Fakenet: monitor network traffic of programs
Fakenet NG is a free program for Microsoft Windows devices that allows you to monitor network traffic of programs by simulating a fake network environment.
Designed specifically to find out about malicious programs, it can be used for other purposes such as finding out if a program phones home, which executable file it uses for that, and to which servers it tries to establish connections to.
While a firewall provides you with some of those information as well, Fakenet does provide you with additional information that firewalls usually don't offer.
Fakenet
The tool allows you to intercept and redirect all or specific network traffic while simulating legitimate network services.
Using FakeNet-NG, malware analysts can quickly identify malware's functionality and capture network signatures.
Penetration testers and bug hunters will find FakeNet-NG's configurable interception engine and modular framework highly useful when testing application's specific functionality and prototyping PoCs.
Here are a couple of things you need to know about Fakenet before you start the program:
- Fakenet takes over DNS on port 53
- It listens to the TCP ports 80, 443 and 25
- It supports DNS, HTTP and SSL protocols.
This means that any traffic that goes through these ports will be recorded by Fakenet, but it won't go through (as it ends in the fake network environment).
It makes sense to stop most programs that connect to the Internet prior to running Fakenet. Basically, you get the best results when you just run the program you want to analyze.
You will still get some noise from Windows itself and maybe background processes that you cannot just terminate.
The program uses ini files which you find in the config directory. You may add ports that you want to monitor, or block ports from being monitored using these files.
The config file uses a simple syntax. It is probably best if you simply copy one of the available presets and edit it to add ports that you want the program to monitor as well.
You may use the "redirectalltraffic" preference to capture traffic on all ports. This can be useful if you are not sure which ports a program will use for communication.
Please note that Fakenet will ignore all other ports. If a program communicates using different ports, then it won't be logged by the application.
Once you are done with all of that, you may run Fakenet NG. The program is provided as a 32-bit and 64-bit application.
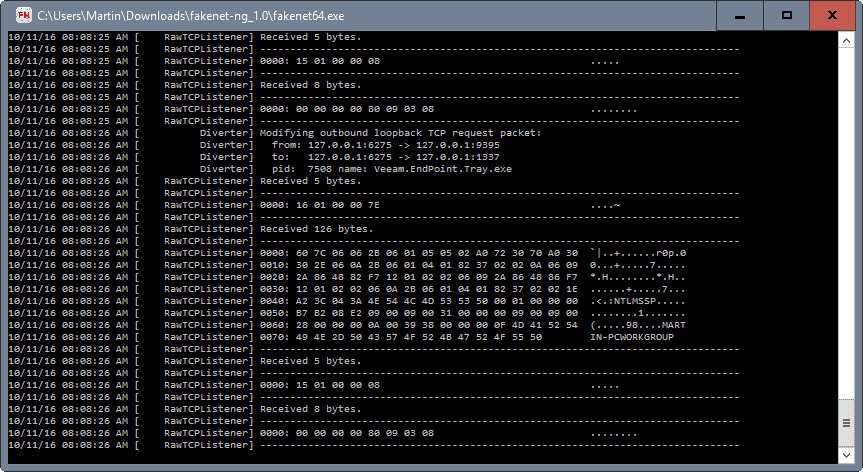
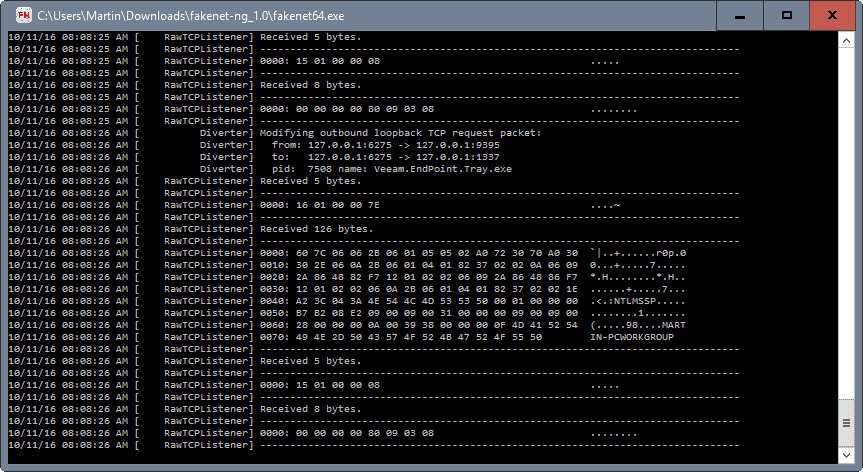
All network traffic that it captures is echoed in the program interface. This may not be overly usable considering that there is no pause option available.
Fakenet saves the data to a pcap file however which you may open in programs like Wireshark that support it.
Closing Words
Fakenet NG is an interesting program to analyze the network traffic on select ports or all of them on a Windows machine. Designed to analyze the network activity of malicious programs, it can be used to monitor any program that runs on the Windows machine.
Since it saves the logged data as pcap files, it is best to analyze the findings in programs like Wireshark as it will make things easier.
The main difference to firewalls is that Fakenet NG will provide you with additional information that firewalls may not provide you with.


























Sweet tool.
Thanx bud for this finding.
I left any AV Solution. All those false positives are worst than getting a real virus and removing them. They just look at what a program does and – in this case – they mark the exe or some dll as malicious beacuse it modifies some standard-vanilla os settings.
Yes, it’s injecting but for good and who installs it is supposed to know this. Really, I get more false positives than real warnings and I can trust more a removal tool as ESET or Emsisoft.
360 Total Security say this file have a Troyan (HEUR/QVM10.1.0000.Malware.Gen).
False Positive.