).
Most versions of Windows 10 are completely unsecure, as there is no way to know what data is being transmitted from your system to external servers.
It’s still horrendous that you can’t disable telemetry in all Windows editions. Microsoft is awful.
The big issue is with Telemetry disabled, you can’t send feedback via their stupid Feedback Hub app. It forces you to set to Basic otherwise you are not allowed to report bugs, give suggestions.
Why would anyone want do that? Microsoft gives a crap on such reports and suggestions. There are tons of reproducable bug reports hanging around for years and decades without any response.
I don’t understand how anyone uses Windows 10.
It’s well documented that data is regularly transferred out of your computer.
It’s largely unknown what data is actually transmitted.
The only hint as to what is possibly being transmitted comes from Microsoft, but trusting that information is like letting the fox guard the hen-house.
It’s a good point, but for me it’s a trade off and an experiment. I was happy with W7, rock steady for years, but the same could be levelled at that OS I suppose.
With the end of support I had to face the Linux or W10 question. Both were free and keeping a lot of my programme knowledge and familiarity with Windows tipped the balance to be honest. I think it’s still an experiment because I may yet transfer to Linux if I can’t wrangle W10 into shape. I’m a little pensive about Linux and don’t welcome a steep learning curve after 30 years of Windows, but am gradually dawning to the lure of open source, a bit like vegitarianism.
I am concerned with security and dislike our surveillance culture of which this is a perfect example, but have yet to bite the bullet and ditch the convenience it represents.
Yes Mike, it’s a conundrum. Use something secure and relatively private, or use Microsoft / Google products instead. It’s up to everyone to decide for themselves.
I won’t put any important data on any Windows 10 system or use Google products for anything meaningful.
I’ve switched many people to linux, and these days it’s pretty easy.
I’m a couple of weeks into W10 pro’ and switched off everything available in settings and used shutup10 and w10privacy. However results were not perfect, so I used Simplewall to block stray traffic. Initially the system slowed to a crawl and began to store commands. I identified the problem started after disallowing sihclient.exe and usocoreworker.exe. Upon allowing these two programmes all stored commands (clicks) were executed and the system recovered. All other OS components are disabled. It seems these are related to updates, so W10, at least my installation, reacts badly to having updates cut off.
Traffic has reduced, but I assume some data is exfiltrated in the update process. So the question remains, does any method exist to secure W10? I suspect the trade off is updates for privacy, one type of security for another.
Learn how to use the Group Policy Editor, gpedit, make your changes at the computer level. (Computer Configuration>Administrative Templates>System & Windows Components.
gpedit is the core of Pro, otherwise, Pro’s not much different than Home. Avoid layers of protection with third party programs, that approach can make a mess out of the registry, eventually leading to a reinstall.
Search in C: for gpedit, then shortcut it; or find it in C:\Windows\System32\gpedit.msc. Do as much as possible in gpedit first.
Turn off any services and tasks not needed, Control Panel>Administrative Tools>Services & Task Scheduler.
Block any outgoing connections not desired in Windows Defender Firewall, same location in Control Panel.
Do often, before each session if needed, system restore points, Control Panel>System>System Properties>System Protection because changes will occasionally wreck something, to revert to before changes state.
Consider not using Windows Defender, go to a simple third party AV, not an internet suite. After turning off multiple “features” giving Defender an open door back to MS is questionable.
If you’re not using Edge, turn off as much as possible in settings. Go to Control Panel>Internet options and do the same.
Document all the changes made; I know, it’s a PIA but reversing a chain you’ve forgotten isn’t much fun maybe impossible.
Gpedit tips:
System>Internet Communication Management>Internet Communication Settings
Has most Internet settings for error reporting, customer experience, update, drivers, etc. uploading to MS.
System>OS Policies
enable or disable activities uploading or tracking
Firewall:
Blocked Apps blocked in Firewall> Allow or Block an app…
also Create Outgoing rules
After gpedit and the Firewall are understood, third party programs won’t seem as attractive.
Similar to overloading a browser with extensions, disabling too many things in Windows can make it function poorly, create frequent restore points!
Let’s talk about what really happened here.
As Martin reported findings were presented in agency’s activity report for 2019, which is a 78 pages long document. As indicated in the table of contents, the Agency under point 3 it titled Control and Audit (page 18 – 22). Subitem 3.4 is titles ” Windows 10 and telemetry data” (page 22). It reads as follows:
3.4 Windows 10 and telemetry data
The data transfer to Microsoft can be deactivated with the Enterprise version.
The use of Windows 10, in particular the transmission of so-called telemetry data from a Windows 10 computer to Microsoft, has occupied data protection supervisory authorities for a long time. For this reason, the Data Protection Conference has founded a sub-working group of the “Windows 10” Technology Working Group, which is to prepare an evaluation of the data flows to Microsoft in terms of data protection law. (www.datenschutzkonferenz-online.de/media/dskb/20190403_positionierung_windows_10.pdf)
This working group met in Ansbach in December2019 for a laboratory analysis of Windows 10, which was conducted by us and the Bavarian State Commissioner for Data Protection. Microsoft employees were also invited (of which more than 10 people, mainly from the technical area, came from Microsoft in the USA) to answer any technical questions that might arise during the laboratory analysis.
A test scenario with a Windows 10 computer, which had an enterprise version (version 1909) installed, was set up in such a way that all data flows from this computer were recorded by means of a man-in-the-middle analysis while still within the laboratory network. The system was configured with information and tools officially provided by Microsoft in such a way that the telemetry level “Security” was set and all data flows could be deactivated.
In the course of this laboratory analysis it was determined that the telemetry data from a Windows 10 computer can be completely deactivated with the Enterprise version. Only calls to (Microsoft) servers that provide up-to-date crypto-graphic certificates could not be deactivated by this configuration, as these are required for the secure operation of a Windows 10 system on a daily basis (e.g. if an invalid SSL root certificate is recalled). These calls can also be prevented by specific system configurations, although such a procedure is not recommended for security reasons.
The result of this meeting in our technical laboratory was that the telemetry data discussed controversially in terms of data protection law can be deactivated in the examined scenario when using the Enterprise version (and thus also the Educa-tion version).
If this result is confirmed in the actual use of Windows 10 in companies, then at least the handling of telemetry data with Windows 10 Enterprise (also in managed environments) does not constitute a legal obstacle to the use of this operating system under data protection law. How, on the other hand, the use of Windows 10 Pro is to be evaluated by those responsible, in which the telemetry data can be reduced but, as is well known, cannot be switched off completely, could possibly become another work assignment of the Data Protection Conference (DSK).
Translated with http://www.DeepL.com/Translator (free version)
Now please recall where headquaters of Germany are situated? You guessed it, headquartes are in Munic, capital of the state of Bavaria. Please also recall that Microsoft’s lobbying activities might have played a role in convincing the Munic city parliament to take a decision on skipping the Munic Limux project (https://www.derstandard.at/story/2000110966260/aus-von-linux-in-muenchen-microsoft-hat-jede-form-von)
And now we have this meeting in this picturesque little town of Ansbach some 200 km north of Munic with more the 10 representatives of Microsoft attending.
“This working group met in Ansbach in December2019 for a laboratory analysis of Windows 10, which was conducted by us and the Bavarian State Commissioner for Data Protection. Microsoft employees were also invited (of which more than 10 people, mainly from the technical area, came from Microsoft in the USA) to answer any technical questions that might arise during the laboratory analysis.”
By the way, the working group is part of “The Conference of the Independent Data Protection Authorities of the Federal and State Governments “, the same body which
is responsible for the following paper: “Data protection with Windows 10
– Check schema -“, which is a guide on how to check whether “Windows 10” is compliant with data protection laws in Germany. (https://www.datenschutzkonferenz-online.de/media/ah/20191106_win10_pruefschema_dsk.pdf).
So make up your mind, about wether there is more to the story than a public PR stunt.
I gave up fighting them about a year after I got Windows 10 and installed KDEneon instead. Best decision ever.
Try to buy a consumer PC with Enterprise. Even Pro is an “option” that is rarely available on consumer models, Home is preloaded by default. Microsoft (and all the biggest US tech companies!) is robbing hundreds of millions of customers and selling their data to third parties.
https://www.theverge.com/2019/7/30/20746868/apple-data-transfer-project-google-microsoft-twitter
https://www.geekwire.com/2018/facebook-data-sharing-partnerships-amazon-microsoft-tech-giants-center-latest-privacy-scandal/
https://www.theatlantic.com/technology/archive/2018/12/facebooks-failures-and-also-its-problems-leaking-data/578599/
https://www.theguardian.com/world/2013/jul/11/microsoft-nsa-collaboration-user-data
“what we are permitted [by the US deep state] to publish continues to fall short of what is needed to help the community understand and debate these issues.” – Microsoft
https://www.mic.com/articles/49009/nsa-prism-facebook-microsoft-reveal-number-government-data-requests-in-wake-of-scandal
To disable Telemetry in Win 10 Enterprise/Education *completely* the solution is simple: migrate to Linux.
You know what Russell, I reckon most people would be fed up with this type of unoriginal and totally unproductive comment.
To end such corporate abuse by Microsoft just migrate to Linux. Stop being a Microsoft masochist.
“The telemetry level of the Windows 10 device was set and tools provided by Microsoft were used to eliminate telemetry activities.”
In other words. It is highly unlikely that your own installed Windows 10 enterprise 1909 with all possible GPO telemetry rules implemented covers all telemetry-phoning-home. As Microsoft delivered additional software to disable telemetry fully.
Probably software, only available to the government and large powerful companies that can enforce this. The ordinary consumer Has to live with the fact that their Windows 10 still sends all-in.
So, the minority of Windows 10 users who qualify for Enterprise or Education licenses *may* be able to control what information gets sent back to Microsoft for — what? — a maximum of 18 months if they’re not running Enterprise LTSC? And so long as a critical security update doesn’t bundle in some new, undefeatable telemetry in the interim? Color me unimpressed.
“The Bayerischen Landesamts für Datenschutzaufsicht”
Martin, you know very well that this isn’t German, unless they now have a completely different idea of declension in Bavaria.
(“Bayerisches Landesamt”.)
He did not write “Data Protection Agency of Germany”.
No, he only wrote “German Data Protection Agency”, which- you know -in context means the same damn thing. It was more than implied.
So how did they do it? No way if translating that pdf document. Any suggestions?
Just use the simplewall firewall to block all other calls home after WPD/ShutUp changes.
https://www.henrypp.org/product/simplewall
You can NOT stop any web sites and IP numbers or ports which the Windows OS itself is using for phone home activities by using a SW firewall, Windows XP was the LAST Windows where one could turn off Windows internal ports and even then an ordinary SW firewall could NOT stop XP, you must dive deeper into the OS and turn off active ports, but XP was the last version, end of story.
Definitely useful, though the maintainer’s attitude is quite weird. Closed legit tickets on Github, like a bug with semicolons in file paths, with reasons that make no sense.
Still not buying the idea that telemetry is necessary, as computers and software development worked just fine for 30+ years without it.
@Kevin:
As well you shouldn’t, because telemetry is 100% not necessary. What telemetry does is to decrease software development and maintenance costs. That’s all.
If MS wants that 30% of desktops still running Win7 to adopt Win10, it will have to make pervasive, uncontrollable telemetry a footnote to its history. MS couldn’t get those users to adopt Win10 by giving it away – at least not this user. Does MS expect those Win users to pay to be abused? That’s an interesting corporate attitude.
So…
Not even firewall blocking to dodgy servers (Crazy Max’s Windows Spyblocker, simplewall, e.g.) will thwart telemetry? Not even via LGPO? Debotnet, O&O ShutUp10, etc.?
(Not that I was ever 100% convinced that this approach is 100% effective, anyway!)
I followed this guidance:
https://consumingtech.com/disable-telemetry-data-collection-in-windows-10/
And also block:
* bing.com
* bing.net
* data.microsoft.com
* telemetry.microsoft.com
* virtualearth.net
As a Windows 10 Home user, I found my settings to already be set for Basic. However I did change Feedback from Never to Once a week. Maybe this is actually useful to the user.
that reminds me a news in 2015 i guess about telemetry, i don’t remember where but i saved it as a word doc with some extra tricks found in comments.
i did one or two changes and never go any further into deep mods.
no third party soft used only clear yet numerous options
Here’s a screenshot for your collection. From LTSC 1809’s GPEdit ;)
https://i.imgur.com/o56PzJB.png
As usual, read carefully the policy decription. You Disable Telemetry by Enabling “Allow Telemetry” policy and setting it to 0-Secure. Disabling this policy actually enables Telemetry (it actually allows you to select the level via Settings, though Secure might not be an option, I can’t remember, nor I’m curious).
Note: some of these might not affect LTSC (for instance you have policies related to STore, even though you have no store). I know. I don’t care.
Yulia,
That setting determines user by user whether an override can be set by the user allowing higher levels than those set by an admin in GP. IOW, leaving it unconfigured allows users to set the level, enabling it sets it at the admin level, graying out the user buttons.
It’s only for diagnostic data, a tiny sliver of all the crap sent to MS.
In Win 10 Pro 1909, “Secure” is still available.
Just checked. Yup, GPedit all the way https://i.imgur.com/oSGPKSN.png
At least Secure doesn’t seem to be selectable via Settings anymore, and I’m not disabling that policy just to verify this.
From 2015 to 2020 many things changed, and now they are more hard to disable.
OK, but how exactly can one disable Telemetry in Win 10 Enterprise/Education *completely*. I would be useful to explicitly mention this as well (although I have a pretty good idea, using gpedit.msc – or is there still something else we should be aware of)?
LTS builds still remain the only usable ones, LTSC 1809 being the better one.
Are they telemetry-free or just CandyCrush-free?
LTS builds don’t even have store, so yes. It’s Windows 7, more or less, the only thing you have to bare is the Settings application, everything else is just Win32 programs, none of the “modern UI” nonsense.
LTS builds have telemetry.
“A Windows 10 version 1909 Enterprise system was set up in a lab; all traffic, incoming and outgoing, of the system was recorded and analyzed.”
That’s never going to be an as definitive proof of what can happen as if code wasn’t proprietary and could be inspected. The spyware/telemetry industry does not hesitate now to do “experiments” on a selected subset of targets (for example 1% of German users) and such tests wouldn’t catch that.
Finally someone else who understand this is a laughable metric.
Well that is good news for the 1%, now let the 99% do the same.
Do they give specifics yet on how to fully disable it beyond “Security” on Enterprise? I use Enterprise and have it set to Security and have disabled everything else that WPD offers. Beyond that I hope for the best.
I use O&O 10 Shutup which is free German software (in English) to disable as much as they recommend.
Regardless of said telemetry, this finding does not stop the fact that Win10 is crapware
The “Bayerischen Landesamts für Datenschutzaufsicht” is not the BSI.
I doubt these findings are useful, you can only trust these guys:
https://en.wikipedia.org/wiki/Federal_Office_for_Information_Security