Firefox WebExtensions may be used to identify you on the Internet
All modern web browsers leak extension information to sites if the sites run scripts to pull the information. We talked about the findings of a research term that published its findings recently in a paper.
Unless scripts are blocked, sites may run scripts that check the response time of the browser as it is different when checks are made for fake extensions and fake resources, and existing extensions and fake resources.
Firefox's situation is special, as it supports the legacy add-on system and the new WebExtensions system. The researcher tested the browser's legacy add-on system only, but suggested that Firefox's new system would also be vulnerable.
An anonymous reader pointed out that Firefox's WebExtensions system uses random IDs, and that this meant that the method to enumerate extensions would not work in that case (unlike in Chrome and other Chromium based browsers).
While that is correct, Mozilla's implementation introduces a new issue that allows sites to identify users if WebExtensions expose content to sites as the random IDs are permanent.
"... in particular, they [Mozilla] changed the initial scheme (moz-extension://[extID]/[path]) to moz-extension://[random-UUID]/[path]. Unfortunately, while this change makes indeed more difficult to enumerate user extensions, it introduces a far more dangerous problem. In fact, the random-UUID token can now be used to precisely fingerprint users if it is leaked by an extensions. A website can retrieve this UUID and use it to uniquely identify the user, as once it is generated the random ID never changes. We reported this design-related bug to Firefox developers as well."
If a site manages to get hold of the ID, it may track the Firefox installation as that ID never changes.
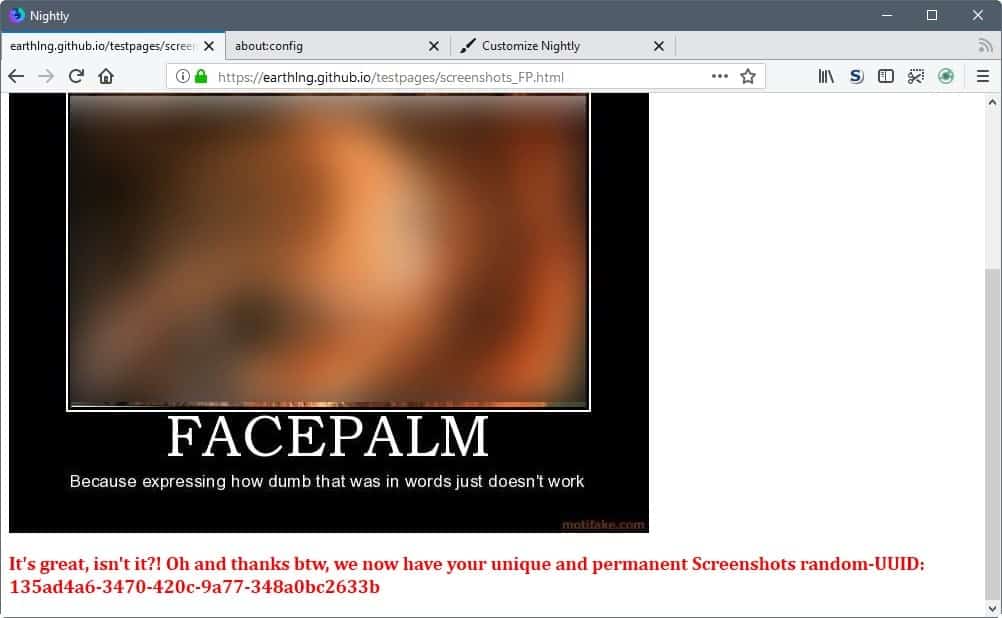
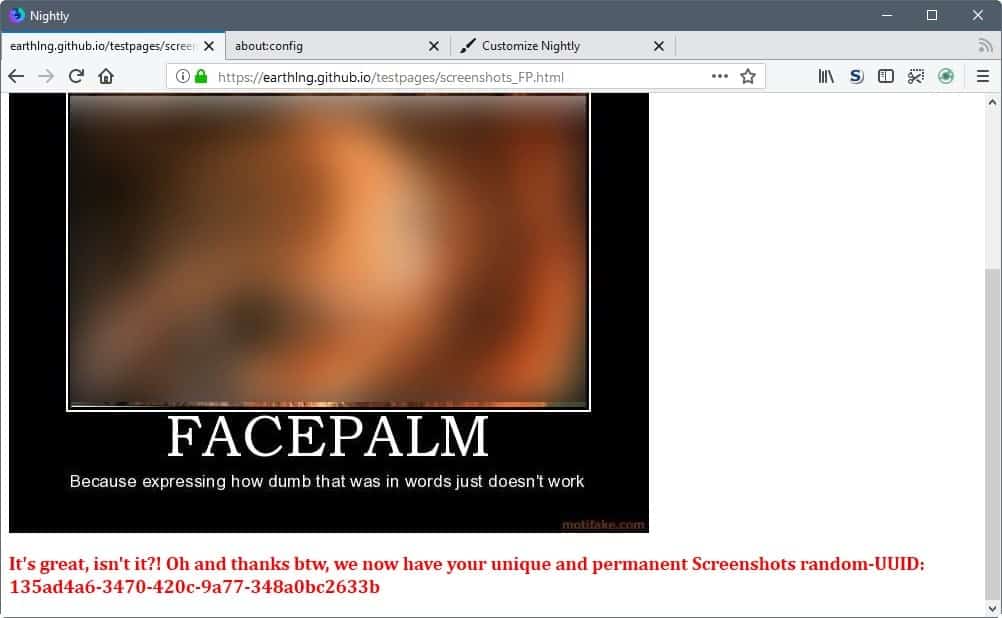
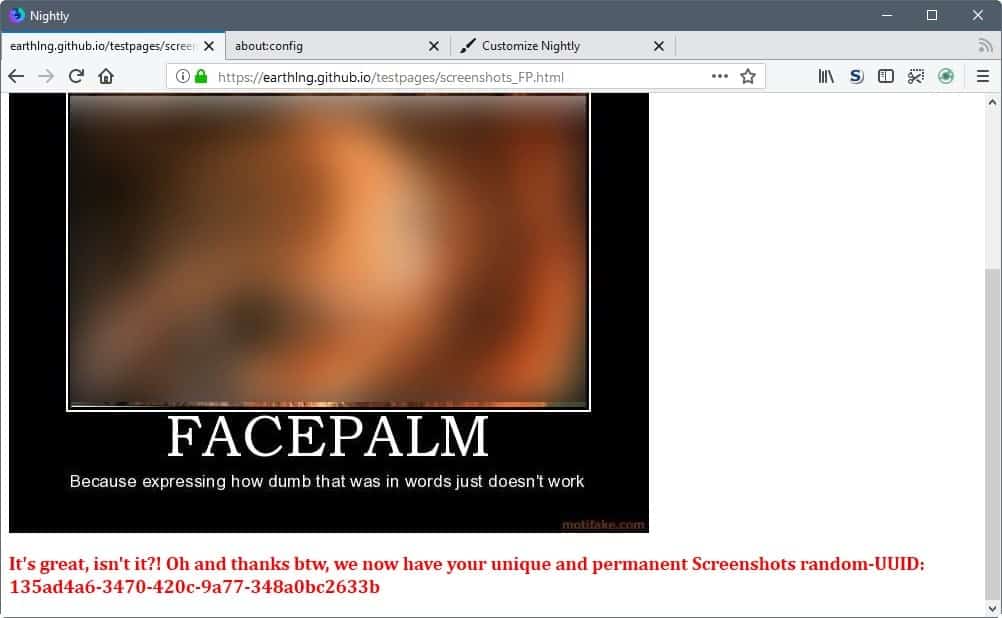
This is not just theoretical either; Earthling, one of the maintainers of the Ghacks Firefox user.js file, has created a proof of concept that highlights a leak in Firefox's native Screenshot tool.
While this particular example requires that users click on the screenshot button in the Firefox interface to make the unique ID available to the site, other extensions may expose content without user interaction.
Apple's Safari uses a random UUID system as well, and the researchers discovered that they could enumerate about 40% of all extensions as its implementation is flawed.
If the WebExtension exposes content to sites because they have implementation flaws, sites may fingerprint users based on the unique ID that gets exposed in the process.
Closing Words
Mozilla needs to rework the implementation to protect users of the browser from this. Even if you don't use WebExtensions at all, you may be vulnerable to this as Firefox ships with several system add-ons that may expose the ID to sites. (Thanks Pants and Earthling)





















This simple test reveals your ublock Filter lists to greatly assist in fingerprinting.
https://browserleaks.com/proxy
However the easy way to defeat this mining is to disable javascript.
Today I can surf almost all websites to get the information they publish. The exception is playing videos (can live without) and sometimes reader comments (Ars Technica). Some sites will not work without javascript enabled like politico.com.
Because of GDPR political.eu works fine.
As for logging into a site it depends upon if they monetize you by allowing third-party analytics tools.
I will enable javascript then disable add-ons IF there is no eavesdropping (for instance as required by law for medical data).
They most severe breach is to inadvertently give ‘to much’ consent by agreeing to be texted your drug list when your prescriptions are ready.
These third-party proxy services are then free to share and sell your listed prescriptions. While the pharmacy is under strict privacy rules, it does not matter as the patient just gave their medical condition away! These privacy policies are next to impossible to obtain while the trusted, highly-intelligent pharmacists are kept unaware.
please post privacy settings for firefox how to change this in about:config to reduce the browser fingerprinting
A Palemoon install, a look at the available addons and a few clicks make the lone M0ZILLA former user happy.
A Palemoon install, a look at the available addons and a few clicks…
Thanks for suggestion.
How do you spell “relief”? Answer is: PALE MOON
Dear FireFox: I have had it!
I am not going to spend a lot of my time for keeping up with your (sometimes rediculous) changes, features, imposed measures (for my own good or safety).
I am not getting a PhD in keeping up with the latest.
I am fed up with your reasoning after it was discovered that you start using Goole’s SW in a modified version “after a year negotiation with Google”, but WITHOUT informing your users what you were doing secretly.
It has been a too long time and too much bs.
It is my feeling that you are on the way out in the long run. Your incremental changes and improvements will not survive. let me illustrate it with the following analogy:
In the old days in the USA the Pony Express got under competitive pressure coming from new technologies. One way to make the ponies run faster was to give them titanium horseshoes that are much lighter than the steel ones. Would you think these lighter horseshoes would have made the Pony Express survive one year longer?
Greetings to the believers in Firefox
@ ALL
Mozilla has ignored extensions’ resource management for more than a 🔥DECADE🔥
It will continue to devolve with respect to user dignity and user cpu cycles.
You’re right. Sorry.
There’s a follow up to this issue. Gorhill says that uBo and uM do not leak anything, as both do not expose web_accessible_resources (for webext) or resource:// (for legacy)
to the outside. I’d like to know more about moz-extension:// (for webext) but alas
Source: https://github.com/ghacksuserjs/ghacks-user.js/issues/227#issuecomment-326277454
The issue is not the devs, its the underlying architecture. Take the above link where we’re vetting some Web Exts for knowledge and peace of mind
Dear /r/firefox … the ghacks user.js was started by Torin Oakenpants, contributed to, and built on, by numerous anonymous commentators. It is called the ghacks-user.js because that is where it started (and where Martin Brinkpants published it). The user.js PROJECT, has always been a one-man band and contributors who have done nothing but be positive and constructive. It now resides on GitHub with more input from like-minded people, and has been there for six months.
caspy7 et al … Just host this user.js PROJECT and all the people following it on your forum. You’ll be warmly hailed by thousand of users who go beyond Firefox GUI. Your millions of users will understand what’s behind about:config and the overall added pings will greatly improve your bank accounts!! Mozilla, akamai, cloudflare will contact you for greater, richer opportunities lying behind the new forum! Just do itâ„¢
Kumar Chandrapants, Financing Assistant.
@ Pants Impairment
UserScripting ghacks far predates this Torin.
💡
Privacy is a right ergo AdBlock
The attempt at humor (sarcasm?) by “No Pants” is ruined by placement of the followup — it’s displayed too far away from the earlier comment, so it just winds up seeming confused / dippy / waaaay-out-there
@Jody Thornton – i agree. The comments can be weird, especially when certain comments have no reply button.
Then why can’t ALL of the posts have reply buttons. That way eveything is in sequence.
Mozilla is a tracking enterprise. Every attempt at resisting is futile. Muahahahah*cough*ahahahah…
@Tom Hawack
Hi, Tom
would you be interested to list the changes you made to Waterfox ? Or give us some basic changes you did. It may be some work but on the other side it could help many people who are interested switching from FF to Waterfox and are not so fit with privacy in browsers. Ok, your are already in Ghacks Hall of Fame but this may put the bay right onto your head. Interested ?
Hi Spaghetti (nice pseudo, miam!),
I was running Firefox ESR 52 with a heavy user.js file, then I just moved to Waterfox 55.0.2.
I had to discover the differences between Firefox 52 and 55 AND the specifics of Waterfox compared to Firefox.
What I did :
I installed Waterfox 55.0.2 because that version now creates its own user profile; the install is supposed to transfer the Firefox’s user profile, but in my case it didn’t : I was faced with a brand new, virgin Water profile : good, I prefer.
From there on I could have copy/pasted my old Firefox profile to my new Waterfox profile : I didn’t, preferring to install all of my 67 previous Firefox add-ons one by one. Good thing I did because some add-ons wouldn’t run on Firefox/Waterfox 55: I have in mind TabMixPlus (since its been updated) which broke, really broke what was already installed, a day’s work, I had to restart from scratch.
Once all add-ons (almost all) installed on my new Waterfox profile, the big work #2 had to be achieved : fine tuning Waterfox’s settings : that’s your question, right?
I used Pants’ ghacks-user.js-55.0-alpha user.js file [https://github.com/ghacksuserjs/ghacks-user.js/releases/tag/v55.0-alpha] : alpha is relative because the user.js file is accomplished. Took me an evening to read, understand and apply or not all the settings provided. I will never sufficiently repeat how this work is helpful : all settings are documented, the user has but to make the effort of not using the user.js file blindly and all turns out excellently well.
Anyway, it took me two days, I’m still looking at (and always will) anything which can be improved, but without this user.js file I would either have missed correct settings or still be working on them : ghacks-user.js is an extraordinary tool, the best available, believe me.
Mentioning the exact changes I operated would mix up those of the settings valuable for all with those which correspond more to a user’s preferences. Best is to do as I did, download the user.js, study it, take your time, make coffee and choose the settings you want.
Hall of Fame is nice but on what ground?! I just happen to come in and out (more of touch and goes to clarify any sexual analogy!). But yes, Ghacks is my favorite place.
@ Tom
http://kb.mozillazine.org/Profile_folder_-_Firefox
@Jody Thornton, please read more carefully. I know the commenting here is weird but I was clearly referring to Appster (even quoted) – never mentioned Tom Hawack.
As for the “long term”… can you really guarantee Firefox’s “long-term” future, or take for granted any such kind of future for anything? Nothing is certain, and Mozilla’s WebExtensions are certainly not something to bet on.
@George
Actually your link simply states that the WebExtension version provides backwards compatibility. Nowhere does it confirm that uBlock will support Pale Moon long term. As of what is understood right now, Tom Hawack is NOT spreading false data.
Besides there’s no need to state it so strongly like that. If Tom had simply misunderstood, just clarify the point for him. No need to accuse him of false date spreading. That’s how fights start.
@Appster,
For those who as myself get lost in computing standards, terminology and development,
[http://www.basilisk-browser.org/preview/] :
“basilisk is a web browser building on the Unified XUL Platform (UXP), an application platform currently in development, a true fork of Mozilla’s pre-servo platform code and using a new iteration of Goanna as a layout and rendering engine, that will allow customizable, cross-platform applications to be built using the XUL markup language. The web browser is both a vessel to facilitate development and testing of UXP, and a direct replacement for Firefox with full add-on capabilities (both NPAPI plugins and all types of extensions).”
[https://github.com/MoonchildProductions/moebius] :
“Unified XUL Platform (UXP)
Codename: Möbius
This repository holds the code for a unified application platform for XUL-based applications. It is a hard fork from the Mozilla code repository (mozilla-central) with an early-2017 fork point.”
This said, I read your thinking path concerning the present and especially the future development of browsers and more specifically in their management of add-ons and Webextensions. That thought is certainly fed by a knowledge I have not : I have to rely on what is stated here and there and make a choice, as many of us.
I had in mind that supporting add-ons (so called “legacy” when it appears that add-on=legacy and that otherwise is called Webextension) because their code support will no longer de facto be enhanced, would represent a static area of the whole browser code, therefor not problematic to keep in parallel to Webextension specific code. I forget that code is a whole and that, as you mention it, new security development will carry on the whole browser, add-ons section as well. My understanding is basic :)
OK- I appreciate your explanations. Firefox, Cyberfox, Waterfox, Pale Moon … Chrome, IE, Edge, Vivaldi and several others. I tend to forget IE & Edge which nevertheless doesn’t reduce the wide array of browsers. Why choose one rather than another is related to quite a few parameters and is a challenge by itself. Of course many of us use several browsers and I always have in mind the default browser when arguing, that thing which opens when you hit on a web link from anywhere in your OS :)
We also have habits tied to our browser experience. I have mine with Firefox/Waterfox and I confess that this fact takes a 50%+1 part in my browser choices. Besides that, I happen to believe that Firefox remains the “less worst” of browsers available nowadays, but I could be wrong of course.
@Tom Hawack: Pretty much yes, a browser supporting both would be optimal. This is why staying on Firefox 52 ESR has never been feasible for me, since it didn’t have decent WebExtensions support. I feel that Waterfox 56 strikes the best balance for me. One developer is totally capable of backporting security fixes from newer versions, so if he manages to do that for Waterfox 56 I’ll be fine for some time. Anyway, he’ll need to implement new web standards at some point in the future, and this will be the interesting part. One single developer can’t do that all by himself. It would be great beyond measure if he can still pull many changes from Mozilla, but I don’t think that will come to pass. Maybe the project gains traction and attracts more developers, which would also be good. Otherwise there is still Basilisk, which is not optimal for reasons already being mentioned, and is also facing the same problems.
To be perfectly honest with you, I’ve already considered jumping ship to Vivaldi, seeing how this browser provides add-ons about as powerful as the ones possible in Firefox 57, and can still be heavily customized. Extensive UI manipulation via CSS code is possible there, while Mozilla has already announced its willingness to cut that out in the future. We’ll see.
Should nothing stick and should the forks die as some haters have already suggested I’ll probably leave the sinking ship. Who would have thought that a Blink-based browser would one day be more customizable than Firefox? Oh well, here we go…
@Appster, I was ware of the moebius project and thanks for mentioning it.
I’ll state my case straightforwardly : I wish a browser handling Webextensions AND legacy add-ons, because I’ve found no argument to prefer one or another : some add-ons will never be able to have their Webextension equivalent and some Webextesnsions run better, faster than their add-on equivalent.
Fundamentally, even though I’m as far from coding skills as an Eskimo is from a bikini I tend to “feel” more than believe that a browser supporting add-ons and Webextensions simultaneously is too beautiful to be true. But I’m also aware of my feelings : I just don’t know. We’ll learn much related to that next year (that’s after the colors of Fall, white snow and Xmas trees, the New year’s hangover, the birds and the bees of Spring 2018). Time flies but we ain’t yet arrived at JFK : seat-belts still loose!
@Appster quote: “The lack of WebExtension support. This is a deal breaker for me personally (and I imagine for you as well), since future versions of Decentraleyes, HTTPS Everywhere, uBlock Origin etc. will be WebExtensions.”
Both Decentraleyes and uBlock Origin authors have specifically said they will continue developing/supporting the XUL versions (for Pale Moon etc.). Where are you getting your data? Or are they just personal assumptions? (…wishful thinking?)
Example: https://github.com/Synzvato/decentraleyes/issues/190
This is just from a few days ago, it’d be best to stop spreading false data.
@Anonymous, undoubtedly some situations more than others illustrate different approaches.
I don’t believe my way of seeing this scheme “How, now, deal with the combination of [keeping legacy add-ons + using the latest browser version] in the perspective of the post Firefox 57?” is the worst.
Assuming that Waterfox will not be able to handle modified post Firefox 57 code in order to keep legacy add-ons running would not have made me opt for Firefox 55 anyway considering Waterfox does cut off several Firefox specific privacy issues besides (or even before) the fact it cuts off as well — for now, ok & for tomorrow is promised but feasible?) denial of legacy add-ons.
> ” I do not think that “reculer pour mieux sauter” a wall could be a good advice IMO.”
(language course – start)
I wouldn’t have known without looking it up how to correctly translate “reculer pour mieux sauter” (that’s French, dear audience!) : I found “take a step back to see the big picture” — “take a step back in order to take a big jump forward” — “prepare to move ahead”
(language course – end!).
That statement assumes Waterfox will not make it with legacy add-ons once Firefox 57 in place. I’m assuming Waterfox wil make it but only by the word of its developer. I understand that anyone who assumes legacy add-ons end with Firefox 57 AND with all Firefox 57 forks — whatever the seriousness of their conviction — may have a different approach than mine.
Finally this is not a trip to Katmandu with 1 buck in the wallet and no return ticket : it’s only a browser and as always in this mad cyberworld the only real important matter is the user’s data : available the only work is to move it from one place to another.
@Tom Hawack + Anonymous: If I was you I would also closely follow: https://github.com/MoonchildProductions/moebius The Basilisk browser will be based on Firefox 52 ESR code, so every legacy add-on which is compatible with Firefox 52 will probably work. Yet as is always the case with the Pale Moon team, they have to include one big disadvantage: The lack of WebExtension support. This is a deal breaker for me personally (and I imagine for you as well), since future versions of Decentraleyes, HTTPS Everywhere, uBlock Origin etc. will be WebExtensions. Staying with older versions is not really feasible in this case. These are add-ons which need to keep up with current web developments, unlike e.g. interface-related add-ons. So I also follow the Waterfox development much more closely, to be honest. Just wanted to suggest this if Firefox 52 minus WebExtension support is feasible for you (I doubt it). Still, it will provide better compatibility than current-day Pale Moon should you ultimately need to switch.
@Tom Hawack: Thanks for your response, however even if I respect all your reasons they are not good for me, also I do not think that “reculer pour mieux sauter” a wall could be a good advice IMO.
@Anonymous, I’ve chosen Waterfox for two reasons,
1- Its features [https://www.waterfoxproject.org/] :
” Disabled Encrypted Media Extensions (EME)
Disabled Web Runtime (deprecated as of 2015)
Removed Pocket
Removed Telemetry
Removed data collection
Removed startup profiling
Allow running of all 64-Bit NPAPI plugins
Allow running of unsigned extensions
Removal of Sponsored Tiles on New Tab Page
Addition of Duplicate Tab option
Locale selector in about:preferences > General ”
2- Its commitment to carry on support for legacy add-ons [https://www.waterfoxproject.org/blog/waterfox-55.0-release-download] :
“[…] Waterfox will CARRY ON SUPPORT for add-ons.[…]”
Point (2) is of course essential, for me and for many Waterfox users. Should this commitment fail that I’d be of course disappointed but I cannot, could not doubt of the developer’s word on the basis that anyone, be it the respected Moonchild declares this add-on support as impossible in the post 57 Firefox series.
For the time being I’m assuming a choice which had to be done, IMO. I could have remained on Firefox ESR until June 2018 but then I’d have been confronted to the same problematic and moreover Firefox/Waterfox would have far more differences with the 52 branch than now (52/55).
What happens if Waterfox slowly abandons legacy add-ons starting 57? It won’t be worse than what it would be now. I’d just have to reconsider Waterfox vs Pale Moon as I did now with Firefox vs. Waterfox.
Everything is moving fast and personally I am cautious with predictions. I’ve only decided to shift from a “wait and see” approach to a “standby” behavior.
#ams, I’d imagine they shared their opinions on topics they had in common, some arguing they had been served first, others pointing out the merits of maturity, and one last the glory of bones when they sleep no longer but in one bed :)
I’m left wondering what your wife and ex-girlfriends did, for 2 days, to keep themselves occupied while you manually reinstalled yer 67 addons???
;^p
Waterfox and the brick wall by Moonchild:
https://forum.palemoon.org/viewtopic.php?f=3&t=15507&p=119774#p119780
“If he intends to keep supporting extensions, he’ll run into a brick wall if he keeps following Mozilla when they hit v57. Firefox won’t have the framework anymore for support of anything but WebExtensions, so I’m pretty sure if Waterfox remains Waterfox (being rebuilds of Firefox-release) that the “add-on store” will be populated with only WEs since those are the only ones compatible. Best make a new thread if you want to discuss Waterfox.”
Can you please give me a good reason to switch to Waterfox in that case?
Tom, thank you for very much for your answer. I will give it a try and see what happens. I like your modest attitude, but I still see you in Ghacks Hall of Fame. Anyways, I eminently enjoy your writing style.
Hello martin, seems like firefox on reddit wants to ban you and your site.
BECAUSE YOU MAKE MOZILLA LOOK BAD!!! KEK
good luck martin, love your articles.
mozillaZine and the Firefox Reddit are temples of worship inhabited by fanboys. Suggestions to ban gHacks over there is basically a knightly accolade for gHacks.
@ams: /r/mozilla is right there of the sidebar of /r/firefox. You need to go to see doctor.
Agree, but your comment is too-levelheaded, too understated. It’s been my longstanding observation that the folks at mozillaZine forum, especially the staff, are MEAN-SPIRITED fanbois.
reddit/r/firefox, well I’ll cut them some slack in regard to the collective “attitude” b/c I realize their venue is a high-profile target for would-be trolls. Thankfully (my opinion), when r/firefox unfairly squelches a topic, it usually resurfaces in reddit/r/linux and elsewhere. BTW, it’s interesting (curious)(odd) interesting to note that reddit/r/firefox does NOT provide a sidebar link to reach reddit/r/mozilla
Dear /r/firefox … the ghacks user.js was started by ME, and contributed to and built on by numerous anonymous commentators. It is called the ghacks-user.js because that is where it started (and where Martin published it). The user.js PROJECT, has always been a one-man band (ME) and contributors who have done nothing but be positive and constructive. It now resides on GitHub with more input from like-minded people, and has been there for six months.
caspy7 et al … ghacks-user.js is NOT ghacks.net. DO NOT CONFUSE THESE TWO SEPARATE ENTITIES please. That is all. Thanks
Could you try if this prevents the UUID from being leaked? According to its GitHub it will be ported to WebExtension.
https://addons.mozilla.org/en-US/firefox/addon/no-enumerable-extensions/
That extension does nothing anymore, it was useful* when the plugins (not addons) could be enumerated using navigator.plugins but mozilla have already removed that to reduce browser fingerprinting.
*Some pages broke after the change and needed to modify their js in order to stop using navigator.plugin but the change wasn’t that much disruptive when mozilla did it but prior to that webs were not in a hurry to modify that code.
Firefox, a privacy-protecting browser… At least according to some folks in the gHacks comment section.
Those folks are actually hallucinating. They don’t even realize that even their ISPs are tracking them.
Tor browser? Nope, many webs are not compatible with it. We don’t even know if the Tor developer put their tracking device or not.
TorGuard.net, not Tor, or other VPN provider who has publicly fought request for information about users.
ftw
* important: This does require diligent self discipline.
@ Appster
I am sure that people who read gHacks would appreciate your input as to which browser, in your opinion, is the best for privacy protection.
Chrome, IE11, Edge ??
Pale Moon is better than Firefox when it comes to privacy (default settings). Other than that, Tor. Yet Tor is not practicable for everyone. Firefox has the inferior defaults in comparison to both. If you are willing to heavily tweak, Firefox may also do the job.
It is not necessary to cynically bring up browsers which are configured even worse than Firefox.
That’s a vulnerability. Even the best security-protecting apps have vulnerabilities.
“It had to be you” … a great Jazz song which immediately came to my mind when reading your comment! You never give up do you? Is it, is it was it used to be, is it not … a privacy-protecting browser? This is an everlasting topic. I know your opinion sometimes shared, you know mine, seems to me we’ve elaborated so intensively that from there on we’re only repeating ourselves like propaganda and counter-propaganda.
But, but, but … now that i’ve switched to Firefox 55 (via Waterfox 55 which does bring privacy and allows legacy add-ons) I must say that if the “55 series” is snappier, faster than the 52 (ESR) it also lowers the user’s privacy by having added new switches which should be opt-in and not opt-out.
So, yes : Firefox (and more specifically Waterfox) is a far more user’s privacy concened browser than its competitors, but no : it is not, out of the box, ultimately set to protect that privacy. The switches are there nevertheless, available, but it requires a user’s commitment, (hard) work, investigation to manipulate the right switches, to manipulate them correctly. To sum up : a novice starting Firefox 55 (and even Waterfox 55) will not be able to say that the browser is ultimately set to respect his privacy. He’ll have to either dig or ask a relative to help him figure it out. Relevant of a modern era aiming to conciliate the freedom of the mighty and ethics for the others : out of the box the mighty are ahead, once correctly configured with available settings, the less mighty catch up, even if they may never be ahead. C’est la vie.
@Tom Hawack: “Surrender” is not a word which belongs in my private dictionary, Tom. Firefox definitely isn’t what it used to be in regards to privacy. I have tightened the security and privacy settings quite a bit, and have not seen any breakage yet. Every website visited (including major ones) worked as intended. Why is Mozilla unwilling to provide that by default?
You know that this whole paragraph in which you talk about how the user can tweak Firefox to achieve better privacy doesn’t count as an excuse. It’s like selling a car without seats (you need to find fitting seats yourself) as the “safest car in the world”. Pretty ridiculous.
What really bugs me is that Mozilla’s advertisement in regards to Firefox is misleading. The user needs to toggle a whole range of settings and needs to install an entire bunch of add-ons to achieve decent privacy. Calling bare-bone Firefox privacy-respecting is kind of absurd.
This is Mozilla’s failure, and we shouldn’t try to elevate ourselves to the rank of experts just because we were forced to figure it out. That’s a bit laughable.
Only a couple changes are enough to make Firefox beat all browsers privacy wise, Tor Browser aside.
It’s just that you can keep ramping up and up.
Here with Waterfox 55.0.2 (yep, I’ve finally quit Firefox ESR 52) I’m still using the ‘No Resource URI Leak’ but no longer its 1.1.0 version available on AMO but its clone 1.1.1 version available from [https://github.com/ghacksuserjs/ghacks-user.js/issues/191]. I’m surprised Pants doesn’t mention it within his above comments.
With this ‘No Resource URI Leak’ (clone) 1.1.1 add-on I get a 100% of NOs on BrowserLeaks’ Firefox Resource Reader page [https://browserleaks.com/firefox].
trying that now, thanks for fyi
I think that page is broken in Firefox 55+ so you should get all NOs with or without No Resource URI enabled, at least I did when I was running Firefox 55.
Tom, that may be correct (er “by design”) for Waterfox. The default prefs may have it spoofing user-agent = firefox-usr
Well, thanks for the information, jupe.
I’ve just ran that Browser Leaks Firefox Resource Reader test page with the ‘No Resource URI Leak’ add-on disabled, and indeed all except the following three are NOs :
Platform Detection ✔Windows
Default Locale ✔ en-US – English (US)
Firefox ESR Channel ✔ Yes
Firefox ESR Channel, checked? When the test is performed with Waterfox (55.0.2)?! Strange. The test seems unreliable if not broken, indeed.
Good to know.
Note: Firefox 57 just got this 100% NO built-in yesterday :)
Considering the heading Mozilla has took, maybe that’s the point of whole webextensions system and they just got caught red handed? /s
By the way, I’m quite not sure if that’s good material for ghacks but it’s interesting that Mozilla and Soros joined forces in planned war against “fake news” on the Internet.
FUD. FUD. FUD. Mozilla didn’t team up with Soros/OSI. There was a misleading AFP headline that seemed to imply a connection between two completely unrelated projects.
You should remove that /s, obviously you meant every word.
Bye-bye Firefox as TOR-Browser!
I doubt that will happen, this issue getting fixed by Mozilla is the more likely.
This is the bugzilla ticket: https://bugzilla.mozilla.org/show_bug.cgi?id=1372288 – currently access denied. It should be opened up soon
The current TBB is based on ESR52.x, which while it uses legacy add-ons with their own issues, is not really WE ready (AFAIK), which is what this issue is about, and it ships with no WE’s. ESR59.x “should”/”will?” address this issue, which Mozilla know about. In fact, it should be fixed for 57 at the very least (but 57 does not affect TBB, excluding security fixes, and this may be considered as one and included before ESR 52 EOL)
Another thing is to vet your WE for contentaccessible manifests – I know I am. I’m going to get the ghacks user.js WE wiki recommendations and all system addon’s vetted. I assume a solution will be found, not in time for those on 54, 55, 56 etc running WE that may expose UUIDs, but long term it can be fixed and not an issue.
Heh .. love how you blurred the nude pussy(cat)
Palemoon it is.
Doesn’t matter, legacy extensions are 100% discoverable as well. Same for other browsers.
Unlike other browsers, Firefox WebExtensions will be fixed in time though: There is a Bugzilla ticket hidden from the public out of security concerns, just like for regular browser vulnerabilities.
The fix is not to pick a different browser, but to block at least 3rd party JavaScript.
Firefox’s privacy.resistFingerprinting should help making legacy extensions harder to figure out since this relies on timing, if I remember correctly.
Yes, keep making idiotic additions into a web browser like… a screenshot tool (it sure helps a lot for browsing the web), and all will be well. Expect more stuff like this to emerge, with the “all-in-one browser suite” concept. Firefox is going down fast and it’s too late to save it… let alone fix it.