Google: Microsoft's focus on Windows 10 puts Windows 7 and 8 users at risk
Microsoft's focus on Windows 10 in regards to security puts users who run devices with older but still supported versions of Windows at risk according to Google Project Zero researcher Mateusz Jurczyk.
The researcher noticed that previous versions of Windows -- Windows 7 and 8.1 to be precise -- were affected by the vulnerability described as Windows Kernel pool memory disclosure in win32k!NtGdiGetGlyphOutline whereas Windows 10 was not.
Microsoft fixed the issue on Windows 10, while it did not patch it on older versions of Windows. Microsoft added a memset to Windows 10 which prevented the information disclosure on the operating system.
This suggests, according to Jurczyk, that Microsoft identified the issue internally and fixed it on Windows 10, but not on Windows 7 or 8.1.
The vulnerability came to light in 2017 when it was revealed publicly. Microsoft fixed the issue on the September 2017 Patch Day for affected operating systems.
The question that came to Jurczyk mind after discovering that the issue affected only previous versions of Windows was how widespread the issue was.
He used binary diffing, a method to reveal differences between different versions of a single product for that, and analyzed the Windows files ntkrnlpa.exe, win32k.sys, ntoskrnl.exe, tm.sys, win32kbase.sys and win32kfull.sys.
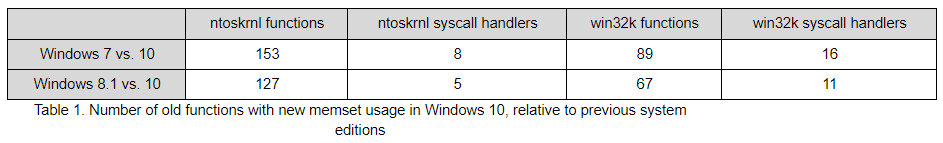
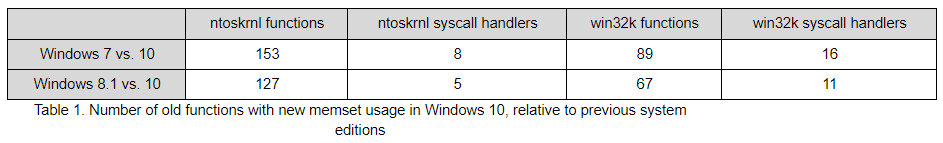
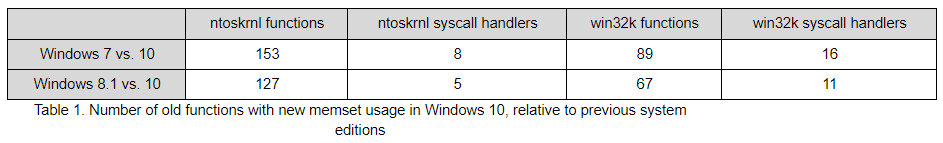
He discovered a large number of differences between Windows 7 and 10, and Windows 8.1 and 10. Windows 7 being the older operating system (compared to Windows 8.1), had more differences when compared to Windows 10 as Windows 8.1.
Quite intuitively, the Windows 7/10 comparison yielded more differences than the Windows 8.1/10 one, as the system progressively evolved from one version to the next. It's also interesting to see that the graphical subsystem had fewer changes detected in general, but more than the core kernel specifically in the syscall handlers.
Google started to investigate these differences and found two new vulnerabilities in the process (the two vulnerabilities that were addressed in the September 2017 Patch Day).
Jurczyk concludes that the focus on patching only the most recent version of a product, in Microsoft's case Windows 10, may be used by malicious actors to find vulnerabilities in older versions of a product.
Not only does it leave some customers exposed to attacks, but it also visibly reveals what the attack vectors are, which works directly against user security. This is especially true for bug classes with obvious fixes, such as kernel memory disclosure and the added memset calls.
Closing Words
Microsoft's focus on Windows 10 is quite problematic from a security point of view, considering that all three versions of Windows are still supported by Microsoft, and that Windows 8.1 is still in mainstream support.
This is something that Windows users and administrators unfortunately cannot do much about (other than upgrade to Windows 10). (via Born and Bleeping Computer)



















At this point, pretty much everyone knows that kind of things Microsoft is up to and whether or not Windows 10 is a good product. The question is how strongly do you feel about how they are behaving. Can you excuse this and support them by “upgrading” to Windows 10 anyway or is it a matter of principles for you so you steadfastly remain with Windows 7 or 8.1? Remember that if you blindly support them by using their product that makes them ad revenue from Cortana, Edge and other crap, you are leaving them with no incentive to make things actually better for the future.
Personally for me, I’m very happy with Windows 8.1 and Classic Shell. The system is lean, doesn’t bloat my disk, and is very stable, fast and highly tweaked. Updates do not change or unravel any of my optimizations like they do on Windows 10. It has no annoyances and does not require a constant vigil, no shock surprises to learn what the next big bloated huge update is going to do to it, what next policy change is going to affect me. None of that rebooting forcibly while I am doing my work too on Windows 8.1 or 7.
You know an operating system is bad when:
a. in 2015, MS found that it couldn’t even give Win 10 away for *free*, so it resorted to installing malware and trickery on Win 7 systems to force the upgrade.
b. Win 10 is so awful and troublesome, that it even makes Win 8 look good!
That’s because Windows 8 IS good. If you guys would try it, disable the Start screen and metro crap, and use Classic Shell, you’d end up with a flatter, faster Windows 7. Then add a transparent 7-like skin to get Windows 7’s feel and look back.
The best thing is, no telemetry – and with the use of Server 2012 updates, you’re golden until October 2023.
:)
You know an operating system is bad when:
(c) It makes a tired, old, lazy, habit-encrusted, change-averse Windows user who now finds mastering new software more tedious than exciting decide to switch to Linux.
“other than upgrade to Windows 10” or ditch microsoft windows.
“Still wondering why people worship Windows 7 so much.”
It’s sort of like the difference between driving your car and taking the bus.
Microsoft: If they don’t convert from a Windows USER to a Windows CONSUMER; we better punish them!
This world is so evil. Oh God, give me some nice pigeons to send emails n stuff. :(
Mr. Gates will soon announce to the world he has abandoned Windows (10) and switched to Linux already, just like he is now using android phone instead of wp.
I’m glad to see this story making rounds in the media. Microsoft made their commitment to customers quite clear when they blocked Ryzen users from critical updates on Windows 8.1, which is still in mainstream support.
But the problem with this business strategy is that (if you aren’t going to honor the support terms for the product you already sold me), I would be silly to think that you will honor them for the new one that you now want to sell me!
Still wondering why people worship Windows 7 so much. They did the SAME thing with XP. Let it go already!!
I find a properly configured firewall saves lots of pain on win/mac/and lin tiny wall ftw
The whining never ends, I bet there still Win2k users out there.
Win2k users?
HA! You have no idea how many are still using Windows 98 http://www.majorgeeks.com/files/details/unofficial_windows98_se_service_pack.html
So what ? People whine about different things. It’s none of your business, just take care of your own little kitchen world.
Google’s Hypocrisy.
“Jurczyk concludes that the focus on patching only the most recent version of a product, in Microsoft’s case Windows 10, may be used by malicious actors to find vulnerabilities in older versions of a product.”
Jurczyk did not conclude that the focus on patching only the most recent version of a product, in Google’s case Android Oreo, While KitKat used by 14.5% of Android users, Lollipop by 28%, Marshmallow by 32%, Nougat by 18% , while Oreo has only 0.2%, may be used by malicious actors to find vulnerabilities in older versions of a product.
Martin–more misinformation and not what the authors of the linked articles even consider as a deliberate attempt by Microsoft to, once again, in some way, persuade users that Windows 10 is more secure:
1. Bleeping – “Other software vendors may be affected; while confirmed with Windows, the issue of inconsistent patching most likely affects other vendors with large software portfolios, such as Oracle, Linux, Cisco, and others.
a) Comment – “Sounds like a valid argument: if you patch a cross version vulnerability, in Win10, without the same for 7 or 8.1, you create a zero-day for the older versions (if I understand it correctly).”
Possible solution – EMET or Malwarebytes Anti-Exploit
2. Born/Comment – “It sounds rather as if Microsoft would build some routines as part of the normal development for Windows 10, without being aware that there were gaps in the older routines in older versions of Windows . . . That one deliberately clear gaps in only one system, and leave open in others, sounds a little very far fetched. Why should you do this if you continue the older systems for years anyway? The fact that sooner or later users notice must be obvious to everyone. So no one is so stupid, and makes something deliberate.”
3. Dr. Windows Interpretation – “It is also important how Microsoft describes these three gaps: An attacker must log on to a PC with valid credentials and run a prepared file to exploit the vulnerability. A direct attack on the system is not possible, however, the spied information could be helpful to carry out further attacks. The degree of probability that this gap will be exploited is indicated by Microsoft as ‘low’.”
Dr. Windows [the real Martin]
“My interpretation, which of course does not have to be followed, is [the following]:
The idea that a fever-grilling Windows developer closes a gap in Windows 10 to leave it open in Windows 7 and 8 may fit into the world of the Zwangsupdate conspiracy theorists, but I think this is unlikely. The current case, I guess so that the corresponding routines for Windows 10 have been optimized. Microsoft probably did not know that these components were not only less efficient but also potentially unsafe in older versions of Windows. In this case you can, of course, be accused of not being aware of it earlier – the accusation that people of older versions deliberately expose security risks, but then I consider them to be too far-fetched.”
from “Google Trolls: Windows 10 threatens security of older versions of Windows”
Martin, not to be confused with the writer at Dr. Windows, promotes more and more conspiracy theories either to promote his own Ãœbermensch agenda–the greater the lie, the more will believe.
Compadre, ¿por qué continúas creando ilusiones en la mente de tus lectores en lugar de promover un excelente periodismo y un pensamiento profundo?
How could they not know? Are they that incompetent?
Maybe they should fire their Hindoo-1B’s and hire American programmers.
Microsoft’s definition of “supported” now seems somewhat questionable.
…..other than upgrade to Windows 10
Which is exactly what MS wants. They have to stop their aggressive “persuasion” tactics, but they still have the initiative, which they are making full use of & making people feel it.
This happens when companies get too big and powerful. Only way to fight this in regard to MS is to change systems and hit them where they feel it. Unfortunately, Linux is too disorganized & chaotic to take advantage of the situation. Linux needs to start trying to understand the lazy minds of windows users to make them switch.
So dumping bucket loads of telemetry spyware on Windows 7 and 8.1 users ( https://www.ghacks.net/2017/02/11/blocking-telemetry-in-windows-7-and-8-1/ ) isn’t enough for Microsoft and they now want to put these systems at risk of hacking by not patching the same vulnerabilities that Windows 10 enjoys. How low can you go Microsoft?
Seems M$ have broken their 10-year support agreements with their users after having collected US$billions from them for the sale of Win 7/8.x licenses, ie by purposely patching only Win 10 and not patching Win 7/8.1, in order to push Win 7/8.1 users onto the Win 10 bandwagon = users have to pay more money to M$ for Win 10 licenses or yearly subscriptions.
……. This may be similar to bait-and-switch sales tactics by unscrupulous companies. This kind of things did not happen to Win XP/Vista.
_ _ _ _ _ _ _
The compulsory twice-yearly Win 10 upgrades is likely designed by M$ to make 4 to 5 years old computers obsolete prematurely by blocking Windows Update, eg when the OEMs will refuse to provide new device drivers for the latest Version of Win 10 and its new features(eg devices for virtual reality).
……. IOW, if you buy a new OEM Win 10 Version 1703 computer today, it may become obsolete in 2021, ie your computer will be blocked by M$ from being upgraded to Win 10 Version 2103 or 2109 through Windows Update(eg processor-blocking) = your 2017 computer cannot be used for about 10 years until 2027 or 2025/EOL, like before with Win 7/8.1(= 2020/2023 EOL).
Fortunately, as an average user, I was able to move from Win 7 to Linux Mint 17.3 Cinnamon in Aug 2016, ie after M$ began crippling Windows Update for Win 7/8.1 in April 2016, eg those who reinstall Win 7/8.1 could not update through Windows Update.
……. “Miraculously”, this updating problem disappeared in Jan 2017, ie soon after M$ imposed compulsory monthly Patch Rollups for Win 7/8.1 in Oct 2016. Likely, those cumulative Patches have hidden updates, eg Win 10-spyware.
Most business users are locked into Windows because their software and hardware(eg device drivers for printers and scanners) are only available for Windows or Macs.
I happen to be using the very same Linux Mint version alongside Windows 8.1 (which for a few things, alas, still is the easier option).
You’re probably right in noting that switching to Linux would be more difficult for business users.
But what Martin said in his post here, quote, “This is something that Windows users and administrators unfortunately cannot do much about (other than upgrade to Windows 10)” is not quite true for home users. In most situations in everyday home use, Linux is already a usable alternative.
MS has forgotten a cardinal rule of business: never give a paying customer a reason to stop doing business with you. As one salesman told me many years ago, it is far cheaper to retain an existing customer than it is to get new ones. Any regular or semi-regular customer is someone who is already willing to spend money with you – do not run them off.
Users considering switching or switching to Macs or Linux are permanently lost. They will not forget why they left even if MS reforms itself.
With businesses, one should be careful about the size. Many SMBs can get by with more or less generic software readily available on Linux and Macs (some comes preinstalled) or in the cloud.
> This is something that Windows users and administrators unfortunately cannot do much about (other than upgrade to Windows 10)
And that’s exactly what MS is doing here, pushing Windows 10 to their (mostly) Enterprise customers because hey look Windows 7 is reaching an EOL state in 2 years and is “less” secure than our super duper latest and greatest OS.
On a personal level i’ll stay with W7 even after the EOL the problem however is not so much the unsupported OS (assuming we won’t have another POSReady* registry hack) that i care but the lack of software updates, as we saw recently with Vista Google Chrome dropped the support immediately for this OS and Mozilla is planning to do the same with Firefox next year.
(*) Windows Embedded Standard 7 EOL is July 27, 2025
http://blogs.directinsight.co.uk/end-of-life-dates-for-windows-embedded-products-2/
Micro$oft’s obsession with having their users on Winblows 10, more like.. So desperately that they are now sabotaging their own operating systems. Happy that Google called them out on this one.
Haha, Winblows 10, couldn’t have said it better. Winsucks 10 also works, but doesn’t roll that well off the tongue. xD
Windows 10 is a mess just like Windows 8 was, except they sort of got it together a little, but not enough for me to abandon the stability, consistence and superb user experience of Windows 7.
Windows 7 was the peak of the Windows operating system, after that it went downhill. Looking at how Microsoft spends resources on making the Winblows 10 mascot a Ninja Cat riding on the back of a T-REX… it really begs the question “Are they that stupid they think this is cool, or they are testing the patience of people and see how stupid THEY are?”
But the fact that Google called them out won’t change a thing, M$ know they screwed up and they know that 10 sucks major balls, but they will still come out with some stupid statement and downplay this and continue on the same path.
@Wellan:
Why don’t you educate yourself and learn to read – you biased twit!
I never defended Windows 10. I was defending Windows 8, which yes has Metro, but most of that can be rooted out, and Windows 8 becomes a more stable Windows 7. I also hate Windows 10, but Windows 8 is a very stable, rock-solid OS.
@Jody Thornton:
You should educate yourself, because apparently you don’t know anything about how Windows 10 works.
The Metro stuff is deeply integrated within and can’t be completely hidden or disabled. First off you have the Settings app, where many important settings are, second, the ClassicShell you mentioned doesn’t work properly anymore with the latest builds of Windows 10. All 3rd party start menu programs don’t work properly anymore for that matter, namely searching within Settings doesn’t work at all and none of those 3rd party programs have been able to bypass this.
I’ve used Windows 10 since August 2015 up to August 2016 when the Anniversary update came and it started annoying me and made me feel like I’m no longer in control of my computer so I went back to Windows 7, over time I tried giving Windows 10 a few more chances, because I was originally very excited about it, but it never worked out – the same stupid issues with restricting me access to certain tweaks or resetting settings on restart or update, all coming from that Metro crap have lead me to stick to Windows 7 and think about moving to Linux when Windows 7 is no longer supported by major programs, like Firefox, Chrome, etc.
The most part of the taskbar in Windows 10 is part of this Metro thing, namely the start button, the notifications, clock, volume, network and all the other icons. I’ve been testing things by deleting whole portions of Metro files in the C:\WINDOWS\ folder to see what exactly breaks and at one point the taskbar (except for the pinned items) completely stops functioning. In previous versions of Windows (think XP-7) you could delete a lot more system files and the version of Windows will still work. This goes to show how unstable Windows 10 is.
In the notion of the taskbar being made out of Metro, this means that using sometihng like UXTheme Patcher to allow you to use 3rd party themes, no longer works as it used to on Windows 10. The taskbar ALWAYS stays the same, window title bar still changes, but it looks so half-assed it’s not even worth it. Here’s a screenshot of how “well” a 3rd party theme “works” on Windows 10: http://downloadpack.net/skin_pack/uxtheme/ux10.png
It’s not about customizing your OS, but it’s about the principle. The principle of having the freedom to do what you want with what you spend your money on. And since Windows 8, The Windows OS has become more and more restricted with each version, until it comes to the point of an iPhone – where you need to install an app so you can change your wallpaper with a 3rd party wallpaper, in case of Windwos 10 Potential Future Update – take your computer to a technician and pay him to change your wallpaper for you, because you are a regular Joe and don’t know what Regedit is (because that’s the only way to change it).
So please take your Windows 10 fanboyism someplace else, you have nothing to say that can justify Windows 10. It may have DX12 and some other neat additions, but these mean nothing to me, even when I play new games, I turn down the visuals to the lowest, because I don’t like how realistic games look, it’s distracting, it’s scary and they don’t look like games anymore.
Windows 10 is a beta that nobody knows when it will reach Official Release and the price tag is the early access paywall.
Sheesh! This Windows h-8 you keep spouting is misinformation. Nix metro stuff and put on Classic shell as a Start Menu replacement, and you have a more stable Windows 7 – period!
Shit all over Winblows 10 all you like, but educate yourself on Windows 8 before you comment.
Because Google is going a good job at protecting its Android users with updates?
@ Kevin:
To my mind, both sealed, non-user-replaceable batteries and failure to provide security updates throughout the reasonable objective lifetime of the device are part of a strategy of planned obsolescence. But GPDC (Got Paid, Don’t Care) describes it pretty well. I’m looking forward to the day the EU mandates user-replaceable batteries and security updates, because I know to a certainty that no institution in the corporate-captured US is going to.
This is not the fault of Google though. Google publishes the Android code freely. The problem is the phone manufacturers and the carriers who sell people locked down phones. Their approach to security in general is GPDC. That stands for “got paid, don’t care”
Phone carriers and manufacturers don’t want you to be able to update the phone that they sold you last year, because they want to sell you this year’s model. But, if you get a standard X86 tablet or a phone with an unlocked boot loader, you are free to install the latest version of Android on it.
@ AnorKnee Merce:
I know very little about cell phone OSes, but several days ago I read that support for Linux LTS kernels (starting with 4.4, I think) had just been officially extended from two years to six years. The article said this was a big deal for Android because it would make it much easier and cheaper for OEMs and carriers to provide security updates to older Android phones. It makes sense to me (as a cell-phone-OS ignoramus), but we’ll see whether Android phone vendors actually start taking their duty to provide security updates as seriously as Apple does.
@ Levi,
Even though it is Google who issue security updates and OS upgrades for Android mobile devices, the onus for providing the updates/upgrades rests on the OEMs. Google’s Nexus and Pixel devices, and OEM-Chromebooks/Chromeboxes get the latest security updates and upgrades.
Most of the OEMs refused to update and upgrade their Android devices because they wanna make more money through Planned Obsolescence.
Buy Pixel Phone or Nokia >> for fast updates >>>
idgaf about Android, or any other mobile OS for that matter. The only good one, Symbian, is dead, and the remaining ones are trash.