What you should do after the September 2018 Facebook Hack
Facebook revealed on September 28, 2018 that attackers managed to exploit a vulnerability on the site that allowed them to take over accounts of Facebook users.
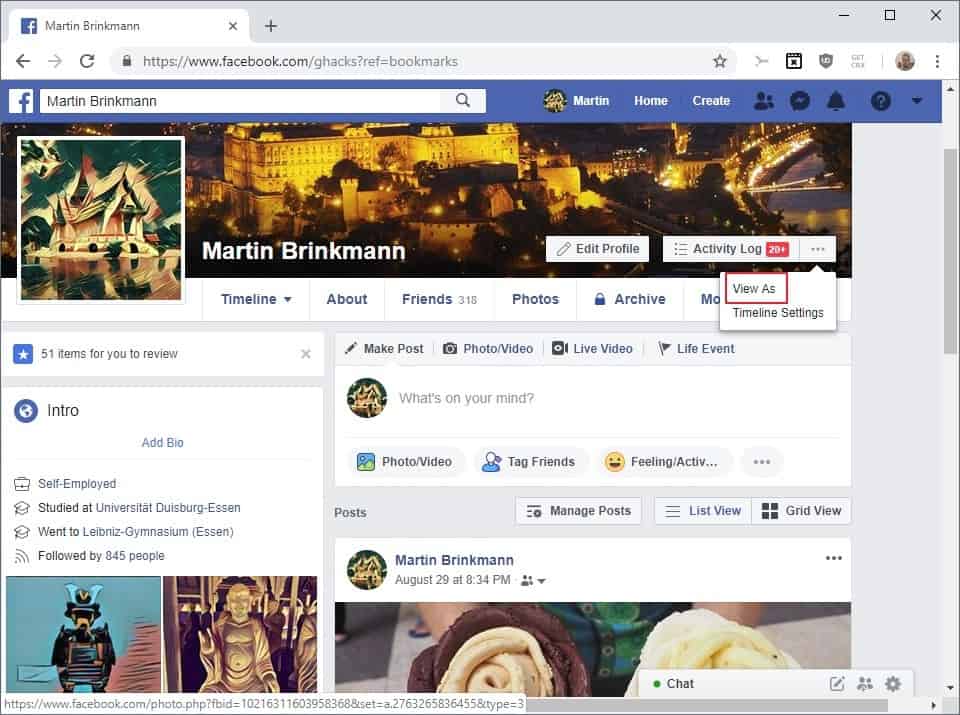
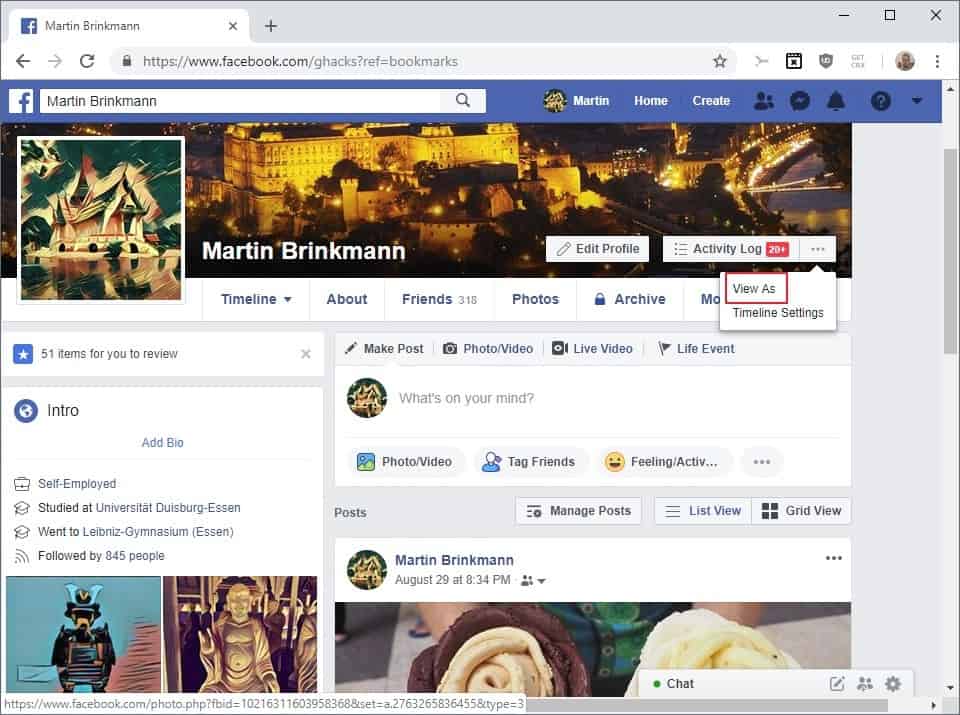
The issue, which affected about 50 million Facebook accounts and potentially 50 million more, used a vulnerability in Facebook's "View As" feature that allows Facebook users to view their profile pages as another user.
Facebook users need to select the "three dots" menu on their profile page and select the "View As" option displayed as an option when they do.
The company turned the feature for now. A notification is displayed to you that the feature has been disabled for the time being.
"Preview My Profile" Disabled
The "Preview My Profile" feature is temporarily disabled. Please try again later.
The attackers managed to obtain access tokens which allow anyone to access an account even without supplying a password.
Facebook's analysis is ongoing at this point in time. The company reacted fast and reset access tokens for affected accounts (nearly 50 million'), and reset access tokens for another 40 million accounts that interacted with View As in the past year.
Investigators have not determined yet whether accounts were misused or if information was accessed. The company plans to update the official security update post on its website once it has more information.
What you may want to do
The attackers managed to gain access to access tokens only. That is why Facebook does not recommend to users to change account passwords as the attackers never got hold of account passwords.
The resetting of the access token blocks access to the Facebook account for anyone who is trying to access it using the old access token.
Facebook displays a login prompt for affected users and a new sign-in to the account generates a new access token that is used from that point on forward.
Facebook users affected by the issue receive a notification about the incident on the next sign-in.
Still, there are some things that you may want to do:
1. Check the last logins
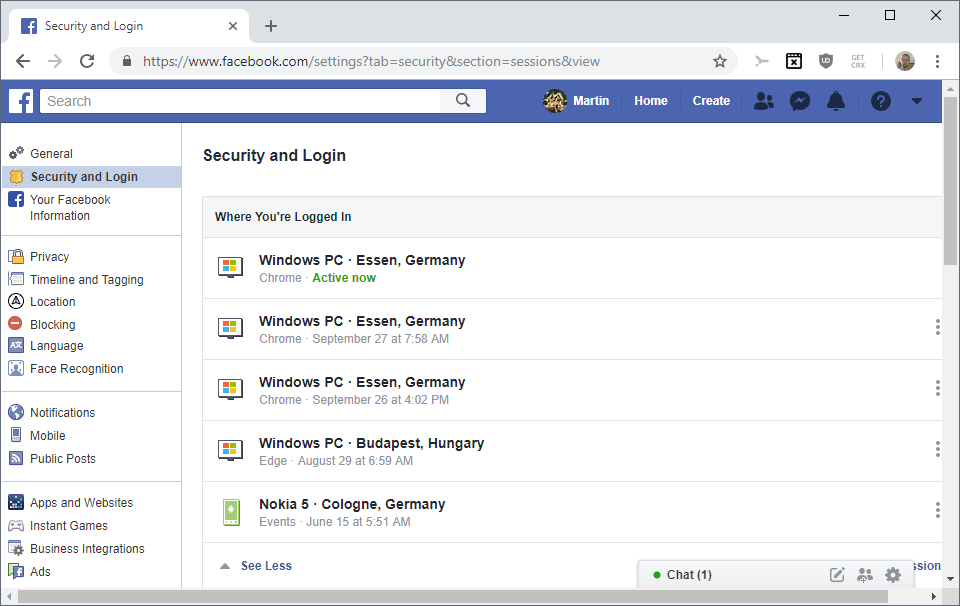
Go to https://www.facebook.com/settings?tab=security§ion=sessions&view and check the devices and locations listed under "where you're logged in".
Make sure that you only see devices and locations there that match your activity. Do the following if you suspect that a logged in session may be by a third-party:
- Click on the three dots on the right of that particular session.
- Select Log Out from the menu.
If you want to start clean, select "log out of all sessions" instead to block any device listed there but the active one from using the access token to access Facebook.
2. Precautions
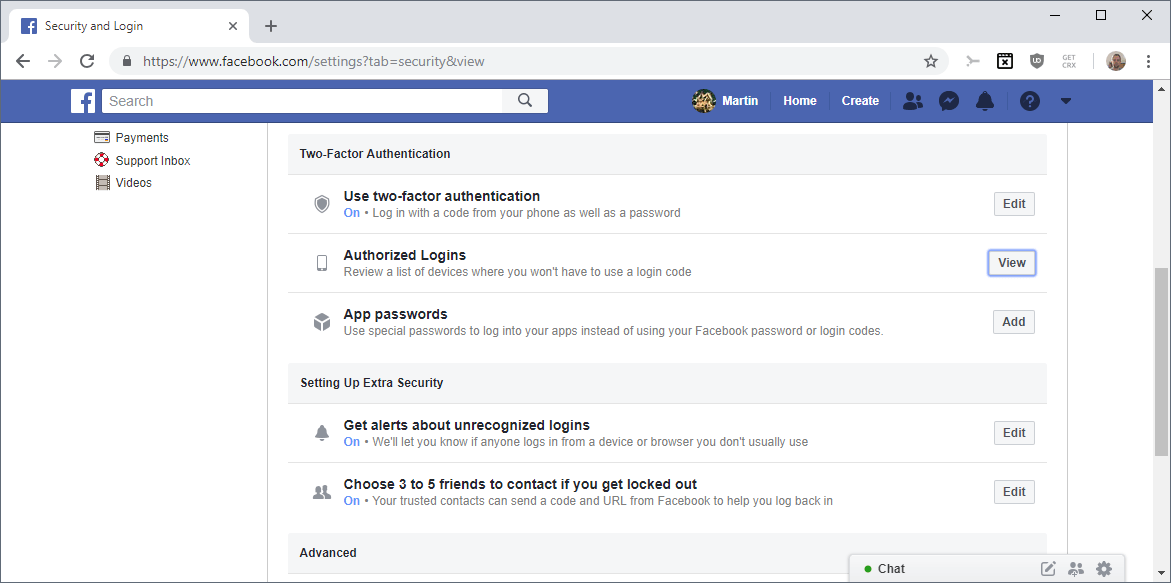
Facebook supports options to better secure an account.
- Get Alerts about unrecognized logins -- Facebook notifies you when it notices logins from devices or browsers that you have not used in the past. Make sure that this is on.
- Authorized Logins -- Check the list of devices where you won't have to use a login code. Remove any device or browser on the list that you don't use anymore or don't have access to.
- Two-factor authentication -- Adds an extra layer of protection to the account. It was discovered recently, however, that Facebook will use the phone number for advertising purposes (advertisers upload lists of phone numbers, and if your phone number is on that list, you will be served ads from that advertiser).
You may also want to be extra careful when it comes to emails or phone calls if you have been affected by the issue. If attackers gained access to the account, they had access to emails, your name, and other personal information that they might use in target phishing or social engineering attacks.




















Great post! Some new developments on this story too.
Facebook banned a ton of ad accounts last night, which is great for the platform and legitimate advertisers. Now, Facebook has always shut down or flat out banned ad accounts for breaking their Terms of Service (TOS). That said, it’s usually auto triggered based on ad disapprovals (sexual, before/after pics, etc)
This wave of shut downs is different.
They do massive shut downs like this periodically, including the last one in August, but nobody I’ve spoken with at Facebook has told me why it’s happening now.
One theory is that they’ve ramped up these massive shut downs because the election is coming up. But having worked with publishers, patriotic brands, and talking to folks who work on political ads, I don’t think this is true.
The next theory is that Facebook really is putting more of an effort into kicking bad actors off their platform, and I think this is true.
This site is a treasure trove of privacy techniques. From command prompt scripts to VPN and DNS info, this site does not lack in knowledge.
I’m a Redneck from TX who thinks the Anon who posted his U.S. Kommie Party, antifa leanings is a disgrace…Announcing to the whole western world how he’d like to twist off is even more bizarre…He should be apologizing to Mr Martin and asking for forgiveness.
What Facebook?
I deleted it since the data breach. I get a lot of Facebook ads everywhere, trying to get me back, but I refuse to rejoin! 🌚
Once you break my trust, you don’t get another chance. Ask my ex. ðŸ˜
I’d be happy to leave FB but the Groups feature is one thing that keeps me there and can’t be replicated on other platforms for various reasons…
Facebook is like alcohol, if you can not use it responsibly, then you should not use it at all.
What’s with the political “experts” posting here? It’s not like fb’s or google’s advertising or linking works but it does seem great at pointing manic posters to irrelevant sites. Can we get diatribes from Togo by trolls who clearly don’t have a clue?
Back OT: Don’t ever give your phone number for two factor authentication. How can something so easy to obtain increase security? It’s a ruse. Tiny phone screens trick users into false trust; the same requests on a gigantic monitor would look huge and scary!
Glad I never used Foolbook…
When celebrities, journalists, bloggers, vendors, shopping websites, talking heads, sports commentators, TV personalities – do I need to go on? stop using Facebook, it will no longer be what it is today. It flourishes because these people use Facebook as a business generating platform. It is a gauge on their relevance and/or popularity. I think their masters insist on them having this presence so they can determine who is in and who should be eliminated. The content or substance of their work is no longer the yard stick. The loudest and most obnoxious more often get the most action. This is not how a healthy society can sustain itself.
The kids have moved on to other platforms but not because kids are better informed, but because the action is more their style somewhere else. The most alarming scenario is that FB is moving more into ‘business services’. Trust them anyone?
Congress can not regulate FB with any modicum of competence. Look at how our utilities are regulated. It could not be more corrupt. Just delete your personal FB account and be done with them. Don’t read FB news feeds or use FB Fin apps.
@Leo: “When celebrities, journalists, bloggers, vendors, shopping websites, talking heads, sports commentators, TV personalities – do I need to go on? stop using Facebook, it will no longer be what it is today.”
True, but Facebook is already losing the most important people in terms of maintaining relevance: the youth. Kids today generally view Facebook as a place for companies and old farts, not a place for them, and Facebook is constantly losing users of that generation. Once that starts happening, it’s the beginning of the end.
Sadly, though, Facebook saw that coming — and that’s why they bought the social media that the kids today actually are using (WhatsApp, Instagram, etc.), and do their best to not tip them off that it’s still Facebook.
Facebook is an entire mess and imho this company should be restricted as soon as possible.
Political comments on Ghacks, humans are hilarious.
I still have facebook, the info on it is sparse and barely revealing, other than my real name and a few pics, likes that can ‘identify’ me there is nothing there. The bigger issue than actually being on FB is the trackers, cookies, etc. that follow me.
Stop making Zuckerberg and his family obscenely rich: delete Facebook, Whatsapp, and Instagram (and any other company they suck into their black hole). They exist only to exploit people and they don’t give a damn about any person or any law.
LOL at the idiot claiming Russia is the problem and not the completely batshit left. I’ll never vote for another democrat in my life. I don’t want a war with leftards, but it seems they’re hell bent on getting one. This redneck voted for Trump and will vote for him again in 2020. For the record, I deleted fakebook too. But not because of MUH Russia, I realized it’s harvesting my personal information and I want my privacy back.
I deleted my Facebook account in 2016, after I saw that users were falling for that Russian Bullshit, which allowed the Trump Rednecks, to get a their fascist moron leader elected. Now we have a Fascist Pig named Trump, that is well on his way to destroying Democracy in the United States, and Trump rednecks that want to start a war with the rest of us US citizens and kill us, with guns. I have been threatened more than once, by these assholes in various stores and even in Mc Donalds. Now that I have a gun, bring it on assholes!
…and
Thanks Facebook, you piece of shit!
@ another “Anonymous” coward
Well Done!
You have skipped retard and gone straight to potato.
Your assumed cause and effect is almost completely wrong but combined with paranoid BS it’s morbidly amusing.
Yeah, fb sucks and never will be under control any more than autonomous cars will be. Both will be hacked forever. Only takes once if you’re the target.
@ Anon
I think you forgot one “asshole” an two “shits”. There aren’t enough in your comment.
Also, I don’t believe for a second you were threatened with a gun in stores and McDonalds in America because you didn’t like Trump. I also don’t believe you acquired a gun license, bought a gun and are willing to draw it in a store if someone recklessly (and probably illegally) draws a legal gun at you for no reason at all.
Also, this is a German website, so your wet dreams about “Trump morons” and guns in McDonalds are completely irrelevant.
Because America never sticks their nose in where it’s not wanted do they? Sounds like you’re still butt hurt that the stupid people didn’t vote the same way as you.
inb4 this mentally unstable individual becomes the next mass shooter
Keep an eye on liveleak, guys.
Right? I’m not even American but I saw Russians pretending to be American plenty of times (I had a few Russian friends elsewhere and can recognize their way of using English, and the expressions, mentality, mistakes and even insults they use – even blindfolded). Still, there’s no point in deserting the battlefield. There were a few posting here too (Cheers “Alex”).
Absolutely everyone know all the bad things about Facebook, not just their regular intentional/unintentional breaches of user data. So if someone chooses to stay on, despite all of that, then their faux outrage and fury when the next bad thing happens can safely be ignored as they’ve shown that they don’t really care.
This line of reasoning is deeply flawed morally.
People should just stop using facebook altogether… it’s high time already.
What you should do after Facebook confessed they are using 2FA cellular number for spamming users with ads ?
Switch to Diaspora.
https://alternativeto.net/software/diaspora/
I think older people (40+) have more difficulty leaving facebook than younger people because they don’t understand the threat and generally old people don’t like change so they stick with it.
And *other* older people are crotchety and suspicious, smell a rat from the outset, and never open an account in the first place! Not that I’d know anyone like that personally, or course… ;-)
That would be me. My attitude is that people who are stupid enough to post personal info online deserve anything they get.
This misuse of user data is getting beyond a joke and your phone number especially should be sacrosanct. To have it used to bombard you with ads when all you thought you were doing was to provide it for two-factor authentication purposes is reprehensible.
I closed my own FB account back in 2012, but for some people, social media has become an addiction which they find difficult if not impossible to quit.
Using facebook feels like being naked in the middle of a crowded city. I don’t know who likes this website, I find it horrible and hostile. “Secret” is a word which Zuckerberg has not learned.
This is unfair, people should pay Facebook to get these data, not have it for free !
They do pay – indirectly. The way FB advertising works, is that nobody knows specifically about you, as all they can do is create an “audience” – it is FB that determines if you fit that audience and then targets the ad towards your timeline feed. If FB didn’t have the audience feature, then FB’s whole advertising model would be broken.
No doubt many would cheer at that – except those cheering now would harbor similar complaints about the next social media platform, as FB “sucks” and became irrelevant, while that other one thrives with new features and updates that keeps “everyone” using it.
Anyone who hasn’t already deleted their FB account by now is a fool.
I intend to (gently) suggest to my friends that they should leave this abusive relationship.