Microsoft Security Bulletins For September 2015
The patch day overview for September 2015 provides you with everything you need to know in regards to security and non-security patches that Microsoft released this month.
It begins with an executive summary listing the most important information about this month's patch day. It is then followed by lists of affected client and server versions of Windows, and other Microsoft products.
The next three groups list security bulletins, security advisories and revisions, and non-security updates released since the last patch day in August.
The final chapters provide you with download and deployment information, and links to important resources.
Executive Summary
- Microsoft released a total of 12 security bulletins this patch day.
- Five bulletins have a maximum severity rating of critical.
- All Windows client operating systems are affected by at least one critical vulnerability.
- Other Microsoft products affected this patch day include Microsoft Office and Microsoft Exchange Server 2013.
Operating System Distribution
Windows 10 is the only client operating system that is affected critically by vulnerabilities reported in two bulletins (MS15-094 and MS15-095) while all other supported client operating systems are only affected critically by MS15-094.
The reason why is easily explained: bulletin MS15-095 is a cumulative security update for Microsoft Edge which is only available in Windows 10.
- Windows Vista: 1 critical, 3 important
- Windows 7: 1 critical, 3 important
- Windows 8 and 8.1: 1 critical, 4 important
- Windows RT and RT 8.1: 1 critical, 2 important
- Windows 10: 2 critical, 3 important
- Windows Server 2008: 2 important, 1 moderate
- Windows Server 2008 R2: 2 important, 1 moderate
- Windows Server 2012 and 2012 R2: 3 important, 1 moderate
- Server core: 3 important
Other Microsoft Products
- Microsoft SharePoint Foundation 2013: 2 important
- Microsoft Exchange Server 2013: 2 important
- Microsoft Office 2007 and 2010: 2 critical
- Microsoft Office 2013: 1 critical
- Microsoft Office 2013 RT: 1 critical
- Microsoft Office for Mac: 1 important
- Office Compatibility Pack SP3, Microsoft Excel Viewer: 1 important
- Microsoft Live Meeting 2007, 2010 and 2013: 1 critical
- Microsoft Lync Server 2013: 1 important
- Skype for Business Server 2015: 1 important
Security Bulletins
MS15-094 - Cumulative Security Update for Internet Explorer (3089548) - Critical - Remote Code Execution
This security update resolves vulnerabilities in Internet Explorer. The most severe of the vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Internet Explorer. An attacker who successfully exploited these vulnerabilities could gain the same user rights as the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS15-095 - Cumulative Security Update for Microsoft Edge (3089665) - Critical - Remote Code Execution
This security update resolves vulnerabilities in Microsoft Edge. The most severe of the vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Microsoft Edge. An attacker who successfully exploited these vulnerabilities could gain the same user rights as the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS15-096 - Vulnerability in Active Directory Service Could Allow Denial of Service (3072595) - Important - Denial of Service
This security update resolves a vulnerability in Active Directory. The vulnerability could allow denial of service if an authenticated attacker creates multiple machine accounts. To exploit the vulnerability an attacker must have an account that has privileges to join machines to the domain.
MS15-097 - Vulnerabilities in Microsoft Graphics Component Could Allow Remote Code Execution (3089656) - Critical - Remote Code Execution
This security update resolves vulnerabilities in Microsoft Windows, Microsoft Office, and Microsoft Lync. The most severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted document or visits an untrusted webpage that contains embedded OpenType fonts.
MS15-098 - Vulnerabilities in Windows Journal Could Allow Remote Code Execution (3089669) - Critical - Remote Code Execution
This security update resolves vulnerabilities in Microsoft Windows. The more severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted Journal file. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
MS15-099 - Vulnerabilities in Microsoft Office Could Allow Remote Code Execution (3089664)Â - Critical - Remote Code Execution
This security update resolves vulnerabilities in Microsoft Office. The most severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted Microsoft Office file. An attacker who successfully exploited the vulnerabilities could run arbitrary code in the context of the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS15-100 - Vulnerability in Windows Media Center Could Allow Remote Code Execution (3087918)Â - Important - Remote Code Execution
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if Windows Media Center opens a specially crafted Media Center link (.mcl) file that references malicious code. An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS15-101 - Vulnerabilities in .NET Framework Could Allow Elevation of Privilege (3089662) - Important - Elevation of Privilege
This security update resolves vulnerabilities in Microsoft .NET Framework. The most severe of the vulnerabilities could allow elevation of privilege if a user runs a specially crafted .NET application. However, in all cases, an attacker would have no way to force users to run the application; an attacker would have to convince users to do so.
MS15-102 - Vulnerabilities in Windows Task Management Could Allow Elevation of Privilege (3089657) - Important - Elevation of Privilege
This security update resolves vulnerabilities in Microsoft Windows. The vulnerabilities could allow elevation of privilege if an attacker logs on to a system and runs a specially crafted application.
MS15-103 - Vulnerabilities in Microsoft Exchange Server Could Allow Information Disclosure (3089250) - Important - Information Disclosure
This security update resolves vulnerabilities in Microsoft Exchange Server. The most severe of the vulnerabilities could allow information disclosure if Outlook Web Access (OWA) fails to properly handle web requests, and sanitize user input and email content.
MS15-104 - Vulnerabilities in Skype for Business Server and Lync Server Could Allow Elevation of Privilege (3089952)Â - Important - Elevation of Privilege
This security update resolves vulnerabilities in Skype for Business Server and Microsoft Lync Server. The most severe of the vulnerabilities could allow elevation of privilege if a user clicks a specially crafted URL. An attacker would have to convince users to click a link in an instant messenger or email message that directs them to an affected website by way of a specially crafted URL.
MS15-105 - Vulnerability in Windows Hyper-V Could Allow Security Feature Bypass (3091287)Â - Important - Security Feature Bypass
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow security feature bypass if an attacker runs a specially crafted application that could cause Windows Hyper-V to incorrectly apply access control list (ACL) configuration settings. Customers who have not enabled the Hyper-V role are not affected.
Security Advisories and updates
Microsoft Security Advisory 3083992 - This update includes improvements to enhance the functionality of Windows 10.
Windows Malicious Software Removal Tool - September 2015 (KB890830)/Windows Malicious Software Removal Tool - September 2015 (KB890830) - Internet Explorer Version
MS15-093: Security Update for Internet Explorer (KB3087985) - This security update resolves several reported vulnerabilities in Internet Explorer. The most severe of these vulnerabilities could allow remote code execution if a user views a specially crafted webpage in Internet Explorer.
MS15-093: Cumulative Update for Windows 10 (KB3081444) - The security update for Windows 10 that is dated August 18, 2015, includes improvements in the functionality of Windows 10 and resolves MS15-093 in Windows.
Non-security related updates
Dynamic Update for Windows 10 (KB3081454) - September 8, 2015, compatibility update for upgrading to Windows 10
Update for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, Windows Server 2012, Windows Server 2008, and Windows Vista (KB3092627) - September 2015 update to fix Windows or application freezes after you install security update 3076895
Update for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2 (KB3083324) - Windows Update Client for Windows 7 and Windows Server 2008 R2: September 2015
Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3083325) - Windows Update Client for Windows 8.1 and Windows Server 2012 R2: September 2015
Update for Windows 7 and Windows Server 2008 R2 (KB3092627) - September 2015 update to fix Windows or application freezes after you install security update 3076895
Cumulative Update for Windows 10 (KB3081448) - This update includes improvements to enhance the functionality of Windows 10.
Update for Windows 10 (KB3081449) - This update improves the Windows 10 out-of-box experience (OOBE)
Dynamic Update for Windows 10 (KB3081451) - August 27, 2015, compatibility update for upgrading to Windows 10
Update for Windows 10 (KB3081452) - August 27, 2015, compatibility update for upgrading to Windows 10
Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3089023) - Unexpected Adobe Flash Player error after security update 3087916 is installed in Windows 8.1 or Windows Server 2012 R2
Dynamic Update for Windows 10 (KB3081437) - August 18, 2015, compatibility update for upgrading to Windows 10
Update for Windows 10 (KB3081441) - Compatibility update for upgrading to Windows 10
Update for Windows 8.1 and Windows Server 2012 R2 (KB3052480) - Unexpected ASP.Net application shutdown after many App_Data file changes occur on a server that is running Windows Server 2012 R2
Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3060746) - You can't open the "Devices" menu in PC Settings in Windows 8.1 or Windows Server 2012 R2
Update for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, and Windows Server 2012 (KB3066441) - Characters overlap and are unreadable in an application in Windows 8.1 or Windows 8
Update for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 7, and Windows Server 2008 R2 (KB3075249) - Update that adds telemetry points to consent.exe in Windows 8.1 and Windows 7
Update for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, Windows Server 2012, Windows Embedded Standard 7, Windows 7, Windows Server 2008 R2, Windows Server 2008, Windows Vista, and Windows XP Embedded (KB3077715) - August 2015 cumulative time zone update for Windows operating systems
Update for Windows 7 and Windows Server 2008 R2 (KB3078667) - System malfunction because memory leak occurs in dwm.exe in Windows 7 or Windows Server 2008 R2
Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3078676) - Event 1530 is logged and ProfSvc leaks paged pool memory and handles in Windows 8.1 or Windows Server 2012 R2
Update for Windows 8.1 and Windows RT 8.1 (KB3079318) - "Connection is unsuccessful" error when you connect a Bluetooth device to an application in Windows 8.1 or Windows RT 8.1
Update for Windows 8.1, Windows RT 8.1, Windows 8, and Windows RT (KB3079850) - Update APN database entry for China Mobile Hong Kong in Windows 8.1 and Windows 8
Update for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 7, and Windows Server 2008 R2 (KB3080149) - Update for customer experience and diagnostic telemetry
Update for Windows 8.1 (KB3080457) - This update provides the latest Microsoft Communications Apps (People, Mail, and Calendar) update for computers that are forbidden to access the Windows Store.
Update for Windows 8.1 (KB3081397) - This update provides the latest Microsoft Bing Finance app update for computers that are forbidden to access the Windows Store.
Update for Windows 8.1 (KB3081398) - This update provides the latest Microsoft Bing Travel app update for computers that are forbidden to access the Windows Store.
Update for Windows 8.1 (KB3081399) - This update provides the latest Microsoft Bing Sports app update for computers that are forbidden to access the Windows Store.
Update for Windows 8.1 (KB3081401) - This update provides the latest Microsoft Bing News app update for computers that are forbidden to access the Windows Store.
Update for Windows 8.1 (KB3081402) - This update provides the latest Microsoft Bing Maps app update for computers that are forbidden to access the Windows Store
Update for Windows 8.1 (KB3081403) - This update provides the latest Microsoft Bing Health & Fitness app update for computers that are forbidden to access the Windows Store.
Update for Windows 8.1 (KB3081405) - This update provides the latest Microsoft Bing Weather app update for computers that are forbidden to access the Windows Store.
Cumulative Update for Windows 10 (KB3081438) - This update includes improvements to enhance the functionality of Windows 10.
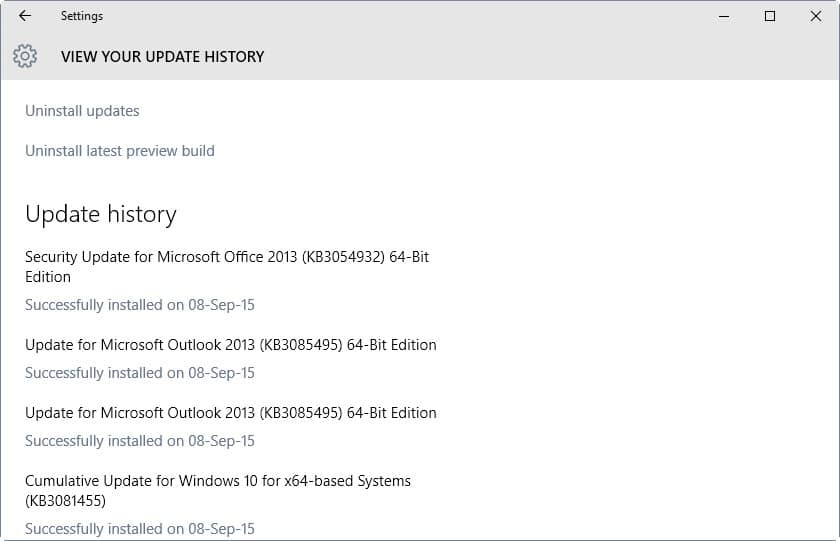
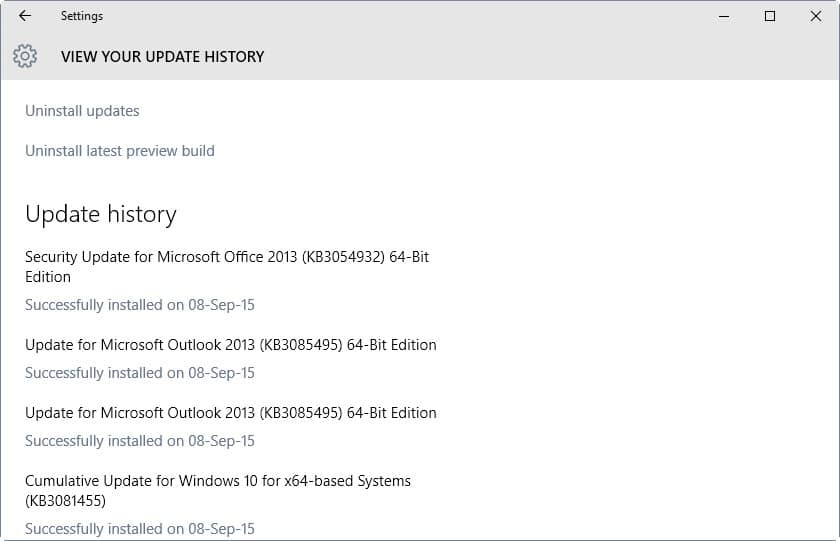
How to download and install the September 2015 security updates
All security updates are already available via Windows Update. It is recommended to check for updates manually if you want to install the updates at the earliest point in time as Windows does not check for updates in real-time.
- Tap on the Windows-key, type Windows Update and select the appropriate option from the search results.
- Locate "check for updates" and click on the link or button
- Windows will run a manual check for updates and display all that are compatible with the system
Updates are also made available on Microsoft's Download Center as standalone patches. There you will also find links pointing to monthly security ISO images that Microsoft releases that contain all patches of a given month.
Additional information
- Microsoft Security Response Center blog on the 2015 Bulletin Release
- Microsoft Security Bulletin Summary for September 2015
- List of software updates for Microsoft products
- List of security advisories of 2015
- Our in-depth update guide for Windows




















This is the BEST site for anything MS and updates, security and more.
Thanks so much for your great blog !
Subscribed !
Thanks and welcome aboard ;)
KB3083324 silently installs Windows 10.
And if you hide it – Windows update center will offer previous versions of this shitty update. Avoid every update that is 3.0 MB (they all do same thing)
KB3083324 is not really “suspect”. At first it was an optional update, and with such little information about it, Woody Leonhard recommended not installing it until there was some more documentation available. But now it’s re-classified as an “important” update. He titled his post “don’t check that box”, and now people are all freaking out, like it’s something evil…
Re: KB3069114 . I have exactly the same problem. I’m operating Windows 8 on a Lenovo G780. I tried all the Windows fixes but it still won’t download. I suspect this problem is widespread and that Windows will cancel and rewrite it.
KB3083324 – no one still seems to have an answer for why this update is suspect. Microsoft has made it ridiculously difficult to determine what any update is for…. all they have to do is list a more informative description in the update window itself.
KB3069114 — I have Win8 [not 8.1] and when I run this portion of the Sept releases, the update fails, all the cures suggested by following the URL on the fail notice didn’t resolve the problem. I’m not sure what programs I use are associated with the “Journal”, but from notes, above, it appears to be connected with .NET somehow, and that alone leaves me concerned that I can’t get the security fix to operate successfully.
All the other updates worked on this batch of updates; shut down & restart doesn’t cure the failure
Anyone have similar experience, or have suggested fixes ?
Hi DCDove, I have been trying all day to download KB3069114, I had almost given up and gave it one last try from their support page. I have used this method more than once today and this time I got a popup msg reading “this update is not applicable to Windows 8” so it appears it was added to this months update schedule in error. I’m operating Windows 8 on a Lenovo G780 (64). I assume this update is for Windows 8.1 only.
Hi DCDove,
All WIndows 8 64 bits in my network which tried so far to install KB3069114 failed (19 computers so far). We use WSUS, so it’s easy to see that on the server.
In my own computer (also Win8 64) the error is 800f0902.
Others have been reporting the same error with this update:
http://news.softpedia.com/news/kb3069114-windows-8-update-failing-to-install-491398.shtml
I’d like to hear if someone actually managed to have this installed on Win8 64…
Even though I am on Windows 10, I still have Patch Tuesday, since Office updates are still released on a regular schedule.
#3080149 & #3075249
Is this Microsoft trying to sneak these back in using a different update numbers again?
i just wanted to look up what KB3083324 is all about, clicked the link in windows update (windows 7), which opened the microsoft site in firefox. i’ve recently disabled cookies an am only using a whitelist to store the logins for a handful of websites, the microsoft site not being one of them of course. the microsoft site now just says that cookies are disabled and i should enable them and refresh the site, as well as that it will only use cookies for analysis and ads and some such. hence, if i want to find out what KB3083324 really does, i have to enable cookies for microsoft to track me and shove ads in my face. my urge to switch to linux increases by the day.
I went to the MS KB site and all it says is this: “an update that contains some improvements to Windows Update Client in Windows 7 Service Pack 1 (SP1) and Windows Server 2008 R2 SP1.”
I have googled around, and while a lot of people are suspicious of it, I haven’t found any evidence that this update is anything nefarious. From what I’ve seen, it’s supposed to help improve the ridiculously long time it takes Windows to check for new updates.
ah, thank you. i understand people being sceptical of telemetry updates and the like, but if we’re starting to be afraid of bog standard updates now as well, then this is a bit much for me. it’s not that ms has always done a great job of explaining what each update does in the past as well, so the fear of KB3083324 seems overblown at this point.
what is so suspicious about KB3083324?
I’m on Win 7 but did not get that suspicious Update KB3083324. Perhaps they revoked it
meanwhile?
Just removed KB3083324
I had promised myself I’d check thoroughly each and every Microsoft Update yet I proceeded too quickly last night. From now on I will wait until full check of reviews before updating. Microsoft is becoming/confirming to be a real pain in the neck. BE EXTRA CAUTIOUS WITH MICROSOFT.
Tracking is the attitude of a crook, be the tracking company a crook or not.
Also for Applocker does it apply for W7 Home Premium? If not then should I bother getting it anyways?
I’m on W7 and I don’t seem to have most of the ones shown by this article, what’s going on? Currently I have
Cumulative Security Update for IE11 for W7 for X64
https://support.microsoft.com/en-us/kb/3087038
Security Update for Microsoft .NET Framework
https://support.microsoft.com/en-us/kb/3074543
https://support.microsoft.com/en-us/kb/3074230
https://support.microsoft.com/en-us/kb/3074550
https://support.microsoft.com/en-us/kb/3069114
https://support.microsoft.com/en-us/kb/3083992 (What does this do? Is there any harm in not installing it? Sounds like it’s just there to prevent pirating)
https://support.microsoft.com/en-us/kb/3084135
https://support.microsoft.com/en-us/kb/3086255
https://support.microsoft.com/en-us/kb/3083324 (Hide this one right?)
https://support.microsoft.com/en-us/kb/890830 (Sounds good, but what if I have disabled IE though not deleted it?)
https://support.microsoft.com/en-us/kb/915597
https://support.microsoft.com/en-us/kb/3092627 (Non-security related but since I have the previous patch afflicted I should get it right? No spyware?)
A lot of these are not covered by your article, yet I was using my computer every day these past 2 weeks and I still saw no updates like the ones you posted.
I’m a bit worried because I see a vast difference between your article and my own update options.
I am with Scrub on this one. I have the same updates he does on Win 7. You do not even list these.
Why???? Something does not smell right.
I come back and there’s still nothing. However I started getting memory leak issues from svchost.exe and when I look it up according to https://www.reddit.com/r/sysadmin/comments/3frcib/heads_up_kb3050265_fixes_major_memory_leak_in/ I’m missing those files, yet since those are optional I assumed they were just telemetry crap. Can I get an opinion on what to grab? I don’t understand what hardening does, whether it would hurt more than help, etc etc.
For a complete scrub like me, all I can get out of these articles is which are a must download, I never understand which are to avoid and which provide some kind of benefit like fixing bugs and stuff. Actually I don’t see how fixing memory leak issues can be anything but mandatory who on earth thinks it’s okay to have your computer freeze up every windows update and possibly crash it? Hence why I would doubt and think “well maybe ghacks knows something I don’t” and makes it even harder to decide.
So Martin, anyone, what do I download to get rid of that problem? Actually what can I download safely period?
https://support.microsoft.com/en-us/kb/890830 has nothing to do with IE. it’s MRT anti-virus software that checks Windows before installing kernel updates. If MRT detects a virus… it will stop the update process (leaving the infected PC vulnerable to security risks as well) until the infected PC is cleaned.
The “non-security” updates listed in the article have been released since Microsoft published the August 2015 security updates. If you check for updates regularly, it means that they may already be installed.
Furthermore, the article lists updates for all systems not just Windows 7. For instance, store app updates don’t affect Windows 7.
I cannot really say why there is a discrepancy between what you see and what is listed here (taken directly from Microsoft).
For those of us concerned about MS snooping, telemetry, etc., are there any updates this month besides 3083324 that we should avoid?
Thank you!
@KyotoKid: never hear of virtualization? Just install VirtualBox and install Windows and the software you need in it.
If you’re really so afraid of the big M, then just change OSs. All this hysteria and lies over absolutely nothing isn’t even funny anymore.
…unfortunately most of my 3D graphics software does not work in Linux even using Wine,
…and MacOS? Well, let me win a lotto first.
So some of us are stuck with the “Big M” with no other option.
My lap top updated today and now my Microsoft edge will not open at all
Very enlightening! Now I learned that specially crafted things are bad.
Just a joke Martin, thank you for this great article as usual. ;)
It’s that time of the month huh? I guess I better shut down Linux Mint and brush the cob webs off of Windows 7 so I can log in and update it. Me too…only critical updates for now on.
Thank you Martin.
I’m on Win 7 as well and have hidden KB3083324.
Thank you.
I’m on Windows 7 and i’ve already hidden updates regarding telemetry. Gonna install security updates only. KB3083324 is kinda suspicious too, so im hiding it too.