QuadRooter Scanner: is your Android phone vulnerable
QuadRooter Scanner is a new application for Android devices that scans a device and tells you whether it is affected by the recently disclosed QuadRooter vulnerability.
QuadRooter is a set of four vulnerabilities affecting Android devices using Qualcomm chipsets. Disclosed on the Check Point web blog on August 7, 2016, the vulnerability is said to affect close to 900 million Android devices that are in circulation currently.
Attackers may exploit the vulnerability using specifically prepared applications. The app would not need special permissions according to the researchers, and could give attackers complete control over an Android device.
If exploited, QuadRooter vulnerabilities can give attackers complete control of devices and unrestricted access to sensitive personal and enterprise data on them. Access could also provide an attacker with capabilities such as keylogging, GPS tracking, and recording video and audio.
The researchers released a short list of affected devices that reads like the who is who of the Android world. Included are the Google Nexus 5X and 6, the new Moto X, The OnePlus One, 2 and 3, the Samsung Galaxy S7 and S7 Edge, The Sony Xperia U Ultra, the LG G5 and G5, and various other devices.
The list is incomplete however, and there was no way of telling up until recently whether a particular device not listed is affected by one of the four vulnerabilities.
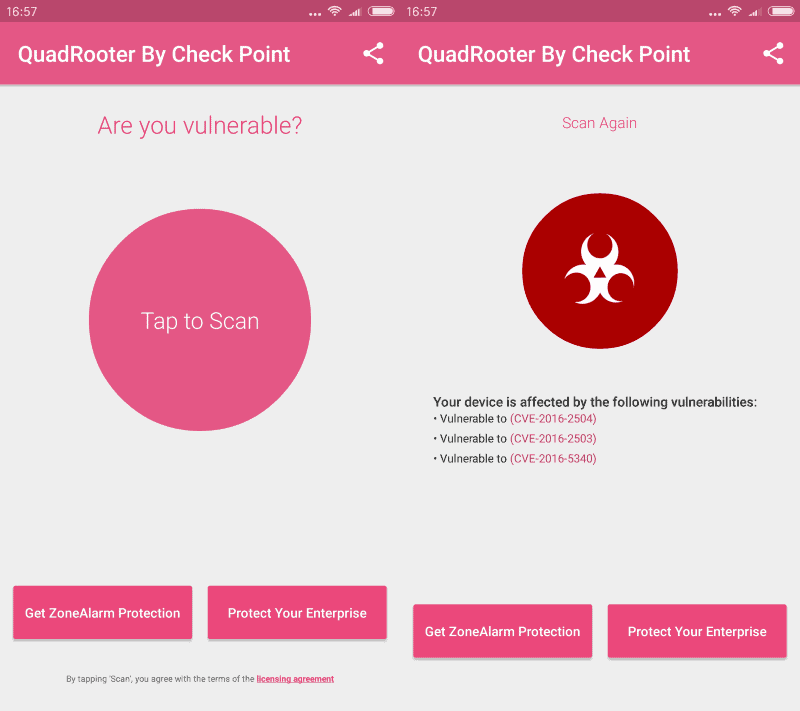
QuadRooter Scanner
QuadRooter Scanner changes that. It is a free application for Android devices that scans the device it is run on to find out whether it is vulnerable to one, some or all of the four vulnerabilities discovered recently.
All it takes is to tap on the scan button after you have installed the app to run the scan. It takes less than a minute to complete, and will list whether the device is vulnerable to some of the vulnerabilities discovered.
Links are provided to the vulnerabilities the device is affected by which may be useful when researching the vulnerabilities.
There is little that you may do however if the device is affected. While you may be more careful than usual, by not installing any apps from outside the Google Play store, and even then making sure it is created by a legitimate company, there is no direct option available to protect the device fully.
It is up to the device manufacturer to release a timely patch for the vulnerabilities the device is affected by. The past has shown that it will take some time before even the companies that care the most push out patches. For some devices, patches may never be created and there is nothing that users can do about it other than switching devices (preferably from a company with a better track record).
Now You: Is your phone vulnerable?
























Just bought a Samsung Galaxy J5 (2016) last week and after running the Checkpoint scanner, the device is vulnerable to the CVE-2016-2054 vulnerability. This particular phone has only been on the market for three weeks too.
For Sony Xperia users: FWIW, three days ago Sony Mobile officially acknowledged the vulnerability, stating, “We are aware of the ‘Quadrooter’ vulnerability and are working to make the security patches available…”.
This is from Xperiablog, which, if you’re a Sony Xperia owner, is definitely worth subscribing to, or at least checking regularly (xperiablog [dot] net). Full blog post below…
Xperiablog post:
“Earlier in the week we reported on a new Android vulnerability affecting smartphones using the Qualcomm chipset. A number of users have been asking what the manufacturers plan to do about this (notwithstanding the fact that any fixes are due from Qualcomm itself). Well, Sony Mobile has responded to questions about the vulnerability by highlighting that they are “working to make the security patches available within normal and regular software maintenanceâ€. No specific timelines are given, but Sony reminds users to stay safe by only downloading apps from trusted app stores. See the full comment below.
Sony Mobile comment on Quadrooter Android vulnerability
“Sony Mobile takes the security and privacy of customer data very seriously. We are aware of the ‘Quadrooter’ vulnerability and are working to make the security patches available within normal and regular software maintenance, both directly to open-market devices and via our carrier partners, so timings can vary by region and/or operator. Consumers are recommended to continuously upgrade their phone software in order to optimize performance of their Xperia™ smartphone. Users can take steps to protect themselves by only downloading trusted applications from reputable application stores.—
“For some devices, patches may never be created and there is nothing that users can do about it other than switching devices (preferably from a company with a better track record).”
That’s a really clueless advice since all phone manufacturers abandon OS updates after 2 years max. And giving advice to change a 400-600$ device every 2 years is totally irresponsible.
Well what would your advice be then for users with affected devices? Sit it out? Ignore the vulnerability? Pray that the manufacturer will push out a patch?
Android devices don’t cost $400 or more. You may not get uber-quality devices, but solid devices. My Xiaomi Mi4C cost considerably less than that for instance.
Flasgships phones still cost in that range, and those are the one that sells the most still. Good advice would be to simply be careful and stop installing stuff outside the play store, and to raise our voice to make manufacturers accountable and to support their devices for a much longer time. Heck, I’d be all for a law forcing security updates for 10 years on any devices (equivalent to the car industry law that requires them to keep manufacturing auto parts for X years) That would probably slow down the amount of phone released every year too(which would be a good thing IMO)
Replacing devices as soon as a vulnerability isn’t patched is truly irresponsible in these days of global warming and diminishing natural resources(you know how much gallons of drinkable water is required just to make one smartphone?) And encouraging stuff like that is like telling device makers to abandon support even sooner. “Samsung exec: Hey, let’s boost sales of our newest Galaxy S57 by disclosing a serious vulnerability in all our previous models and making sure we spread the word that we won’t patch it! We can even count on tech blogs writer to tell people to change their device right away!”
I think you misunderstand me. If you want a patched device, and if the manufacturer does not update it, then you can only get a new device for that or, with some luck, install a custom ROM.
Naturally, you would not buy a device by the same manufacturer as you know that company’s track record of keeping you save.
Sure, you can live with a vulnerability, be careful and all. That’s fine, but it does not address the issue at hand at all.
Yes, manufacturers should not provide patches for a short period of time and jump to the next product forgetting about every other product they released before it.
I have a Galaxy Tab2 7 inch tablet that I purchased in 2012. I’ve never updated the OS on it. Running Belarc, it reports about 79 vulnerabilities, some of which are quite serious. I’ve had so many system speed issues after updating/upgrading OS’s on small mobile devices (esp iPhones) that I don’t dare update the tablet for fear of turning it into a turtle!! It would really be preferable, security wise, that I update the thing but if I do it just might become useless on account of speed issues.
I absolutely hate Samsung Kies as a tool and device manager. Anyone out there have an alternative to that, which would enable me to save my existing OS & apps, allow updating the OS and allowing a rollback if things are not good?
Thanks
Four vulnerabilities on a Galaxy S4 (SPH-L720) running Cyanogenmod 12.1 (Android 5.1.1)
just damn.
Yes, most android is (permanently) vulnerable, because of the non-updating. Better to be on a battened down xp machine. You read android architecture is different, you don’t need av, etc. You still need av to scan incoming, and something like Malwarebytes to keep a running check on your apps. I had an innocuous app that had been fine for months, then, immediately after its last update, Malwarebytes picked up that it had gone rogue, (trojan), and strongly advised me to get rid of it, which I did. (AV didn’t pick it up). Give yourself a scare, and download Belarc Security Advisor. Dream/Wish: a Linux distro which ran on android. The whole android updating thing needs to be overhauled by the providers.
Same those three are found on my Nexus 4 as well. Oh well..
I ran this scanner about 2 hours ago on my Nexus 6P, and was chagrined to find it had 2 vulnerabilities. Before I could even look up the details from the links in the scanner results, I was notified that I had a security update ready to install, so I launched that first. Running this scanner again revealed only 1 vulnerability remains. I can’t be sure but I fully expect Google to patch that weakness with the September security update if not sooner. In the meantime I will continue to practice safe smartphone usage as best I can.
The Nexus devices will be patched and maybe, in a couple of months, even the latestes Galaxy devices. All the other, forget it.
>But imho if the Android industry doesn’t get its act together over stuff like this (by unifying security update methods for a start) they’re going to hand the market back to Apple.
Yes, my next phone will be an Apple for this very reason, even though I think their products are overpriced.
I’m with you, mate. Though it won’t be to Apple – won’t touch their stuff for reasons well discussed. So where? Seems to me the problem isn’t with Apple, Android, Windows, etc. It’s with an industry that – whatever their claims for innovations and excellence – is currently intellectually moribund. Thinner products (as if that mattered a damn.) Updates to OS’s (except you can’t have it because your device isn’t compatible.) The industry isn’t a technological marvel – it’s a bloody mess.
My phone is a ‘dumb’ model – and it’s going to stay that way.
I do have an Android tablet – hate to be without it. But updates – especially security updates – seem to be a massive failing of the whole Android scene. I’m aware that different makers use different Android (though I fail to understand why.) But imho if the Android industry doesn’t get its act together over stuff like this (by unifying security update methods for a start) they’re going to hand the market back to Apple.
Like many, I often grumble about Windows – but at least a Windows update is a Windows update – it doesn’t depend on manufacturer and doesn’t vary from device to device.
Android is backdoored.
Always.
This is not the first unpatched, so far Qualcomm chipsets vulnerability. We had 2 month ago TrustZone kernel vulnerability.
So what can do you do if your Android device is QuadRooter vulnerable ? Nothing, as there won’t be any security updates to the majority of users, except maybe for the Nexus devices.
This is not the first unpatched, so far Qualcomm chipsets vulnerability. We had 2 month ago TrustZone kernel vulnerability.