How will Microsoft fix bugs that security updates introduce?
Microsoft switched how updates are delivered to the client operating systems Windows 7 and Windows 8.1 -- and also server operating systems -- in October 2016.
Updates were provided as individual patches, and classified as security or non-security updates in the past. This meant that users and administrators could pick what they wanted to install on the system; excellent to avoid any Telemetry updates or other updates designed to introduce unwelcome functionality or changes to the operating system.
Also, great for troubleshooting as it meant that you could remove problematic updates while keeping every other update installed.
From October 2016, updates are delivered as so-called rollup patches. Microsoft offers a security-only rollup patch which includes only security updates, and a monthly rollup patch which includes security and non-security updates.
While the system is not in full swing right now, individual security patch downloads are still available on the Microsoft Download Center, it leaves users and administrators with just three choices:
- Block all updates.
- Install only the Security rollup for each month.
- Install the monthly rollup.
So, if users or admins select to install only security rollup updates, they won't get any of the non-security updates.
There are two issues with the way these things are handled apart from the obvious one that users won't be able to install feature updates that they want, unless they install any other patch that Microsoft adds to the rollup updates:
- Will Microsoft separate security and non-security updates strictly?
- How are fixes for bugs that security updates introduce handled?
Clear distinction between security and non-security updates?
Security updates should be included in the security rollup for each month, and non-security updates in the monthly rollup.
Users who want to keep their system secure can do so in theory by only installing security patches. The past has shown however that Microsoft did include non-security updates in security patches.
In March 2016, it released MS16-023 which installed new "Get Windows 10" functionality along with the security fixes.
Since it has been done before by Microsoft, there is a possibility that the company will push non-security updates by adding them to the security rollup patch for a given month.
To play devils advocate, Microsoft could add Telemetry patches to the security rollup update. This would put users and administrators who install only the security updates in a position that they cannot escape from. Either install the security rollup to keep the system secure but deal with the unwanted patches, or don't and leave the system open to attacks.
Fixes for bugs that security updates introduce
How will Microsoft handle bugs that are introduced by security updates? Will Microsoft add patches for those bugs to the security rollup of the month, or will it add those only to the monthly rollup update?
The former would mean that non-security updates are added to the security rollup update, the latter that users who only install security rollups won't get those patches.
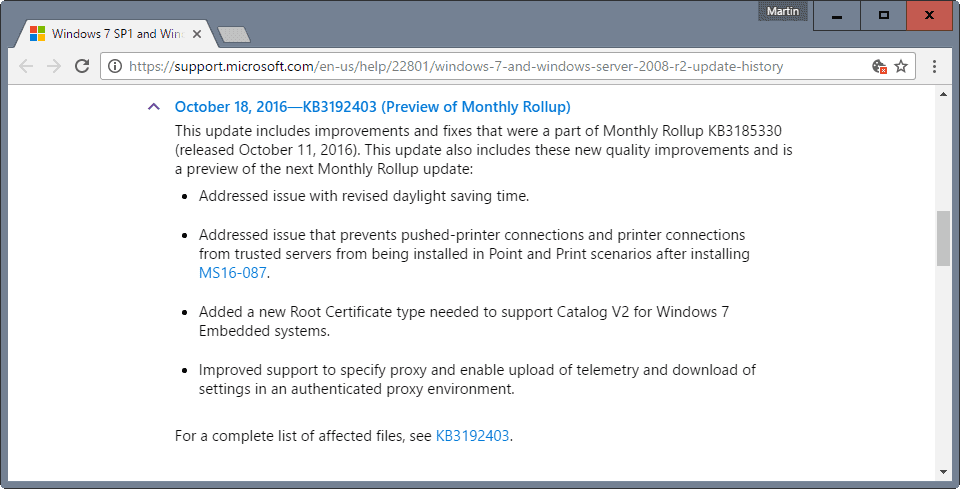
The security update MS16-087 introduced a bug that prevented "pushed-printer connections and printer connections from trusted servers from being installed in Point and Print scenarios".
If you check the changelog of the November 2016 monthly rollup preview which Microsoft published on Tuesday, you will notice that it includes a fix for that issue.
There is a third possibility, but it seems unlikely: Microsoft could update the security patch so that the issue that it introduces gets fixed by it.
Now, that does not mean that the update won't be added to the security rollup update for November for affected operating systems. We don't know if that will be the case, but will monitor the situation closely. (via Ask Woody)
Now You: What's your take on these updating changes?



















I had installed the latest nov update rollup on my win 7 64 bit the other day and by a miracle i put it back to normal. The cd door in my comp would open on its own every 5 min and the comp would not shut down until it performed certain functions. Wish you all luck
Hmmm
I realize what I am about to say is a bit far fetched. But, in light of the gigantic uproar from Microsoft’s user base and the obvious complete indifference to it, perhaps the real reason for all of this nonsense lies in another direction. Clearly the powers that be do not want a well informed citizenry. Currently thanks to the PC, the internet and dare I say the likes of Microsoft, citizen access to underlying facts and figures was until very recently at such high levels that truly informed decisions were within reach of the average citizen. Since the start of this presidential election cycle that access has been curtailed significantly. Witness virtually all 4 major search engines now actively controlling and manipulating searches and the social media sites actively censoring comments at here to fore unimaginable levels.
Obviously as the number of users that refuse these “roll-ups” increases the damage done by hackers (many of whom have been now been identified as state sponsored) will eventually reach a point that many individual machines will be rendered essentially useless. What if the powers that be want to create an online environment that is so fraught with “danger” real or imagined, that people, begin to limit their time online or turn away from the internet all together? Seems to me what Microsoft is doing is a great way to make some variation on this theme happen. What is that old saw? just because your paranoid, doesn’t mean they are not out to get you……………
Most banking transactions in the Netherlands are conducted online and therefore it’s essential that users have the latest security patches installed, but those are the only ones I’ve been installing on my Windows 8.1 system.
But now I wouldn’t even consider installing any of the so-called “reliability updates” since I note from the October preview of KB3192404 that it contains telemetry updates, quote: “Improved the upload of telemetry and download of telemetry settings in an authenticated proxy environment.” https://support.microsoft.com/en-us/help/24717/windows-8-1-windows-server-2012-r2-update-history
It makes me so angry that Microsoft seems to think it has my express permission to snoop on everything I do on my own machine in the same way it does on Windows 10 and this machine will be the last one with a Windows OS that I’ll consider buying when support expires in 2023.
I welcome all Windows updates. They have all installed successfully for me on a 5 year old Dell XPS 8300 desk top, well maintained. Perhaps I’m just one of the lucky ones but I’m thanking my lucky stars anyway. Running 1607 Build 14393.351
Bigger than 120 MB is too big for me and will be ignored, hidden or completely blocked. Don’t forget that a patch whether it’s a security patch or a non-security one was originally supposed to fix a problem, bug or introduce some incremental improvement. The original purpose of the “update” is now completely gone. What we do today is mindless updating that doesn’t bring any meaningful improvements compared to its size or the time it takes to install it or the resources it consumes on the device.
That these patches became so ridiculously big, out of control abusing your internet connection and wasting your disk space, causing unnecessary writes on SSDs and always breaking something is nothing but an engineering failure of Microsoft. I choose to not install this crap constantly on my machine. It brings nothing of value. When it was reasonably sized, installed quickly without causing any productivity loss, did not break anything and actually did something useful, it was worth it. Thanks to Microsoft for redefining the meaning of the word update. It now takes over your important tasks, wastes a shitload of your time, often breaks something and doesn’t do anything particularly useful anyway.
@Undecided
No, apple has done everything msoft is doing now, for years.
They have full control over your computer and have already
deleted files on peoples computers. If I remember correctly
they did it for – what they called – security reasons.
Telemetry data is only one small part of what is sent from your
computer to apple. Every search, everything you type and
data on every program you use is sent to apple, as is every
spoken word and gesture.
I’d say msoft have had a close eye on apple and is now doing
exactly the same.
I use OSX (not the new MacOS) and it can be made private.
Using location services allows apps to determine where you are, and time can be set automatically from an Apple server. However, if a user is concerned about privacy these services can be turned off. In addition, the firewall can be set to block all sharing services. There are specific privacy setting in “System Preferences” that allow the user to turn off diagnostic/usage telemetry and app crash reports.
Unless Apple is completely disregarding its own privacy statement and lying about OS settings I think the Mac OS is OK.
Privacy in Apple’s Safari web browser can be tricky. I think it depends on the features you select. You can set Safari to deny all website data and have that choice overridden. I prefer Firefox.
The only things I’ve ever had deleted were Apple’s screen savers by an OS upgrade.
If you’re talking about iOS then yes, however if you’re talking about macOS then perhaps a citation is needed as everything I’ve read seems to indicate your making false claims.
Good Lord. It’s years that I never update except for offline Service Packs.
Ditto
Maybe someone can help me out. After watching the debacle with Microsoft’s update issues and their unbelievable sneaky ways to push Win10 on me I am wondering if Mac (Apple) has a better attitude towards their customers or not. I would be glad to hear about the experience of Mac users (laptop). Please do not turn this into a war between Windows or Apple fan boys. I know the machines are more expensive but I wouldn’t mind if a decent company stands behind the product. I would like to get away from Microsoft as soon as possible as I have lost complete trust in this company but do not want to end up with another daemon after having fired his ugly brother. Thank you.
Excellent write up Sebby, even though I’m not a Mac person it’s refreshing to read what seemed like an honest opinion on both the pro’s and con’s of owning a Mac, thanks for taking the time do it.
YW and I hope it helps those who might be on the fence. No doubt about it that with Mac the price you pay is, well, money, for new Macs. My oldest Mac is a lovely 2010 Mac Mini, now running Windows XP but capable of running the latest. So, eight years isn’t a bad estimate of their useful life.
And yeah, privacy is totally under your control–disable automatic downloads, disable “Spotlight Suggestions”, disable Siri, disable Diagnostics & Usage (AKA telemetry, and it actually asks you this during install/setup). It’s a nice universe, if you’ll stomach Apple’s wily ways with new hardware.
U can expect practical use of a new Mac cptr for about 5 years b4 Apple will intentionally make it obsolete, eg cannot be upgraded to the latest MacOS, the latest apps/programs on Apple’s App Store will not support yr “obsolete” 5 yr old Mac cptr, no spare parts available, etc = Planned Obsolescence. IOW, u will need to buy a new Mac cptr after about 5 years.
……. This was one of the reasons, consumers had flocked to buy Windows cptrs. Some Win XP cptrs r still running well after 13 years when M$ ended support for Win XP in 2014.
.
So, the choice for u r; buy a Mac cptr n run it for 5 years only or buy a Win 10 cptr n run it for about 9 years or more.
.
If u only do basic stuffs on the cptr, eg read online news, send emails, stream videos, shop online, light office work, etc, free Linux is a good choice n it will run until the cptr dies.
Well, I’m a Mac user since 2008 or so, and I think you’re in better hands with a Mac. It’s how I escape from Windows. I wish more people would try them out, especially those who just want a computer that works. It does all the things you’d need, has a good (but not vast) selection of free and paid software for it, runs lots of Open Source (Unix underneath, great for developers), it’s not Windows, you don’t have to fiddle with it just to get it running, the machines are of good quality and have decent longevity (and consequent resale value), and Mac OS is a general-purpose OS that, although it’s frustratingly opaque sometimes, runs exceptionally well on Apple’s hardware. The first-party apps are useful and the integration of hardware and software is a breath of fresh air compared to anything you’ll get on either Windows or Linux, out of the box.
Now, of course, Mac is not perfect. Chiefly, nowadays, this is because Apple makes money from hardware, so you need to understand that, like their mobile devices (which are, more and more, influencing the design choices in Mac OS) Macs have a planned life expectancy under Mac OS. You don’t need to upgrade the OS if you don’t want to, but Apple always offers it for free if you do. But since they’re basically X86-64 PC hardware, you can run Linux or Windows on them to make them run for longer than Apple supports them, or continue using older OSs for two years after they are replaced, with security updates. Apps run from inside or outside Apple’s store, but Apple expects developers to pay to sign their apps; you can override this, but this is another way that Apple controls revenue. And quality control has been slipping lately, but on the Mac it’s especially noticeable as Apple are focusing their efforts onto their mobile platforms, which of course make them a lot more money. Some people take issue with Apple’s different ways of doing things; I say it’s something you learn, or learn to appreciate, and this is nothing to fear, but I’ve lost count of the number of people who, for example, say they hate iTunes. You can always use alternatives, naturally. The Mac is not “closed†as iOS is, but it is also fair to say that Apple caters for the 95% at the expense of the 5%, so you tend to find yourself in the deep end more often than on Windows (but not Linux) if you have particularly advanced needs, often using the command line in Terminal.
So, is it better than Windows? Hell yeah! But does Apple respect you? They’re a giant now, selling iPhones. I can’t in good faith say I’m happy with Apple’s direction, but I’ll take the Mac over Windows as it currently stands any day, especially if M$ continue this reckless disregard for user control over their updates and privacy, both of which I’m fairly confident Apple won’t change. For me, Macs are the least worst option. I run Windows and Linux in VMs under OS X Yosemite, which is still in support but is two generations behind the current releases; I’ll upgrade to the newest release once I’m convinced the bugs are ironed out, or I’ve found the workarounds and Yosemite is no longer supported for security.
Over to you. :)
I am very grateful for the expressiveness of your answer. Can’t ask for more and combined with the other posts it gives me a good idea what to expect from Apple.
I think I will give it a shot after having some research done on Macbooks, maybe a good time to buy one would be around Black Friday.
There is probably only one thing I do not care much about: it’s the planned obsolescence. Still, if that would be the only trouble I could and would live with it.
JM in his post stated that Apple is doing pretty much the same nasty stuff that MS is pulling (or vice versa) on their customers with telemetry and much personal info being send to them. I will have to take a good look into that because this may be just the only “killer” of the deal. As I wrote in my question I have no desire to exchange the daemon for another devil. But we will see.
Thanks to all of you for helping me out and giving me really good answers. Would be highly satisfying for me being able to say goodbye to a company like MS.
I had my take on Microsoft’s updating changes, which was to try to continue installing individual security patches from the Microsoft Download Center, and if those stopped being available, to install security-only roll-ups … always after vetting them against real-world reports of problems. But my take didn’t matter. I had set Windows Update to “download updates but let me choose whether to install them.” Microsoft apparently decided that merely viewing the list of pre-checkmarked “important” updates and failing to uncheckmark them before closing the Windows Update window meant that I had chosen to install them, and they got installed when I shut down the computer. (I never clicked an install button.) The same thing happened on one of my father’s Windows 7 Enterprise laptops. Another “accident,” like when some people “accidentally” got updated to Windows 10 without their consent? “My” failure to correctly understand the user interface, like when people “misinterpreted” the the red X button on Get Windows 10 windows to mean cancel and clicked it instead of a small link in the middle of the page? Except that this time canceling had to be done by uncheckmarking all the pre-checkmarked updates? [Needless to say, I’ve changed my and my father’s Windows Update settings to “check for updates but let me decide whether to download and install them.”]
I’ve previously mentioned on Ghacks that if Microsoft made it too burdensome to continue running Windows 7 until end of life in January 2020 I would move to Linux, and I think I’ve reached that point. I’ve been extremely busy recently, but in my limited spare time I have been experimenting with various distros in VirtualBox and have whittled down my potential candidates to Linux Mint (Cinnamon) and PCLinuxOS (KDE). I probably eliminated some distros unfairly simply because I couldn’t get VirtualBox guest extensions installed for them and thus couldn’t get a proper screen aspect and resolution or access my VirtualBox shared Windows folders. (Note to Linux distro developers: If you want to woo Windows users, make sure that using your distro in a virtual environment is as easy and painfree as possible.) Anyway, Linux Mint 18.1 is due out pretty soon, and it will supposedly include both Flatpak and Snap (~sandboxed, ~installed-portable app) support, promising the eventual ability to run the latest versions of a greater number of apps without dependency conflicts. I already have new hard drives for the install. (I’m not doing a dual- or multi-boot and I’m not burning my Windows bridges behind me in case I encounter a major problem using Linux.) So, when things slow down for me, and Linux Mint 18.1 has come out and been vetted by real-world users, I’m going to install either Linux Mint or PCLinuxOS, copy my data, and switch to Linux. The only things I’m certain I’ll be giving up is the ability to manage my iPod (which I never do anyway) and the ability to update my Garmin GPS (which I definitely do). For that, I can either swap in my Windows drive or borrow a friends’ or relatives’ computer. (Note to Garmin: Get with the program. Your software is based on Linux so release a Linux or Web updater already.) Okay, and when I buy a new computer, I’m going to have to make sure its UEFI and hardware haven’t “accidentally” been designed in a way that prevents Linux from being installed or working properly (as with the Lenovo Yoga 900 and 900S, to name only the most recent instances).
So I guess my new take on Microsoft’s recent updating changes is that I am actually, really, truly going to switch to Linux. And it’s Microsoft that kept egging me on and gave me the final push.
@A different Martin +1
Last night our Netflix and Youtube, to the TV was slow to non existent. I am using an old Acer laptop running the Vista it came with but pared down to the basics and “Never check for updates” in the Update page.
Did some quick research and Linux was not having the same issues with the incoming DSL, so checked the wifi stream to the Acer. It was pounding (146MB downloaded at that point) the Acer from a msoft link. I shut it all down and restarted about ten minutes later and during the boot up the pounding started again. Tried another shut down, wait and restart and again and same. Finally just left it running and went back to using the FireTVstick for the evening. Hate that thing. :)
About an hour later the Acer was happy. I have no idea what was downloaded so this morning I rolled it back to the bare Vista image I had made few weeks back and so far no more downloads. But will see what happens over the next few days.
Msoft definitely not playing fair or being honest. WOW, there’s a revelation.
Microsoft will do what its been doing with Windows 10 cumulative updates, keep issuing patches for previous patches hoping to eventually fix the fix, I’ve lost track of what the record is for reissuing a patch but IIRC it stand at something like six and still counting.
It seems no one told Microsoft that patching something as complicated as an OS doesn’t result in 100% success rate when dealing with millions of heterogenous systems, that’s only made more complicated when you start trying to fix more than a single issue.
I don’t update at all. I use windows only for gaming. Better way to get security without headache dual boot with linux.
No rollups on my 8.1 machine. I just don’t want to risk it. I have been so careful with all the patches I installed before october
I really dislike what MS has done. Once again it is yet another incentive to start looking for another OS.
I’ve decided to avoid all rollups, security only included. I still download/install individual updates concerning i.e. .Net Framework, latest of which “Update for .NET Framework 3.5.1 on Windows 7 SP1 and Windows Server 2008 R2 SP1 for x64 (KB3188730)”. I may be wrong, taking an inconsiderate risk, but that will be my policy regarding Windows Updates.
I do not want so-called rollup updates, mainly for the reasons mentioned in this article. I’ll manage I believe until January 2020 or before to keep the machine healthy. Or after since avoiding WinUpdates will sort of diminish Win7′ lifetime imperatives. Whatever, I’ll quit Win7 one day or another.
But avoiding Windows Updates is similar to vegetarianism : avoiding is not enough if what is missed for the worse is not substantially replaced by what is missed for the best (eating potatoes and apples all day long will ruin one’s health). Hence, have a good, a very good, the best computer overall security you can imagine and stay as always extremely cautious on that wild, wild … Web.