DNS66 Host-based Blocker for Android
DNS66 is a host-based blocker for Android devices that is easy to setup and does not require root or special permissions.
Setting up proper blocking on Android devices is not as easy as it sounds. Solutions that don't require root are often limited when it comes to functionality.
DNS66 is a free application for Android that changes that. Basically, what it does is establish a virtual VPN connection to gain control over the network traffic. It uses filter lists to block connections to blacklisted sites, and won't interfere with any site that is not blacklisted.
It is also offering to use free no-logging DNS servers on top of all that, but supports the default DNS server the device is configured to use as well if that is preferred.
DNS66
DNS66's source is provided on GitHub, and the application itself on F-Droid but not on Google Play. F-Droid is an app marketplace for free and open source applications.
To install DNS66, install F-Droid first on your Android device if you have not done so already. Once done, use the app to install DNS66 on the device to get started (by searching for it on F-Droid).
The app displays a couple of tutorial screens on first start that provide you with the most important information on its uses. You may do the following when the tutorial ends:
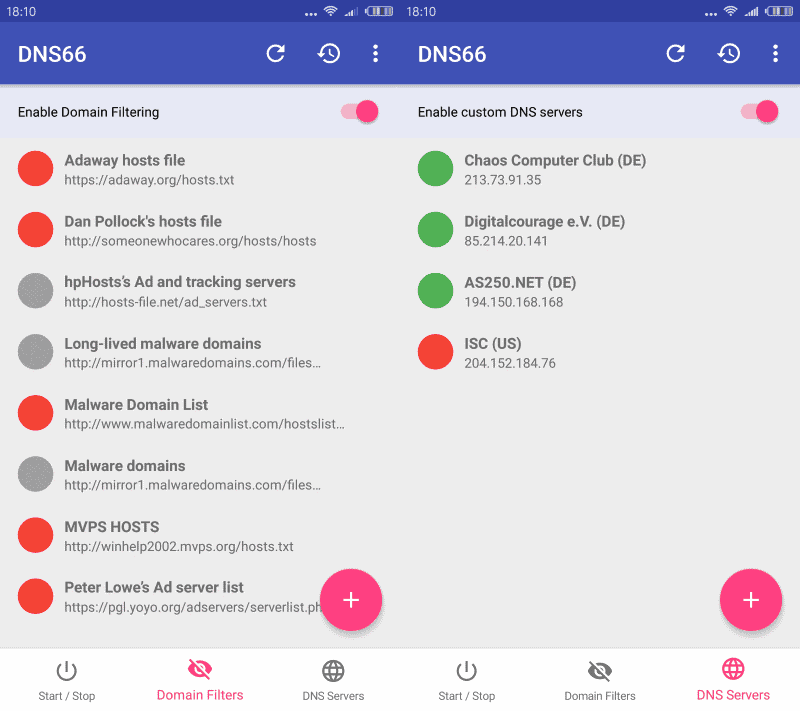
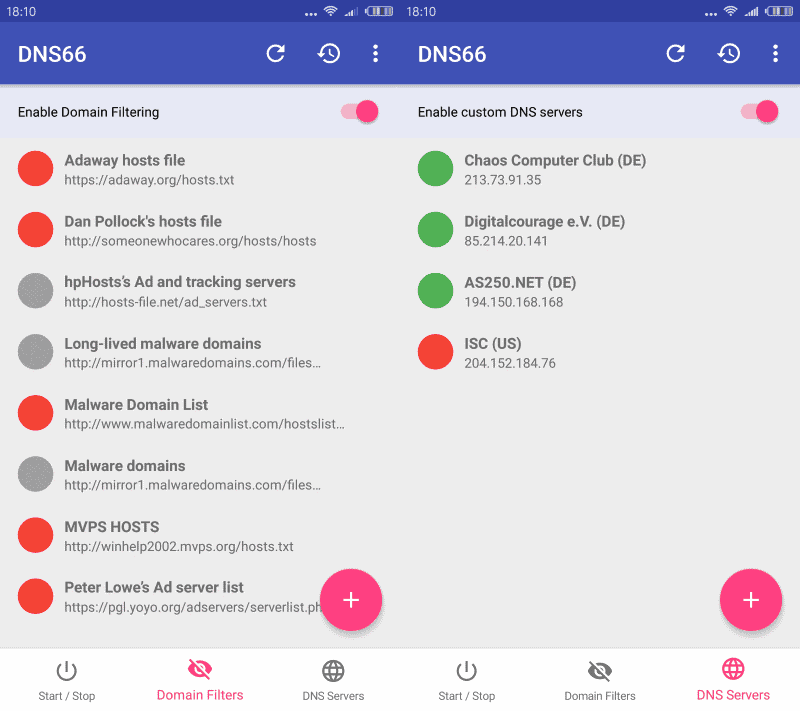
- Select DNS Servers and either enable or disable custom servers, or use of DNS servers the app ships with completely. The servers the app ships with are no-logging DNS servers operated by the German Chaos Computer Club and others.
- Open the Domain Filters listing and enable or disable the filter lists that you want to use. A couple of lists like the MVPS Hosts file or Peter Lowe's Ad server list are selected by default. You may add custom lists by specifying a URL or host. Also, you may choose to deny, allow or ignore those.
You need to tap on the refresh button in the main interface once. This downloads the latest filter lists to the local device. Once done, long-tap on the start button to start the service.
You will get the usual DNS connection query by Android which you need to accept. Once that is out of the way, you can verify that DNS66 is up and running by opening the notification area on your Android device.
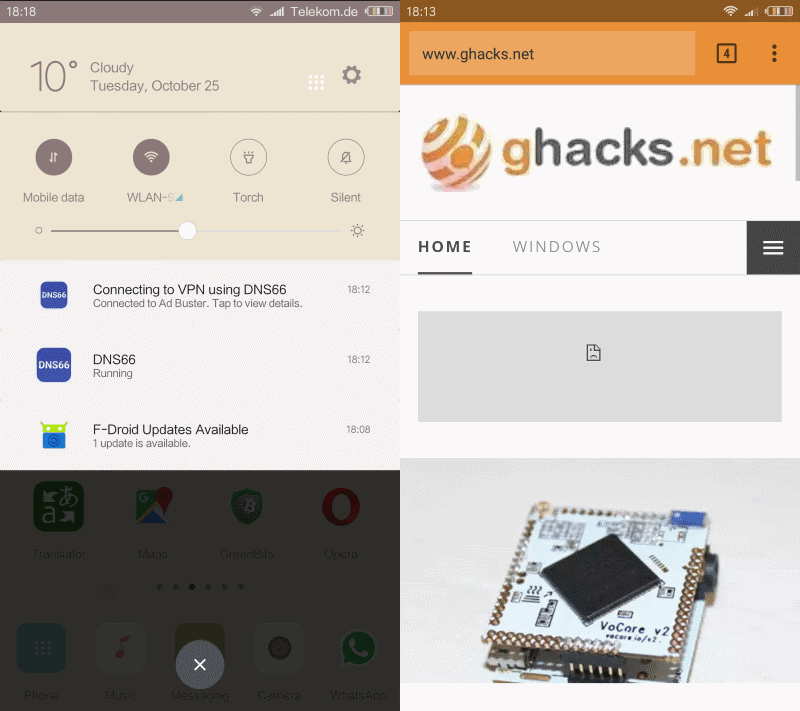
You should see that the device is connected to a VPN using DNS66, and that DNS66 is running as well. Test this by visiting Internet sites. You should not see ads or other elements that you have selected for blocking in the application.
Caveats
There are a couple of caveats currently. First, it is difficult to whitelist sites. As a webmaster, I'd like to encourage you to whitelist sites that you visit regularly to make sure they are around for a long time.
Second, the app does not support automatic updates currently. This means that you will need to tap on the refresh button regularly to load the latest filter definitions. Also, IPv6 servers and host files containing just host names are not supported just yet.
Closing Words
DNS66 is an easy to use blocking solution for Android device. It is easy to set up filtering and most of it is automated after the initial setup. The app could use better whitelisting, and some improvements in regards to the caveats listed above.
























This is working excellent on OnePlus 5t mobile and Mi note4, no ads from apps and browser, I tried with other aps it didn’t work, DNS 66 working good
Better use personalDNSfilter
http://www.zenz-solutions.de/personaldnsfilter/
Thanks for the hint!
overall seems smaller footprint in sense of size and memory usage. It is also easier to use as far as I can see.
It also uses the default DNS servers for up stream which I prefer.
I have ads enabled on your website, because Ghacks is one of the last truly informative websites on the internet, without click-bait titles and things like that, so this is a good opportunity to let you know that there are some adult services that advertise on your website (screenshot at https://i.imgur.com/DKoXApr.png ). I don’t really mind them, but I guess some people might be turned off because of that and often such ads point to malware.
Would you say the site is a legitimate site (dating maybe)?
After taking a quick look it’s a sex chat site. It’s not illegal, it just tries to make users subscribe to a paid sms service which costs 6,15zl (about 1,5€) 3 times a week (per their ToS http://archive.is/gAubl ). It’s a popular ‘business model’ in Poland, as it’s mostly kids that subscribe without reading. But it’s harmless otherwise.
I didn’t look into the free period they advertise (b/c of uMatrix) so I don’t know if it already requires subscribing, just defers the payments or not.
Thanks for letting me know, I try to keep an eye on that and see if I can do something about it.
I’m rooting and customising an HTC One M9. If I can get this to work, sounds good!
Martin, not Martini… Sorry about that.
Martini, I was intrigued when I read your article, and decided to give DNS66 a try on my non-rooted Nexus 6P running Android 7.0.
Frankly, I was disappointed with the results. I found DNS66 blocked far fewer ads in my browsers than (non-rooted) Adguard, and had virtually no effect on in-app ads.
I have since uninstalled DNS66, and re-enabled Adguard, but I will keep this on my radar to track and test future improvements.
It all depends on the filter lists that you enable for the app to make use of. Have you tried adding more?
I’ve had DNS66 in all my Android boxes and never had a problem. I happy with it.
Yes, I actually loaded in everything available, did the proper refresh/restart, and it made no difference. I find this weird because I have experimented with hosts lists before on this same phone, including some of the same ones offered by DNS66 and had much better results than this time around. Can’t explain why it didn’t work this time, but like I said, I’m game to try it again another version or two down the line.
Nice! Thanks for the review, Martin.
Was previously using Block This, which is also open-source, but the DNS requests are routed to the developer’s DNS server. DNS66 is similar, but also gives us the option to use the default DNS.
Is it also blocking In-App Ads?
It should if the ads use servers that are on a filter lists.
must have android 5 or newer