Encryption and Strong Passwords
Encryption is becoming more and more recommended and less and less for the tinfoil hat wearing type. It’s not uncommon to hear of people in the tech world encrypting their harddrives just for the purpose of extra security. I personally encrypt my laptop; both the Windows side I keep for image and audio/video editing, and the GNU/Linux side I use for everything else.
But, while popularity of full disk encryption is on the rise, it’s from my experience that many people actually understand it beyond, “It means that if someone gets my laptop, they can’t access my files,†which is only half correct; full disk encryption will protect you from an adversary accessing your files if your machine is off at the time it falls into the wrong hands.
All GNU/Linux operating systems that I am aware of, support the use of dm-crypt to do full disk encryption, since it’s built directly into the Linux kernel itself as of kernel 2.6. However, not all graphical installation utilities included with some distributions give full disc encryption as an option.
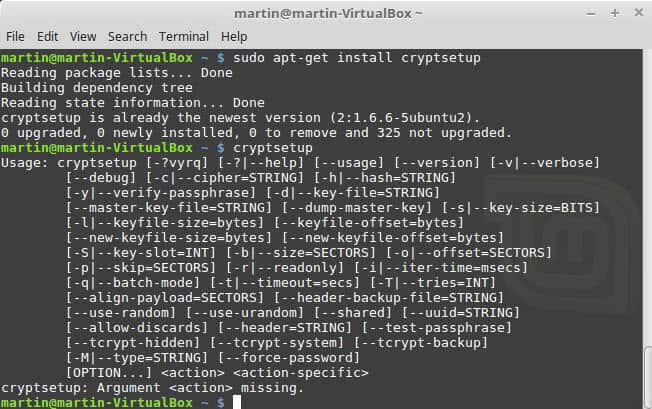
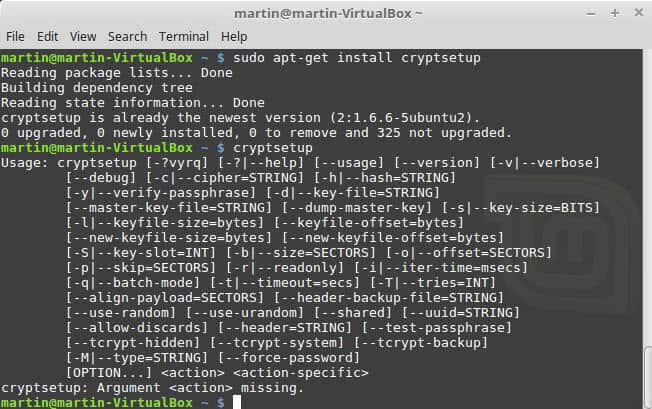
To install the dm-crypt tools if they are not already available use
- apt-get update
- apt-get install cryptsetup
When encrypting your system at the initial install, one of two ciphers will be used, depending on your distribution:
- aes-xts-plain64:sha256 (More common nowadays)
- aes-cbc-essiv:sha256 (More common in older distribution versions)
Both of these utilize AES, which is the very same cryptography used when we talk about SSL, TLS, and programs like Veracrypt also utilize it. The hashing algorithm is SHA-256, which is also industry standard. Neither AES nor SHA-256 are known to have any holes in them, or to have been broken, so if you select to encrypt your install; you can be assured that your setup is reasonably safe.
Strong Passwords are key
With that being said, you absolutely MUST ensure you use a secure password. Passwords such as, “password123†can be figured out within minutes or even seconds by amateurs, never mind adversaries with know how, or botnets, or supercomputers. A good example of a secure password would be something like, “!gh$mXjkKE4%72#Mxnb%$k3@!†Which would be next to impossible to crack before you died old age.
Note: The secure password protects your encrypted partition or drive. Since you cannot save the password to a password manager on the drive, you either need to memorize it, or use another means to remember it (another password manager on your smartphone for instance).
Now, this leaves a question of how does one create a secure password like the example, that you can actually remember? I’ll teach you my method; it may not work for you, but it might!
First, think of a song that you REALLY enjoy. Let’s say the song is “Michael Jackson – Dirty Diana.†Pick any part of the song that stands out in your mind, I selected:
Diana walked up to me,
She said I'm all yours tonight
At that I ran to the phone
Sayin' baby I'm alright
I said but unlock the door.
Because I forgot the key.
She said he's not coming back
Because he's sleeping with me
Now, we want to take the first letter of each word, and add symbols and capital letters. How I like to do this is rotate each ‘sentence’ into caps/nocaps. After each sentence, I also add a symbol. An example of this could be:
DWUTM!ssiayt@ATIRTTP#sbia$ISBUTD%biftk^SSHNCB&bhswm*
As you can see, the song Dirty Diana now became a highly secure password, and easy to remember; each sentence has been either capitalized or not, and I’ve added a symbol after each sentence, in order, down the keyboard number keys. If you can remember the song, you can remember this password.
This password is secure. Could it be more secure? Probably, is anyone ever going to manage to brute-force that? I’d be willing to bet everything I own, not.
This method may or may not work for your memory, but perhaps it will spark another method for you!
Final Words
I personally recommend everyone encrypt their hard disks. There is a negligible performance hit that on modern hardware you likely won’t even feel, but it adds a lovely layer of extra security on your devices. Even if you “Have nothing to hide,†why wouldn’t you take extra security measures when they are available to you? But remember, you could use every encryption method in the book, but if you use weak passwords, it won’t matter!
How about you, do you encrypt? Do you have another method for creating strong passwords?

















I use a similar method to the song, but I use books. Same book, different pages. Then I use the the 1st, 2nd or whatever paragraph in a similar way to the song. All my passwords are different and I rarely use passwords of less than 16-20 characters. All stored in KeePass with a long password generated in the same way. I steer clear of websites and services who think rigmarole is the same thing as security (and that’s a topic that could do with more discussion.) Changing my passwords simply involves picking other page numbers or perhaps another book.
Given the mention of UK data laws, what I find astonishing is that politicians who can’t wire a plug or change a light bulb think they can ever control surveillance data. They have to rely on specialists with their own agendas – people who might promise that their masters are exempt from surveillance but are surely never going to pass up a chance to hold the last ace. In the UK what’s now frightening is the sheer range of petty officialdom now empowered to examine personal internet data. There is already a growing record of shocking misuse by people like local councils. Theresa May – if she survives the next few days – wants even more powers, and there seem to be plenty of people foolish enough to believe mass surveillance is necessary to protect us, or that we can ever trust politicians and bureaucrats in such matters. Any who can’t see the dangers there has never read a history book.
“Give me six lines written by the most honest of men and I will find something in them to hang him.”
I made a simple and secure Random Password Generator that takes due care to preserve entropy when running on a system that provides an entropy pool like /dev/random or /dev/urandom; something that pwgen does not.
https://github.com/ankitpati/rpg
I will never use full disk encryption. Why? Because I do not trust my data to some programmer’s faulty software which could at any time prevent me from decrypting that data. Which is why I also never use an archive protocol when backing up my data: mess up one byte of that data and the extracting of that data may prove impossible due to incompetent programming.
Why do you think ransomware is so prevalent? Because it holds your data to ransom by encrypting it. The same result could easily occur if the decryption software fails.
If you’re going to be paranoid, go all the way. Don’t trust encryption software without having an unencrypted backup somewhere safe.
VeraCrypt on Windows. Use Diceware with EFF’s wordlist, 7 or 8 words.
Are most people here criminals?
Sure sounds like it.
I used to buy used back in the day.
The old 166mmx had the area’s mental health data on it,
so I figured I’d do them a favour and wipe it.
Back then people thought formatting was safe.
Local thieves would sell laptops the same day with everything still on it.
Local attacks?
A Brazilian banker kept out the FBI with Truecrypt,
way back in 2010.
It’s remote attacks you’re defending against.
I haven’t heard anything convincing to stop them.
One spy said it takes £35m to secure one computer,
good luck with that.
too bad we cannot like comments on here; I’d give you a bunch
There are new password guidelines coming down from NIST. They suggest using longer passwords like passphrases. Stop forcing forcing mixed character types (upper/lower or special characters) or forcing password changes that are dated based. Hopefully websites will pay attention to the changes.
For rotating or having one password discussion > you’re gonna give up that to an officer at the airport in us, canada (soon coming to europe) so having one password will f u for life.
here comes the duality – one set of public facing bs accounts and passwords to the same, and more fake, private, underground profiles, groups etc.
All hail the end of freedom of speech as led by the fearless orange cheetoh in charge
Hmm… How do you estimate the entropy of this scheme? How many bits are added with rotation? Maybe 2?
This is only memorable if the stanza is really well known to the user, which means that the entropy can be reduced via social engineering, personal familiarity, or snooping social networks.
Great article! Thanks for giving some insight into encryption esp.
Btw, if you don’t want to think of a strong password yourself, you can generate one through LastPass. And if you don’t have LastPass or prefer a not to use it for generating secure passwords, DuckDuckGo is your friend :-) Just enter
password xx strong
in the DDG search field (replace xx with the desired length of the password, for example: password 15 strong).
The same LastPass that’s been hacked and you give ALL your passwords to? no thanks
I just signed up for PasswordWrench. We’ll see how it goes. They have a generator or a card i can use and print and be happy under my tin foil hat gnashing my teeth together
> DWUTM!ssiayt@ATIRTTP#sbia$ISBUTD%biftk^SSHNCB&bhswm*
> and easy to remember
Hmkay.
> Some say rotating passwords are better than strong passwords.
Never in this case.
You try to protect yourself against someone who has either your PC or a copy of your data. Against neither of those changing your password will help at all.
With passwords there is only one thing: longer passwords. Sure, throw in some numbers or special characters if you want, but each character more will significantly(!) increase your password strength.
People need to abandon passwords and move to passphrases.
The key here is not complexity but pure length. A 32 character password that is just one character repeated 32 times is massively more resistant to brute-force attacks than ANY 8 character password.
Passphrases are better than passwords because they are long and yet effortless to remember (and also don’t take forever to type out by hand). For example, the phrase: “When the wind shines, the sun blows.” is a 36-character passphrase that contains uppercase, lowercase, and special characters, and yet it is easy to remember, takes only a couple seconds to type, and does not appear in any dictionary. Passphrases make security painless and effective.
Another thing that makes encryption painless and effective is hardware encryption. Many SSDs and some HDDs automatically employ always-on full disk encryption. The problem is in order to secure access to the data you need to set the ATA password aka hard drive password, and for some reason few BIOSes make this function open to users, even though virtually all hard disks and SSDs allow you to set an ATA password as part of the standard. ATA password setting is usually found in higher end laptops and mobile workstations. I use a Lenovo Thinkpad T61p which has the option to set a hard drive password, and I use it to secure my main drive, which is a Crucial M550 SSD.
Now i would love to see a tutorial on how to encrypt a Windows 10-partition. (I wont use Bitlocker, it obviously has backdoors for the government to use.)
Check out this: https://www.ghacks.net/2012/08/08/how-to-encrypt-partitions-with-diskcryptor/
Sadly, Diskcryptor has not been updated since 2014. Considering its lack of development and that its core drivers must be constantly running, a user runs a greater risk of compromise by hackers & unauthorized access via software and driver vulnerabilities.
I would also recommend that users serious about security utilize applications that have been audited by an outside source. Open source is typically a decent solution, but oftentimes when dealing with applications so complex as encryption, many users lack the technical ability to provide a qualified response to what they have reviewed. This sometimes leads to users qualifying the program as okay because it is open-source, has many users, and has great reviews. While not a bad method for most, it may be to risky for those where the integrity of a program is critical.
VeraCrypt has been audited multiple times and by a number of sources, one of which by The Open Source Technology Improvement Fund (OSTIF), which took about 32-man-days and addressed multiple issues, many of which were fixed with their latest release.
eff.org link regarding Diskcryptor update:
https://ssd.eff.org/en/module/how-encrypt-your-windows-device
OSTIF publication/results of Veracrypt audit:
https://ostif.org/the-veracrypt-audit-results/
https://ostif.org/wp-content/uploads/2016/10/VeraCrypt-Audit-Final-for-Public-Release.pdf
Gibson Research Corporation (GRC) that outlines the VeraCrypt audit:
https://www.grc.com/sn/sn-582-notes.pdf
Thanks! But does this work with Windows 10? (GPT + UEFI)
I read a article on this site, mentioning that TrueCrypt could cause issues with Windows 10 because of that.
I run this on a Windows 10 Pro UEFI system without issues-
Some say rotating passwords are better than strong passwords. I don’t know. The main issue still seems that people using one password for everything and not changing it regularly.
@Ben
You are right about that, though not saving passwords for paypal etc. is a good thief countermeasure ;)
I truly respect security concerned people, just at the end of the day a driver can ruin it:
https://www.modzero.ch/modlog/archives/2017/05/11/en_keylogger_in_hewlett-packard_audio_driver/index.html
Though this is unlikely to happen on a *NIX system, but how many companies use GNU/Linux except on servers?
1) They can always drop a USB flash drive during a raid with something on that gets you jail time.
2) Then there is this law in the UK where they can lock you up until you give them the password, if you don’t decrypt.
Either way you go INNOCENTLY to prison.
Encryption only protects those that would get LONGER jail time if they would decrypt. I don’t encrypt drives because of reason 1) and 2), so only encrypting company laptops to protect corporate secrets is an option.
If Martin doesn’t mind a link:
https://arstechnica.com/tech-policy/2007/10/uk-can-now-demand-data-decryption-on-penalty-of-jail-time/
This shows the importance of
1. Using encrypted filesystems,
2. Secure location of removable storage containing sensitive data away from your systems. If they can’t find prove they exists, they can hardly demand you decrypt them.
3. Solid encryption of all sensitive date on removable storage with encrypted volumes in layers. This allows you to decrypt the outer volume they somehow find the drives and apply the rubber hose.
There was a time when I would have written off anyone outside of government departments dealing in classified information as paranoid. Not any more. The more people who do this, the less tenable is the argument that you are suspicious for doing so. By protecting ourselves from overreaching governments and from criminals, we are also protecting each other.
This could provide plausible deniability that certain data exists.
First of all encryption prevents some thief from accessing my ebay/amazon/x/y/z/a/b/c and posting my nudes all over the internet.
And not encrypting does not help against your “1) & 2)” obviously.
If one uses a password such as $!yN1Ov92^x7e%1K6%#KOGT6Dl6jFv6o there is no need to rotate it, in my opinion.
For Linux users, pwgen is a great little tool for creating good, strong passwords.
Was not “rotating passwords” rebuked some time ago that it does not add anything to the security of your passwords? Agree that reusing passwords is probably as bad, if not worse than using weak passwords.