Opera Software shareholders greenlight sale
The sale of Opera Software to a Chinese consortium for 1.2 billion US Dollars has received the required 90% shareholder acceptance rate.
Rumors that Opera Software was up for sale emerged as early as 2012 but nothing came out of the rumored acquisition of the company by Facebook.
It was revealed in February 2016 that a consortium of Chinese Internet companies, among them Kunlun and Qihoo 360, have offered 1.2 billion US Dollars for the Norwegian company.
Opera Software, best known for the Opera web browser available for desktop and mobile devices but more successful in the advertising business, announced yesterday that the 90% shareholder acceptance rate has been reached.
The offer period for the Offer expired at 16:30 (CET) on 24th May 2016. The preliminary result, which is subject to confirmation and may be adjusted, is that the Offeror has received acceptances of the Offer for in total 132,911,316 shares in the Company representing approximately 90.6% of the outstanding share capital and 90.9% of the votes in the Company.
While a preliminary result, it seems likely that the final acceptance rate won't fall under the 90% mark.
Acceptance of the deal by shareholders is an important step but it is not the last. Authorities in both Norway and in China need to approve the deal as well.
It is rather interesting to note that core Opera executives, notably Opera CEO Lars Boilesen and CTO HÃ¥kon Wium Lie, told TechCrunch that the decision to sell Opera Software was not made by them.
I have been working for Opera since 99, HÃ¥kon Boilesen said. He's No. 8; I'm No. 16. We've been with Opera for many years. We got listed on the Stockholm stock exchange in 2004. So basically, the shareholders they decided to initiate this process. It was kind of their decision. It wasn't our decision.
That does not imply that the executives don't approve of the decision on the other hand.
It is unclear right now how the deal will impact Opera Software's operations, but it would certainly help Opera Software in the Chinese market.
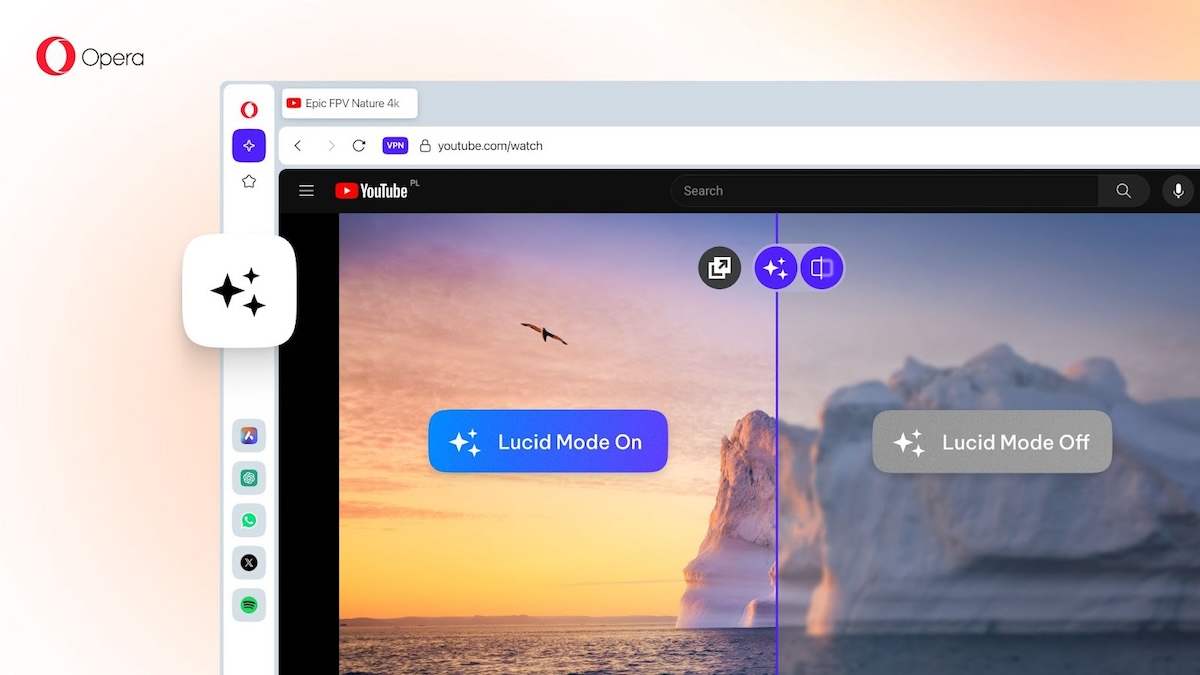
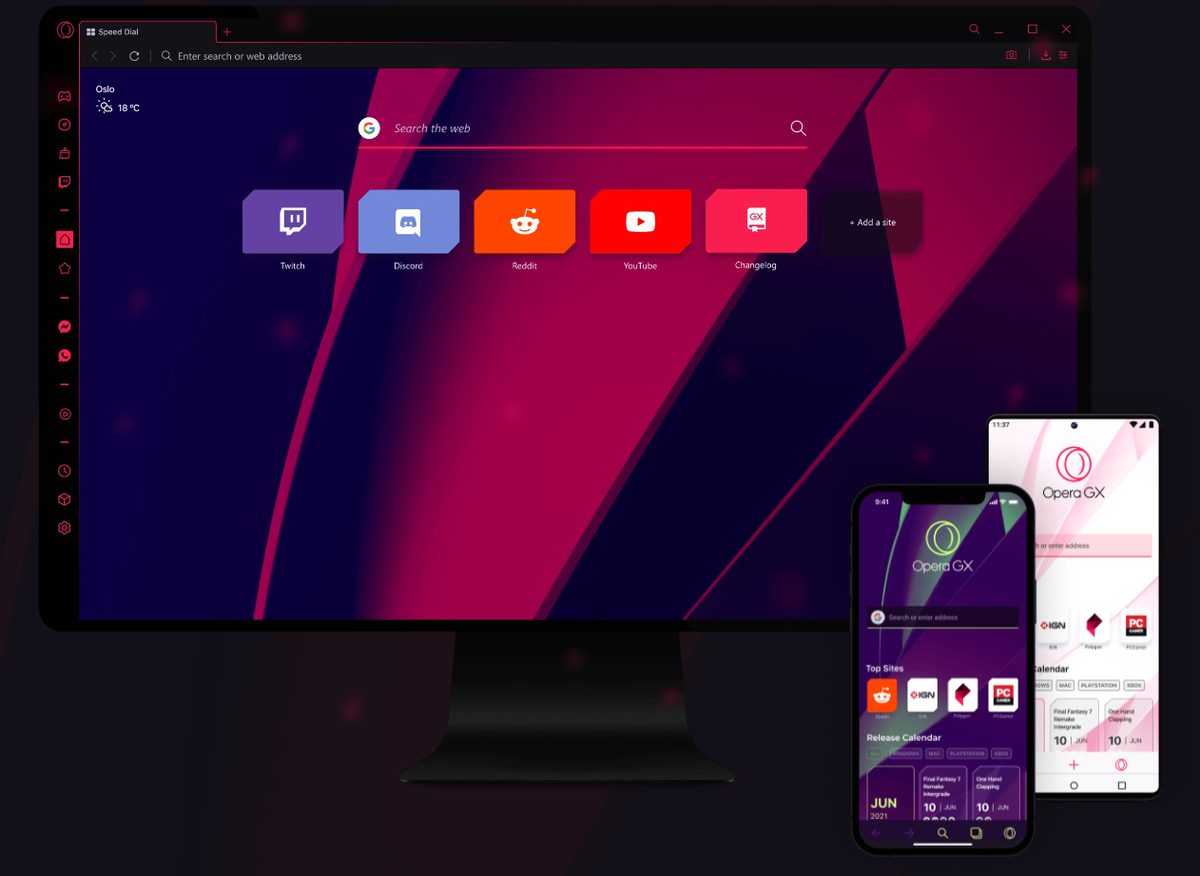
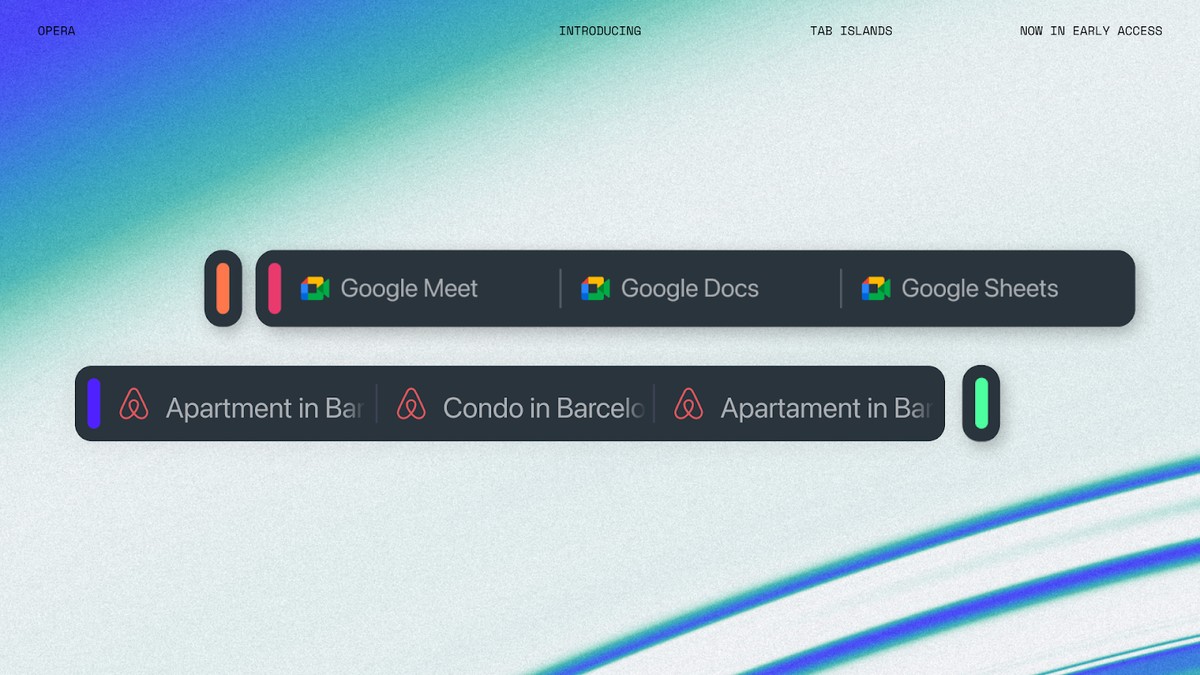
Opera Software has added several interesting updates to the Opera browser in the last couple of months.
Power Saver has been designed to reduce power consumption of the browser when the device it is running on runs on battery.
Opera VPN on the other hand is a built-in browser proxy to improve user privacy while using the web browser.
Now You: What's your take on the deal?















Opera.. The same traitors like Mozilla, sacrificing features, options and advanced users for being as Chrome similar as possible, in the hope to absorb many Chrome users to be also of relevance.
What they do forget, is that you can also be relevant if you are smaller and offer features for different users who are much more dedicated than simple users ever will be.
So, i am not sad for the loss of new Opera, the only one which was of relevance is old Opera.
Bye bye and be careful of the Chinese sharks, they do actually bite!
What’s wrong with using the legacy Opera 12.18? Can it no longer be trusted? One would think of it as more secure because hackers are busy targeting the big 3.
I still use Opera but this news is bad news, time to switch.
Opera is currently only my third browser on the desktop (Firefox and Slimjet being first and second, respectively), so it’s easily replaceable there. What worries me is that Opera mobile is my FIRST browser on my smartphone and I’d hate having to look for another one. I have already tried several mobile browsers and still find that Opera is the best. It’s fast, user-friendly and, above all, it DOES have text reflow (an essential feature, if you ask me). Most mobile browsers, including Chrome and many others, rely on webview to display websites. But Google, in its infinite wisdom, removed the text reflow feature from Webview a couple of years ago (see: http://www.androidpolice.com/2014/01/28/bug-watch-text-reflow-removed-from-webviews-in-kitkat-probably-not-coming-back/), so now Opera is one of the very few Android browsers that currently still have that feature. I think Firefox, through an add-on, has it too.
Vivaldi anyone…
Ah yes, a “Chinese consortium”… Forest Gump’s “Box of Chocolats” in the world of international commerce.
I’ve taken a mild interest in web browsers recently, especially concerning privacy. My interest has led me to some very unexpected conclusions. I reckon it will surprise nobody to find that not all browsers are created equal, or even close to equal. What may surprise folks is exactly what is actually stored with your browser.
Try this simple exercise: Find and view the “certificates” downloaded and stored with your browser. In Firefox, this will go something like >Options>Advanced>Certificates>View Certificates. Pay close attention to the certificates stored under “Servers” and “Authorities”. The list may surprise you. The first time I did this on my “primary” Firefox profile, I found several from the Chinese Government, Japan, etc. What the devil is all this? I wondered…
I never frequent sites related to the National Bank of China or it’s government, so where are all these strange certificates coming from?
After much research, I learned that my downloading files, files I needed (and so do you) for such things as drivers for my Gigabyte Motherboard, or my ASUS Wi-Fi dongle, or even my Samsung laser printer often install these certificates of authority. They also come in numerous other sneaky ways. Further educating myself found that they are all relatively harmless… Still, find your browser settings and do some digging. You will likely be surprised.
This has led me to another, what I think is a much more important conclusion: We are all doing this wrong. What I mean is, “we” (you and I) often speak in terms of such and such being our “primary” browser, and such and such being our secondary. I do. Firefox is primary for me, TOR is currently my second, or “playground” browser. We need to stop this way of thinking! Really, if privacy and security are your primary concerns, you should select one browser, and carefully configure that browser for just that… Browsing. No, I repeat, NO downloading on your primary browser! Not even a PDF file, not even from a “trusted” site. Turn off auto-playback of everything… Videos, FlashPlayer, etc.
A secondary browser, (or perhaps a portable version of your primary) should be used for all downloads, and really, even to view videos or Flash animations, etc. Keep both on your taskbar. It means some extra steps whenever you want to do something as innocent as downloading an updated driver (Primary browser used to research and find the file – Secondary browser used to do the actual download).
I’m still getting used to this way of working. Right now, I still use a fresh copy of Firefox as my primary, and it’s pretty locked down. It does have all my bookmarks, and it’s what I use to browse. If I need to view a video, download a file, or even fill out a Flash form or view an animation, I fire up my secondary browser and do a copy/paste from my primary.
Lastly, every now and then just uninstall and re-install the secondary browser… I choose to do this with each update. I’m thinking of using Vivaldi as my secondary. This is a different mind-set. Right now, it seems, you really can’t have “one” browser to “do it all”… If you do, you will end up not being as secure or private as you may think you are.
Use two browsers, and flush the second one periodically.
Now go and see what strange certificates are currently installed with your browser and tell me what you found!
Regards,
Mr. Joey
Mr. Joey,
I appreciate your comments to the point that I’ve saved them. Thanks for giving a trail to research, so many others spout rhetoric and never back it up. ;-)
It’s a shame that so many folks “think” that they’re going to get to be one of the über rich from investments (the reason they try to tear apart any dissenting views). If they ever bothered to go to an insiders conference on the stocks, markets, and taxes, they might have a clue.
And no, I choose not to transfer information to those who are too lazy to inform themselves with a little bit of actual work – pay for a conference yourselves. (This last addressed to all with the exception of Mr. Joey)
Mr. Joey, you mentioned “much research”. Can you point us to credible research that provides evidence that legitimate driver downloads are installing security certificates into browsers without the user’s consent?
@Tony
Very well. We’re leave it like that. I would be interested to know how your browser conducts communication with SSL or encrypted sites without the exchange and installation of security certificates containing the private key. I think it’s hilarious you believe “nothing” gets installed when you simply visit a site whose address begins with HTTPS. Very well. If you and I were prospective employers, and this were a sort of job related review, you would classify me as “misinformed”. I like that. That’s a very nice way of putting it. Since I’ve been in IT for 35 years, I think we should call it “Seriously misinformed” – Haha!
On the other hand, I would classify you as “Dangerous”.
The whole reason I brought up the issue of Security Certificates is because many people have taken to configuring their browsers to delete all history from one session to the next. This gives them a feeling of security. Sure, your browsing history may be deleted. However, what a treasure trove your Security Certificates hold. Every site you visit that uses encryption and/or secure sockets layer has a private certificate stored with your browser. It contains a private key which is matched to a public key on the server you connect to. A temporary additional key is also created for each session, and is only valid for that session. The keys are managed by Security Certificates. There is a certificate for EVERY site you visit that uses encryption (HTTPS/SSL). These certificates ARE NOT deleted as part of your browsing history.
If I were someone with bad intentions, and I could get a hold of your Firefox Profile, for example, I could find every secure site you use. Could I decipher the key? No, I could not. But I could garner the secure web address of every secure site you use… Where you shop and bank, etc. It would be an important step in hacking somebody’s identity.
Except of course, for Tony’s browser.
Nothing gets installed when he visits secure sites.
There is no trace on his browser.
According to Tony, I’m a nice old fart who is tragically misinformed.
But Tony? The information Tony is putting forth is actually dangerous.
Cheers and Good Luck,
Mr. Joey
Joey, I can’t quite tell if you’re a troll or a very misinformed person.
Unless you have active malware or a component of your system has a serious security issue, visiting a site does not ever install a Certificate Authority.
Just like you shown us that you don’t understand the difference between Java and JavaScript, you also don’t seem to understand the difference between a Certificate Authority and a site certificate.
Nothing gets installed on your computer when you visit a website unless something takes advantage of an exploit.
Assuming you’re not just a troll, you seem like a nice person. That’s probably the most important thing in life.
Where would you like to begin?
Browser security certificates are a function of HTTPS SSL encryption. Any site using SSL or HTTPS (or claiming to) is using encryption to, presumably, protect you. This is managed through certificates issued from what your browser considers a “trusted” authority.
How this plays out in the real world basically means that anytime you are connected to a site with an address beginning with HTTPS, you are using encryption, and there will be a stored certificate with your browser.
Quite often, the name of the certificate and it’s origin bear no resemblance to the name of the web-site. For example, I like to use Duck-Duck-Go as my preferred search engine. It claims to protect my privacy while performing searches. It uses encryption. The certificate installed in Firefox is titled “DigiCert Global Root CA”. An example I used in previous comment was ASUS. To download drivers for my router, ASUS uses a secure site, the title for that certificate is “Baltimore CyberTrust Root”… Not a clue it has anything to do with ASUS.
These certificates are installed automatically by the browser. No user confirmation is ever requested. No option to have a user approval is offered. (Firefox does have an option to notify you if a site requests a certificate FROM you, but not the other way around).
So I’m not sure how to answer your question. You could do as I did and perform search queries such as “What are browser security certificates?” and then read about Secure Socket Layer and HTTPS (Wikipedia has some good starting articles) or you can read a lot more about the companies that issue these certificates and what your browser considers “trusted” authorities… United States Homeland Security has several pages of information about that.
Seems to me, by the phrasing of your query, that you want evidence of legitimate sites installing security certificates without your consent.
Simply type “startpage.com” or “duckduckgo.com” into your address bar, watch HTTP change to HTTPS and bingo, you just installed a security certificate… Or rather, your browser did.
Further, the phrasing of your query seems to put me on defensive, by demanding I provide links to what YOU consider credible research. I call total bunk on that. I’ve been around a long time, somebody calling upon me to provide them credible research (of which they will be the judge) is the definition of a loaded question. You can never satisfactorily answer that type of query, so I’ll choose to ignore that bit.
I may be missing the mark concerning the tenor of your query. I’ll take that risk. I certainly don’t care if you agree or disagree with me, if you like or dislike anything I write, and as for credibility, I consider myself to be a credible source. One of the advantages of age is a resume of credentials earned during one’s tenure.
Regards,
Mr. Joey
Funny, all those who want to stay away from Chinese owned software because of presumed government spying, as if the US government does not do any spying nor forces tech companies to cooperate. And the likes of Google & Microsoft: innocent like choir boys, right? Talking about a blinkered view.
Anyway, I moved from Chrome to Opera when developer version 38 came out & have been very happy since.
A bad egg isn’t so bad when the others eggs are just as bad.
Nice logic.
I agree. Certain countries actively promote “patriotism”, which is just a fancy word for “stupidity”.
The sheeples in these countries think every other government out there is out to spy on them, but not their own governments.
Years later, the truth is disclosed.
Brain washing at it’s finest.
Bravo Tony !!
last nail in the coffin…
R.I.P. Opera
Better Dead Than Red [TM].
I currently use Opera, despite being disappointed when they changed direction after version 12. But knowing that:
1. hacking being actively and openly being promoted by the Chinese government
2. many Chinese companies known for backdoors in their products
3. seeing a huge proportion of hacking attempts coming from China on my servers
I’ll be moving away. Vivaldi looks very promising
I’ve not used Opera’s web browser since it was still at version 3.x, and I’m not at all likely to use it, so the deal won’t affect me much, but it’s my understanding that Opera also owns Fastmail (webmail services), so I’m curious to know who will be in control of that, or if the deal affects only the web browser?
No, Fastmail is sold to fastmail creators years earlier and it is currently not with Opera.
Opera should’ve waited until they see the profits after adding adblocking, VPN features in all/most of their products.
Also, selling to a consortium consisting of cheat & fraud Qihoo 360 will bring Opera down to hell in future. Also, Qihoo is ad lover and they will kill all good features or create problems within.
I loved the old Opera and still miss it. I lost faith in them so I never downloaded the new iteration. Then I saw its new look, and was glad I hadn’t been tempted to try it. Still, I must have been holding a little hope in my heart, because reading this just made me sad. Who would trust their banking to a Chinese browser?
I only have it as a backup browser, along with Edge, IE, Firefox, Maxthon and Slim Browser.
Great!!! I’m already out since last year.
Bummer. I haven’t used Opera for anything personal after v12 died (too many missing features and I find Chromium to be completely unreliable and unpredictable), but still is my secondary browser, so..
I tried using webkit/blink/pick-a-name based Opera but it’s just not the same thing – it’s just another Chrome clone with different skin. The real Opera based on Presto is already dead and this thing is just a sad imposter.
Never Opera again, I remember the ‘VPN’ story which is only a proxy. Nope thanks, wrong decisions over the years and now they try to copy Mozilla/Google. Skip !
I won’t touch Chinese software with a 10 foot pole, especially not something like a web browser.
I know it sounds harsh, but I’m simply acting on information that I see (lots of reports of government spyware etc.).
Why? What’s China gonna do to you? The government you should be concerned out it your own, as well as their allies.
I understand what you mean, I feel the same, and yet, we all have chinese hardware in our home routers and computers already…
That’s how I initially felt as well. And then I thought about the embarrassing record of Great Britain and the USA on these matters, and I think it’s equally unreasonable to trust anything coming out of those two countries.