A closer look at Opera's Browser VPN
Opera Software launched what it calls a Browser VPN or just VPN depending on where you find it in the browser in a recent developer edition of the web browser.
Browser VPN can be enabled in Opera with a simple check of a box in the browser's settings, and then turned on or off on the frontend.
It protects traffic by using encryption which improves both the privacy and security while using the browser.
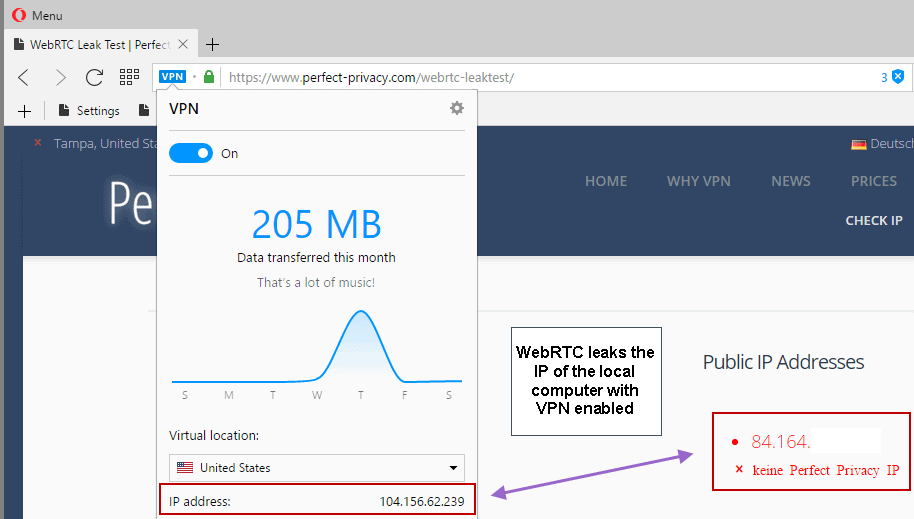
We have mentioned previously that Browser VPN does not support WebRTC or plugin traffic yet which means that sites and services may find out about the public IP address of the device used to connect to it even if the VPN is enabled.
A detailed analysis of Opera's VPN integration revealed that it is not a full VPN solution which protects all traffic on the device but a proxy instead.
When you enable the VPN in Opera, the following happens:
- Opera connects to the SurfEasy API to obtain credentials and IP addresses (SurfEasy is an Opera company).
- The browser sends requests to the proxy with proxy authorization request headers whenever sites or services are loaded in the browser. These include the device ID and device password.
- These information can be grabbed and used on different machines, even in other programs that are not Opera (as you have the proxy IP address, username, and password).
The connection itself is secure, with HTTPS being used even if non-HTTPS sites are loaded. Hostname resolution is done remotely on the proxy server which means that hostnames are not leaked as well when the VPN is used.
Two issues emerge from this; first, Opera's VPN is not a real VPN but a HTTP proxy. Second, Browser VPN uses a device ID that is linked to the device you are using.
Opera's VPN is not a real VPN but a HTTP proxy
Most users who run developer or beta editions of browsers probably assumed as much when they read about the new VPN that is built-in to the Opera browser.
Opera's Browser VPN works for the most part just like other VPN extensions that you can install for it.
The main difference is that the feature is built-in to the browser so that it may theoretically make use of features that extensions cannot make use of.
Additionally, when it comes to trust, users may trust Opera more than third-party browser extensions considering that they are using the Opera web browser which too requires some level of trust.
The takeaway is that Opera's Browser VPN does not encrypt all browser traffic currently (WebRTC and plugins are not included currently but you can disable those features if you don't require them), and that it won't work on a system-wide level but only within the browser.
Opera is aware of this however and plans to fix this in future releases (probably before it hits the stable channel).
Browser VPN uses a device ID that is linked to the device you are using
The device ID that is used by the VPN is the same ID that Opera has been using for a long time. You can read about it by loading opera://about/privacy in the web browser. There you find the following information about it:
Your installation of Opera browser contains a unique ID that can not be linked to you as an individual person. This unique ID is required for auto-updates of the software and any installed extensions. Data about the features (not websites) used in Opera browser is collected with the purpose to improve the software and services. The software also creates a unique ID that is linked to your computer. This unique ID is processed with the sole purpose to measure marketing campaigns and distribution partners.
Opera stated that they have a strict no-logging policy when it comes to the VPN/Proxy.














Hi there, how can i activate the vpn in the opera browser settings? i cant find the feature, has it been removed?
Mark.
The feature is still there. You need to open the Settings and go to Advanced > Privacy & Security. Scroll down to the VPN section and toggle the “Enable VPN” switch to enable it.
SurfEasy offers very little coverage, you have to purchase the premium version soon after using Opera.
vpn is not working from today onwards please clear that problem it was blocking proxy and all
..does not support WebRTC or plugin traffic
-What about Zenmate for Firefox or Chrome?
the Current Dev. version of opera is 38.0.2213.0, which fixes the IP address leaking issue with WebRTC. With this current version it is no longer necessary to use WebRTC “blocking” extensions. Also, if you are looking for the Windows 64 bit version, you can now download and install it with this current release.
http://www.opera.com/blogs/desktop/changelog-38/#b2213.0
they still have a 64bit-version, linux:
http://ftp.opera.com/pub/opera-developer/38.0.2205.0/linux/opera-developer_38.0.2205.0_amd64.deb
I can’t see any reason to install Opera until they have a 64bit version.
Martin, do you know of a way to check if Flash content is being “tunneled” through Opera’s proxy/VPN?
As far as I know, Flash never uses any VPN or proxy you might be using.
Opera stated that plugins, which includes Flash, and WebRTC, are not tunneled currently.
it’s only a browser-proxy – ok. No problem. If it would function without problems. Opera advertised loud and then they discovered, that it would be a question of resources to manage this. The days after publishing, opera-servers could not manage the load really. At times not useable. Now it’s ok (+/-), but f.e. streams like zattoo are not.
To manage the webrtc-bug in opera, one can use addon ‘WebRTC Leak Prevent’. All other (older) options are inoperable meanwhile.
I can only imagine when the VPN lands in the stable channel.
How does it differ from the Off-road Mode (f.k.a. Opera Turbo), which also is a compressing proxy?
Browser VPN does not compress, and it works for HTTPS content as well.
Martin, you state above “We have mentioned previously that Browser VPN does not support WebRTC or plugin traffic yet which means that sites and services may find out about the public IP address of the device used to connect to it even if the VPN is enabled.”
That was 1 or 2 days ago. But in that same article you also recommended an extension to plug the WebRTC leak, which works well. For completeness’ sake I believe it should be mentioned in your article above too, otherwise you contribute t the confusion & misunderstanding that is now building up about this subject.
I think I have mentioned that already: The takeaway is that Opera’s Browser VPN does not encrypt all browser traffic currently (WebRTC and plugins are not included currently but you can disable those features if you don’t require them), and that it won’t work on a system-wide level but only within the browser.
Or do you mean something else?
Calling VPN what is in fact a plain proxy is not a semantic approximation : it is a misleading information. Of course ‘VPN’ sounds, looks nicer than a plain, rude ‘proxy’ in terms of appeal but engineers over at Opera should have insisted on the requirement of stating truth and not verbose incentives. The opera plays the wrong partition.
As others have mentioned on this debate on forums like HackerNews.
VPN itself is a type of proxy. There isn’t really any misleading advertising since they are using the underlying technology and functionality of SurfEasy which was a VPN provider.
Calling it proxy would be misleading as well. As the Opera post on VPN dev release mentioned with the GWI report, different people use VPN for different reasons.
Those who want anonymity are a minority in fact.
Bypassing geo-block to watch/stream some video, this is also understood by end users to be a job for a VPN and this feature of Opera does that.
Its Semantics were fair use in the end-user case context.
Tom, Dave, Var you are all correct. Perhaps a better way of defining Opera VPN is to simply call it a form of spoofing. Obfuscation is a term I prefer, and to be critical, its just browser obfuscation. Obviously not every device a user may use on their network, or indeed WiFi, will benefit from this now open and indeed useful technology. Consequently it is not real VPN. Very useful though.
Wait, how do I use Opera VPN/proxy in Firefox? This seems like something I want.
Can I use StartPage proxy in Firefox too?
I agree. False advertising.