Password mistakes that increase the chance of getting hacked
Selecting a secure, unique password is not science, but it can be a frustrating experience for Internet users especially if they don't use a password manager program to assist them in the task.
To make matters worse, there is no clear definition of when a password is considered safe (from brute force or guessing attempts) which means it is up to you to select a minimum character length and character set for your passwords.
Weak passwords are included in every password dictionary list, and good brute force applications take variations into account as well.
The list of "worst passwords of 2015" and "worst passwords of 2014" did not change all that much, and weak passwords like 123456 or password are still found at the top of the list after years of tech sites hammering it into people's brains that these passwords are bad.
There is no excuse for making these password mistakes. All modern browsers support the saving of passwords so that you don't need to remember them, and passwords manager are available in abundance for all devices you can possibly run.
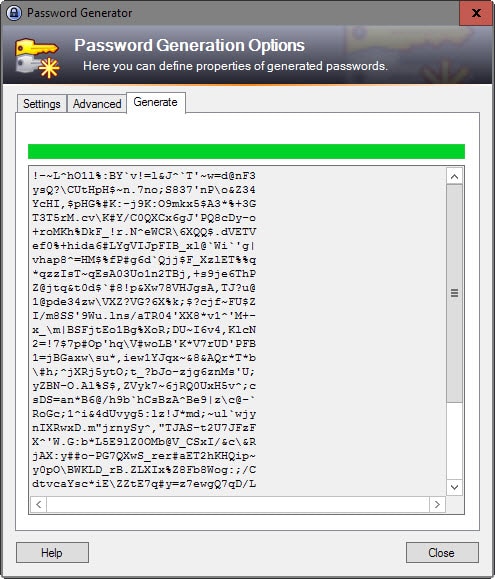
I'm using KeePass for all things passwords, but there are many alternatives out there like LastPass or Sticky Password that you can make use of.
Password Mistakes
Short and common-word passwords are easy to remember, and that is likely the main reason why they are used by many Internet users.
Even if your password is not on the list of bad passwords of 2015 or previous years, you are not necessarily safe as brute force dictionaries include lists of thousands of passwords that are commonly used.
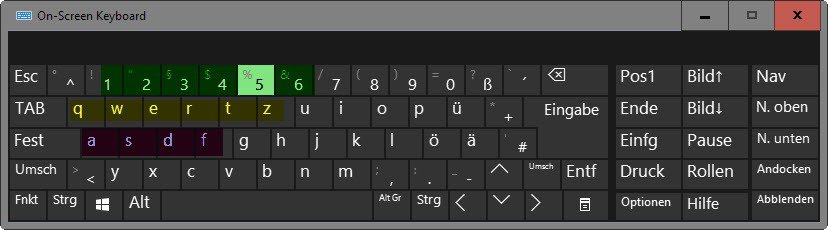
Any password that is a sequence on the keyboard
Passwords that are sequences on the computer keyboard are used often as you only have to look at the keyboard to remember them.
You can be certain that all obvious sequences, as well as repeat sequences, are used by crackers and hackers in brute force attacks.
Not only are the majority found high on "weak passwords" lists, anyone with a keyboard can spot these sequences easily as well.
This includes pattern passwords on mobile devices as well as they follow the same rules.
Examples are 123456, qwerty, 1234567890 or asdfasdf.
Any password that is found in a dictionary
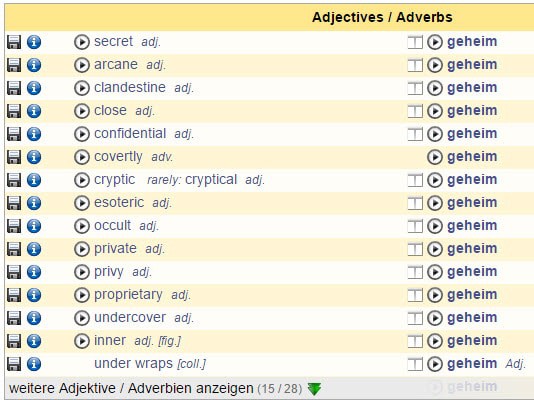
Any word that is found in a dictionary is a bad choice for a password, even the ones that are not used a lot in modern days.
The reason is simple: It is easy enough to use a dictionary, say English words, in a brute force attack. Simply run through all words of the dictionary, or the most x-common ones. It takes no time and effort to create these attack list.
Examples are password, private, football, or princess.
Any password that substitutes letters with characters
Some users like to substitute letters with characters to improve password security which is another password mistake. They replace I with 1, O with 0, or e with 3 in hope that it improves the strength of the password.
Since these substitutes are known, or easily identified, it is not improving the strength of the password by much.
Many brute force programs ship with options to use password variations, e.g. substitutions or adding characters like 1 or ! to the end of the password to test these variations as well.
Examples are f00tb@ll, pr1ncess or pa$$word.
Short passwords
This one is obvious. Short passwords are easier to crack as computers have become powerful enough to run attacks quickly on passwords below a certain length. There are simply not enough variations available to make short passwords secure even if special characters are used.
Examples are short, ice or pass.
Pop Culture
Pop culture passwords are popular which is why they are included when it comes to password mistakes. They may include a favorite sports team, your favorite singer or band, or a popular movie character among other things.
It is no coincidence that Solo and Star Wars made the Top 25 worst passwords of 2015 list.
Examples are Broncos, Eminem or DanielCraig.
Keeping default passwords
Hardware and software may ship with default passwords. The router or modem is a prime example, and you often see admin/admin, root/blank or admin/password as the default usernames and passwords for access.
Not changing these immediately can have severe consequences as default passwords are public knowledge as well.
Instead of having to brute force the device or account, an attacker could try default passwords first to see if they have not been changed by the user or admin.
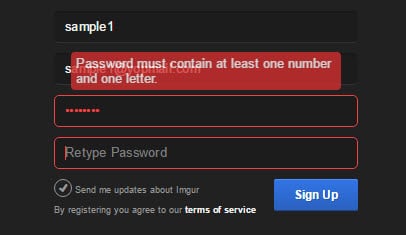
Not using numbers or special characters
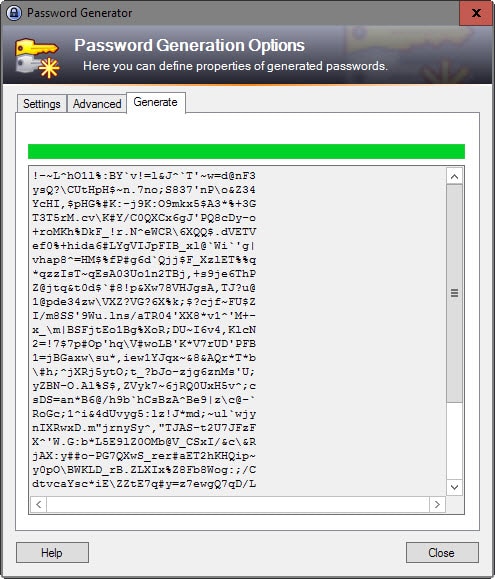
Passwords that exceed a certain length are secure which means that a password like GNLxypVVoCZDfAvSpiZZuluFySJUCuXe is generally considered secure.
You can increase the complexity of a password by adding numbers, e.g. GVdEwjaTc5N9c1z7khbpSl097xMMcwo3 and/or special characters to it like ZoXhEi"C6G"Op6s_oMxHhrf`t/+6-3UU.
Doing so forces the attacker to include all characters in the attack and not only letters (52 if you consider upper and lower case). And if they don't, they will never crack the password using brute force attacks even if they have access to the most powerful machine in the world.
Personal passwords
You may not want to choose passwords that can be linked to you. This includes your license plate or social security number, name of your boyfriend, your favorite football team or the name of your dog or cat.
Social engineering may come into play to get these passwords. It may be as easy as looking at photos that you have published on Facebook (showing your brand new car and its license plate).
Now You: Got anything to add or correct?


















My second language is German, among the top 5 languages on the Internet, among the most widely languages published in, the 3rd most widely learned foreign language in the US and 1st in most other major Anglophone countries. No, I do not use German words as my password.
Just download and use KeePass. It’s so easy to generate a password.
“..after years of tech sites hammering it into people’s brains that these passwords are bad.”
People don’t browse tech sites, are not registered to tech sites and don’t understand the language anyway.
Pants, the fbi and the kgb are after you. Run dude, run!
The FBI, the NSA, the KGB, the Chinese Communist Party, organized crime, Google, telemarketers, your soon-to-be ex-spouse’s divorce lawyer, potential employers who want to know if you have any health problems that might drive up their health plan costs, just to name a few.
I’m seeing redheads in the nude on harleys in code .. I think I have bigger issues :)
Yesterday I was watching the ‘Hackers’ movie from 1995. When I saw Zero Cool I thought “He may be awesome but not as awesome and stealth as Pants”.
Dude you must change all your passwords like 3 or 4 times a day. They are everywhere man! Cool.
one should keep be careful when using some local or online retailers (avoid reusing passwords), even authorizing personal access (e.g., running Apple’s iTunes) on a 3rd-party site.
To build lines of defense, one can do the following:
* completely uninstall all other unused even unknown apps or programs on computer. For help, pay a visit to https://removeunwantedprograms.wordpress.com/
* perform security check regularly by using an up-to-date security program;
* never run or open 3rd-party items like mail attachment directly;
* turn off all wireless networks (except for mobile data) when shopping via smartphone or at a public location;
* use credit cards ( * avoid using debit cards).
I once read on some website that the strongest password is one that even you don’t know. That’s the case with me. I don’t know any of my passwords. They are long and convoluted. So I use a password manager.
On an unrelated note, it’s also a good idea to use a complex password as your security answer when registering for online accounts. I can’t take credit for this idea either – it was in a random YouTube video of a geek suggesting to do this.
Example:
Security question: What was the name of your first pet?
Security answer: `2?Ghb^H-7*LcO’5O2l7UF*d;;nXJ@VE$sPJ0s 9mg;0Lc8wzUf&=,~4!+’bSuIxdK2iOCE`j)]eDAV(#
Some sites allow you to write both the question and answer, in which case, do the same as above in addition to making the question a password itself.
* Password generated using KeePass
It always helps to save some trivial facts about your life that you’ve never told anyone.
BTW, if your security questions are non-sensible, you will probably forget them when you need them.
Security question: What was the name of your first pet?
Answer: an avocado tree
Security question: What was the name of your favorite childhood superhero?
Answer: the ice cream man
Of course really critical passwords, you’ve just got to remember. The more often you use them, the easier they are to remember.
I don’t really care about forgetting security questions and their answers. That’s what the password manager is for. I’ve been using the outlined techniques for over half a decade and it’s worked out pretty well so far.
I just never put my password database on any cloud, sun, or rainbow online service. Now that’s non-sensible, and I don’t understand people who do that.
I believe that every category of security – online or otherwise – inherently comes with its own set of hassles. As such, if one cares about their security, they’d be feeling less inconvenienced by its hassles.
`2?Ghb^H-7*LcO’5O2l7UF*d;;nXJ@VE$sPJ0s 9mg;0Lc8wzUf&=,~4!+’bSuIxdK2iOCE`j)]eDAV(#
I just ran that thorough an image decoder, turns out a nude redhead on a motorcycle
All pets are nude, but I can’t think of any redhead pet on a motorcycle except a red fox.. so.. Firefox?! ;)
That’s actually good advice. I mentioned this back in 2012: https://www.ghacks.net/2012/08/23/security-tip-do-not-answer-security-questions-correctly/
I think it’s possible that the said geek read your article, took your advice, and shared it on YouTube. Either way, I’m glad you brought to light this matter in a separate post ~4 years ago. The more people get educated, the less we have to cringe at horrifying password management. True story: my siblings store their passwords in a word document, even after teaching them how to use KeePass properly.
Why don’t more websites, especially critical ones like banking sites etc. limit the tries to say 5 or less after which the site locks you out for an hour or so. Would this not almost totally eliminate brute force attacks? A total or indefinite lockout is not a great idea as sometimes people, myself included have a brain fart and just keep trying the same wrong pswd til we get locked out.
@Jung-Tech,
Both of my banks lock me out after 3 tries. I have to call or go in, verify who I am and then they’ll send a request for it to be unlocked, usually by the end of the next business day. One bank will only let me do it 2x a week. Also password rotation is set every 90 days with no similar password in the last 365 days.
Worst part is, the bank that allows me to do the least online (such as only transfer between accounts I own, and limited to 2 transfers a day) has the most security while the one that allows me to do the most (send money to any account as long as I have the right info) has lesser security, to a degree.
However, many bruteforce attacks aren’t done to the login, but after they’ve obtained the database. It would be impractical and very obvious if one particular account had 2million incorrect password attempts in the last 3 hours. They’ll do these things locally where they can do 10,000 words a second (and possibly more depending on the computer and program). Most companies have their database information pretty secure, but access to them might not as secure.
(@Jung-Tech, if this comment is not nested correctly for some reason like the last time I posed)
When you hear about these sorts of brute force attacks or “the weakest passwords” lists, it’s often the case that a site’s entire/partial password database/file has been obtained through other vulnerbilities in the site itself, not through vulnerabilities in people’s passwords.
Once they have that data, crackers can plug away as long as they want in the privacy of their own homes. Essentially, if your password is in one of these leaked databases, in the hands of a skilled cracker, unless it’s ridiculously strong(and probably even if it is), it /will/ be cracked eventually.
Then somewhat relatedly, once they have your login and super-weak password they still won’t need more than one attempt to try the same combination at other sites.
Some links for folks:
http://world.std.com/~reinhold/diceware.html <– diceware word list pdf
https://www.random.org/dice/ <– dice
http://arstechnica.com/security/2013/05/how-crackers-make-minced-meat-out-of-your-passwords/ <– probably the article mentioned by Pants in an earlier comment, good read, if a little depressing
Read this one too: http://arstechnica.com/security/2015/09/once-seen-as-bulletproof-11-million-ashley-madison-passwords-already-cracked/
Salting is important, so is choice of ciphers, so is implementation/configuration. Security is hard. One screw up from Ashley Madison caused magnitudes of order of time saved for crackers. These are the consequences of being in a world governed by physics and mathematics (and Kanye West). If only the Higgs Boson had been 140 GeV and not 125 GeV, the world would have a far more interesting place (but only as long as it decided to not wink out of existence like some Douglas Adams in-house joke), and Kanye West probably would be here. Damn you Higgs Boson.
Because banks (and other sites) don’t give a shit. Security is secondary, making money is the primary goal. I asked my bank when they were going to increase the field size from 16 chars and allow more than just alphanumeric. They said never. Basically in this case it comes down to logistics/costs. Even if they did increase it, would end users take advantage (probably not, only a small percentage), so why waste money, and it’s the users responsibility to make sure they use unique passwords. In other words, not their problem, and you’re covered anyway (as long as you took reasonable steps – eg AV, didn’t give anyone your password, didn’t use something stupid). Personally I think financial sites should be forced by law or thru some banking ombudsman to 1) salt hashes 2) all employ a decent minimum length 3) force alpha numeric and special chars 4) use 2FA
@ Pants
You know I asked my bank also when they were going to increase the field size from 16 characters and the girl looked at me like I was crazy. She told me they have never been hacked and I should be fine.I looked at her smiling and said the last time I bragged about my vehicle the transmission went out shortly. That is true it did. That is what you get for bragging…lol. I don’t know why I was surprised. If they thought things were going to start changing soon they would not be coming out with hacker insurance for companies. I doubt that is cheap. I heard that on the news while coming into the room the other night.
I agree some of this is going to have to be forced by law or other, if we see any kind of worth while change to financial sites. You know how that goes people are willing to give up some security for convenience. That is just getting very expensive for all of us. People are getting where they play that on everything. If it bit them I would not mind it, but the trouble is it is biting us all on the ass.
No mention of pass phrases, the only tenable solution?
I see correct horse battery staple is in the comments but I’m quite surprised to not see any mention of a passphrase in the article.
Diceware, as well, provides a solution with enough entropy to ensure that a pass phrase of 4 to 6 words, while easy to memorise, will be hard to crack.
If it hasn’t already been done previously on ghacks, I would love to see an article on these topics as well as I feel they are definitely topical for user security.
Passphrases are a great compromise between human and computer. Unfortunately, most systems do not support them. Maximum 12 characters and include symbols and digits.
Dictionary words are perfectly OK if used in sufficient numbers. I tried to post the link to xkcd but saw it has been already mentioned.
There is a discussion about the XKCD comic here: http://security.stackexchange.com/questions/62832/is-the-oft-cited-xkcd-scheme-no-longer-good-advice
Obviously, if you add enough dictionary words together, you get a good password strength, but the same is true for any other thing you add a lot of times together. If you use qwertyasdfghzxcvbn123456 that’s probably fine as well.
I disagree with the assumptions at the end of your article. I’d recommend you read this XKCD cartoon to understand why. http://xkcd.com/936/
Just an observation, and I’m not an expert. But I don’t think dictionary attacks are very common. I have read several in depth ArsTechnica articles about how some of these experts attack large sets of hashes (which may or may not be salted). They will start with the easy ones, and then slowly increase the complexity as well as using known tricks/techniques – each iteration yielding lower ever diminishing returns over exponential attack cycles times. The faster they can bring down the number of remaining unencrypted passwords, the less work for the next cycle. They don’t just ever run a brute attack trying all combos. There are huge databases of rainbow tables available – and every time some hack of passwords is dumped and the experts get around to working a lot of them out (eg Ashley Madison data) – new entries are added to the tables, which get propagated around I assume. It’s all very interesting. I tried really getting into cryptography back in the late 1990s, but it just did my head in.
On a semi-side note. Those list of the 20 worse, or 20 most common passwords etc are totally useless – click bait drivel. The nature of passwords, where everyone should be trying to be unique (high entropy), means that even if only 0.1% of people are complete idiots and use “password”, “abcdef”, “123456” etc and all those common variants etc, they will still come out top, because by its very nature, the other 99.9% will be trending rapidly towards being unique.
I’d really like to see some real analysis on say the top 100,000 or 1million – such as average length, complexity, ratio of numbers to letters to special characters and so on. Are 4 digit years common, if so do they always start with 19 or 20? How popular is 1066 or 1945 or other significant years in history? Placement of numbers, ratio of first characters starting with a letter vs number. And so on. It’s this kind of analysis that allows the hacking experts to use “tricks” to beat the odds.
I’m not an expert, but think of it like Google Translate. Google’s translating (or anyone’s) was shit back in the day. They all tried to basically translate word for word, with some smart algorithms throw in. Then google switched it up, and basically decided to store everything they could translated by humans – phrases, idioms, sentences, everything they could get their hands on. So now it can be rather good (I assume because I’ve only ever used it like 5 times). Colloquialisms, slang, etc is picked up on. Example “to lick windows” in french means to go window shopping. THIS is how brute force attacks are done – by storing huge amounts of data of previously know passwords, and build huge tables that incorporate statistically likely combinations, derived from intense analysis of what is already known. Which in turns leads to more discovers, bigger data sets, more analysis.
At least that’s how I see it.
Nothing to add nor to correct.
“[…]weak passwords like 123456 or password are still found at the top of the list after years of tech sites hammering it into people’s brains that these passwords are bad.”
Well, hammering again and again might one day make those users who just don’t realize the absurdity of their password behavior finally move their brains : I guess it’s just a synapse which hasn’t been set to ON.
Concerning the strength of the password, besides dedicated sites there is an interesting application, ‘Strong Passwords Need Entropy’ (SPNE) which I always mention in this topic.
As for password management all I can say is that, if an application such as those mentioned in this article are not used, if them sesames are held in Firefox then at least do use the Master Password which will also encrypt them.
The basic idea is that a password manager is imperative as it is the only conclusion to 1- Strong passwords are indispensable and must never be the same and 2- human brains cannot memorize what is required for many strong passwords.
Always good to be recalled. I really hope this article will participate to an awareness comparable for some users to a revelation, an illumination, an enlightenment! — Let ie be said and repeated.
For all those already aware, forgive my speech :)
The problem with the idiots with the insecure passwords is partly that they think they have been safe so far, and they think this because they do not know that you usually do not know if you’ve been hacked. It’s like the Enigma Machine from World War 2. The British were clever enough to use the information in a way that the Germans had no idea that their messages were being intercepted. You can be sure that today’s hackers, mostly organized crime and governments, are doing the same.
For a password manager, I just use bcrypt from the command line to encrypt a plain text file. It’s free and real easy to use. It eliminates any traces it might have left on your computer.
Errrgh .. where did the edit go .. I take it back .. “selecting” is not science, that’s a human element. I agree. Sorry. My bad. My brain is in the other room and my head is elsewhere.
Edit: after posting a comment, I now have to F5. Could swear I never had to do that before.
test
“Selecting a secure, unique password is not science”
Yes it is. It’s mathematics.
Edited: Read next comment