CCleaner 5.35 released with new digital signature
Piriform, the company behind the highly successful Windows cleaning software CCleaner, released version 5.35 of the application on September 20th, 2017.
The new version was signed with a brand new digital signature, the only change of the release.
The company's infrastructure was attacked successfully recently, and a modified signed version of CCleaner was distributed for a time using the official distribution channels.
According to information provided by Piriform and Avast, Piriform's parent company, the malware was contained only in the CCleaner program. The company states that the malware did not spread on its own, for instance to infect other files on the computer system, a computer network the device was connected to at the time, or even on the Internet.
The company released a malware-free version of CCleaner, version 5.34 on September 12th, 2017. The new version overwrites the old if installed on the system, which in turn would eliminate the malware by doing so according to the company.
Cautious users may want to restore a backup of the system that was created prior to the update of the software to version 5.34 on the system.
The free version of CCleaner does not support automatic updates which means that users who run the free version of the software need to download the latest version manually to update the build.
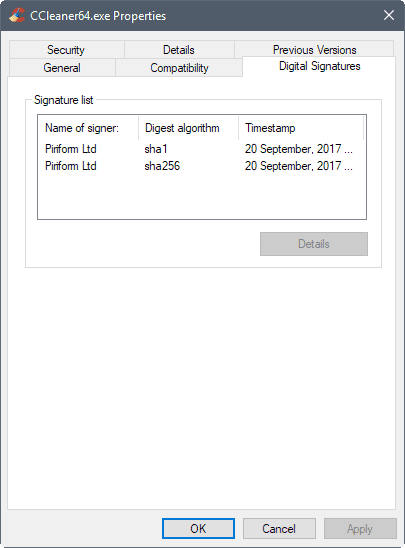
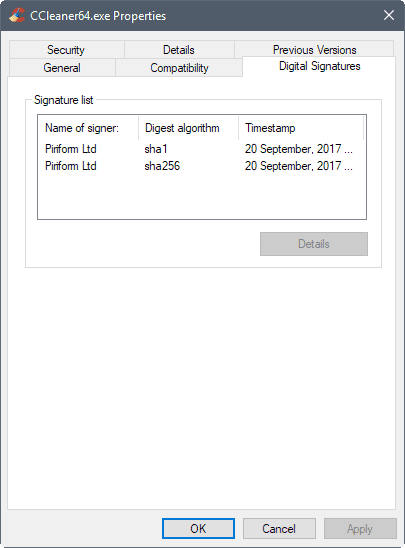
The new CCleaner 5.35 version comes with a new digital signature. This is different from version 5.34 which was shipped with the old digital signature which the compromised version of CCleaner did use as well.
You can verify that a new digital signature is used in the following way:
- Open the folder that the CCleaner executable files are located in.
- Right-click on ccleaner.exe or ccleaner64.exe, and select properties from the context menu.
- Switch to the digital signatures tab.
You should see September 20th, 2017 as the timestamp, and Piriform Ltd as the signer.
CCleaner users may download the portable version or the installer of CCleaner 5.35 from Piriform's Build page.
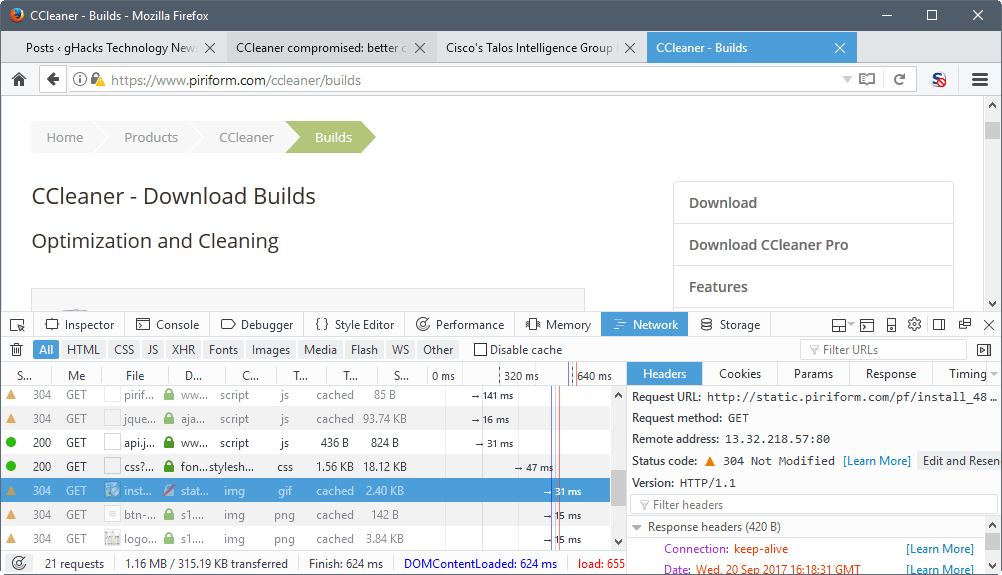
Please note that the connection comes up as "not secure" right now. This is caused by an image resource being loaded from a HTTP source instead of a HTTPS source.
Now You: Were you affected by this? What have you done so far?


















for the users with a 64 bit system, when you download the “Ccleaner” installer program, sure it will be detected as a trojan, because it has both the 32bit and 64bit version of Ccleaner rolled into one .EXE installer ,
Ccleaner 5.34 .EXE will have both 32bit and 64bit as well.
including the stand-alone version of Ccleaner 5.35 that was given all new signatures .
what piriform has to do is not put two into one .EXE.
they should have two download link/options.
one 32BIT and one 64BIT, from here on out . i dont know why they dont do it this way, most other software programs have that option.
this is not the only company that this has happened too, they fixed the problem, now alls they have to do is give two download options.
“what piriform has to do is not put two into one .EXE.”
I noticed this after installing CCleaner 5.35 when it became available and then looking around for what and how it was done. I was surprised at the sloppy design of including x32 and x64 in the same download. I imagine it would be a slight hack to make x32 install regardless of an x32 or x64 machine identity.
I’ve got the Pro version of CCleaner, and My digital time stamp is 7th September for version 5.34.
I never run the CCleaner installation, I used 7-Zip to extract the files, CCleaner is basically portable. Also the proversion updates directly from the program so no manually downloading required.
It doesn’t cleanup the mess the version 5.33 created?
Im not so sure if 64bit systems werent affected. Because my antivirus still flagged the exe having a virus in it on my 64bit system. If they werent targetted surely it wouldnt flag.
Well my geeky faith was not shaken. I went over to mostly portable stuff anyway, and that includes CCleaner, x64 version.
I don’t think that people should use this news as a reason to get rid of what is a good utility. Alright so they fell down, who doesn’t? who won’t?
Just get v535 and go about your business like always. There are too many people getting hysterical about this, and ultimately what it adds up to, is that we’ve all given some tech sites a lot of baity clicks. : )
In all the years I have used ccleaner never once had a problem with it. I have helped setup many a pc with ccleaner being one of only a few programs I would always suggest. What happened here, with a piece of software so widely used, it was inevitable. Some what surprised it hasnt happened sooner. I am very thankful to piriform not only for ccleaner but speccy, recuva and defraggler too, Ive used them all on occasion.
Anyhow thats my 2 cents.
If you have the CCleaner 5.33 your computer is infected. I have scan my computer with Malwarebytes antimalware and have detected a trojan. I have uninstalled CCleaner.
Got the new update today on the Professional version.
Thanks for the heads-up Martin.
Put me down as not panicked but taking some precautions.
Found it before reading the information release using the VirusTotal option of Mark Russinovitch’s Autoruns.
Uninstalled immediately. Noted that VirusTotal listed Malwarebytes as 1 of 8 who currently lised the infection. Ran Malwarebytes to find no further infections. Uninstalled Cloud programs (but kept directories) to reduce the chance any undetected insertion will infect my 2nd PC (Win 64). Keeping up with the reading but reasonably confident that Avast doesn’t want to lose a fortune on CCleaner and will not have told users all is clear unless they were very sure that is the case. I plan to regularly run secondary scanners and keep up the reading. Will reinstall cloud programs in a month or two. Alternately, if Windows update keeps crashing on KB4038788, (failed 10 times before setting connection as ‘metered’) Imay ground zero the device and start again.
Noted later that Windows Defender was late on the list of VirusTotal’s detectors. I may move this box to Kaspersky insted of staying with Defender.
so like i had the 5.33 on my computer but i was 64-bit windows 7. am i fine? i ran a malwarebytes scan + norton scan and both came up with nothing.
You are fine as long as it was the 64 bit version of CCleaner if you installed the 32 bit version (which you can do even though you have a 64 bit operating system) then you’re in trouble. There are plenty of guides telling you how to check which version you have installed.
x64 Windows systems weren’t affected by that problem, Justin.
Good to hear, thanks satrow.
The weeping about something you could simply have avoided by blocking the program with your firewall. Damn … There is no reason to switch to another service or program just because it got compromised, you really that naive to believe that this can’t be happen with other programs? Oh my …. but go on weep more *popcorn*.
Bleachbit is not an alternative it doesn’t come with basic features like tray icon, or the fact that it cleans your leftovers after you close the browser and 100 other missing features. It’s more comparable with a .bat which cleans specific areas but it can’t compared with the ccleaner, since it’s more an all in one tool now.
How would a firewall have helped if the official program initiated an auto-update and the user had no reason to doubt the quality of the updated file? Unless you always wait (for how long) to see if something bad is happening (more likely due to one software interacting with another one), then any firewall or hips alert would have been allowed.
Where is your github project?
My GitHub page and all my projects and gists are on hold till I removed all the things which the GitHub bot complained about.
Maybe back online next week, I need to review 2k+ gists manually.
I know all companies are to a greater or lesser extent vulnerable to a hack. But we trust CC with the very core of our PC or laptop. That means they know everything. This hack feels like a huge violation. I uninstalled CC immediately. Sorry, but I doubt any kind of remedy or apology can get me back. That’s just the price you pay for getting hacked I fear – I just can’t trust CC ever again. Sure there are going to be others who will use statistics to explain how it could happen to anyone and even credit rating firms have this issue. But this feels very personal because I let this company into the very depths of my PC. Now that trust has gone.
You’re worried about a compromise that exposed very little information. Most of it is already publically available. If the hack had further evil intentions, they were blocked before they had a chance to do any real harm.
You should be outraged about the recent hack of Equifax where critical information was harvested for almost half of the people in the US.
Not quite accurate – although Avast are still saying there was no further infection, the analysis by Talos indicates that it was a selective secondary infection.
http://blog.talosintelligence.com/2017/09/ccleaner-c2-concern.html
For me it’s too late, I did a clean install on my box yesterday and I don’t intend to install CCleaner anymore. I don’t trust in Avast.
It’s a shame because I liked the program, although it was fucking up the favicon bookmarks on Firefox lately so, it was not doing any good anyway…
I will just use the Disk Cleanup from Windows for now on and maybe test the BleachBit in the future.
you lost me .. bleachbit seems ok , whats a few other free good ones?
Wise Care 365 is good.
System ninja perhaps
All other alternatives suck unfortunately, and also people are kidding themselves if they think something like this can’t happen to those other alternatives…. remember Classic Shell/Start Menu & Audacity destroying MBR? Yeah their host was compromised, and being “small time” things like this will just go unnoticed for even longer.