Chrome: sites may record audio/video without indication
A security vulnerability was reported to Google on April 10, 2017 which allows an attacker to record audio or video using Chrome without indication.
Most modern web browsers support WebRTC (Web Real-Time Communications). One of the benefits of WebRTC is that it supports real-time communication without the use of plugins. This includes options to create audio and video chat services, p2p data sharing, screen sharing, and more using the technology.
There is also a downside to WebRTC, as it may leak local IP addresses in browsers that support WebRTC. You can protect the IP address from being revealed in Firefox, Chrome and Vivaldi, for instance.
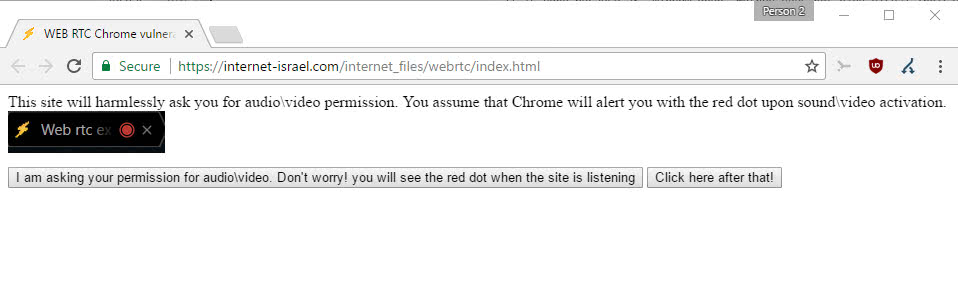
The reported vulnerability affects Chrome but it may affect other web browsers as well. For it to work, you'd have to visit a site and allow it to use WebRTC. The site that wants to record audio or video would spawn a JavaScript window then without header, a pop under or pop up window for instance.
It can then record audio or video, without giving indications in Chrome that this is happening. Chrome displays recording indicators usually in the tab that uses the functionality, but since the JavaScript window is headerless, nothing is shown to the user.
A proof of concept was created which you find linked on the Chromium Bugs website. All you need to do is click on two buttons, and allow the site to use WebRTC in the web browser. The proof of concept demo records audio for 20 seconds, and gives you an option afterwards to download the recording to the local system.
A Chromium team member confirmed the existence of the issue, but did not want to call it vulnerability.
This isn't really a security vulnerability - for example, WebRTC on a mobile device shows no indicator at all in the browser. The dot is a best-first effort that only works on desktop when we have chrome UI space available.
The explanation does not make a whole lot of sense to me. Because Android does not show an indicator in first place, and Chrome on the desktop only if enough interface space is available, it is not a security vulnerability? At the very least, it is a privacy issue and something that users need to be aware of.
While users do have to trust sites enough to give them permissions to use WebRTC, it and the fact that the site needs to launch a popup window are the only things needed to exploit this.
Google may improve the situation in the future, but users are on their own right now when it comes to that.
The best form of protection is to disable WebRTC which can be done easily if you don't require it, the second best to allow only trusted sites to use WebRTC. If you allow a site to use WebRTC, you may want to look out for any other windows that it may spawn afterwards on top of that.
Now You: Do you use services or apps that use WebRTC?



















Useful site to see what’s enabled at a glance: https://whoer.net/#extended
In Firefox open about:config. Type of copy/paste from here: media.peerconnection.enabled and then double click it to set it to false. Confirm that you’ll be careful if required (I always remove the checkmark to prevent the warning from showing).
Anyone else noticed how many of these security issues are found by people in Israel? Makes me wonder if they are experts, if it’s coincidence, or whatever the reason could be *cough*
The reason is Israel is very good in computer security. Weren’t you aware of it ? Any problem with that ? What do you think the reason could be, cough ?
For Chrome under Windows 10 CU Home, I now use WebRTC Control extension 0.1.4 from Google Store. It provides easy control, but it is not the only way to achieve its result. I will see if I keep it.
The key term here is “the user allowed the voice activation”.I dont believe this is detrimental to chrome but rather malicious activity on the server side…..
This is a protection of course, but browsers should, in my opinion, always highlight if audio or video is recorded.
Definitly agree.seems like a sneaky practice all these companys that do this and Not making user aware,another red flag to add to the growing list of privacy decay,you the man martin keep up the good work,much gratitude for keeping us in the loop.
I cover my Apple computer’s cameras with opaque stickers and transfer sound input to “Audio line in port” instead of “internal microphone.” I also turn input volume down but Apple resets it every time I reboot. I’m not certain the world could handle the sight of me naked or mumbling incoherently into my morning coffee. My Win7 machine is off-line for the duration.