Microsoft Security Bulletins For July 2015
Welcome to the July 2015 patch overview that reviews all security and non-security patches that Microsoft released this month for Microsoft Windows and other company products.
This is the last Patch Tuesday before the release of Microsoft's new operating system Windows 10.
The guide starts with an executive summary that provides you with a quick overview of the most important information.
It is then followed by information detailing which Microsoft products and versions are affected by security patches, and then the list of security patches and security advisories.
Afterwards, we list non-security patches that may be of interest and how to download and deploy the updates.
Executive Summary
- Microsoft released a total of 14 different security bulletins in July 2015.
- Four of the bulletins have received the highest aggregate severity rating of critical.
- All client and server operating systems with the exception of Server Core are affected by at least one critical bulletin.
- Software affected by vulnerabilities this month include Microsoft Office, Microsoft SharePoint Server and SQL Server.
Operating System Distribution
Windows Vista is affected by two critical bulletins while all other client operating systems are only affected by one. The bulletin that affects Vista but no other client operating system is MS15-066 which patches vulnerabilities in the VBScript Scripting Engine.
The server side shows a similar picture, only that Server 2003 and 2008 are affected by the same vulnerability while newer Server versions are not.
- Windows Vista: 2 critical, 2 important (MS15-065, MS15-066, MS15-072, MS15-073)
- Windows 7: 1 critical, 2 important (MS15-065, MS15-072, MS15-073)
- Windows 8 and 8.1: 1 critical, 2 important (MS15-065, MS15-072, MS15-073)
- Windows RT and Windows RT 8.1: 1 critical (MS15-065)
- Windows Server 2003: 1 critical, 2 important, 1 moderate (MS15-065, MS15-072, MS15-073, MS15-066)
- Windows Server 2008: 1 critical, 2 important, 1 moderate (MS15-065, MS15-072, MS15-073, MS15-066)
- Windows Server 2008 R2:Â 2 important, 1 moderate (MS15-065, MS15-072, MS15-073)
- Windows Server 2012 and 2012 R2: 2 important, 1 moderate (MS15-072, MS15-073, MS15-065)
- Server Core: 2 important (MS15-072, MS15-073)
Other Microsoft Products
- Microsoft SQL Server 2008 Service Pack 3, Service Pack 4: 1 important (MS15-058)
- Microsoft SQL Server 2008 R2 Service Pack 2, Service Pack 3: 1 important (MS15-058)
- SQL Server 2012 Service Pack 1, Service Pack 2: 1 important (MS15-058)
- SQL Server 2014: 1 important (MS15-058)
- Microsoft Office 2007, 2010, 2013, 2013 RT, Office for Mac, Excel Viewer 2007, Word Viewer, Office Compatibility Pack Service Pack 3: 1 important (MS15-070)
- Microsoft SharePoint Server 2007, 2010, 2013: 1 important (MS15-070)
Security Bulletins
- MS15-058 - Vulnerabilities in SQL Server Could Allow Remote Code Execution (3065718) - Important - Remote Code Execution
- MS15-065 - Security Update for Internet Explorer (3076321) - Critical - Remote Code Execution
- MS15-066 - Vulnerability in VBScript Scripting Engine Could Allow Remote Code Execution (3072604) - Critical - Remote Code Execution
- MS15-067 - Vulnerability in RDP Could Allow Remote Code Execution (3073094) - Critical - Remote Code Execution
- MS15-068 - Vulnerabilities in Windows Hyper-V Could Allow Remote Code Execution (3072000) - Critical - Remote Code Execution
- MS15-069 - Vulnerabilities in Windows Could Allow Remote Code Execution (3072631) - Important - Remote Code Execution
- MS15-070 - Vulnerabilities in Microsoft Office Could Allow Remote Code Execution (3072620) - Important - Remote Code Execution
- MS15-071 - Vulnerability in Netlogon Could Allow Elevation of Privilege (3068457) - Important - Elevation of Privilege
- MS15-072 - Vulnerability in Windows Graphics Component Could Allow Elevation of Privilege (3069392) - Important - Elevation of Privilege
- MS15-073 - Vulnerability in Windows Kernel-Mode Driver Could Allow Elevation of Privilege (3070102) - Important - Elevation of Privilege
- MS15-074 - Vulnerability in Windows Installer Service Could Allow Elevation of Privilege (3072630) - Important - Elevation of Privilege
- MS15-075 - Vulnerabilities in OLE Could Allow Elevation of Privilege (3072633) - Important - Elevation of Privilege
- MS15-076 - Vulnerability in Windows Remote Procedure Call Could Allow Elevation of Privilege (3067505) - Important - Elevation of Privilege
- MS15-077 - Vulnerability in ATM Font Driver Could Allow Elevation of Privilege (3077657) - Important - Elevation of Privilege
Security Advisories and updates
- Security Update for Internet Explorer Flash Player for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, and Windows Server 2012 (KB3065823) - Microsoft security advisory: Update for vulnerabilities in Adobe Flash Player in Internet Explorer: July 8, 2015
- Security Update for Internet Explorer Flash Player for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, and Windows Server 2012 (KB3074219) - Microsoft security advisory: Update for vulnerabilities in Adobe Flash Player in Internet Explorer: June 23, 2015
- MS15-057: Security Update for WEPOS and POSReady 2009 (KB3033890) - MS15-057: Vulnerability in Windows Media Player could allow remote code execution: June 9, 2015
- Â Microsoft Security Advisory 2974294 - Vulnerability in Microsoft Malicious Software Removal Tool Could Allow Elevation of privilege
- Microsoft Security Advisory 3057154 - Update to Harden Use of DES Encryption
Non-security related updates
- Update for Windows 7 (KB2952664) - Compatibility update for upgrading Windows 7
- Update for Windows 8.1 (KB2976978) - Compatibility update for Windows 8.1 and Windows 8
- Update for Windows 8.1 and Windows 7 (KB3035583) - Update installs Get Windows 10 app in Windows 8.1 and Windows 7 SP1
- Update for Windows 7 (KB2977759) - Compatibility update for Windows 7 RTM
- Update for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2 (KB3065987) - Windows Update Client for Windows 7 and Windows Server 2008 R2: July 2015
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3065988) - Windows Update Client for Windows 8.1 and Windows Server 2012 R2: July 2015
- Update for Windows 8.1 and Windows Server 2012 R2 (KB3013791) - "DPC_WATCHDOG_VIOLATION (0x133)" Stop error when there's faulty hardware in Windows 8.1 or Windows Server 2012 R2
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3018467) - Items in the navigation pane of File Explorer may disappear in Windows
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3029438) - Can't open Windows Store applications in Windows 8.1 or Windows Server 2012 R2
- Update for Windows 8.1 and Windows RT 8.1 (KB3029606) - Update to improve Bluetooth driver diagnosis in Windows 8.1
- Update for Windows 7 and Windows Server 2008 R2 (KB3040272) - Start time increases after another language pack is added to Windows
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3049989) - HKSCS characters are displayed incorrectly by PDF APIs in Windows
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3053863) - Windows 8.1 can't discover Samsung TV as wireless display device
- Update for Windows Server 2012 R2 (KB3054203) - Update for SIP to enable WinVerifyTrust function in Windows Server 2012 R2 to work with a later version of Windows
- Update for Windows Server 2012 (KB3054204) - Update lets the WinVerifyTrust function in Windows Server 2012 work with a later version of Windows
- Update for Windows Server 2008 R2 (KB3054205) - Update for SIP to enable WinVerifyTrust function in Windows Server 2008 R2 SP1 to work with a later version of Windows
- Update for Windows Server 2008 (KB3054206) - Update for SIP to enable WinVerifyTrust function in Windows Server 2008 SP2 to work with a later version of Windows
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3054256) - Reliability improvements for Windows 8.1: June 2015
- Update for Windows 8.1 and Windows RT 8.1 (KB3056347) - Location feature is not turned off after you enable "Turn off location" policy setting in Windows RT 8.1 or Windows 8.1
- Update for Windows 8, Windows RT, and Windows Server 2012 (KB3058163) - Activation doesn't work if the sppsvc.exe process doesn't start automatically in Windows 8 or Windows Server 2012
- Update for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, and Windows Server 2012 (KB3058168) - Update that enables Windows 8.1 and Windows 8 KMS hosts to activate a later version of Windows
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3059316) - You cannot move the scrollbar on Windows by dragging the mouse
- Update for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, and Windows Server 2012 (KB3060383) - Decimal symbol and digit grouping symbol are incorrect for the Swiss language locale in Windows
- Update for Windows Server 2012 R2 (KB3060681) - SIL hourly task fails to forward complete data over https in Windows Server 2012 R2
- Update for Windows 8.1 and Windows Server 2012 R2 (KB3060793) - "0x0000001E" or "0x00000133" Stop error when you transfer data through a USB-based RNDIS device on Windows
- Update for Windows 8.1, Windows RT 8.1, Windows 8, and Windows RT (KB3061421) - Updated APN database entry for Northern Michigan University (NMU) for Windows 8.1 and 8
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3061468) - June 2015 compatibility update for Windows RT 8.1, Windows 8.1, and Windows Server 2012 R2
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3063843) - System takes too long time to log on to a computer because of large numbers of WNF state name registrations in Windows
- Update for Windows 8.1 and Windows RT 8.1 (KB3064059) - Explorer.exe process crashes after File History item in Control Panel is opened in Windows 8.1
- Update for Windows 8.1, Windows Server 2012 R2, Windows 8, Windows Server 2012, Windows 7, and Windows Server 2008 R2 (KB3064209) - June 2015 Intel CPU microcode update for Windows
- Update for Windows Embedded Standard 7, Windows 7, Windows Server 2008 R2, Windows Server 2008, Windows Vista, Windows Server 2003, and Windows XP Embedded (KB3065979) - "GsDraw error (1): GenericError" error occurs and application crashes when you create text outline in Windows
- Update for Windows 8.1 (KB3064683) - Windows 8.1 OOBE modifications to reserve Windows 10
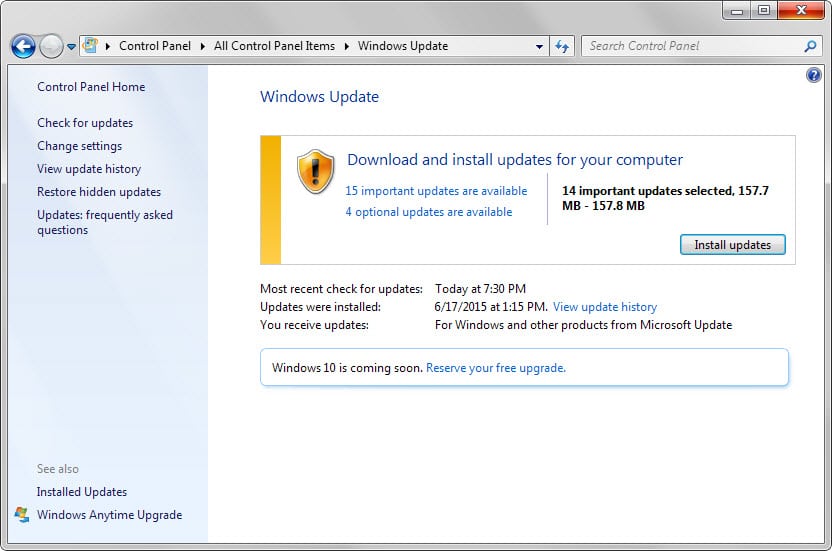
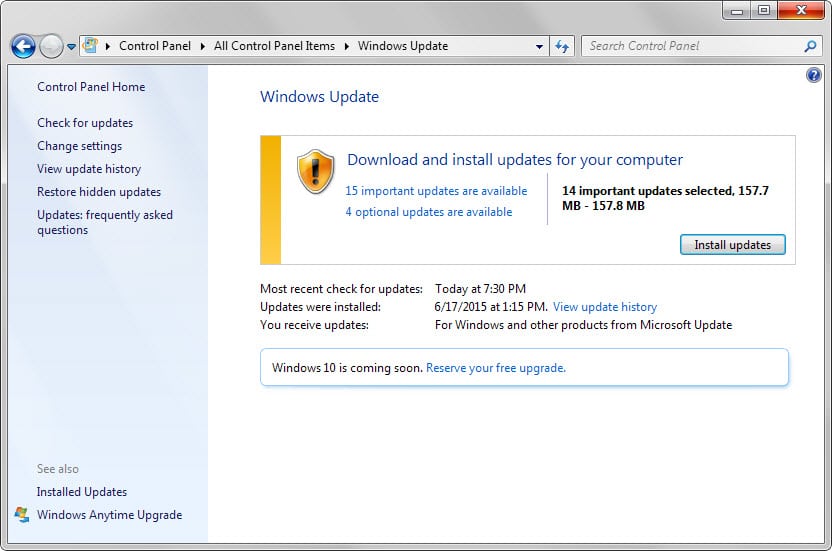
How to download and install the July 2015 security updates
Updates are provided via Windows Update if automatic updates are enabled. Updates are not picked up in real-time by Windows which is why you may want to run a manual check for updates to download and deploy them as soon as possible.
- Tap on the Windows-key.
- Type Windows Update and select the right result.
- When the new window opens, click on "check for updates" to run a manual check.
Windows users who don't want to download updates automatically find them listed on Microsoft's Download Center as well.
There they are offered as individual downloads and as a monthly security ISO image.
Last but not least, several third-party programs exist that you can use to download all patches in one operation without using Windows Update.
Additional information
- Microsoft Security Response Center blog on the 2015 Bulletin Release
- Microsoft Security Bulletin Summary for July 2015
- List of software updates for Microsoft products
- List of security advisories of 2015
- Our in-depth update guide for Windows




















Thanks Beau,
some additional steps that may help others:
In case you use a VM with the Administrator account disabled and the rocovery console does not accept any password proceed as follows:
a) Shut down the VM
b) Add the disk that contains the OS of the Windows 2003 server to a secondary VM with Windows OS
c) Start the secondary VM and run regedit
d) Navigate to HKEY_LOCAL_MACHINE
e) Under File select ‘Load Hive’
f) Select file(!) %windir%/system32/config/software from the added disk(!) e.g. G:\WINDOWS\system32\config\software
g) Assign a name e.g. Offline
h) in the Offline folder go to HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\Setup\RecoveryConsole and set the DWORD value of SecurityLevel to 1
i) Unload hive, shutdown the secondary VM, remove the disk, again start the primary VM and proceed as discribed by Beau
Hope this helps,
Martin
Thanks Beau, I almost gave up with one critical SQL server as that would not boot up after latest patches.. was always restarting and in safe mode stopped with ACPITABL.DAT file, Found tons of tricks to fix it and none helped until I found this tip of removing the KB3067505.
Need to check other servers as well as we unfortunately still need few in production use.
Awesome and perfect timing with the fix. For each one that died, I have had only enough time to setup dhcp on another server with a higher ip pool range. I thought I shut off updates on the other servers, but found another dead this morning. The fix worked perfectly.
Of all the servers that installed the updates it was only the x64 bit machines that failed.
Thanks so much for this great service every month.
I do not use Internet Explorer or email programs from MS. My question is do I need to download the updates for IE?. Thanks.
Thanks for the hint about the kb3067505 being a dud. We had a few 2003 systems die because of it. Using the recovery console and getting it out fixes the problem and gets the systems back online.
Interesting how one of the last updates for 2003 kills the system. I wonder if microsoft will step up with a fix for it, or if it is just a big middle finger salute to whoever is still stuck with the system.
Joao
Hey Jim or anyone else.
I had the same problem on a clients Windows 2003 server. Seems KB3067505 is the problem.
Load a CD/ISO and get into recovery mode and run the following
CHDIR C:\WINDOWS\$NTUNINSTALLKB3067505$\SPUNINST
BATCH SPUNINST.TXT
This will uninstall the update and you should be good to go.
**We only just sorted this out after installing the updates today. I actually uninstalled a few before this one, as I was doing them one at a time and rebooting each time. Came good after that update was uninstalled, so it’s possible it’s a combination of updates. If you’re not sure what updates have been installed, just type “DIR” into the recovery console and see all the $NTUNINSTALL folders and see which one’s match the install date.
Thank you so much! I reposted your solution in my blog linking to your original comment. I was about to embark on a search to find the culprit and was lucky enough to find your comment and save time.
Thank you !!
I did the update and now windows will not load. Anyone else have this problem?
I´ve got the same here…more than 30 computers can´t load windows after install the updates, it stops on that “Applying updates..” screen. Anyone with the same issue? Any idea how to fix it?
I have three servers that no longer boot.
STOP: c000021a (Fatal System Error)
The windows Logon Process System process terminated unexpectedly with a status of 0x00000080 (0x00000000 0x00000000).
The system has been shut down.
Haven’t been able to recover them yet.
KB2952664 – Compatibility update for upgrading Windows 7 left aside here as I have for all updates concerning the enthronement of HRH Windows 10.
Up to now, here on Windows 7SP1 x-64, these updates are :
KB2830477
KB2990214
KB3013531
KB3021917
KB3035583
KB3068708
KB2952664
All concerning and concerning only coming update of Windows 10, which I wish not, not at all, not at this time anyway.
I got 3 optional updates that want to put the Win 10 reminder thing back in my systray, despite having hid those 3 in the past. I figured they’d auto-unhide them again. sigh.
Also, after doing the critical security updates, my (legit) Win 7 de-activated itself, and I was given a popup telling me I needed to activate windows. I’ve had this copy of Windows since beta in 2009. It was just a simple matter of running the activation bit, but still… weird.
kb3067903
I question most of these updates. ” if an attacker first places a specially crafted dynamic link library (DLL) file in the target user’s current working directory.” the disclaimer clearly says, “if”, how does the end
user not know and is assured that microsoft is clandestinely updating its disabled, telemetry
devices. End users need to know exactly the specific details. Generic descriptions like the above
does not give me confidence in any of _microsofts_products.
I get an error when trying to view that link so I can’t see any info it has on it. Would you mind describing it?
Thank you.
I could have sworn I saw a content page when I opened it, but I do get a no page exist error as well now. Strange.
MS15-069: Description of the security update for Windows: July 14, 2015 (KB3067903)
This security update resolves vulnerabilities in Microsoft Windows. The vulnerabilities could allow remote code execution if an attacker first places a specially crafted dynamic link library (DLL) file in the target user’s current working directory. Then, the attacker convinces the user to open an .rtf file or to start a program that is designed to load a trusted DLL file. But instead, the program loads the attacker’s specially crafted DLL file. An attacker who successfully exploited the vulnerabilities could take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts that have full user rights.
I see a kb3067903 also. I can’t find any info on it.
This one? https://support.microsoft.com/en-us/kb/3067903
For Windows Server 2003 these are the last updates as starting today, Microsoft no longer supports Windows Server 2003.
Yeah, worth a mention.