Lenovo once again in hot waters over Lenovo Service Engine BIOS
The year has not been good for Lenovo so far. After news broke in February that the company shipped some of its computer systems with adware and a problematic root certificate, it seemed unlikely that a major incident like this would happen again.
Recent threads on Reddit and Hacker News indicate that Lenovo used a utility it called Lenovo Service Engine in the BIOS of some products that downloaded a program called OneKey Optimizer to user systems and sent "non-personally identifiable system data" to Lenovo servers.
What makes this particularly worrisome is that Windows files were overwritten on boot, that files were added to the Windows system32 directory, and that a service was set up on the system to transfer the data to Lenovo.
The collected data, according to Lenovo, consists of machine type and model, a system UUID, region and date. Once the data has been submitted successfully the service is automatically disabled on the system.
Since the tool is based in the BIOS, it will do its work even if the Lenovo machine is formatted and Windows is installed cleanly afterwards.
Security vulnerabilities were discovered in Lenovo's implementation, which the company admits were not consistent with Microsoft's security guidelines for Windows Platform Binary Table.
But what is the Windows Platform Binary Table?
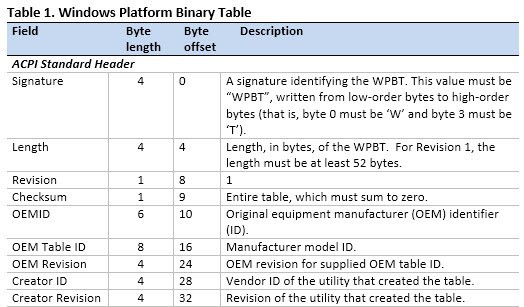
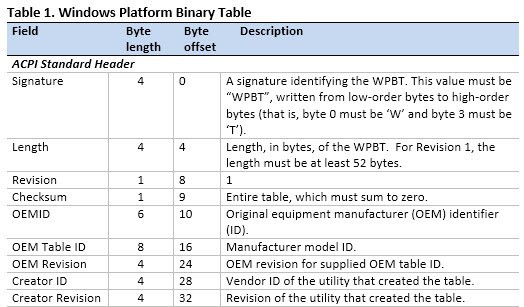
The WPBT is a fixed Advanced Configuration and Power Interface (ACPI) table that enables boot firmware to provide Windows with a platform binary that the operating system can execute.
[..]
It is expected that the binary pointed to by the WPBT is part of the boot firmware ROM image. The binary can be shadowed to physical memory as part of the initial bootstrap of the boot firmware, or it can be loaded into physical memory by extensible boot firmware code prior to executing any operating system code.
Affected products (according to this news post)
Lenovo Notebooks: Flex 2 Pro 15 (Broadwell), Flex 2 Pro 15 (Haswell), Flex 3 1120, Flex 3 1470/1570, G40-80/G50-80/G50-80 Touch, S41-70/U41-70, S435/M40-35, V3000 , Y40-80, Yoga 3 11 , Yoga 3 14, Z41-70/Z51-70, Z70-80/G70-80
Lenovo Desktop: A540/A740, B4030, B5030, B5035, B750, H3000, H3050, H5000, H5050, H5055, Horizon 2 27, Horizon 2e(Yoga Home 500), Horizon 2S, C260, C2005, C2030, C4005, C4030, C5030,
X310(A78), X315(B85)
Lenovo Desktop (China): D3000, D5050, D5055, F5000, F5050, F5055, G5000, G5050, G5055, YTÂ A5700k, YT A7700k, YT M2620n, YT M5310n, YT M5790n, YT M7100n, YT S4005, YT S4030, YT S4040, YT S5030
The fix
Lenovo has released BIOS updates for affected products that disable the Lenovo Service Engine, and a tool that removes services and files on systems running Windows 7, Windows 8 and 8.1, and Windows 10.
The removal tool runs the following operations on affected systems:
- Stops the LSE service
- Deletes all files installed by the LSE module, which include C:\windows\system32\wpbbin.exe,
C:\windows\system32\LenovoUpdate.exe, C:\windows\system32\LenovoCheck.exe - Repairs the autocheck files in Windows
- Disables the UEFI variable that enables LSE if the system is running Windows 8, 8.1 or 10 in UEFI mode
Downloads are provided on the Lenovo support website.
Closing Words
This is Lenovo's second major security incident this year that affects company products. While some customers may have drawn a line earlier this year when the first incident occurred, it is likely that others will do so after this second incident.
Now You: Have you bought Lenovo in the past? Will you do so in the future?

















Third time this year!
http://boingboing.net/2015/09/22/yet-another-pre-installed-spyw.html
I do find it curious that Lenovo have received so much flak for this, yes they used the Windows Platform Binary Table (WPBT) to install some dodgy software but it’s not like other companies aren’t using WPBT in a similar manner, both HP and Dell use the WPBT to install software before the OS boots.
Personally I would point the finger at Microsoft and possibly the other companies who are members of the UEFI Forum, its not called the Windows Platform Binary Table for no reason, this was something Microsoft wanted implemented so its Windows OS’s from 8 onwards could load a binary file before the OS loads.
A few weeks ago I bought my first Lenovo (E540 Think Pad) specifically to be able to access its innards (like the fan and cleaning)
– Toshiba and many others are a nightmare to clean.
Lenovo is an excellent machine although the “missing” function keys is a pest.
– no problems yet and support has been very good.
No complaints here
I got caught twice by MS Windows updates last year … were they a chinese conspiracy too? :sarcasm:
– and then there is Google constantly watching our every move … !
If you know for sure someone is a robber or any kind of criminal do you invite him (or her) to your home?
I know what I do.
So if it’s from China no, thank you.
Or from America…
So, who is welcome in your home?
My first ever Lenovo is a Flex10 netbook/tablet combo – it will be the last, due to underperforming hardware, plus the enormous amount of third-party and other bloatware, besides the Superfish scandal.
Shame, as it’s quite a well-built unit as netbooks go.
yep, a chinese computer company…why would anyone trust them….. just a laugh.
I’m actually less concerned about what the Chinese government wants to know about me and what they might do with it than I am the U.S. government and all its three letter tentacles.
So, move to China then.
I try never to buy from Chinese Red Army affiliated companies.
And where is the hardware you do use manufactured ?
Japan. Korea. Or my basement from parts sourced from various California companies. And no, components were not subcontracted out to China. So nope, I don’t use Apple products.
Outrage fatigue is setting in….
“Windows 10 automatically spies on your children and sends you a dossier of their activity”
https://boingboing.net/2015/08/10/windows-10.html
“The collected data, according to Lenovo, consists of machine type and model, a system UUID, region and date. ”
Microsoft’s Windows 10 submits more data regarding your PC and will never issue a FIX.
UUID is unique. That UUID pertains to a single Laptop all over the world.
The person who bought it is the only one linked to that UUID.
It’s not your fathers IBM. To bad IBM sold off it’s PC business to Lenovo. China is not our friend. How long is it going to take Washington and our business leaders to realize this???
US is neither nobody’s friend.
How do we know if they’ve realized it or not? Maybe they believe they just don’t have the choice. Options is the key-word and the best on the long term may not correspond to the best on the short term. Like with Chess, anticipating is mandatory. And considering China as not a friend may be incompatible with anticipation whether or not it is true now. Nowadays brains tends to replace muscles, it’s where the true power is.
What did you say?
The only Lenovo product I’ve ever bought is a pair of bluetooth headphones…and I’m starting to worry about that. :)
The Lenovo Support Team now know you listen to Dr Hook, Dr. Dre, Doctor Doctor, Doctor’s Orders and Doctor & the Medics. But their “spin doctor” department says it’s all harmless. They were simply protecting you from Justin Bieber. Nothing to see here. Move along.
Do tey connect via usb? If they do they could be “bad usb” https://srlabs.de/badusb/
Same here. My old ThinkPad X201 is great, but the newer ones are rubbish. Nasty screens, poorer keyboards (media keys the default on a business machine? what were they thinking!), and horrible buttonless trackpads too. Add on two malware issues in one year and it’s very clear to see that my next laptop won’t be a Lenovo.
Unfortunately, Dell are going hand in hand with Lenovo when it comes to lousy laptop screens, so the choice here is very limited…
Incidentally, Dell also defaulted their Precision M3800 to “media keys” – and what’s more, their support staff didn’t know what I was talking about when I phoned them, desperate to know how to reassign the F keys as hotkeys for my recording software etc. Fortunately I eventually found the settings for myself, buried in Control Panel under Mobility Settings :-/
I’m truely dispointed by this behaviour. You used to know where you stood with a quality thinkpad (still got an x61 that gets used from time to time). Aside from the issue earlier this year the last new lenovo I used (a yoga maybe) had a horrid touchpad. Guess my next laptop will be a dell at this rate.
I always build my desktops from parts, so I didn’t use Lenovo nor will I use it in the future. However, as an outside observer, I cannot help but notice that these incidents do not look random; Lenovo seem to be decided to try different methods to push spyware on their customers computers. I might be wrong, but the future will tell…
It certainly doesn’t seem accidental that they installed something to the BIOS specifically to force Windows to transmit data to them.
Short: If it has to be Lenovo, get a ThinkPad.
short: even if it has to be lenovo, don’t get a lenovo.